Powerpoint Templates and Google slides for Data Secure
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data centric security ppt powerpoint presentation styles professional cpb
Data centric security ppt powerpoint presentation styles professional cpbPresenting this set of slides with name Data Centric Security Ppt Powerpoint Presentation Styles Professional Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Data Centric Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
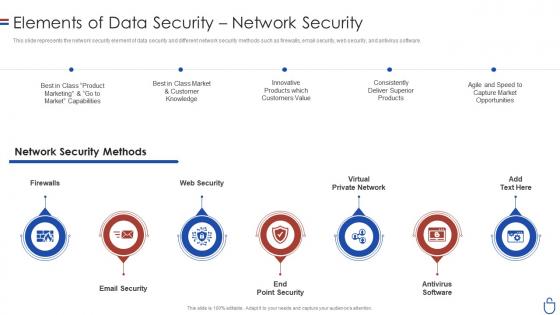 Data security it elements of data security network security
Data security it elements of data security network securityThis slide represents the network security element of data security and different network security methods such as firewalls, email security, web security, and antivirus software. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security Network Security. This template helps you present information on seven stages. You can also present information on Email Security, End Point Security, Antivirus Software, Virtual Private Network, Web Security, Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it key elements of data security ppt slides background
Data security it key elements of data security ppt slides backgroundThis slide represents the different elements of data security such as application security, network security, information security, etc. Introducing Data Security IT Key Elements Of Data Security Ppt Slides Background to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Application Security, Network Security, End User Education, Cloud Security, Operational Security, Disaster Recovery Planning, Information Security, using this template. Grab it now to reap its full benefits.
-
 Checklist To Implement Cloud Security In Business Cloud Data Protection
Checklist To Implement Cloud Security In Business Cloud Data ProtectionThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Checklist To Implement Cloud Security In Business Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Logging And Monitoring, Networking, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Different Types Of Network Security For Preventing Data Safely
Different Types Of Network Security For Preventing Data SafelyThis slide showcases various types of network security. The main purpose of this template is to ensure organizational data safety from any kind of threats. This includes firewall, remote access VPN, Network segmentation, email security, etc. Presenting our set of slides with Different Types Of Network Security For Preventing Data Safely. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Segmentation, Data Loss Prevention.
-
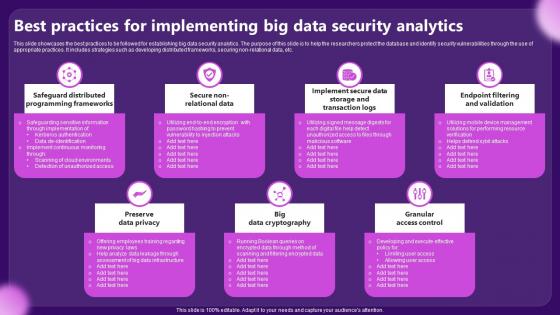 Best Practices For Implementing Big Data Security Analytics
Best Practices For Implementing Big Data Security AnalyticsThis slide showcases the best practices to be followed for establishing big data security analytics. The purpose of this slide is to help the researchers protect the database and identify security vulnerabilities through the use of appropriate practices. It includes strategies such as developing distributed frameworks, securing non relational data, etc. Presenting our set of slides with Best Practices For Implementing Big Data Security Analytics. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preserve Data Privacy, Granular Access Control.
-
 Timeline For Cloud Data Security Implementation Cloud Data Encryption
Timeline For Cloud Data Security Implementation Cloud Data EncryptionThis slide represents the timeline to implement cloud data encryption in an organization. The main components included are determine sensitive data and required encryption technique, choose a cloud service provider, implement encryption solution in cloud, etc. Introducing Timeline For Cloud Data Security Implementation Cloud Data Encryption to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Test Encryption Solutions, Implement Encryptions Solution, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security
Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data SecurityThis slide discusses the features of utility tokenization in data security. The purpose of this slide is to showcase the characteristics of utility tokenization which include service provided to user, purpose, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security. This template helps you present information on seven stages. You can also present information on Utility Tokenization, Data Security, Platforms Economic Activity, Blockchain Powered Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Role Of Visualization Security For Understanding Complex Data
Role Of Visualization Security For Understanding Complex DataThis slides showcase ways of simplifying data through visualization security. The main purpose of this template is to showcase ways in which data can be protected and gain insights from customers. This includes simplifying complex data, identification trends, real time monitoring, etc. Presenting our set of slides with Role Of Visualization Security For Understanding Complex Data. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Simplifying Complex, Identification Trends, Driving Innovation.



