Powerpoint Templates and Google slides for Data Secure
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cloud application governance model for data security management
Cloud application governance model for data security managementPresenting this set of slides with name Cloud Application Governance Model For Data Security Management. The topics discussed in these slides are Business, Technology, Service. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Big data security framework with data protection and privacy
Big data security framework with data protection and privacyIntroducing our Big Data Security Framework With Data Protection And Privacy set of slides. The topics discussed in these slides are Data Management, Data Protection And Privacy, Network Security, Infrastructure Security And Integrity, Access Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data and security breach process
Data and security breach processThis slide exhibits data and security breach attack process conducted by hackers to get access to company data. It includes multiple activities such as- link forwarding by emails, data sharing and attacking and so on. Introducing our Data And Security Breach Process set of slides. The topics discussed in these slides are Research, Stage Attack, Exfiltrate. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data breach security requirements and goals
Data breach security requirements and goalsThis slide exhibits data breach security requirement with major goals and requirements. It includes multiple section like securing cardholder data, manage vulnerability program and so on. Introducing our Data Breach Security Requirements And Goals set of slides. The topics discussed in these slides are Goals, Measures, Management, Secure Network, Product. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data security breach response plan
Data security breach response planFollowing slide exhibits data security breach response plan. It includes major elements such as-developing containment plan, hardware requirement assessment and so on. Introducing our Data Security Breach Response Plan set of slides. The topics discussed in these slides are Response Stage, Response Team, Key Questions And Tasks. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Process for responding to security data breach
Process for responding to security data breachThis slide exhibits process for responding to security data breach. It includes multiple steps such as- analyzing the current damage, keeping record how much damage is caused and so on. Introducing our Process For Responding To Security Data Breach set of slides. The topics discussed in these slides are Survey, Limit, Learn, Engage, Record. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security data breach incident report
Security data breach incident reportThis slide exhibits security data breach incident report. It includes multiple steps such as- report the number of personal data record lost, analyze the possible effects of personal data breaches and so on. Introducing our Security Data Breach Incident Report set of slides. The topics discussed in these slides are Consequences, Measures, Data Breach Details. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security data breach process by backdoor
Security data breach process by backdoorFollowing slide showcase how a data breach process is performed by hacker to collect and utilize company data. It includes following activities such as- code integration with company software, so on. Introducing our Security Data Breach Process By Backdoor set of slides. The topics discussed in these slides are Execution Persistence, Defense Evasion, Supply Chain Attack, Exfiltration, Backdoor Activates. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Steps for minimizing security and data breach
Steps for minimizing security and data breachFollowing slide exhibits steps for minimizing security and data breach. It includes major steps such as- malware protection and monitoring, source code assessment etc. Introducing our Steps For Minimizing Security And Data Breach set of slides. The topics discussed in these slides are Vulnerability Management, Infrastructure Management, Cyber Analysis, Incident Response, Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Communication plan for cybersecurity events and incidents corporate data security awareness ppt aids
Communication plan for cybersecurity events and incidents corporate data security awareness ppt aidsThis slide covers the communication delivery channels for cyber security awareness training for different departments target audience along with program topics. Deliver an outstanding presentation on the topic using this Communication Plan For Cybersecurity Events And Incidents Corporate Data Security Awareness Ppt Aids. Dispense information and present a thorough explanation of Development, Security, Management, Cybersecurity, Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Corporate data security awareness automated security awareness platform and cost ppt background
Corporate data security awareness automated security awareness platform and cost ppt backgroundThis slide covers the Automated training programs for security awareness that will help educate workers to act appropriately, even when introduced to entirely new risks. Present the topic in a bit more detail with this Corporate Data Security Awareness Automated Security Awareness Platform And Cost Ppt Background. Use it as a tool for discussion and navigation on Platform, Functioning, Benefits, Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Corporate data security awareness comparison ppt powerpoint presentation inspiration show
Corporate data security awareness comparison ppt powerpoint presentation inspiration showIncrease audience engagement and knowledge by dispensing information using Corporate Data Security Awareness Comparison Ppt Powerpoint Presentation Inspiration Show. This template helps you present information on two stages. You can also present information on Male Users, Female Users using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Corporate data security awareness organization compliance metrics ppt powerpoint layout
