Powerpoint Templates and Google slides for Data Secure
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Computer system security prepare data backup for sensitive information
Computer system security prepare data backup for sensitive informationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Introducing Computer System Security Prepare Data Backup For Sensitive Information to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Prepare Data Backup For Sensitive Information, using this template. Grab it now to reap its full benefits.
-
 Computer system security detail impact computer security plan can reduce the risk of data breach in organization
Computer system security detail impact computer security plan can reduce the risk of data breach in organizationThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Present the topic in a bit more detail with this Computer System Security Detail Impact Computer Security Plan Can Reduce The Risk Of Data Breach In Organization. Use it as a tool for discussion and navigation on System Misconfiguration, Network Intrusion, Automated Information Exfiltration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it assessment matrix of cyber risks ppt slides outline
Data security it assessment matrix of cyber risks ppt slides outlineThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Present the topic in a bit more detail with this Data Security IT Assessment Matrix Of Cyber Risks Ppt Slides Outline. Use it as a tool for discussion and navigation on Systems Involved, Owner Tenant, Mobile, Web Applications, Health Care. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it best practices for cloud security ppt slides portfolio
Data security it best practices for cloud security ppt slides portfolioThis slide represents the best practices for cloud security, such as the shared responsibility model, operations management, building controls, and processes and data encryption. Deliver an outstanding presentation on the topic using this Data Security IT Best Practices For Cloud Security Ppt Slides Portfolio. Dispense information and present a thorough explanation of Operations Management, Building Controls And Processes, Data Encryption, Security And Compliance Monitoring using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data security it circular diagram ppt slides show
Data security it circular diagram ppt slides showIntroducing Data Security IT Circular Diagram Ppt Slides Show to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Circular Diagram, using this template. Grab it now to reap its full benefits.
-
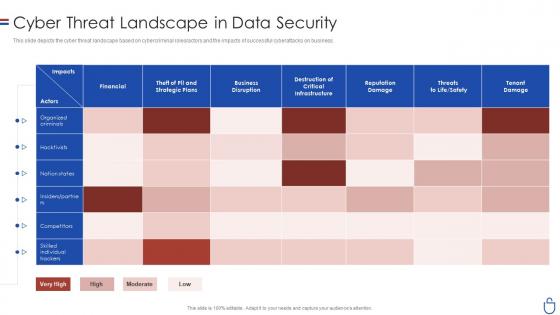 Data security it cyber threat landscape in data security
Data security it cyber threat landscape in data securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Data Security IT Cyber Threat Landscape In Data Security. Use it as a tool for discussion and navigation on Financial, Business Disruption, Reputation Damage, Tenant Damage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
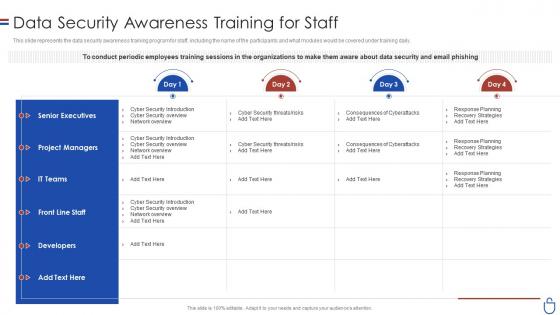 Data security it data security awareness training for staff
Data security it data security awareness training for staffThis slide represents the data security awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Present the topic in a bit more detail with this Data Security IT Data Security Awareness Training For Staff. Use it as a tool for discussion and navigation on Senior Executives, Project Managers, IT Teams, Developers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it elements of data security cloud security
Data security it elements of data security cloud securityThis slide defines the cloud security element of data security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security Cloud Security. This template helps you present information on seven stages. You can also present information on Data Breaches, Malware Injections, Distributed Denial Service Ddos, Malicious Insiders, Account Hijacking, Advanced Persistent Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
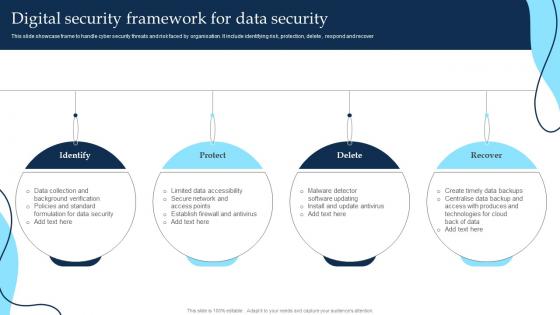 Digital Security Framework For Data Security
Digital Security Framework For Data SecurityThis slide showcase frame to handle cyber security threats and risk faced by organisation. It include identifying risk, protection, delete, respond and recover Presenting our set of slides with Digital Security Framework For Data Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Protect, Recover.
