Powerpoint Templates and Google slides for Data Secure
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Lock piece for company data security ppt slides
Lock piece for company data security ppt slidesPresenting lock piece for company data security ppt slides. This is a lock piece for company data security ppt slides. This is a two stage process. The stages in this process are security.
-
 Data and business network security techniques ppt slides
Data and business network security techniques ppt slidesPresenting data and business network security techniques ppt slides. This is a data and business network security techniques ppt slides. This is a one stage process. The stages in this process are security.
-
 Six folders for data security analysis ppt slides
Six folders for data security analysis ppt slidesPresenting six folders for data security analysis ppt slides. This is a six folders for data security analysis ppt slides. This is a six stage process. The stages in this process are big data analytics, security.
-
 Usb security shield and tools for data safety ppt slides
Usb security shield and tools for data safety ppt slidesPresenting usb security shield and tools for data safety ppt slides. This is a usb security shield and tools for data safety ppt slides. This is a two stage process. The stages in this process are security.
-
 Securing business data powerpoint slide deck template
Securing business data powerpoint slide deck templatePresenting securing business data powerpoint slide deck template. This is a securing business data powerpoint slide deck template. This is a one stage process. The stages in this process are identify data, secure access, back up to the cloud, encrypt your data, control downloads.
-
 Data management and security powerpoint guide
Data management and security powerpoint guidePresenting data management and security powerpoint guide. This is a data management and security powerpoint guide. This is a two stage process. The stages in this process are un breakable encryption, accept and manage encryption.
-
 Data security strategies powerpoint ideas
Data security strategies powerpoint ideasIntroducing data security strategies PPT design. Fully regulated PowerPoint template quite reasonable for the management professionals and business specialists. Extensive scope for reviving the dummy data and can add company logo, trademark etc. Reconvert able background PPT images, subject matter, designs, context etc. according to need. Versant with all Google Slides and other system applications. Can be easily projected over wide screen with exceptional picture quality.
-
 Data share points and security powerpoint images
Data share points and security powerpoint imagesPresenting, data share points and security PowerPoint images. Other than providing you with an excellent experience this PPT slide can be used by professionals for discussing financial and business security using a flow chart. You can easily ungroup the elements shown in the diagram and according to your liking. Download this slide and insert your company's logo for a professional look and experience it in full screen version. Include your company logo here in the PPT to personalize further. We have shown a high-quality design which does not deteriorate in quality when edited or projected on a widescreen.
-
 Digital data security powerpoint slide
Digital data security powerpoint slidePresenting digital data security PowerPoint slide. Slideshow is fully editable. You can change all the design components and customize is according to your business requirements. Include business related data into text place holders provided in PPT design. Complete error free downloading is available. Download the design into JPEG and PDF formats. PPT is fully supported on Google Slides, MS PowerPoint and other compatible software.
-
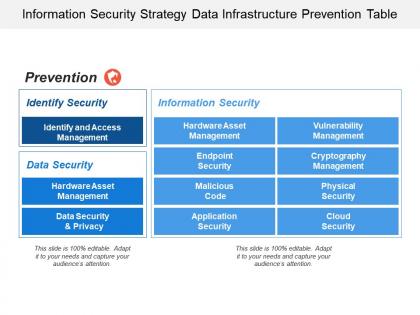 Information security strategy data infrastructure prevention table
Information security strategy data infrastructure prevention tablePresenting this set of slides with name - Information Security Strategy Data Infrastructure Prevention Table. This is a two stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
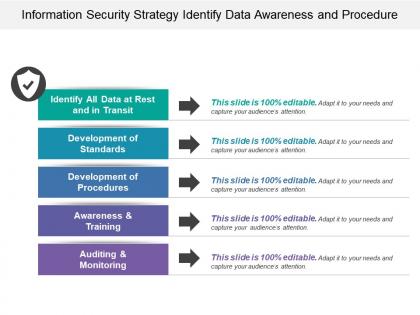 Information security strategy identify data awareness and procedure
Information security strategy identify data awareness and procedurePresenting this set of slides with name - Information Security Strategy Identify Data Awareness And Procedure. This is a five stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
 Half yearly data strategy govern integrate store security swim lane
Half yearly data strategy govern integrate store security swim lanePresenting this set of slides with name - Half Yearly Data Strategy Govern Integrate Store Security Swim Lane. This is a two stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
 Quarterly data strategy govern integrate store security swim lane
Quarterly data strategy govern integrate store security swim lanePresenting this set of slides with name - Quarterly Data Strategy Govern Integrate Store Security Swim Lane. This is a four stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
 Six months data strategy govern integrate store security swim lane
Six months data strategy govern integrate store security swim lanePresenting this set of slides with name - Six Months Data Strategy Govern Integrate Store Security Swim Lane. This is a six stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
 Three months data strategy govern integrate store security swim lane
Three months data strategy govern integrate store security swim lanePresenting this set of slides with name - Three Months Data Strategy Govern Integrate Store Security Swim Lane. This is a three stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
