Powerpoint Templates and Google slides for Data Secure
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Logistics framework inventory management cyber security customer data
Logistics framework inventory management cyber security customer dataEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Logistics Framework Inventory Management Cyber Security Customer Data is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
 Data management maturity information security business growth architecture
Data management maturity information security business growth architectureDeliver a credible and compelling presentation by deploying this Data Management Maturity Information Security Business Growth Architecture. Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The twelve slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Data Management Maturity Information Security Business Growth Architecture PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
-
 Computer system security dispose data and equipment properly
Computer system security dispose data and equipment properlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Deliver an outstanding presentation on the topic using this Computer System Security Dispose Data And Equipment Properly. Dispense information and present a thorough explanation of Dispose Data And Equipment Properly using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data security it post it notes ppt slides visual aids ppt slides picture
Data security it post it notes ppt slides visual aids ppt slides pictureIncrease audience engagement and knowledge by dispensing information using Data Security IT Post IT Notes Ppt Slides Visual Aids Ppt Slides Picture. This template helps you present information on three stages. You can also present information on Post IT Notes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
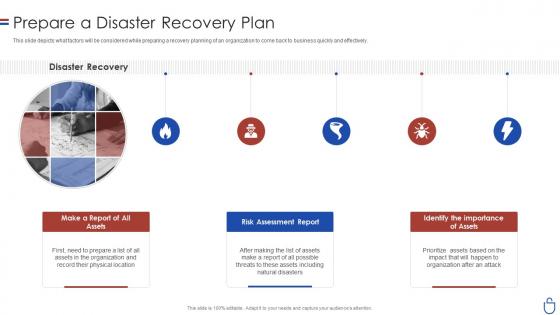 Data security it prepare a disaster recovery plan ppt slides rules
Data security it prepare a disaster recovery plan ppt slides rulesThis slide depicts what factors will be considered while preparing a recovery planning of an organization to come back to business quickly and effectively. Introducing Data Security IT Prepare A Disaster Recovery Plan Ppt Slides Rules to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Disaster Recovery, Make Report Assets, Risk Assessment Report Assets, Identify importance, using this template. Grab it now to reap its full benefits.
-
 Data security it prepare data backup for sensitive information
Data security it prepare data backup for sensitive informationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Present the topic in a bit more detail with this Data Security IT Prepare Data Backup For Sensitive Information. Use it as a tool for discussion and navigation on Data Backup, Provide Cloud Services, Prevent Data, Natural Disasters. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
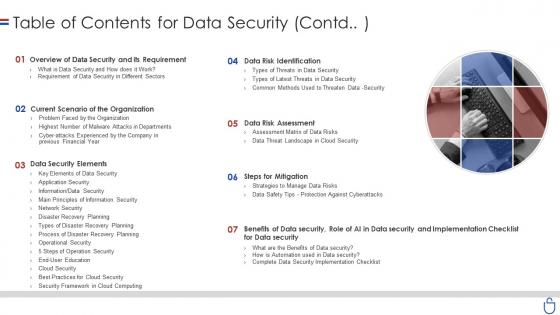 Data security it table of contents for data security contd
Data security it table of contents for data security contdIncrease audience engagement and knowledge by dispensing information using Data Security IT Table Of Contents For Data Security Contd. This template helps you present information on seven stages. You can also present information on Overview Data Security And Its Requirement, Current Scenario Organization, Data Security Elements, Steps Mitigation, Data Risk Assessment, Data Risk Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
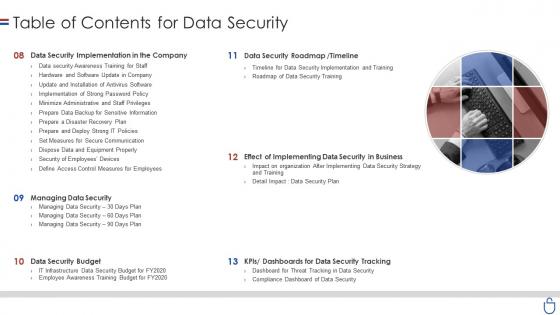 Data security it table of contents for data security ppt slides display
Data security it table of contents for data security ppt slides displayIntroducing Data Security IT Table Of Contents For Data Security Ppt Slides Display to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Data Security Implementation Company, Data Security Roadmap, Timeline, Managing Data Security, Data Security Budget, Dashboards Data Security Tracking, using this template. Grab it now to reap its full benefits.
-
 Icons slide for data security it
Icons slide for data security itPresenting our premium Icons Slide For Data Security IT set of slides with flexible icons. The icons are designed by our group of professionals. Add these Icons Slide For Data Security IT to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
 Data security it 30 60 90 days ppt slides infographic template
Data security it 30 60 90 days ppt slides infographic templateIntroducing Data Security IT 30 60 90 Days Ppt Slides Infographic Template to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days, using this template. Grab it now to reap its full benefits.