-
 Measures To Maintain Data Security In Datafication Datafication In Data Science
Measures To Maintain Data Security In Datafication Datafication In Data ScienceThis slide talks about the measures to keep data secure in datafication, including legal requirements, technical measures and business practices, containing marketing campaigns, sales operations and customer service. The technical measures include encryption, firewalls, and access controls.Introducing Measures To Maintain Data Security In Datafication Datafication In Data Science to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Legal Requirements, Technical Measures, Business Practices, using this template. Grab it now to reap its full benefits.
-
 Importance Data Security In Powerpoint And Google Slides Cpb
Importance Data Security In Powerpoint And Google Slides CpbPresenting our Importance Data Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Importance Data Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data Breaches
Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data BreachesThis slide represents 30-60-90 plan to protect companies and their employees from data breach attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data Breaches. This template helps you present information on three stages. You can also present information on Strengthen Access Controls, Implement Continuous Monitoring, Implement Data Encryption, Continue Employee Awareness Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 On Ramp Option 2 Applications And Data Zero Trust Security Model
On Ramp Option 2 Applications And Data Zero Trust Security ModelThis slide describes the second on-ramp option, which is the applications and data of ZTNA implementation. The purpose of this slide is to give an overview of practices and technologies used in this approach, such as data classification, data loss prevention, authentication and authorization of microservices, container security, etc. Deliver an outstanding presentation on the topic using this On Ramp Option 2 Applications And Data Zero Trust Security Model. Dispense information and present a thorough explanation of Authentication, Authorization, Microservices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Datafication Of HR Measures To Maintain Data Security In Datafication
Datafication Of HR Measures To Maintain Data Security In DataficationThis slide talks about the measures to keep data secure in datafication, including legal requirements, technical measures and business practices, containing marketing campaigns, sales operations and customer service. The technical measures include encryption, firewalls, and access controls. Increase audience engagement and knowledge by dispensing information using Datafication Of HR Measures To Maintain Data Security In Datafication. This template helps you present information on four stages. You can also present information on Legal Requirements, Technical Measures, Business Practices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Datafication Framework Measures To Maintain Data Security In Datafication
Datafication Framework Measures To Maintain Data Security In DataficationThis slide talks about the measures to keep data secure in datafication, including legal requirements, technical measures and business practices, containing marketing campaigns, sales operations and customer service. The technical measures include encryption, firewalls, and access controls. Introducing Datafication Framework Measures To Maintain Data Security In Datafication to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Legal Requirements, Technical Measures, Business Practices, using this template. Grab it now to reap its full benefits.
-
 Data Breaches Cyber Security In Powerpoint And Google Slides Cpb
Data Breaches Cyber Security In Powerpoint And Google Slides CpbPresenting our Data Breaches Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Data Breaches Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Plan Useful Data Backup Schedule Improving Cyber Security Risks Management
Plan Useful Data Backup Schedule Improving Cyber Security Risks ManagementThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Present the topic in a bit more detail with this Plan Useful Data Backup Schedule Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Incremental Backup, Plan Useful, Data Backup Schedule. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Strategies To Secure Business Data
Key Strategies To Secure Business DataThis slide showcase strategies that can be used for securing cyberattacks and target organizational data security and access. It includes updating devices, secure iot technology, track cloud storage, train employees and secure network access. Introducing our premium set of slides with Key Strategies To Secure Business Data. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Updated Devices, Track Cloud Storage, Train Employees. So download instantly and tailor it with your information.