 Yearly data strategy govern integrate store security swim lane
Yearly data strategy govern integrate store security swim lanePresenting this set of slides with name - Yearly Data Strategy Govern Integrate Store Security Swim Lane. This is a five stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
 Firewall setup for business data security icon
Firewall setup for business data security iconPresenting this set of slides with name Firewall Setup For Business Data Security Icon. This is a three stage process. The stages in this process are Firewall Setup, Business Data, Security Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cloud computing data protection binary security codes
Cloud computing data protection binary security codesPresenting this set of slides with name Cloud Computing Data Protection Binary Security Codes. This is a three stage process. The stages in this process are Cloud Computing Data Protection Binary Security Codes. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Online information security system icon for protecting user data
Online information security system icon for protecting user dataPresenting this set of slides with name Online Information Security System Icon For Protecting User Data. This is a one stage process. The stages in this process are Online Information, Security System, Icon Protecting, User Data. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Data centre layout icon with security key
Data centre layout icon with security keyPresenting this set of slides with name Data Centre Layout Icon With Security Key. This is a three stage process. The stages in this process are Data Centre Layout Icon With Security Key. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Network security technology for data privacy
Network security technology for data privacyPresenting this set of slides with name Network Security Technology For Data Privacy. This is a two stage process. The stages in this process are Network Security Technology For Data Privacy. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Woman using vpn technology for data security
Woman using vpn technology for data securityPresenting this set of slides with name Woman Using VPN Technology For Data Security. This is a three stage process. The stages in this process are Woman Using VPN Technology For Data Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 World wide secure data transmission icon
World wide secure data transmission iconPresenting this set of slides with name World Wide Secure Data Transmission Icon. This is a two stage process. The stages in this process are World Wide Secure Data Transmission Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cloud security and data protection icon
Cloud security and data protection iconPresenting this set of slides with name Cloud Security And Data Protection Icon. This is a one stage process. The stage in this process is Cloud Security And Data Protection Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Company cloud data security icon with digital lock
Company cloud data security icon with digital lockPresenting this set of slides with name Company Cloud Data Security Icon With Digital Lock. This is a three stage process. The stages in this process are Company Cloud Data Security Icon With Digital Lock. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon for cloud data security and protection
Icon for cloud data security and protectionPresenting this set of slides with name Icon For Cloud Data Security And Protection. This is a four stage process. The stages in this process are Icon For Cloud Data Security And Protection. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon representing cloud server data security
Icon representing cloud server data securityPresenting this set of slides with name Icon Representing Cloud Server Data Security. This is a one stage process. The stage in this process is Icon Representing Cloud Server Data Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Security firewall icon for cloud data protection
Security firewall icon for cloud data protectionPresenting this set of slides with name Security Firewall Icon For Cloud Data Protection. This is a four stage process. The stages in this process are Security Firewall Icon For Cloud Data Protection. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Verified security icon for company cloud data
Verified security icon for company cloud dataPresenting this set of slides with name Verified Security Icon For Company Cloud Data. This is a four stage process. The stages in this process are Verified Security Icon For Company Cloud Data. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Connected data network through lock depicting cyber security
Connected data network through lock depicting cyber securityPresenting this set of slides with name Connected Data Network Through Lock Depicting Cyber Security. This is a one stage process. The stages in this process are Connected Data Network Through Lock Depicting Cyber Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Data security it security of employees devices ppt slides brochure
Data security it security of employees devices ppt slides brochureThis slide depicts that the security of employees hardware or devices is also essential while applying the cyber security model. Introducing Data Security IT Security Of Employees Devices Ppt Slides Brochure to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Intrusions, Project, Peripheral Devices, using this template. Grab it now to reap its full benefits.