-
 Data security it agenda for data security ppt slides gallery
Data security it agenda for data security ppt slides galleryIncrease audience engagement and knowledge by dispensing information using Data Security IT Agenda For Data Security Ppt Slides Gallery. This template helps you present information on five stages. You can also present information on Employees, Data And Information Systems, Strategies And Tools using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it dispose data and equipment properly
Data security it dispose data and equipment properlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Increase audience engagement and knowledge by dispensing information using Data Security IT Dispose Data And Equipment Properly. This template helps you present information on three stages. You can also present information on Employees, Organization, Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it elements of data security disaster recovery planning
Data security it elements of data security disaster recovery planningThis slide depicts the disaster recovery plan in the data security model and what strategies an organization needs to adopt to recover from an attack or natural disaster. Introducing Data Security IT Elements Of Data Security Disaster Recovery Planning to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Business, Natural Disasters, Human Interfered Security Incidents, Technology, using this template. Grab it now to reap its full benefits.
-
 Data security it how is automation used in data security
Data security it how is automation used in data securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Present the topic in a bit more detail with this Data Security IT How Is Automation Used In Data Security. Use it as a tool for discussion and navigation on Threat Detection, Threat Response, Human Augmentation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it latest threats in data security ppt slides background designs
Data security it latest threats in data security ppt slides background designsThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Increase audience engagement and knowledge by dispensing information using Data Security IT Latest Threats In Data Security Ppt Slides Background Designs. This template helps you present information on three stages. You can also present information on Dridex Malware, Romance Scams, Emotet Malware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Digital Security And Data Audit Icon
Digital Security And Data Audit IconIntroducing our Digital Security And Data Audit Icon set of slides. The topics discussed in these slides are Data, Security, Digital. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Security Risk Treatment Action Plan Icon
Data Security Risk Treatment Action Plan IconPresenting our set of slides with Data Security Risk Treatment Action Plan Icon. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Security Risk Treatment, Action Plan Icon.
-
 Data Breach Prevention Security Software To Protect Business From Data Breach
Data Breach Prevention Security Software To Protect Business From Data BreachThe purpose of this slide is to highlight the available security tools to stay safe from data breaches. The popular security software are access control solutions, Security Information And Event Management SIEM tools, and antivirus software. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention Security Software To Protect Business From Data Breach. This template helps you present information on three stages. You can also present information on Security Information And Event Management, Amends Permissions As Needed, Security Software To Protect Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Challenges And Solution For Protecting Data
Network Security Challenges And Solution For Protecting DataThis slide showcase solution and challenges for network security. The main purpose for this template is to save company data from getting into hands of rival businesses. This includes data theft, insider threat, password attack, etc. Presenting our set of slides with Network Security Challenges And Solution For Protecting Data. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Challenges, Solution.
-
 Network Security Framework For Preventing Data Theft
Network Security Framework For Preventing Data TheftThis slide showcase model of network security. The main purpose of this template is preventing company confidential data from getting in the hands of rival companies. This includes third party, sender, and receiver. Introducing our Network Security Framework For Preventing Data Theft set of slides. The topics discussed in these slides are Message Modification, Confidential Information. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Network Security Highlighting Important Steps For Protecting Data
Network Security Highlighting Important Steps For Protecting DataThis slide showcase steps of network security. The main reason for this slide is showcasing management of network without any uninterrupted operations. This includes internal networks, protection security, cyber security, etc. Presenting our well structured Network Security Highlighting Important Steps For Protecting Data. The topics discussed in this slide are Internal Network, Protected Payment.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Network Security Icon For Protecting Data From Theft
Network Security Icon For Protecting Data From TheftIntroducing our Network Security Icon For Protecting Data From Theft set of slides. The topics discussed in these slides are Network Security Protecting Data. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Understanding Security Risk Related With Dark Data Dark Data And Its Utilization
Understanding Security Risk Related With Dark Data Dark Data And Its UtilizationThis slide focuses on the security risks associated with dark data. Some of the risks associated with dark data include vulnerability to hacking, negative impact on the business, and an increased workload for IT teams, etc. Introducing Understanding Security Risk Related With Dark Data Dark Data And Its Utilization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability To Hacking, Negative Impact On Business, Increased Workload For IT Teams, using this template. Grab it now to reap its full benefits.
