Powerpoint Templates and Google slides for Data Secure
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data security management ppt powerpoint presentation layouts slideshow cpb
Data security management ppt powerpoint presentation layouts slideshow cpbPresenting this set of slides with name - Data Security Management Ppt Powerpoint Presentation Layouts Slideshow Cpb. This is an editable three stages graphic that deals with topics like Data Security Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Data security management ppt powerpoint presentation infographics icon cpb
Data security management ppt powerpoint presentation infographics icon cpbPresenting this set of slides with name - Data Security Management Ppt Powerpoint Presentation Infographics Icon Cpb. This is an editable five stages graphic that deals with topics like Data Security Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Data flow home security system ppt powerpoint presentation infographic cpb
Data flow home security system ppt powerpoint presentation infographic cpbPresenting Data Flow Home Security System Ppt Powerpoint Presentation Infographic Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Data Flow Home Security System. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Payroll system security data protection ppt powerpoint presentation infographic template cpb
Payroll system security data protection ppt powerpoint presentation infographic template cpbPresenting our Payroll System Security Data Protection Ppt Powerpoint Presentation Infographic Template Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Payroll System Security Data Protection. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Secure offsite data storage ppt powerpoint presentation outline demonstration cpb
Secure offsite data storage ppt powerpoint presentation outline demonstration cpbPresenting Secure Offsite Data Storage Ppt Powerpoint Presentation Outline Demonstration Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secure Offsite Data Storage. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Secure exchange electronic data ppt powerpoint presentation ideas gridlines cpb
Secure exchange electronic data ppt powerpoint presentation ideas gridlines cpbPresenting our Secure Exchange Electronic Data Ppt Powerpoint Presentation Ideas Gridlines Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Secure Exchange Electronic Data. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Big data it security of information in big data
Big data it security of information in big dataThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Introducing Big Data It Security Of Information In Big Data to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Information, Companies, Professionals, using this template. Grab it now to reap its full benefits.
-
 Secure data storage cloud computings ppt powerpoint presentation example cpb
Secure data storage cloud computings ppt powerpoint presentation example cpbPresenting Secure Data Storage Cloud Computings Ppt Powerpoint Presentation Example Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secure Data Storage Cloud Computings. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 6 step process to implement data availability security
6 step process to implement data availability securityThis slide represents 6 step process to implement data availability security illustrating simplified recording, on-site maintenance and online security, training, record disposal and plan. Presenting our set of slides with 6 Step Process To Implement Data Availability Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Management, Implement, Organization.
-
 Addressing internal and external sources of threat data corporate security management
Addressing internal and external sources of threat data corporate security managementThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Introducing Addressing Internal And External Sources Of Threat Data Corporate Security Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Targeted Intelligence, Malware Intelligence, Reputation Intelligence, using this template. Grab it now to reap its full benefits.
-
 Network Security Prepare Data Backup For Sensitive Information
Network Security Prepare Data Backup For Sensitive InformationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Increase audience engagement and knowledge by dispensing information using Network Security Prepare Data Backup For Sensitive Information. This template helps you present information on three stages. You can also present information on Information, Protect, Manipulation, Service using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security Data Backup For Sensitive Information
Information Technology Security Data Backup For Sensitive InformationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Introducing Information Technology Security Data Backup For Sensitive Information to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Prepare Data Backup For Sensitive Information, using this template. Grab it now to reap its full benefits.