-
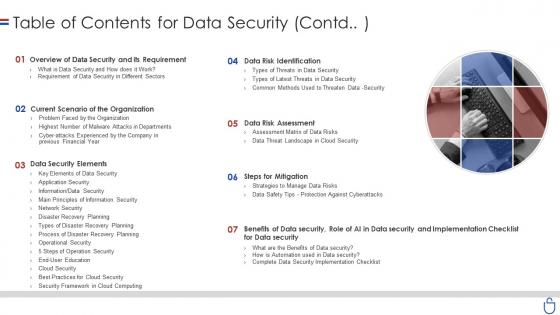 Data security it table of contents for data security contd
Data security it table of contents for data security contdIncrease audience engagement and knowledge by dispensing information using Data Security IT Table Of Contents For Data Security Contd. This template helps you present information on seven stages. You can also present information on Overview Data Security And Its Requirement, Current Scenario Organization, Data Security Elements, Steps Mitigation, Data Risk Assessment, Data Risk Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
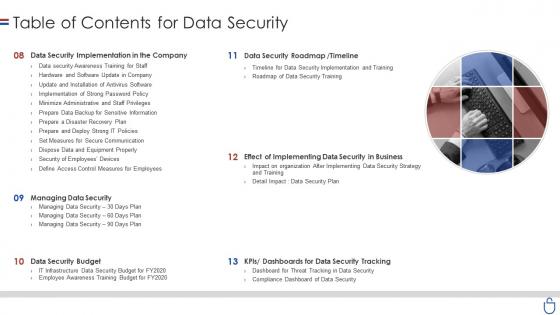 Data security it table of contents for data security ppt slides display
Data security it table of contents for data security ppt slides displayIntroducing Data Security IT Table Of Contents For Data Security Ppt Slides Display to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Data Security Implementation Company, Data Security Roadmap, Timeline, Managing Data Security, Data Security Budget, Dashboards Data Security Tracking, using this template. Grab it now to reap its full benefits.
-
 Data security it elements of data security cloud security
Data security it elements of data security cloud securityThis slide defines the cloud security element of data security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security Cloud Security. This template helps you present information on seven stages. You can also present information on Data Breaches, Malware Injections, Distributed Denial Service Ddos, Malicious Insiders, Account Hijacking, Advanced Persistent Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it main steps of operational security
Data security it main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Increase audience engagement and knowledge by dispensing information using Data Security IT Main Steps Of Operational Security. This template helps you present information on one stages. You can also present information on Financial Details, Product Research, Exploit Data, Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wireless security icon of cloud servers to secure data
Wireless security icon of cloud servers to secure dataPresenting our set of slides with Wireless Security Icon Of Cloud Servers To Secure Data. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Wireless Security Icon Of Cloud Servers To Secure Data.
-
 Security Program Icon For Protecting Client Data
Security Program Icon For Protecting Client DataPresenting our set of slides with name Security Program Icon For Protecting Client Data. This exhibits information on one stage of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Program Icon For Protecting Client Data.
-
 Cloud Data Protection Architecture Of Cloud Security
Cloud Data Protection Architecture Of Cloud SecurityThis slide defines the architecture of the cloud security system and how data is kept, managed, and secured based on customer and service providers responsibilities. Increase audience engagement and knowledge by dispensing information using Cloud Data Protection Architecture Of Cloud Security. This template helps you present information on two stages. You can also present information on Customer Data, Customer Responsibility, Cloud Service using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Data Protection Key Challenges In Cloud Security
Cloud Data Protection Key Challenges In Cloud SecurityThis slide describes the critical challenges in the cloud security system, such as compliance violations, access control, Daniel of service, and unsecured APIs. Introducing Cloud Data Protection Key Challenges In Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Compliance Violations, Access Control, Organizations, using this template. Grab it now to reap its full benefits.