-
 Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V
Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS VThis slide represents overview of ICT information and communication technology business security It covers types and features for security such as network security, endpoint security etc Present the topic in a bit more detail with this Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Unauthorized Sources, Factor Authentication, Organizations Information This template is free to edit as deemed fit for your organization Therefore download it now
-
 Big Data Analytics Security Icon
Big Data Analytics Security IconIntroducing our Big Data Analytics Security Icon set of slides. The topics discussed in these slides are Big Data Analytics Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Big Data Security Analytics Ppt Powerpoint Presentation Infographics Format
Big Data Security Analytics Ppt Powerpoint Presentation Infographics FormatPresenting our well structured Big Data Security Analytics Ppt Powerpoint Presentation Infographics Format. The topics discussed in this slide are Big Data Security Analytics.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Encryption Techniques Icon For Securing Big Data Analytics
Encryption Techniques Icon For Securing Big Data AnalyticsIntroducing our Encryption Techniques Icon For Securing Big Data Analytics set of slides. The topics discussed in these slides are Encryption Techniques, Securing Big Data Analytics. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Types Of Encryption For Securing Big Data Analytics
Types Of Encryption For Securing Big Data AnalyticsThis slide highlights the various types of encryption techniques utilized for protecting big data analytics. The purpose of this slide is to help the business safeguard sensitive information for preventing data breaches and information thefts. It includes quantum proof encryption, homomorphic encryption, etc. Introducing our premium set of slides with Types Of Encryption For Securing Big Data Analytics. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Homomorphic Encryption, Differential Privacy. So download instantly and tailor it with your information.
-
 Cyber Security Data Capture Plan Icon
Cyber Security Data Capture Plan IconIntroducing our premium set of slides with Cyber Security Data Capture Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data, Capture, Security. So download instantly and tailor it with your information.
-
 Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V
Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V. Use it as a tool for discussion and navigation on Backup Repository, Encrypted Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V
Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V Use it as a tool for discussion and navigation on Employee Headcount, Average Employee Age, Gender Diversity Ratio This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display visual representation of internet of Things IoT security. The slide covers information about various IoT sensors, cloud for data collection, administration level, etc. Deliver an outstanding presentation on the topic using this Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Data, Security, Cyber using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V
Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, using this template. Grab it now to reap its full benefits.
-
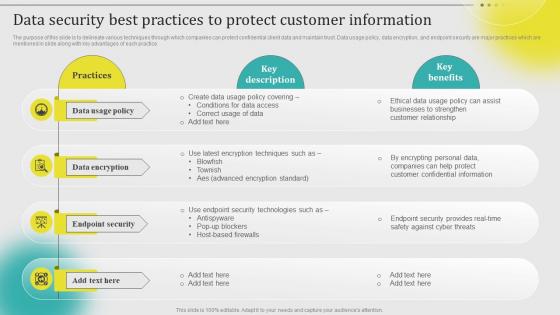 Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS V
Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Data Security Best Practices To Developing Targeted Marketing Campaign MKT SS V
Data Security Best Practices To Developing Targeted Marketing Campaign MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Increase audience engagement and knowledge by dispensing information using Data Security Best Practices To Developing Targeted Marketing Campaign MKT SS V. This template helps you present information on four stages. You can also present information on Policy, Encryption, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Security Best Practices To Protect Complete Introduction To Database MKT SS V
Data Security Best Practices To Protect Complete Introduction To Database MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Increase audience engagement and knowledge by dispensing information using Data Security Best Practices To Protect Complete Introduction To Database MKT SS V. This template helps you present information on four stages. You can also present information on Policy, Encryption, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies
Overview Of Encryption For Securing Data At Rest Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data at rest. The storage methods include file servers, network shares, document management systems, external storage, databases, endpoint devices, mobile devices, cloud storage, etc. Present the topic in a bit more detail with this Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies. Use it as a tool for discussion and navigation on Database Encryption, Information Rights Management, Data Leak Prevention, Mobile Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Employee Data Security Compliance Icon
Employee Data Security Compliance IconPresenting our set of slides with Employee Data Security Compliance Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Employee Data, Security Compliance.
-
 Digital Transformation Ensuring Erp Data Security And Compliance DT SS
Digital Transformation Ensuring Erp Data Security And Compliance DT SSPresent the topic in a bit more detail with this Digital Transformation Ensuring Erp Data Security And Compliance DT SS Use it as a tool for discussion and navigation on Robust Access Controls, Data Encryption, Compliance With Regulations This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Management Framework For Organization Data Protection
Information Security Management Framework For Organization Data ProtectionThis slide represents framework that assists organizations in developing information security management to enhance data protection. This model sets information security at tactical level, strategic level, and operational level. Introducing our Information Security Management Framework For Organization Data Protection set of slides. The topics discussed in these slides are Information Security Plan, Consciousness Management, Risk Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Software Defined Virtual Infrastructure For Cloud Management And Data Security
Software Defined Virtual Infrastructure For Cloud Management And Data SecurityThis slide represents the virtual infrastructure framework assisting companies to enhance data security and maintain business continuity. It includes various key components such as cloud management layer, physical layer, storage, etc. Presenting our well structured Software Defined Virtual Infrastructure For Cloud Management And Data Security. The topics discussed in this slide are Service Management, Business Continuity, Security Compliance. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Wireless Lan Network Icon For Data Security
Wireless Lan Network Icon For Data SecurityPresenting our well structured Wireless Lan Network Icon For Data Security. The topics discussed in this slide are Wireless, Data Security . This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V
Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Increase audience engagement and knowledge by dispensing information using Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V. This template helps you present information on four stages. You can also present information on Policy, Encryption, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
 Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It
Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age ItThis slide describes the cloud cryptography trends. The purpose of this slide is to highlight the emerging trends in the field of cloud encryption. These include homomorphic encryption, quantum-safe cryptography, secure multi-party computation, etc. Introducing Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Homomorphic Encryption, Quantum Safe Cryptography, Secure Multi Party Computation, using this template. Grab it now to reap its full benefits.
