Powerpoint Templates and Google slides for Data Secure
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data security it security of employees devices ppt slides brochure
Data security it security of employees devices ppt slides brochureThis slide depicts that the security of employees hardware or devices is also essential while applying the cyber security model. Introducing Data Security IT Security Of Employees Devices Ppt Slides Brochure to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Intrusions, Project, Peripheral Devices, using this template. Grab it now to reap its full benefits.
-
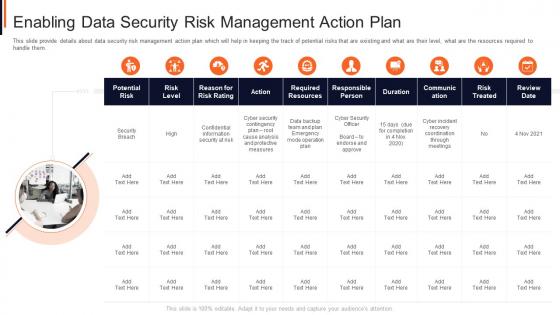 Enabling data security risk management action plan project safety management it
Enabling data security risk management action plan project safety management itThis slide provide details about data security risk management action plan which will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them. Introducing Enabling Data Security Risk Management Action Plan Project Safety Management It to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Analysis, Measures, Plan, Security, Risk, using this template. Grab it now to reap its full benefits.
-
 Icon showcasing data availability security against risks and threats
Icon showcasing data availability security against risks and threatsPresenting our set of slides with Icon Showcasing Data Availability Security Against Risks And Threats. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Showcasing Data Availability Security Against Risks And Threats.
-
 Information Technology Security Dispose Data And Equipment Properly
Information Technology Security Dispose Data And Equipment ProperlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Introducing Information Technology Security Dispose Data And Equipment Properly to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Dispose Data And Equipment Properly, using this template. Grab it now to reap its full benefits.
-
 Information Security Dispose Data And Equipment Properly
Information Security Dispose Data And Equipment ProperlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Increase audience engagement and knowledge by dispensing information using Information Security Dispose Data And Equipment Properly. This template helps you present information on three stages. You can also present information on Dispose Data And Equipment Properly using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Program Icon For Protecting Client Data
Security Program Icon For Protecting Client DataPresenting our set of slides with name Security Program Icon For Protecting Client Data. This exhibits information on one stage of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Program Icon For Protecting Client Data.
-
 Cloud Data Protection Tools Used In Cloud Security
Cloud Data Protection Tools Used In Cloud SecurityThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud. Increase audience engagement and knowledge by dispensing information using Cloud Data Protection Tools Used In Cloud Security. This template helps you present information on one stage. You can also present information on Cloud Solutions, Security, Networks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Checklist Data Encryption Cloud Data Protection
Cloud Security Checklist Data Encryption Cloud Data ProtectionThis slide represents the importance of data encryption in cloud security and what type of data should always be encrypted through private keys. Introducing Cloud Security Checklist Data Encryption Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Data Servers, Network, Cloud, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Checklist Logging And Monitoring Cloud Data Protection
Cloud Security Checklist Logging And Monitoring Cloud Data ProtectionThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, Network, Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Checklist Security Patches And Updates Cloud Data Protection
Cloud Security Checklist Security Patches And Updates Cloud Data ProtectionThis slide depicts the importance of security patches and timely updates of security technologies. It also shows how it is crucial to scan systems, servers, and frameworks regularly. Introducing Cloud Security Checklist Security Patches And Updates Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Technologies, Organization, Servers, using this template. Grab it now to reap its full benefits.
-
 What Are The Benefits Of A Cloud Security System Cloud Data Protection
What Are The Benefits Of A Cloud Security System Cloud Data ProtectionThis slide represents the benefits of a cloud security system, such as efficient recovery, openness, no hardware requirement, DDOS protection, and data security. Introducing What Are The Benefits Of A Cloud Security System Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Efficient Recovery, Efficient Data Security, Business Capacity, using this template. Grab it now to reap its full benefits.