-
 Cloud Data Protection Tools Used In Cloud Security
Cloud Data Protection Tools Used In Cloud SecurityThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud. Increase audience engagement and knowledge by dispensing information using Cloud Data Protection Tools Used In Cloud Security. This template helps you present information on one stage. You can also present information on Cloud Solutions, Security, Networks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Data Protection What Are The Downsides Of A Cloud Security
Cloud Data Protection What Are The Downsides Of A Cloud SecurityThis slide describes the downsides of the cloud security system, including loss of control over data, data loss, insider theft, and data breaches. Introducing Cloud Data Protection What Are The Downsides Of A Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Data Security, Organizations, Data Breaches, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Checklist Data Encryption Cloud Data Protection
Cloud Security Checklist Data Encryption Cloud Data ProtectionThis slide represents the importance of data encryption in cloud security and what type of data should always be encrypted through private keys. Introducing Cloud Security Checklist Data Encryption Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Data Servers, Network, Cloud, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Checklist Logging And Monitoring Cloud Data Protection
Cloud Security Checklist Logging And Monitoring Cloud Data ProtectionThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, Network, Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Checklist Networking Cloud Data Protection
Cloud Security Checklist Networking Cloud Data ProtectionThis slide defines the importance of network security under cloud security. It also shows how data should transfer over a network to protect it from malicious attacks. Introducing Cloud Security Checklist Networking Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Ensure Security, Network, Critical Data, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Checklist Security Patches And Updates Cloud Data Protection
Cloud Security Checklist Security Patches And Updates Cloud Data ProtectionThis slide depicts the importance of security patches and timely updates of security technologies. It also shows how it is crucial to scan systems, servers, and frameworks regularly. Introducing Cloud Security Checklist Security Patches And Updates Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Technologies, Organization, Servers, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Compliance Violations Cloud Data Protection
Cloud Security Threats Compliance Violations Cloud Data ProtectionThis slide depicts the value of compliance violations threat of cloud security in a business and how fast an organization can switch to a non-compliance state. Introducing Cloud Security Threats Compliance Violations Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Authentication Procedures, Business, Organizations, using this template. Grab it now to reap its full benefits.
-
 How Does Cloud Security Work Data Security Cloud Data Protection
How Does Cloud Security Work Data Security Cloud Data ProtectionThis slide represents the data security under the cloud security work process, and it also shows the various factors that cover data security. Introducing How Does Cloud Security Work Data Security Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Wireless Security, Internet Security, Application Security, Network Security, Information Security, using this template. Grab it now to reap its full benefits.
-
 How To Manage Cloud Security Cloud Data Protection
How To Manage Cloud Security Cloud Data ProtectionThis slide represents how data is managed in a cloud security system and what service providers and organizations take security measures. Introducing How To Manage Cloud Security Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Business Procedures, Enforcing Privacy Policies, Compliance Is Effective, using this template. Grab it now to reap its full benefits.
-
 Pillars Of Cloud Security Identity Security Cloud Data Protection
Pillars Of Cloud Security Identity Security Cloud Data ProtectionThis slide depicts the identity security pillar of cloud security. It also shows how it could be beneficial to protect data from loss. Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Identity Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Pillars Of Cloud Security Identity Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Pillars Of Cloud Security Network Security Cloud Data Protection
Pillars Of Cloud Security Network Security Cloud Data ProtectionThis slide defines the network security pillar of cloud security and what precautions are taken to protect networks from attacks. Introducing Pillars Of Cloud Security Network Security Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Micro Segmentation, Operations, Security, using this template. Grab it now to reap its full benefits.
-
 What Are The Benefits Of A Cloud Security System Cloud Data Protection
What Are The Benefits Of A Cloud Security System Cloud Data ProtectionThis slide represents the benefits of a cloud security system, such as efficient recovery, openness, no hardware requirement, DDOS protection, and data security. Introducing What Are The Benefits Of A Cloud Security System Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Efficient Recovery, Efficient Data Security, Business Capacity, using this template. Grab it now to reap its full benefits.