-
 Privacy Framework Icon For Securing Business Data
Privacy Framework Icon For Securing Business DataPresenting our well structured Privacy Framework Icon For Securing Business Data. The topics discussed in this slide are Privacy Framework Icon, Securing Business Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data Security Crime Prevention Management Flowchart
Data Security Crime Prevention Management FlowchartThis slide depicts the internal data security crime prevention team. Its purpose is to understand duties of the heads to prevent internal crimes. This slide includes data security, technical security, crime prevention, security support, etc. Introducing our Data Security Crime Prevention Management Flowchart set of slides. The topics discussed in these slides are Security Director, Prevention Head, Security Support This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS
Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SSThis slide analyses the need of implementing data security initiatives to address key customer data challenges in retail industry. It also mentions types of customer data collected such as account, location, browsing, and profile. Deliver an outstanding presentation on the topic using this Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS Dispense information and present a thorough explanation of Customer Trust, Sensitive Information, Balancing Personalization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V
Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Automated Backup, Track Backup using this template. Grab it now to reap its full benefits.
-
 Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process
Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management ProcessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process. This template helps you present information on five stages. You can also present information on Malware Infection, Systems With Passwords, Employees Feels, Allow Official Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Aerospace Big Data Security Metrics Checklist
Aerospace Big Data Security Metrics ChecklistThis slide represents checklist for security metrics of aerospace big data. It aims to help organization to effectively engage with different departments of organization by determining risk and threats. It includes various elements such as risks signed off, adequate resolution of internal compliance, etc. Presenting our set of slides with Aerospace Big Data Security Metrics Checklist. This exhibits information on nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risks Signed Off, Post Awareness Initiatives, Security Occurrences.
-
 Tokenization For Improved Data Security Tokenization Global Market Report Coverage
Tokenization For Improved Data Security Tokenization Global Market Report CoverageThis slide represents the market report coverage of tokenization across the globe. The purpose of this slide is to showcase the market growth for the year 2021 and the predicted growth for coming years. Present the topic in a bit more detail with this Tokenization For Improved Data Security Tokenization Global Market Report Coverage. Use it as a tool for discussion and navigation on Market Growth, Tokenization Global Market, Protection Of Payment Gateways. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Asymmetric Data Encryption For Web Security
Asymmetric Data Encryption For Web SecurityThis slide showcases the workflow of asymmetric data encryption for security of web which includes components such as public key, private key, original text, etc. Introducing our Asymmetric Data Encryption For Web Security set of slides. The topics discussed in these slides are Asymmetric Data Encryption, Web Security, Private Key, Original Text. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Wireless Internet Security To Secure Data
Icon For Wireless Internet Security To Secure DataPresenting our well structured Icon For Wireless Internet Security To Secure Data. The topics discussed in this slide are Wireless Internet, Security, Secure Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Fingerprint Biometric Technology Icon For Securing Data
Fingerprint Biometric Technology Icon For Securing DataIntroducing our Fingerprint Biometric Technology Icon For Securing Data set of slides. The topics discussed in these slides are Fingerprint Biometric Technology, Icon For Securing Data This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Network Virtualization Icon To Enhance Data Security
Network Virtualization Icon To Enhance Data SecurityIntroducing our Network Virtualization Icon To Enhance Data Security set of slides. The topics discussed in these slides are Network Virtualization, Data Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Technology Project Goals Icon To Strength Data Security
Technology Project Goals Icon To Strength Data SecurityPresenting our set of slides with Technology Project Goals Icon To Strength Data Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technology, Goals, Strength.
-
 Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SS
Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SSThis slide provides glimpse about utilizing secure multi-party computation SMPC approach that can help businesses in boosting data confidentiality. It includes stages such as input sharing, secure computation, output reconstruction, etc. Present the topic in a bit more detail with this Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SS. Use it as a tool for discussion and navigation on Secure Computation, Output Reconstruction, Input Sharing. This template is free to edit as deemed fit for your organization. Therefore download it now.