-
 Incident Response Playbook Best Work From Home Data Security Practices
Incident Response Playbook Best Work From Home Data Security PracticesPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Increase audience engagement and knowledge by dispensing information using Incident Response Playbook Best Work From Home Data Security Practices. This template helps you present information on six stages. You can also present information on System Update, Avoid Using External Device, Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Incident Response Playbook Checklist For Work From Home Data Security
Incident Response Playbook Checklist For Work From Home Data SecurityIncrease audience engagement and knowledge by dispensing information using Incident Response Playbook Checklist For Work From Home Data Security. This template helps you present information on one stages. You can also present information on Training, Policies, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Threats Loss Of Data Cloud Information Security
Cloud Security Threats Loss Of Data Cloud Information SecurityThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Information Security This template helps you present information on four stages. You can also present information on Cloud Administrations, Protection Frameworks, Technology Advances using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Securing Our Data With CRM Customer Relationship Management Deployment Strategy
Securing Our Data With CRM Customer Relationship Management Deployment StrategyThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security.Increase audience engagement and knowledge by dispensing information using Securing Our Data With CRM Customer Relationship Management Deployment Strategy This template helps you present information on three stages. You can also present information on Factor Authentication, Storage And Failover, Communication Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Of Information In Big Data Ppt Sample
Security Of Information In Big Data Ppt SampleThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real time, and so on.Increase audience engagement and knowledge by dispensing information using Security Of Information In Big Data Ppt Sample This template helps you present information on one stage. You can also present information on Securing Massive, Data Collections, Comprehending, Preserving using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 3 Step Cyber Security Plan For Data Protection
3 Step Cyber Security Plan For Data ProtectionThis slide signifies the three stage cyber security program to improve data protection. It covers information about steps like prevention, response and remediation. Presenting our set of slides with 3 Step Cyber Security Plan For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevention, Response, Remediation.
-
 Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber Security
Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to exhibit biggest cyber security awareness challenges which is faced by the organization. Outdated content, burden on administrators, low employee participation rate and employees losing interest are some of the key challenges which are highlighted in the slide. Increase audience engagement and knowledge by dispensing information using Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber Security. This template helps you present information on five stages. You can also present information on Outdated Content, Employees Lose Interest, Burden On Administrators using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Image Of IoT Industrial Automation To Ensure Secure Data
Image Of IoT Industrial Automation To Ensure Secure DataPresenting our set of slides with Image Of IoT Industrial Automation To Ensure Secure Data. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Image Of Iot Industrial, Automation Ensure Secure Data.
-
 Business Expansion And Data Security Strategy Icon
Business Expansion And Data Security Strategy IconIntroducing our premium set of slides with Business Expansion And Data Security Strategy Icon. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Business Expansion, Data Security Strategy Icon. So download instantly and tailor it with your information.
-
 Key Strategies To Secure Business Data
Key Strategies To Secure Business DataThis slide showcase strategies that can be used for securing cyberattacks and target organizational data security and access. It includes updating devices, secure iot technology, track cloud storage, train employees and secure network access. Introducing our premium set of slides with Key Strategies To Secure Business Data. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Updated Devices, Track Cloud Storage, Train Employees. So download instantly and tailor it with your information.
-
 Corporate Data Security Policy In Powerpoint And Google Slides Cpb
Corporate Data Security Policy In Powerpoint And Google Slides CpbPresenting our Corporate Data Security Policy In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Corporate Data Security Policy This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
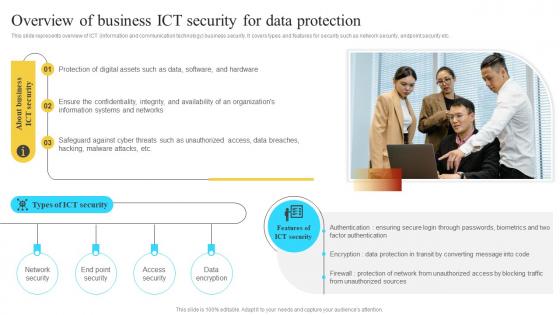 Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V
Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Digital, Safeguard Against Cyber, using this template. Grab it now to reap its full benefits.