Corporate data security awareness organization compliance metrics ppt powerpoint layoutThis slide covers the metrics that measure what you are doing with the awareness project, exactly how you will train and how. Such metrics are of particular importance for purposes of compliance and monitoring. Present the topic in a bit more detail with this Corporate Data Security Awareness Organization Compliance Metrics Ppt Powerpoint Layout. Use it as a tool for discussion and navigation on Training Completion, Communication Methods, Policy Sign Off. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Corporate data security awareness organization impact metrics strategic ppt powerpoint images
Corporate data security awareness organization impact metrics strategic ppt powerpoint imagesThis slide the metrics That assess how your security awareness plan serves the overall security system of your company, and therefore the organizations mission. Deliver an outstanding presentation on the topic using this Corporate Data Security Awareness Organization Impact Metrics Strategic Ppt Powerpoint Images. Dispense information and present a thorough explanation of Organization, Policy Violations, Data Loss Incidents, Human Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enhancing overall project security it enabling data security risk management action plan
Enhancing overall project security it enabling data security risk management action planThis slide provide details about data security risk management action plan which will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them. Present the topic in a bit more detail with this Enhancing Overall Project Security It Enabling Data Security Risk Management Action Plan. Use it as a tool for discussion and navigation on Management, Confidential, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building organizational security strategy plan selecting data centre management solution
Building organizational security strategy plan selecting data centre management solutionThis slide will help firm in choosing the suitable data center management solution by analyzing on various parameters such as server health management, firmware update, ghost server detection, equipment scheduling, etc. Deliver an outstanding presentation on the topic using this Building Organizational Security Strategy Plan Selecting Data Centre Management Solution. Dispense information and present a thorough explanation of Equipment, Management, Solution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Data Protection Phase 2 Secure Your Cloud
Cloud Data Protection Phase 2 Secure Your CloudThis slide depicts how organizations could secure their cloud and what factors should keep under consideration while protecting the cloud. Deliver an outstanding presentation on the topic using this Cloud Data Protection Phase 2 Secure Your Cloud. Dispense information and present a thorough explanation of Implement Information Security, Data Encryption, Segmented Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Security Best Practices Cloud Data Protection
Cloud Security Best Practices Cloud Data ProtectionThis slide defines the best practices of cloud security, including understanding cloud utilization and risk, protection of cloud, and responding to cloud protection issues. Deliver an outstanding presentation on the topic using this Cloud Security Best Practices Cloud Data Protection. Dispense information and present a thorough explanation of Cloud Protection Issues, Cloud Service, Infrastructure As A Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Difference Between Cloud Security Solutions And Traditional Cloud Data Protection
Difference Between Cloud Security Solutions And Traditional Cloud Data ProtectionThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses. Deliver an outstanding presentation on the topic using this Difference Between Cloud Security Solutions And Traditional Cloud Data Protection. Dispense information and present a thorough explanation of Opportunity, Low Efficiency, Cloud Security, Expense using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Hybrid Cloud Security Solutions Cloud Data Protection
Hybrid Cloud Security Solutions Cloud Data ProtectionThis slide describes the hybrid cloud security solutions, which include categorization of services and redundancy. Deliver an outstanding presentation on the topic using this Hybrid Cloud Security Solutions Cloud Data Protection. Dispense information and present a thorough explanation of Categorization Of Services, Procedures, Servers, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Cloud Security Use Cases Cloud Data Protection
Key Cloud Security Use Cases Cloud Data ProtectionThis slide represents the key use cases of cloud security namely privileged account access, data exfiltration, suspicious network connections, man-in-the-cloud attack, and unsecured storage containers. Present the topic in a bit more detail with this Key Cloud Security Use Cases Cloud Data Protection. Use it as a tool for discussion and navigation on Suspicious Network Connections, Data Exfiltration, Unsecured Storage Containers. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 What Makes Cloud Security Different Cloud Data Protection
What Makes Cloud Security Different Cloud Data ProtectionThis slide shows two factors that make cloud security different, and these factors are, convenience over security, and centralization and multi-tenant storage system. Deliver an outstanding presentation on the topic using this What Makes Cloud Security Different Cloud Data Protection. Dispense information and present a thorough explanation of Innovation, Development, Essential Strategy, Convenience Over Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Why Cloud Security Is Important Cloud Data Protection
Why Cloud Security Is Important Cloud Data ProtectionThis slide defines why cloud security is essential based on data centralization, cost, diminished control, and data reliability. Present the topic in a bit more detail with this Why Cloud Security Is Important Cloud Data Protection. Use it as a tool for discussion and navigation on Centralized Security, Cost Effective, Cloud Security. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Risk Assessment And Management Plan For Information Security Current Information And Data Security
Risk Assessment And Management Plan For Information Security Current Information And Data SecurityThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating Present the topic in a bit more detail with this Risk Assessment And Management Plan For Information Security Current Information And Data Security. Use it as a tool for discussion and navigation on Information, Capabilities, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