-
 Cryptographic Algorithms Used In Data Security Cloud Cryptography
Cryptographic Algorithms Used In Data Security Cloud CryptographyThis slide talks about algorithms used for implementing cryptography in data security. The purpose of this slide is to explain the different implementation steps. The techniques discussed are RSA Rivest, Shamir, Adleman cryptographic algorithm and Data Encryption Standard algorithm. Deliver an outstanding presentation on the topic using this Cryptographic Algorithms Used In Data Security Cloud Cryptography. Dispense information and present a thorough explanation of Cryptographic, Algorithms, Data Encryption Standard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Security In Cloud Computing Architecture Cloud Cryptography
Data Security In Cloud Computing Architecture Cloud CryptographyThis slide talks about the key components of working of a cloud cryptography system. The purpose of this slide is to explain the main steps involved in functioning of cloud cryptography. The techniques explained are data-in-transit, data-at-rest and legal and regulatory issues. Present the topic in a bit more detail with this Data Security In Cloud Computing Architecture Cloud Cryptography. Use it as a tool for discussion and navigation on Architecture, Cryptographic, Data Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Network Security Challenges And Solution For Protecting Data
Network Security Challenges And Solution For Protecting DataThis slide showcase solution and challenges for network security. The main purpose for this template is to save company data from getting into hands of rival businesses. This includes data theft, insider threat, password attack, etc. Presenting our set of slides with Network Security Challenges And Solution For Protecting Data. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Challenges, Solution.
-
 Network Security Framework For Preventing Data Theft
Network Security Framework For Preventing Data TheftThis slide showcase model of network security. The main purpose of this template is preventing company confidential data from getting in the hands of rival companies. This includes third party, sender, and receiver. Introducing our Network Security Framework For Preventing Data Theft set of slides. The topics discussed in these slides are Message Modification, Confidential Information. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Network Security Tips For Protecting Important Data
Network Security Tips For Protecting Important DataThese slide showcase ways of protecting network security. The main purpose of this template is how to keep office data safe from any kind of theft, this includes careful grant access, strong password, secure servers, text security. Presenting our set of slides with Network Security Tips For Protecting Important Data. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Careful Grant Access, Strong Password.
-
 Data Security Industry In Powerpoint And Google Slides Cpb
Data Security Industry In Powerpoint And Google Slides CpbPresenting Data Security Industry In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Data Security Industry. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Understanding Security Risk Related With Dark Data Dark Data And Its Utilization
Understanding Security Risk Related With Dark Data Dark Data And Its UtilizationThis slide focuses on the security risks associated with dark data. Some of the risks associated with dark data include vulnerability to hacking, negative impact on the business, and an increased workload for IT teams, etc. Introducing Understanding Security Risk Related With Dark Data Dark Data And Its Utilization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability To Hacking, Negative Impact On Business, Increased Workload For IT Teams, using this template. Grab it now to reap its full benefits.