-
 Information Security Data Backup For Sensitive Information
Information Security Data Backup For Sensitive InformationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Increase audience engagement and knowledge by dispensing information using Information Security Data Backup For Sensitive Information. This template helps you present information on three stages. You can also present information on Protect, Information, Manipulation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Manage Sensitive Data Securely Ppt Powerpoint Presentation Infographics Files Cpb
Manage Sensitive Data Securely Ppt Powerpoint Presentation Infographics Files CpbPresenting Manage Sensitive Data Securely Ppt Powerpoint Presentation Infographics Files Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase nine stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Manage Sensitive Data Securely. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Data Security Statistics Ppt Powerpoint Presentation Slides Graphic Tips Cpb
Data Security Statistics Ppt Powerpoint Presentation Slides Graphic Tips CpbPresenting our Data Security Statistics Ppt Powerpoint Presentation Slides Graphic Tips Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Data Security Statistics This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data Cloud Security Ppt Powerpoint Presentation Gallery Sample Cpb
Data Cloud Security Ppt Powerpoint Presentation Gallery Sample CpbPresenting Data Cloud Security Ppt Powerpoint Presentation Gallery Sample Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase ten stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Data Cloud Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Checklist To Implement Cloud Security In Business Cloud Data Protection
Checklist To Implement Cloud Security In Business Cloud Data ProtectionThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Checklist To Implement Cloud Security In Business Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Logging And Monitoring, Networking, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Checklist Policies And Procedures Cloud Data Protection
Cloud Security Checklist Policies And Procedures Cloud Data ProtectionThis slide depicts the policies and procedures of the cloud security checklist. It also represents how it is essential to create new and update the current policies in an organization. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Policies And Procedures Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, On Boarding Employees, Cloud Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Risks Or Threats Cloud Data Protection
Cloud Security Risks Or Threats Cloud Data ProtectionThis slide represents the list of threats or risks that can impact the security of a cloud these risks include loss of intellectual property, compliance violations, malware attacks, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Security Risks Or Threats Cloud Data Protection. This template helps you present information on eight stages. You can also present information on Revenue Losses, Compliance Violations, Loss Of Data using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats End User Control Cloud Data Protection
Cloud Security Threats End User Control Cloud Data ProtectionThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Business Data, Customers, Centralized Data, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Malware Attacks Cloud Data Protection
Cloud Security Threats Malware Attacks Cloud Data ProtectionThis slide represents the malware threat of cloud security and how it can affect data stored on the cloud, further leading to company loss. Introducing Cloud Security Threats Malware Attacks Cloud Data Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Frameworks, Targets, Technology, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Revenue Losses Cloud Data Protection
Cloud Security Threats Revenue Losses Cloud Data ProtectionThis slide represents the revenue loss threat of cloud security and how an organization could lose customers trust and loyalty when it doesnt have a good recovery plan. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Revenue Losses Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organizations Could, Revenue, Customers using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats Shared Vulnerabilities Cloud Data Protection
Cloud Security Threats Shared Vulnerabilities Cloud Data ProtectionThis slide describes how organizations and providers share vulnerabilities of a system, so each party must take precautions to protect data. Introducing Cloud Security Threats Shared Vulnerabilities Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Secure Cloud Data, Organizations, Data Security, using this template. Grab it now to reap its full benefits.
-
 Data Cloud Security Ppt Powerpoint Presentation Model Pictures Cpb
Data Cloud Security Ppt Powerpoint Presentation Model Pictures CpbPresenting our Data Cloud Security Ppt Powerpoint Presentation Model Pictures Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Data Cloud Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
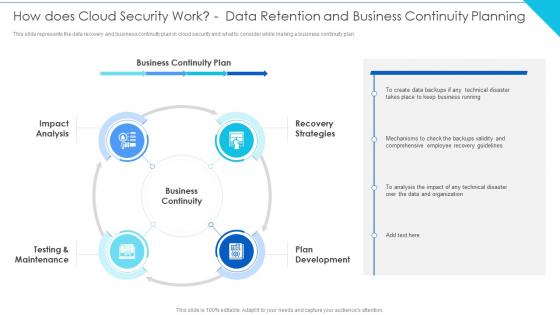
 Cloud Computing Security How Does Cloud Security Work Data Retention And Business
Cloud Computing Security How Does Cloud Security Work Data Retention And BusinessThis slide represents the data recovery and business continuity plan in cloud security and what to consider while making a business continuity plan. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security How Does Cloud Security Work Data Retention And Business. This template helps you present information on four stages. You can also present information on Impact Analysis, Recovery Strategies, Testing And Maintenance, Plan Development using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Building Data Analytics And Cyber Security Strategy Framework
Building Data Analytics And Cyber Security Strategy FrameworkThis slide covers various practices to be employed to expand healthcare business. It includes data culture, internal integration, predictive analytics, shareholders involvement and data security. Introducing our premium set of slides with Building Data Analytics And Cyber Security Strategy Framework. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Collection, Data Normalization, Expansion. So download instantly and tailor it with your information.