-
 What Is Cloud Security Cloud Data Protection
What Is Cloud Security Cloud Data ProtectionThis slide depicts the meaning of cloud security, and parties involve in a cloud security framework, such as customers and service providers. Increase audience engagement and knowledge by dispensing information using What Is Cloud Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Organizations, Cloud Security, Ensure Business, Threats, Cloud Computing Systems using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 3 Step Cyber Security Plan For Data Protection
3 Step Cyber Security Plan For Data ProtectionThis slide signifies the three stage cyber security program to improve data protection. It covers information about steps like prevention, response and remediation. Presenting our set of slides with 3 Step Cyber Security Plan For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevention, Response, Remediation.
-
 Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery
Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation galleryThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Increase audience engagement and knowledge by dispensing information using Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery. This template helps you present information on two stages. You can also present information on Challenges, Solution, Data Collections using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Analyzing Cloud Based Service Offerings Best Practices To Improve Data Security
Analyzing Cloud Based Service Offerings Best Practices To Improve Data SecurityThis slide showcases various tips which can be adopted by business to enhance data security of SAAs application. It provides information regarding end to end encryption, application testing, data deletion policy and VPN. Introducing Analyzing Cloud Based Service Offerings Best Practices To Improve Data Security to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on End To End Encryption, Application Testing, Data Deletion Policy, Vpn, using this template. Grab it now to reap its full benefits.
-
 Management Of Redundant Data Understanding Security Risk Related With Dark Data
Management Of Redundant Data Understanding Security Risk Related With Dark DataThis slide focuses on the security risks associated with dark data. Some of the risks associated with dark data include vulnerability to hacking, negative impact on the business, and an increased workload for IT teams, etc. Introducing Management Of Redundant Data Understanding Security Risk Related With Dark Data to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Increased Workload For IT Teams, Negative Impact On Business, Vulnerability To Hacking, using this template. Grab it now to reap its full benefits.
-
 Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SS
Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SSThis slide major types of encryption technology, focused on improving data privacy and security of todays business. It provides details about symmetric, asymmetric, RSA, data encryption standard, etc. Introducing Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Encryption, Asymmetric Encryption, RSA Encryption, using this template. Grab it now to reap its full benefits.
-
 Endpoint Data Loss Prevention Tool Building Next Generation Endpoint Security Cybersecurity SS
Endpoint Data Loss Prevention Tool Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases endpoint data loss prevention DLP tool process. It includes stages such as identification, assistance and tracking of endpoint data.Increase audience engagement and knowledge by dispensing information using Endpoint Data Loss Prevention Tool Building Next Generation Endpoint Security Cybersecurity SS. This template helps you present information three stages. You can also present information on Identify, Assist, Track, Potential Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
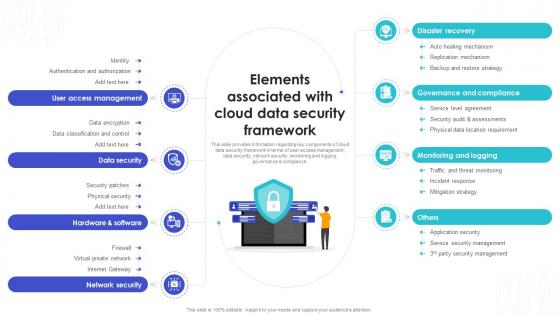 Elements Associated With Cloud Data Security Safeguarding Business With Data Loss Cybersecurity SS
Elements Associated With Cloud Data Security Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding key components of cloud data security framework in terms of user access management, data security, network security, monitoring and logging, governance and compliance.Increase audience engagement and knowledge by dispensing information using Elements Associated With Cloud Data Security Safeguarding Business With Data Loss Cybersecurity SS. This template helps you present information on eight stages. You can also present information on Disaster Recovery, User Access Management, Data Security, Network Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Phase 4 Of Dlp Success Focus On Proactive Security Safeguarding Business With Data Loss Cybersecurity SS
Phase 4 Of Dlp Success Focus On Proactive Security Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding focusing on proactive security for successful data loss prevention execution. It will include initiatives such as infiltration, exfiltration, automated protection, etc.Increase audience engagement and knowledge by dispensing information using Phase 4 Of Dlp Success Focus On Proactive Security Safeguarding Business With Data Loss Cybersecurity SS. This template helps you present information on one stages. You can also present information on Exhibited Behavior, Objective, Customization, High Risk Events using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.