-
 Big Data Security Analytics Ppt Powerpoint Presentation Infographics Format
Big Data Security Analytics Ppt Powerpoint Presentation Infographics FormatPresenting our well structured Big Data Security Analytics Ppt Powerpoint Presentation Infographics Format. The topics discussed in this slide are Big Data Security Analytics.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
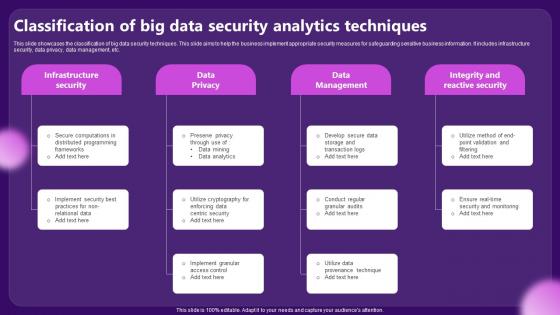 Classification Of Big Data Security Analytics Techniques
Classification Of Big Data Security Analytics TechniquesThis slide showcases the classification of big data security techniques. This slide aims to help the business implement appropriate security measures for safeguarding sensitive business information. It includes infrastructure security, data privacy, data management, etc. Presenting our set of slides with Classification Of Big Data Security Analytics Techniques. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure Security, Data Management.
-
 Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V
Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Increase audience engagement and knowledge by dispensing information using Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V. This template helps you present information on three stages. You can also present information on Authentication, Encryption, Firewall using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Security Providers In Powerpoint And Google Slides Cpb
Data Security Providers In Powerpoint And Google Slides CpbPresenting our Data Security Providers In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Data Security Providers This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Timeline For Cloud Data Security Implementation Cloud Data Encryption
Timeline For Cloud Data Security Implementation Cloud Data EncryptionThis slide represents the timeline to implement cloud data encryption in an organization. The main components included are determine sensitive data and required encryption technique, choose a cloud service provider, implement encryption solution in cloud, etc. Introducing Timeline For Cloud Data Security Implementation Cloud Data Encryption to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Test Encryption Solutions, Implement Encryptions Solution, using this template. Grab it now to reap its full benefits.
-
 IoT Cyber Security Technologies For Data Improving IoT Device Cybersecurity IoT SS
IoT Cyber Security Technologies For Data Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase various types of Internet of Things IoT security technologies which can assist companies in safeguarding customer data. Blockchain, IoT security analytics, Zero Trust Architecture, and Edge Computing are the most trending technologies which are outlined in slide. Increase audience engagement and knowledge by dispensing information using IoT Cyber Security Technologies For Data Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Devices, Architecture, Computing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLP
Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLPThis slide describes the difference between Cloud Access Security Broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Comparison Between CASB And Data Loss Prevention DLP. Dispense information and present a thorough explanation of Content Inspection, Data Classification, Encryption, Access Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Pillar Data Security Ppt Icon Backgrounds
Cloud Access Security Broker CASB V2 Pillar Data Security Ppt Icon BackgroundsThis slide talks about the data security pillar of the Cloud Access Security Broker pillar. This slide highlights how CASB data security can help organizations improve their IT requirements and business operations and detect security breaches before they happen. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pillar Data Security Ppt Icon Backgrounds. This template helps you present information on four stages. You can also present information on Document Fingerprinting, Data Security Pillar, Cloud Access Security Broker Pillar using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
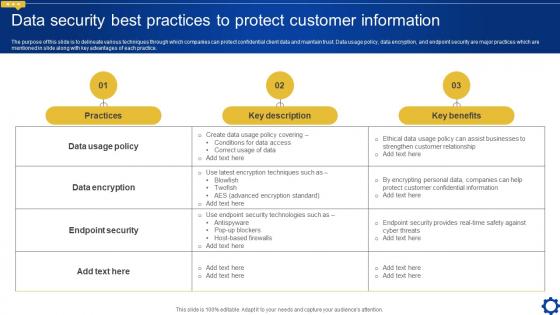 Data Security Best Practices To Protect Customer Creating Personalized Marketing Messages MKT SS V
Data Security Best Practices To Protect Customer Creating Personalized Marketing Messages MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Present the topic in a bit more detail with this Data Security Best Practices To Protect Customer Creating Personalized Marketing Messages MKT SS V. Use it as a tool for discussion and navigation on Practices, Key Description, Key Benefits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impacts Of Cyber Security Data Compliance
Impacts Of Cyber Security Data ComplianceThis slide shows benefits of cyber security compliance which helps in aiming to protect sensitive data and maintain the integrity of information systems. It further includes benefits such as strengthening data protection etc. Presenting our set of slides with Impacts Of Cyber Security Data Compliance. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strengthening Data Protection, Regulatory Compliance.