-
 Secured Data Protection For Online Security System Icon
Secured Data Protection For Online Security System IconPresenting our set of slides with Secured Data Protection For Online Security System Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secured Data Protection, Online Security System Icon.
-
 IT Audit Evaluation Icon For Data Security
IT Audit Evaluation Icon For Data SecurityIntroducing our premium set of slides with IT Audit Evaluation Icon For Data Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like IT Audit, Evaluation Icon, Data Security. So download instantly and tailor it with your information.
-
 Impacts Of Cyber Security Data Compliance
Impacts Of Cyber Security Data ComplianceThis slide shows benefits of cyber security compliance which helps in aiming to protect sensitive data and maintain the integrity of information systems. It further includes benefits such as strengthening data protection etc. Presenting our set of slides with Impacts Of Cyber Security Data Compliance. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strengthening Data Protection, Regulatory Compliance.
-
 Components Of Virtual Infrastructure For Effective Data Management And Security
Components Of Virtual Infrastructure For Effective Data Management And SecurityThis slide represents key components of virtual infrastructure that help businesses with data security and disaster management. It includes various components such as virtualized computing, virtualized storage, management solutions, and virtualized security. Introducing our premium set of slides with Components Of Virtual Infrastructure For Effective Data Management And Security. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Virtualized Compute, Virtualized Networking Security, Virtualized Storage. So download instantly and tailor it with your information.
-
 Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS V
Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Offsite Backup, Automated Backup, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Icon For Insurancing Data Breaches
Cyber Security Icon For Insurancing Data BreachesPresenting our set of slides with Cyber Security Icon For Insurancing Data Breaches. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Icon, Insurancing Data Breaches.
-
 Online Data Cyber Security Services
Online Data Cyber Security ServicesThis slide showcases data cyber security services that protect personal data and help to preserve reputation. It includes elements such as firewall, antivirus, email filtering, device control and content filtering. Presenting our set of slides with Online Data Cyber Security Services. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Firewall, Antivirus, Device Control.
-
 Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SS
Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SSThis slide showcases the significant role of edge computing in enhancing IoT data security and privacy. It include role such as data filtering and processing, localised threat identification, and reduce attack surface. Introducing Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Filtering Processing, Reduce Attack Surface, Trusted Entities Interacting, using this template. Grab it now to reap its full benefits.
-
 Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SS
Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits personal data handling regulations for organisations across various regions. It includes data regulations such as general data protection regulation, the California consumer privacy act, and personal data protection act in Singapore. Increase audience engagement and knowledge by dispensing information using Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on three stages. You can also present information on Protection Regulation, Data Collection Consent, Data Breach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS
Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Increase audience engagement and knowledge by dispensing information using Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS This template helps you present information on six stages. You can also present information on Customer Data Protection, Online Transactions, Management Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Centre Colocations Icon For Securing Information
Data Centre Colocations Icon For Securing InformationPresenting our set of slides with Data Centre Colocations Icon For Securing Information This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Centre Colocations Icon, For Securing Information
-
 Implementing Byod Policy To Enhance Develop Security Policies For Data Protection
Implementing Byod Policy To Enhance Develop Security Policies For Data ProtectionThis slide shows major data protection policies for handling sensitive data of corporate. It include policies such as device security, network and data handling, etc. Introducing Implementing Byod Policy To Enhance Develop Security Policies For Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Data Handling, Device Security, Data Protection, using this template. Grab it now to reap its full benefits.
-
 Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy
Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod PolicyThis slide shows essential considerations for protecting crucial data of company in organization. It include security areas such as device security, network security and software updates, etc. Increase audience engagement and knowledge by dispensing information using Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy. This template helps you present information on five stages. You can also present information on Device Security, Mobile Device Management, Network Security, Malware Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies
Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By CompaniesThe purpose of this slide is to assess security and privacy challenges, and their impact on data migration process. It includes challenges and need for ensuring data privacy. Introducing Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Data Security And Privacy Challenges, Loss Of Customers, Sensitive Data, Poses Security And Privacy Concerns, using this template. Grab it now to reap its full benefits.