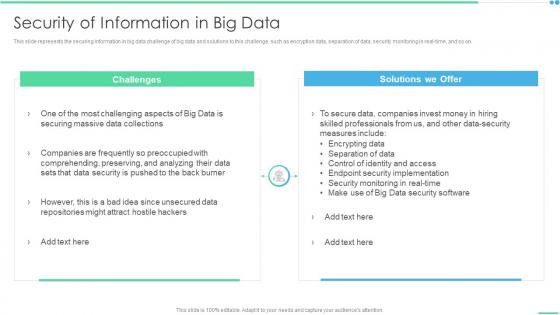 Security Of Information In Big Data Ppt Layouts Layouts
Security Of Information In Big Data Ppt Layouts LayoutsThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Increase audience engagement and knowledge by dispensing information using Security Of Information In Big Data Ppt Layouts Layouts. This template helps you present information on two stages. You can also present information on Challenges, Solutions We Offer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementation Steps Enable Data Security Crm System Implementation Guide For Businesses
Implementation Steps Enable Data Security Crm System Implementation Guide For BusinessesThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Implementation Steps Enable Data Security Crm System Implementation Guide For Businesses. Use it as a tool for discussion and navigation on Implementation, Compliance, Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Crm Implementation Process Implementation Steps Enable Data Security
Crm Implementation Process Implementation Steps Enable Data SecurityThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Crm Implementation Process Implementation Steps Enable Data Security. Use it as a tool for discussion and navigation on Implementation, Authentication, Restrictions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Steps Enable Data Security Crm Software Deployment Guide
Implementation Steps Enable Data Security Crm Software Deployment GuideThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Implementation Steps Enable Data Security Crm Software Deployment Guide. Use it as a tool for discussion and navigation on Implementation, Authentication, Restrictions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Steps Enable Data Security Crm Platform Implementation Plan
Implementation Steps Enable Data Security Crm Platform Implementation PlanThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Deliver an outstanding presentation on the topic using this Implementation Steps Enable Data Security Crm Platform Implementation Plan. Dispense information and present a thorough explanation of Authentication, Implementation, Security Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Customer Relationship Management System Implementation Steps Enable Data Security
Customer Relationship Management System Implementation Steps Enable Data SecurityThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Deliver an outstanding presentation on the topic using this Customer Relationship Management System Implementation Steps Enable Data Security. Dispense information and present a thorough explanation of Implementation, Authentication, Restrictions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Backup Evaluation Sheet Security Incident Response Playbook Ppt Slides Background Image
Data Backup Evaluation Sheet Security Incident Response Playbook Ppt Slides Background ImageMentioned slide addresses evaluation sheet which can be used for assessing data backup activities. Sections covered in the sheet are backup testing frequency, type of backup solution and responsible person details. Present the topic in a bit more detail with this Data Backup Evaluation Sheet Security Incident Response Playbook Ppt Slides Background Image. Use it as a tool for discussion and navigation on Evaluation, Responsible, Solution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Incident Response Playbook Checklist For Work From Home Data Security
Security Incident Response Playbook Checklist For Work From Home Data SecurityDeliver an outstanding presentation on the topic using this Security Incident Response Playbook Checklist For Work From Home Data Security. Dispense information and present a thorough explanation of Remote, Workstations, Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Steps To Build Data Security And Privacy Plan
Steps To Build Data Security And Privacy PlanThe following slide showcases some steps to draft data safety and protection plan to gain user trust and confidence. It includes elements such as creating internal and external policy, implementation, responsibility, security vulnerabilities etc. Presenting our well structured Steps To Build Data Security And Privacy Plan. The topics discussed in this slide are Collect Relevant Information, Train Employees, New Policies. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Checklist For Data Security Incident Management
Checklist For Data Security Incident ManagementIntroducing our Checklist For Data Security Incident Management set of slides. The topics discussed in these slides are Additional Data Losses, Response Team, Risk Assessment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Data Analysis With Reported Incident Metrics
Cyber Security Data Analysis With Reported Incident MetricsThis slide shows the scorecard of the data security with key performance indicators. It also includes the progress status of data readiness and security audits with their value and targets that has to be achieved during the period. Presenting our well structured Cyber Security Data Analysis With Reported Incident Metrics. The topics discussed in this slide are Data Production Readdress, Data Production Officer Nominated, Explicit Consent Tracking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Current Information And Data Security Capabilities Of Firm Formulating Cybersecurity Plan
Current Information And Data Security Capabilities Of Firm Formulating Cybersecurity PlanThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating. Deliver an outstanding presentation on the topic using this Current Information And Data Security Capabilities Of Firm Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Identify, Protect, Detect, Response using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Current Information And Data Security Cybersecurity Risk Analysis And Management Plan
Current Information And Data Security Cybersecurity Risk Analysis And Management PlanThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating Present the topic in a bit more detail with this Current Information And Data Security Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Capabilities, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information System Security And Risk Administration Current Information And Data Security Capabilities Of Firm