-
 Cloud Information Security How Does Cloud Security Work Data Planning
Cloud Information Security How Does Cloud Security Work Data PlanningThis slide represents the data recovery and business continuity plan in cloud security and what to consider while making a business continuity plan.Increase audience engagement and knowledge by dispensing information using Cloud Information Security How Does Cloud Security Work Data Planning This template helps you present information on five stages. You can also present information on Implement Information, Authentication Process, Data Encryption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Does Cloud Security Work Data Security Cloud Information Security
How Does Cloud Security Work Data Security Cloud Information SecurityThis slide represents the data security under the cloud security work process, and it also shows the various factors that cover data security.Introducing How Does Cloud Security Work Data Security Cloud Information Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Accessibility, Knowledge, Organized Documented using this template. Grab it now to reap its full benefits.
-
 Approaches Of Cloud Disaster Recovery For Data Security
Approaches Of Cloud Disaster Recovery For Data SecurityThis slide shows four approaches of cloud disaster recovery that can be used by an organization to create a data secure environment. It includes backup and restore, warm study, pilot light and multi site active or active approach. Introducing our premium set of slides with Approaches Of Cloud Disaster Recovery For Data Security. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Backup And Restore, Warm Standby, Pilot Light. So download instantly and tailor it with your information.
-
 Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery
Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation galleryThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Increase audience engagement and knowledge by dispensing information using Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery. This template helps you present information on two stages. You can also present information on Challenges, Solution, Data Collections using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing Data Inventory Collection Android Device Security Management
Addressing Data Inventory Collection Android Device Security ManagementThis slide provides information regarding data inventory collection with mobile device management system storing information such as hardware, software, management and additional information. Introducing Addressing Data Inventory Collection Android Device Security Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Hardware Information, Software Information, Management Information, using this template. Grab it now to reap its full benefits.
-
 Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security
Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT-based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems
Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting SystemsThis slide discusses the concept of governance tokenization in data security. The purpose of this slide is to showcase the overview of governance tokenization which include usage, features, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems. This template helps you present information on eight stages. You can also present information on Lack A Central Authority, Pivotal Decision Making, Widely Used Savings Protocol using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money Transfer
Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money TransferThis slide outlines the introduction of transactional tokenization. The purpose of this slide is to highlight the overview of transactional tokenization such as efficiency, lower cost, facilities, etc. Introducing Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money Transfer to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Tokenization, Data Security, Considering Security Tokens, Conventional Financial Securities, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Reasons For Conducting Tokenization In Data Security
Tokenization For Improved Data Security Reasons For Conducting Tokenization In Data SecurityThis slide outlines the rationale for implementing tokenization n data security. The reasons include minimizing risks, build customer trust, advancement in payment methods, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Reasons For Conducting Tokenization In Data Security. This template helps you present information on five stages. You can also present information on Card Accepting Businesses, Regulatory Compliance, Bureaucratic Processes For Businesses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain
Tokenization For Improved Data Security Role Of Utility Tokens In BlockchainThis slide discusses the objective of utility tokens in block chain. The purpose of this slide is to highlight the role of utility tokens which include decentralized storage, exchange value for service, etc. Introducing Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Storage, Block Chain Currency, Enhanced User Experience, Token Ownership Rights, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security
Tokenization For Improved Data Security Salient Features Of Tokenization In Data SecurityThis slide outlines the key characteristics of tokenization in data security. The purpose of this slide is to highlight the properties of tokenization that include underlying representation, transferability, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security. This template helps you present information on five stages. You can also present information on Underlying Representation, Transferability, Fungibility, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Selecting Appropriate Tokenization Solution For Business Needs
Tokenization For Improved Data Security Selecting Appropriate Tokenization Solution For Business NeedsThis slide discusses about choosing right tokenization solution for business needs. The purpose of this slide is to highlight the ways of selecting which include applicability to business, data elements, etc. Introducing Tokenization For Improved Data Security Selecting Appropriate Tokenization Solution For Business Needs to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Consistency Requirement, Data Elements For Tokenization, Applicability To Business, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System
Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based SystemThis slide highlights the key functions within a cloud-based system in data security. The purpose of this slide is to outline the Process activities in a cloud-based system which include gathering, creating, retrieving data, etc. Introducing Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization Process Activities, Cloud Based System, Retrieving Data, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit Cards
Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit CardsThis slide describes the tokenizing of debit and credit cards for transactional purposes. The purpose of this slide is to showcase the transactional tokenization of debit and credit cards. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit Cards. This template helps you present information on six stages. You can also present information on Unique Alternate Codes, Consumer Benefits, Enhanced Security, Debit And Credit Cards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets
Tokenization For Improved Data Security Working Of Security Tokenization In Financial AssetsThis slide highlights the phases of security tokenization. The purpose of this slide is to showcase the working of security tokenization along with its phases which include creation, dividend distribution, etc. Introducing Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Working Of Security Tokenization, Financial Assets, Dividend Distribution, Security Token Classification, using this template. Grab it now to reap its full benefits.