-
 Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process
Strategic Approach For Effective Data Migration Steps For A Secure Data Migration ProcessThe purpose of this slide is to represent the process of secure and safe data migration from one platform to another. It includes various stages such as assessing data sources, choosing method, designing architecture, etc. Introducing Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Design Architecture, Validate And Verify Results, Assess Data Sources, Data Migration Process, using this template. Grab it now to reap its full benefits.
-
 Icon For Data Loss Prevention In Information Security
Icon For Data Loss Prevention In Information SecurityPresenting our set of slides with Icon For Data Loss Prevention In Information Security. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Data Loss, Prevention In Information Security
-
 Authentication In Application Security For Data Protection
Authentication In Application Security For Data ProtectionThis slide discusses about the overview of authentication in application security and the various elements of MFA. Increase audience engagement and knowledge by dispensing information using Authentication In Application Security For Data Protection. This template helps you present information on five stages. You can also present information on Knowledge Factor, Possession Factor, Biometric Factor, Data Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Authorization In Application Security For Data Privacy
Authorization In Application Security For Data PrivacyThis slide discusses the overview of authorization in application security for authorized access of resource. Increase audience engagement and knowledge by dispensing information using Authorization In Application Security For Data Privacy. This template helps you present information on five stages. You can also present information on Application Security, Data Privacy, Helps Servers Identify Clients using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Components Of IP Security To Protect Sensitive Data
Major Components Of IP Security To Protect Sensitive DataThis slide showcases key elements of IP security for protecting data. The main purpose of this template is to showcase protection and trustworthiness of data. This includes encapsulating security payload, authentication header, and internet key exchange. Presenting our set of slides with name Major Components Of IP Security To Protect Sensitive Data. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Internet Key Exchange, Authentication Header, Encapsulating Security Payload.
-
 Big Data Analytics Technologies In Cyber Security
Big Data Analytics Technologies In Cyber SecurityThis slide showcases cyber security technologies in big data analytics. This includes encryptions, user access control and centralizsed key management systems. Presenting our set of slides with name Big Data Analytics Technologies In Cyber Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Big Data Analytics, Centralized Key Management, Technologies In Cyber Security.
-
 Visualization Security Icon For Data Protection
Visualization Security Icon For Data ProtectionPresenting our set of slides with Visualization Security Icon For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Visualization Security, Data Protection.
-
 Csirt Cyber Security Icon For Protecting Data
Csirt Cyber Security Icon For Protecting DataIntroducing our premium set of slides with Csirt Cyber Security Icon For Protecting Data. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Csirt Cyber Security, Protecting Data. So download instantly and tailor it with your information.
-
 Data Protection Server Security Technology Icon
Data Protection Server Security Technology IconPresenting our set of slides with Data Protection Server Security Technology Icon. This exhibits information on threestages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Server Security Technology.
-
 Types Of Wireless Internet Security For Data Protection
Types Of Wireless Internet Security For Data ProtectionThe following slide highlights key points such as WEP, WPA, WPA2, and WPA3 protocols to show types of wireless internet security for privacy protection. It helps in understanding and comparing different safety procedures for effective data protection. Introducing our premium set of slides with Types Of Wireless Internet Security For Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Wireless Internet. So download instantly and tailor it with your information.
-
 Virtual Private Cloud Icon Representing Data Security
Virtual Private Cloud Icon Representing Data SecurityPresenting our set of slides with Virtual Private Cloud Icon Representing Data Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Security, Representing, Cloud Icon.
-
 Cloud Virtualization Icon Showcasing Data Security
Cloud Virtualization Icon Showcasing Data SecurityPresenting our set of slides with name Cloud Virtualization Icon Showcasing Data Security This exhibits information on Threestages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Virtualization Icon, Showcasing Data Security
-
 Data Center Facility Security Plan
Data Center Facility Security PlanThe purpose of this slide is to ensure comprehensive protection against unauthorized access, physical threats, and data breaches including security aspects such as data center layout, environmental controls, etc. Introducing our premium set of slides with name Data Center Facility Security Plan. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Environmental Controls, Data Center Layout, Network Security, Vendor And Contractor Access. So download instantly and tailor it with your information.