Information System Security And Risk Administration Current Information And Data Security Capabilities Of FirmThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating. Deliver an outstanding presentation on the topic using this Information System Security And Risk Administration Current Information And Data Security Capabilities Of Firm. Dispense information and present a thorough explanation of Risk Management Functions, Required Standard Rating, Actual Standard Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability
Checklist For Work From Home Data Security Cybersecurity Incident And VulnerabilityDeliver an outstanding presentation on the topic using this Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Data Security, Reporting Process, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security
Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Course Description, Instructor, Rating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Security Reporting, Phishing Simulations, Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Cyber Security Breach Lost Revenue Preventing Data Breaches Through Cyber Security
Impact Of Cyber Security Breach Lost Revenue Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the consequences of cyber security breach on the company revenue. It provides information about the revenue lost over different months caused by different cyber attack such as malware, social engineering attack, business email compromise etc. Deliver an outstanding presentation on the topic using this Impact Of Cyber Security Breach Lost Revenue Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Malware, Social Engineering Attack, Business Email Compromise using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 In House Training Schedule We Will Implement Preventing Data Breaches Through Cyber Security
In House Training Schedule We Will Implement Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to exhibit a comprehensive cyber security awareness training plan for the stakeholders. Information covered in this slide is related to malware, social engineering attack, business email compromise, ransomware, password attack, crypto jacking and IoT Based attack. Present the topic in a bit more detail with this In House Training Schedule We Will Implement Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Compromise, Training. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Measuring Security Awareness Campaign Results With KPIS Preventing Data Breaches Through Cyber Security
Measuring Security Awareness Campaign Results With KPIS Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase various key performance indicator KPIs which can assist the company to effectively track cyber security awareness campaign results. The KPIs are phishing rate, self reported incidents, security breaches, cost of security breach and campaign participation rate. Deliver an outstanding presentation on the topic using this Measuring Security Awareness Campaign Results With KPIS Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Phishing Rate, Security Breaches, Campaign Participation Rate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Preventing Data Breaches Through Cyber Security Awareness Table Of Contents
Preventing Data Breaches Through Cyber Security Awareness Table Of ContentsPresent the topic in a bit more detail with this Preventing Data Breaches Through Cyber Security Awareness Table Of Contents. Use it as a tool for discussion and navigation on Employees, Awareness Training, Cyber Security Breach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Pricing Plan Of Security Awareness Packages Preventing Data Breaches Through Cyber Security
Pricing Plan Of Security Awareness Packages Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the pricing plan of cyber security awareness package. It covers information about the total number of employees along with different packages such as silver, gold, platinum and diamond. Deliver an outstanding presentation on the topic using this Pricing Plan Of Security Awareness Packages Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Employees, Security, Awareness Packages using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Recognizing The Cyber Security Gaps Faced By Key Preventing Data Breaches Through Cyber Security
Recognizing The Cyber Security Gaps Faced By Key Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline the different cyber security gaps which are faced by employees, line and senior managers. Information covered in this slide is related to ransomware, password attack, crypto jacking, IoT based attack, malware etc. Present the topic in a bit more detail with this Recognizing The Cyber Security Gaps Faced By Key Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Comprise, Iot Based Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber Security
Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber SecurityPresent the topic in a bit more detail with this Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Compromise, Iot Based Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response Playbook
Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response PlaybookDeliver an outstanding presentation on the topic using this Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Process, Technology, Standards using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Schedule Matrix To Increase Data Security
Cyber Security Schedule Matrix To Increase Data SecurityThis slide signifies the IT schedule table to enhance data protection. It covers information about weekly schedule of activities to be conducted like configure technical security, conduct penetration test, install firewalls, conduct formal training.Presenting our well structured Cyber Security Schedule Matrix To Increase Data Security. The topics discussed in this slide are Conduct Stimulated, Configuring Technical, Unnatural Activities. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data Security Principles In Powerpoint And Google Slides Cpb
Data Security Principles In Powerpoint And Google Slides CpbPresenting our innovatively-designed set of slides titled Data Security Principles In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Data Security Principles that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well-structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design.