-
 Securing Food Safety In Online Leveraging Data Analytics To Forecast Deliveries
Securing Food Safety In Online Leveraging Data Analytics To Forecast DeliveriesThis slide covers utilizing data analytics tools to forecast demand involves key components such as predictive analytics, customer segmentation and sentiment analysis. Introducing Securing Food Safety In Online Leveraging Data Analytics To Forecast Deliveries to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Predictive Analytics, Customer Segmentation, Sentiment Analysis, using this template. Grab it now to reap its full benefits.
-
 Incorporating Secure Multi Party Computation To Boost Data Implementing Digital Transformation And Ai DT SS
Incorporating Secure Multi Party Computation To Boost Data Implementing Digital Transformation And Ai DT SSThis slide provides glimpse about utilizing secure multi party computation SMPC approach that can help businesses in boosting data confidentiality. It includes stages such as input sharing, secure computation, output reconstruction, etc. Increase audience engagement and knowledge by dispensing information using Incorporating Secure Multi Party Computation To Boost Data Implementing Digital Transformation And Ai DT SS. This template helps you present information on three stages. You can also present information on Increase Security Against Attacks, Boost Data Confidentiality, Input Sharing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Physical Security Systems To Enhance Data Safety
Physical Security Systems To Enhance Data SafetyThis slide showcases physical control systems to manage and safeguard crucial data. The systems covered are cable infrastructure, fire alarm, building management, etc. Introducing our premium set of slides with Physical Security Systems To Enhance Data Safety. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cable Infrastructure, Electronic Security Systems, Building Management. So download instantly and tailor it with your information.
-
 Big Data Model Of Security Sharing Based On Blockchain
Big Data Model Of Security Sharing Based On BlockchainThis slide gives an overview of the big data model of security sharing based on blockchain which include citizen, government, school, student, individual, etc. Presenting our set of slides with Big Data Model Of Security Sharing Based On Blockchain. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Collect Data, Smart Contract, Query Data.
-
 Data Transmission In Blockchain Security Icon
Data Transmission In Blockchain Security IconIntroducing our premium set of slides with Data Transmission In Blockchain Security Icon. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Transmission, Blockchain Security, Icon. So download instantly and tailor it with your information.
-
 Data Analytics Importance In Identity And Access Management Securing Systems With Identity
Data Analytics Importance In Identity And Access Management Securing Systems With IdentityThis slide showcases the importance of Identity and Access Management based data analytics. The purpose of this slide is to explain the benefits, which are anomaly detection, account monitoring, policy violation detection, and so on. Increase audience engagement and knowledge by dispensing information using Data Analytics Importance In Identity And Access Management Securing Systems With Identity This template helps you present information on Five stages. You can also present information on Anomaly Detection, Identity Certification Campaigns using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Introduction Of Cyber Threat Intelligence For Data Security
Introduction Of Cyber Threat Intelligence For Data SecurityThis slide discusses the overview of cyber threat intelligence for proactively blocking attacks and security purpose. Introducing Introduction Of Cyber Threat Intelligence For Data Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Evolving Threats Demand Intelligence, Vital For Security Architecture, Proactively Blocks Attacks, using this template. Grab it now to reap its full benefits.
-
 Introduction Of Data Layer In Web Security Solution
Introduction Of Data Layer In Web Security SolutionThis slide discusses the overview of the sixth layer of web security, which is the data layer for enhancing security in the web. Introducing Introduction Of Data Layer In Web Security Solution to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Ensure Data Integrity, Employing Data Encryption Is Crucial, Safeguard Against Unintentional Data Loss Deletion, using this template. Grab it now to reap its full benefits.