-
 Components Of Virtual Infrastructure For Effective Data Management And Security
Components Of Virtual Infrastructure For Effective Data Management And SecurityThis slide represents key components of virtual infrastructure that help businesses with data security and disaster management. It includes various components such as virtualized computing, virtualized storage, management solutions, and virtualized security. Introducing our premium set of slides with Components Of Virtual Infrastructure For Effective Data Management And Security. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Virtualized Compute, Virtualized Networking Security, Virtualized Storage. So download instantly and tailor it with your information.
-
 Information Security Management Controls To Enhance Data Integrity
Information Security Management Controls To Enhance Data IntegrityThis slide represents controls that help businesses to manage information security effectively from data breaches. It includes controls such as physical control, access control, procedural control, etc, Presenting our well structured Information Security Management Controls To Enhance Data Integrity. The topics discussed in this slide are Physical Control, Access Control, Procedural Control. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Security Management Framework For Organization Data Protection
Information Security Management Framework For Organization Data ProtectionThis slide represents framework that assists organizations in developing information security management to enhance data protection. This model sets information security at tactical level, strategic level, and operational level. Introducing our Information Security Management Framework For Organization Data Protection set of slides. The topics discussed in these slides are Information Security Plan, Consciousness Management, Risk Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process
Devsecops Best Practices For Secure Environment And Data Security For Devsecops ProcessThis slide discusses the environment and data security for DevSecOps. The purpose of this slide is to highlight the process, including standardizing and automating the environment, centralizing user identity and access control, isolating containers for security, and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process. Use it as a tool for discussion and navigation on Standardize And Automate Environment, Isolate Containers For Security, Encrypt Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches
Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data BreachesThis slide represents 30-60-90 plan to protect companies and their employees from data breach attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches. This template helps you present information on three stages. You can also present information on Strengthen Access Controls, Conduct Regular Security Audits, Provide Data Security Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Breach Response Plan Responsibility Matrix For Secure Operations Phase
Data Breach Response Plan Responsibility Matrix For Secure Operations PhaseThis slide shows the matrix to assign multiple responsibilities to the different teams for the secure operations phase of data breach response plan. The responsibilities include secure physical area, contact search engines, document investigation, etc. Present the topic in a bit more detail with this Data Breach Response Plan Responsibility Matrix For Secure Operations Phase. Use it as a tool for discussion and navigation on Secure Physical Area, Contact Search Engines, Document Investigation, Responsibility Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Response Plan Security Breach Events Tracking Dashboard
Data Breach Response Plan Security Breach Events Tracking DashboardThis slide represents the dashboard to track data breach attacks. The purpose of this slide is to provide a graphical representation of cyber attacks that occurred in a specific period. It also depicts the overview of different types of attacks. Present the topic in a bit more detail with this Data Breach Response Plan Security Breach Events Tracking Dashboard. Use it as a tool for discussion and navigation on Security Breach Events, Tracking Dashboard, Track Data Breach Attacks, Inspection Of Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Highlighting Cyber Security Unawareness Among Employees Cyber Risk Assessment
Data Highlighting Cyber Security Unawareness Among Employees Cyber Risk AssessmentThe following slide depicts some figures to analyze the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Introducing Data Highlighting Cyber Security Unawareness Among Employees Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Highlighting, Cyber Security Unawareness using this template. Grab it now to reap its full benefits.