-
 Medical Data Security Measures For Healthcare Organizations
Medical Data Security Measures For Healthcare OrganizationsThis slide covers the details related to the protection of healthcare data. The purpose of this template is to address threats and implement measures for data safety. It includes details related to the restricting access to data and applications, logging and monitoring use, etc. Introducing our Medical Data Security Measures For Healthcare Organizations set of slides. The topics discussed in these slides are Restricted Access, Data And Applications, Conduct Frequent Risk. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Policy Data Classification Policy Overview And Approaches
Cyber Security Policy Data Classification Policy Overview And ApproachesThis slide represents the data classification policy overview and approaches. Approaches include highly restricted, restricted, and internal use and types of data each approach will include. Deliver an outstanding presentation on the topic using this Cyber Security Policy Data Classification Policy Overview And Approaches. Dispense information and present a thorough explanation of Highly Restricted, Approaches, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Selecting Data Centre Management Solution Strategic Organizational Security Plan
Selecting Data Centre Management Solution Strategic Organizational Security PlanThis slide will help firm in choosing the suitable data center management solution by analyzing on various parameters such as server health management, firmware update, ghost server detection, equipment scheduling, etc. Deliver an outstanding presentation on the topic using this Selecting Data Centre Management Solution Strategic Organizational Security Plan. Dispense information and present a thorough explanation of Software, Ghost Server, Firmware Update using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative Analysis Of Information And Network Data Security
Comparative Analysis Of Information And Network Data SecurityThe slide showcases the key differences between Information security and network security. It compares on the basis on aspects like data, part of , protection, attacks, scope and usage. Introducing our Comparative Analysis Of Information And Network Data Security set of slides. The topics discussed in these slides are Aspects, Information Security, Network Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Plan Useful Data Generating Security Awareness Among Employees To Reduce
Plan Useful Data Generating Security Awareness Among Employees To ReduceThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Present the topic in a bit more detail with this Plan Useful Data Generating Security Awareness Among Employees To Reduce Use it as a tool for discussion and navigation on Plan Useful, Data Backup Schedule This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB Comparison Between CASB And Data Loss Prevention
Cloud Access Security Broker CASB Comparison Between CASB And Data Loss PreventionThis slide describes the difference between cloud access security broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB Comparison Between CASB And Data Loss Prevention. Dispense information and present a thorough explanation of Purpose, Focus Area, Use Cases using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enable Data Centre Management Through Hyper Strategic Plan To Secure It Infrastructure Strategy SS V
Enable Data Centre Management Through Hyper Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the development of hyperconverged infrastructure for data center management. The focus areas include multi cloud support, data protection and security, flexible scaling, etc. Present the topic in a bit more detail with this Enable Data Centre Management Through Hyper Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Management, Infrastructure, Agility And Simplicity . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Action Plan For Data Center Security
Action Plan For Data Center SecurityThis slide illustrates data center security action plan. It includes security measures such as regular inspection, improve access control system, improve video surveillance, build redundant utilities and action taken with responsible authority Introducing our Action Plan For Data Center Security set of slides. The topics discussed in these slides are Security, Data, Plan. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Vendor Data Security Checklist For Market Research Company
Vendor Data Security Checklist For Market Research CompanyThe purpose of this slide is to showcase checklist for supplier information security for market research company. It includes various process to be completed such as vendor possess a security rating that meets with expectations, supplier has invested in data protection and information security controls etc. Introducing our Vendor Data Security Checklist For Market Research Company set of slides. The topics discussed in these slides are Supplier Has Invested, Protection Information This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.