-
 Different Encryption Methods To Secure Business Data
Different Encryption Methods To Secure Business DataThis slide represents various types of encryption method which assists businesses to protect data and maintain regulatory compliances. It includes different encryption methods to secure business data such as advance encryption standards, rivest shamir adleman, etc. Introducing our premium set of slides with name Different Encryption Methods To Secure Business Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Format Preserving Encryption, Blowfish, Advance Encryption Standards. So download instantly and tailor it with your information.
-
 Mobile Device Encryption Plan For Data Security Mobile Device Security Cybersecurity SS
Mobile Device Encryption Plan For Data Security Mobile Device Security Cybersecurity SSThis slide showcases data encryption plan that can help to enhance mobile security. Its key elements are target devices, employees, encryption technique used, software used, authentication method etc. Introducing Mobile Device Encryption Plan For Data Security Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Encrypted Communication, Secure Remote Access, Data Privacy using this template. Grab it now to reap its full benefits.
-
 Mobile Device Encryption Policy To Safeguard Data Mobile Device Security Cybersecurity SS
Mobile Device Encryption Policy To Safeguard Data Mobile Device Security Cybersecurity SSThis slide showcases mobile encryption policy that can help in data privacy. Its key components are purpose of policy, scope and encryption policy Increase audience engagement and knowledge by dispensing information using Mobile Device Encryption Policy To Safeguard Data Mobile Device Security Cybersecurity SS This template helps you present information on Three stages. You can also present information on Geographical Region, Detected Globally, Mobile Cyber Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Analyzing Cloud Based Service Offerings Best Practices To Improve Data Security
Analyzing Cloud Based Service Offerings Best Practices To Improve Data SecurityThis slide showcases various tips which can be adopted by business to enhance data security of SAAs application. It provides information regarding end to end encryption, application testing, data deletion policy and VPN. Introducing Analyzing Cloud Based Service Offerings Best Practices To Improve Data Security to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on End To End Encryption, Application Testing, Data Deletion Policy, Vpn, using this template. Grab it now to reap its full benefits.
-
 Desktop As A Service Icon For Improving Data Security
Desktop As A Service Icon For Improving Data SecurityPresenting our set of slides with Desktop As A Service Icon For Improving Data Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Desktop As A Service Icon, Improving Data Security
-
 NIDS Cyber Security Icon For Sensitive Data Protection
NIDS Cyber Security Icon For Sensitive Data ProtectionIntroducing our premium set of slides with NIDS Cyber Security Icon For Sensitive Data Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Sensitive, Cyber Security. So download instantly and tailor it with your information.
-
 Employee Data Security Operations Center Icon
Employee Data Security Operations Center IconIntroducing our premium set of slides with name Employee Data Security Operations Center Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Employee data, security operations center. So download instantly and tailor it with your information.
-
 Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SS
Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SSThis slide major types of encryption technology, focused on improving data privacy and security of todays business. It provides details about symmetric, asymmetric, RSA, data encryption standard, etc. Introducing Encryption For Data Major Types Of Encryption For Data Security Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Encryption, Asymmetric Encryption, RSA Encryption, using this template. Grab it now to reap its full benefits.
-
 Endpoint Data Loss Prevention Tool Building Next Generation Endpoint Security Cybersecurity SS
Endpoint Data Loss Prevention Tool Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases endpoint data loss prevention DLP tool process. It includes stages such as identification, assistance and tracking of endpoint data.Increase audience engagement and knowledge by dispensing information using Endpoint Data Loss Prevention Tool Building Next Generation Endpoint Security Cybersecurity SS. This template helps you present information three stages. You can also present information on Identify, Assist, Track, Potential Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security In Banking Icon To Protect Customer Data
Cyber Security In Banking Icon To Protect Customer DataIntroducing our premium set of slides with Cyber Security In Banking Icon To Protect Customer Data. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security In Banking, Icon To Protect, Customer Data. So download instantly and tailor it with your information.