-
 Practices To Ensure Secure Cloud Data Migration
Practices To Ensure Secure Cloud Data MigrationThis slide provides the best practices for effective monitoring of cloud data migration that helps to eliminate the potential risks associated with data deployment. Key steps are use of native solutions, compliance audit, etc. Presenting our set of slides with Practices To Ensure Secure Cloud Data Migration. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Security Architect, Track And Automate, Implement Compliance.
-
 Encryption For Data Homomorphic Cryptography For Data Base Security Cybersecurity SS
Encryption For Data Homomorphic Cryptography For Data Base Security Cybersecurity SSThis slide showcases homomorphic cryptography deployment which can help employees increase data privacy and outsourcing security. It provides details about private key, plaintext, decryption, etc. Introducing Encryption For Data Homomorphic Cryptography For Data Base Security Cybersecurity SS to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Homomorphic Encryption, Classified Plaintext, Decrypted Results, Data Owner Organization, using this template. Grab it now to reap its full benefits.
-
 Encryption For Data Roles And Responsibilities Of Cyber Security Department Cybersecurity SS
Encryption For Data Roles And Responsibilities Of Cyber Security Department Cybersecurity SSThis slide showcases roles and responsibilities of cybersecurity teams which can help improve business data encryption. It provides details about CTO, key management, encryption specialist and engineer, etc. Introducing Encryption For Data Roles And Responsibilities Of Cyber Security Department Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Key Management, Encryption Engineer, Chief Technology Officer, Encryption Specialist, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Data Security In Remote Healthcare Monitoring
Best Practices For Data Security In Remote Healthcare MonitoringThe slide outlines best practices to safeguard sensitive patient information on remote healthcare monitoring system. It include tips such as using data encryption, implementing strong access control and security testing. Presenting our set of slides with Best Practices For Data Security In Remote Healthcare Monitoring. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Utilize Data Encryption, Security Testing And Patching, Strong Access Controls .
-
 IOT Security System Tools For Data Protection
IOT Security System Tools For Data ProtectionThis slide showcases methods to secure IoT security systems. It includes digital certificates, network and application programming interface security. Presenting our set of slides with name IOT Security System Tools For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Security, API Security, Digital Certificates.
-
 Comparative Assessment Of Encryption Algorithms For Organizational Data Security
Comparative Assessment Of Encryption Algorithms For Organizational Data SecurityThis slide provides a comparative assessment of various data encryption algorithms on different parameters. The multiple parameters used for assessment are encryption standard and use cases. Introducing our premium set of slides with Comparative Assessment Of Encryption Algorithms For Organizational Data Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Aes, Tdes, Twofish, Blowfish. So download instantly and tailor it with your information.
-
 E Commerce Subscription Data Security Management Techniques
E Commerce Subscription Data Security Management TechniquesThis slide highlights the techniques to secure e-commerce subscription data to ensure data protection and management for trust building. Key strategies are encryption strategy, hand-on monitoring, and contingency planning. Introducing our premium set of slides with E Commerce Subscription Data Security Management Techniques Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Encryption Strategy, Hands-On Monitoring, Contingency Planning So download instantly and tailor it with your information.
-
 Server Security Data In Powerpoint And Google Slides Cpp
Server Security Data In Powerpoint And Google Slides CppPresenting our Server Security Data In Powerpoint And Google Slides Cpp PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Server Security Data This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data Security Analysis In Powerpoint And Google Slides Cpp
Data Security Analysis In Powerpoint And Google Slides CppPresenting our Data Security Analysis In Powerpoint And Google Slides Cpp PowerPoint template design. This PowerPoint slide showcases Three stages. It is useful to share insightful information on Data Security Analysis This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Protecting Sensitive Data From Network Security Threats
Protecting Sensitive Data From Network Security ThreatsThis slide highlights network security threats to protect from unauthorized access including trojan viruses, malware, and computer worms. Introducing our premium set of slides with name Protecting Sensitive Data From Network Security Threats. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Trojan Virus, Malware, Computer Worms. So download instantly and tailor it with your information.
-
 Cloud Encryption Essentials For Robust Data Security
Cloud Encryption Essentials For Robust Data SecurityThe purpose of this slide is to highlight how cloud encryption essentials bolster robust data security. It safeguard sensitive information stored in cloud environments through cryptographic techniques. Presenting our set of slides with name Cloud Encryption Essentials For Robust Data Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Insider Threat Defense, Secure Data Transfers, Organizational Integrity.