-
 About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It
About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role and functionality of IPsec Internet Protocol Security in securing connections between devices. This slide also outlines the uses of IPsec such as protecting data during transmission over open networks, use in building VPNs, etc. Deliver an outstanding presentation on the topic using this About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Overview, Protocol Security, Destination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
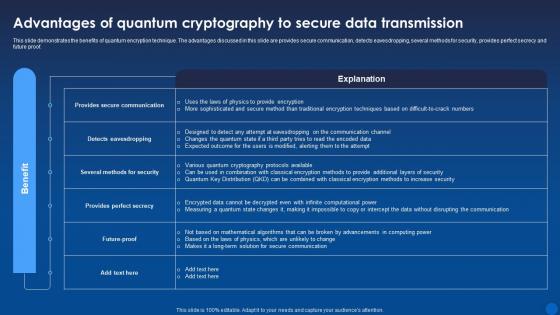 Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It
Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of quantum encryption technique. The advantages discussed in this slide are provides secure communication, detects eavesdropping, several methods for security, provides perfect secrecy and future proof. Present the topic in a bit more detail with this Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Quantum, Cryptography, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Applications Secure Email Content Encryption For Data Privacy In Digital Age It
Applications Secure Email Content Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the importance of email encryption in protecting the privacy and security of email communications. The key components of secure email transfer are public key, private key, encryption, decryption, etc. Present the topic in a bit more detail with this Applications Secure Email Content Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Applications, Encryption, Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
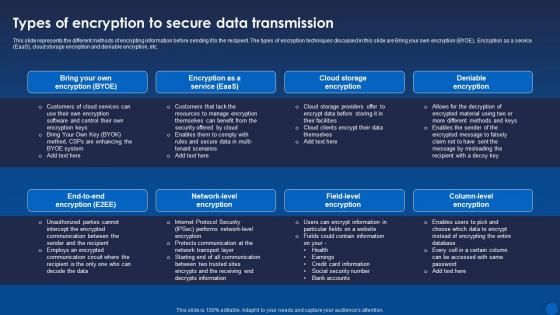 Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It
Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age ItThis slide represents the different methods of encrypting information before sending it to the recipient. The types of encryption techniques discussed in this slide are Bring your own encryption BYOE, Encryption as a service EaaS, cloud storage encryption and deniable encryption, etc. Present the topic in a bit more detail with this Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Transmission, Encryption, Deniable Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Security Crime Prevention Management Flowchart
Data Security Crime Prevention Management FlowchartThis slide depicts the internal data security crime prevention team. Its purpose is to understand duties of the heads to prevent internal crimes. This slide includes data security, technical security, crime prevention, security support, etc. Introducing our Data Security Crime Prevention Management Flowchart set of slides. The topics discussed in these slides are Security Director, Prevention Head, Security Support This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Saas Software Architectural Framework For Data Security
Saas Software Architectural Framework For Data SecurityThis slide demonstrates SaaS software architectural framework for contributing to design, development and operation of scalable and efficient cloud based applications. It includes basis such as autonomous management, user interface, operational processes, application layer, etc. Introducing our Saas Software Architectural Framework For Data Security set of slides. The topics discussed in these slides are Autonomous Management, Service Provider, Subscriber This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS
Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SSThis slide analyses the need of implementing data security initiatives to address key customer data challenges in retail industry. It also mentions types of customer data collected such as account, location, browsing, and profile. Deliver an outstanding presentation on the topic using this Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS Dispense information and present a thorough explanation of Customer Trust, Sensitive Information, Balancing Personalization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker Pillar Data Security Next Generation CASB
Cloud Access Security Broker Pillar Data Security Next Generation CASBThis slide talks about the data security pillar of the cloud access security broker pillar. This slide highlights how CASB data security can help organizations improve their IT requirements and business operations and detect security breaches before they happen. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Pillar Data Security Next Generation CASB This template helps you present information on five stages. You can also present information on Complex Cloud, Sensitive Material, Risk Assessments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process
Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management ProcessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process. This template helps you present information on five stages. You can also present information on Malware Infection, Systems With Passwords, Employees Feels, Allow Official Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS
Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SSThis slide showcases avoiding unnecessary resources on internet of things IoT devices, helping developers avoid transmission and storage costs. It provides details about data classification, compliance, etc. Deliver an outstanding presentation on the topic using this Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Privacy And Compliance Considerations, Data Privacy And Compliance, Data Access Storage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Smart Contracts Implementation Plan Statistical Data Of Security Breach Incident
Smart Contracts Implementation Plan Statistical Data Of Security Breach IncidentThis slide summarizes the security breach incident across different organizational departments, such as sales, IT department, finance, marketing, operations, etc. Present the topic in a bit more detail with this Smart Contracts Implementation Plan Statistical Data Of Security Breach Incident. Use it as a tool for discussion and navigation on Statistical Data, Security Breach Incident, Finance, Marketing, Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tokenization For Improved Data Security Tokenization Performance Recording And Monitoring Dashboard
Tokenization For Improved Data Security Tokenization Performance Recording And Monitoring DashboardThis slide showcases the performance tracking dashboard for tokenization. The purpose of this slide is to highlight the performance of tokenization by including components such as key management, crypto, tokenize, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Tokenization Performance Recording And Monitoring Dashboard. Use it as a tool for discussion and navigation on Tokenization Performance Recording, Monitoring Dashboard, Tracking Dashboard, Key Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tokenization For Improved Data Security Training Budget For Tokenization In Data Security
Tokenization For Improved Data Security Training Budget For Tokenization In Data SecurityThis slide showcases the breakdown cost for performing tokenization for data security. The purpose of this slide is to showcase the training cost breakdown for different components such as instructor, training cost, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Training Budget For Tokenization In Data Security. Use it as a tool for discussion and navigation on Training Budget, Tokenization In Data Security, Training Cost, Performing Tokenization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security For Big Data Analytics Trend
Cyber Security For Big Data Analytics TrendThis slide represents trends for big data analytics in cybersecurity. This includes bar graph showcasing rise of big data volume in industries for analysis along with key takeaways. Introducing our Cyber Security For Big Data Analytics Trend set of slides. The topics discussed in these slides are Cyber Security, Big Data Analytics Trend, Big Data Analytics In Cybersecurity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
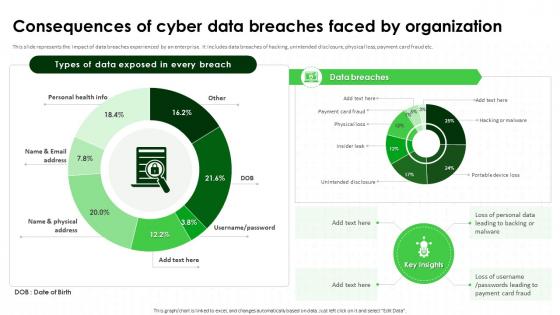 Consequences Of Cyber Data Breaches Faced IT Security Awareness Training Cybersecurity SS
Consequences Of Cyber Data Breaches Faced IT Security Awareness Training Cybersecurity SSThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Consequences Of Cyber Data Breaches Faced IT Security Awareness Training Cybersecurity SS. Use it as a tool for discussion and navigation on Consequences Of Cyber Data Breaches, Unintended Disclosure, Physical Loss, Payment Card Fraud. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Security Awareness Training Statistical Data Highlighting It Security Unawareness Cybersecurity SS
IT Security Awareness Training Statistical Data Highlighting It Security Unawareness Cybersecurity SSThis slide represents statistical insights highlighting importance of implementing strategy adopted by IT teams and security professionals for preventing and mitigating security risks. Present the topic in a bit more detail with this IT Security Awareness Training Statistical Data Highlighting It Security Unawareness Cybersecurity SS. Use it as a tool for discussion and navigation on Implementing Strategy, Security Professionals, Mitigating Security Risks. This template is free to edit as deemed fit for your organization. Therefore download it now.




