Powerpoint Templates and Google slides for Cybersecurity Threat
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Advanced security monitoring plan to remove cybersecurity threat and data infraction complete deck
Advanced security monitoring plan to remove cybersecurity threat and data infraction complete deckDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction Complete Deck is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the fourty six slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Minimize cybersecurity threats in healthcare company case competition complete deck
Minimize cybersecurity threats in healthcare company case competition complete deckDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Minimize Cybersecurity Threats In Healthcare Company Case Competition Complete Deck is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the fourty five slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Adware As A Cyber Threat In Cybersecurity Training Ppt
Adware As A Cyber Threat In Cybersecurity Training PptPresenting Adware as a Cyber Threat in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Identifying Threats As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Threats As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Threats as a Step for Cybersecurity Risk Identification. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Spam As A Threat In Cybersecurity Training Ppt
Spam As A Threat In Cybersecurity Training PptPresenting Spam as a Threat in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Threat Technology Security Displaying Cybersecurity Companies
Threat Technology Security Displaying Cybersecurity CompaniesIntroduce your topic and host expert discussion sessions with this Threat Technology Security Displaying Cybersecurity Companies. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the twelve slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 Statistics Associated With Retail Cybersecurity Threats
Statistics Associated With Retail Cybersecurity ThreatsThis slide highlights stats data for vulnerabilities affecting retail cybersecurity. The purpose of this template is to provide businesses with quantitative for fostering strategic defences and risk management. It includes elements such as credential phishing, ransomware, etc. Introducing our Statistics Associated With Retail Cybersecurity Threats set of slides. The topics discussed in these slides are Statistics Associated, Retail Cybersecurity Threats This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SS
Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SSThis slide showcases common internet of things IoT threats in the company, referable for related businesses. It provides details about network scan, command injection, SQL, zero-day, etc. Present the topic in a bit more detail with this Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Cyber Security Awareness, Quality Threat Modeling Tools, Weak Passwords, Authentication Practices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Emerging Threat Trends In Cybersecurity Industry Global Cybersecurity Industry Outlook
Emerging Threat Trends In Cybersecurity Industry Global Cybersecurity Industry OutlookThe slide presents the latest threat trends in the global cybersecurity industry. The purpose of the slide is to raise awareness about the evolving landscape of cyber threats, which is crucial for individuals and organizations to stay protected. It covers threat such as automotive hacking, cloud services attacks, social engineering attacks, 5g network threats, and ransomware attacks. Increase audience engagement and knowledge by dispensing information using Emerging Threat Trends In Cybersecurity Industry Global Cybersecurity Industry Outlook. This template helps you present information on three stages. You can also present information on Automotive Hacking, Attacks Against Cloud Services, Social Engineering Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Edr Cybersecurity Dashboard To Track Threats Building Next Generation Endpoint Security Cybersecurity SS
Edr Cybersecurity Dashboard To Track Threats Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases endpoint detection and response EDR dashboard which can help analyze malicious operations Malops and provide information about scans, investigations, activities, etc.Deliver an outstanding presentation on the topic using this Edr Cybersecurity Dashboard To Track Threats Building Next Generation Endpoint Security Cybersecurity SS. Dispense information and present a thorough explanation of Affected, Affected Users, Recent Activity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Dashboard To Track Cyber Threats In Organization Mobile Device Security Cybersecurity SS
Dashboard To Track Cyber Threats In Organization Mobile Device Security Cybersecurity SSThis slides showcases dashboard that can help to track number of cyber threats in organization. Its key elements are hacker attacks, spyware, viruses and zero day attacks Present the topic in a bit more detail with this Dashboard To Track Cyber Threats In Organization Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Track Cyber Threats, Attacks Types This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Distribution Of Spyware Threats By Geographical Region Mobile Device Security Cybersecurity SS
Distribution Of Spyware Threats By Geographical Region Mobile Device Security Cybersecurity SSThis slide showcases impact of mobile threats on organization. It highlights impact in terms of company financial loss, operational distribution, cybersecurity expenses, data breach etc. Present the topic in a bit more detail with this Distribution Of Spyware Threats By Geographical Region Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Support And Maintenance, Device Troubleshooting, Access Control This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Faced By Organization Due To Mobile Threats Mobile Device Security Cybersecurity SS
Impact Faced By Organization Due To Mobile Threats Mobile Device Security Cybersecurity SSThis slide showcases impact of mobile threats on organization. It highlights impact in terms of company financial loss, operational distribution, cybersecurity expenses, data breach etc. Present the topic in a bit more detail with this Impact Faced By Organization Due To Mobile Threats Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Before Mobile Security, Management Plan This template is free to edit as deemed fit for your organization. Therefore download it now.
-
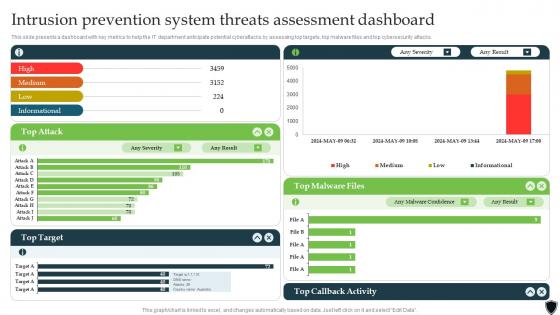 Implementing Intrusion Prevention Intrusion Prevention System Threats Assessment Cybersecurity SS
Implementing Intrusion Prevention Intrusion Prevention System Threats Assessment Cybersecurity SSThis slide presents a dashboard with key metrics to help the IT department anticipate potential cyberattacks by assessing top targets, top malware files and top cybersecurity attacks. Present the topic in a bit more detail with this Implementing Intrusion Prevention Intrusion Prevention System Threats Assessment Cybersecurity SS. Use it as a tool for discussion and navigation on Callback Activity, Malware Files, Target. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Common Ecommerce Platforms Cybersecurity Threats B2b Ecommerce Service Challenges
Common Ecommerce Platforms Cybersecurity Threats B2b Ecommerce Service ChallengesThis slide showcases current vulnerabilities in b2b ecommerce platforms, referable for businesses in recognizing major issues. It provides details about the lack of proper security testing, inadequate encryption protocols, etc.Present the topic in a bit more detail with this Common Ecommerce Platforms Cybersecurity Threats B2b Ecommerce Service Challenges. Use it as a tool for discussion and navigation on Inadequate Encryption Protocols, Proper Security Testing, Software And Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Gathering And Analyzing Threat Intelligence How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
Gathering And Analyzing Threat Intelligence How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases various data sources that are leveraged by ChatGPT for threat intelligence to tack cyber attack on organization. Various data sources for threat intelligence are security blogs, social media and security forums. Introducing Gathering And Analyzing Threat Intelligence How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security, Information, Updates, using this template. Grab it now to reap its full benefits.
-
 How ChatGPT Can Strengthen Threat How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
How ChatGPT Can Strengthen Threat How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases ChatGPT usage for threat intelligence for tackling cyber attacks on organizations. Its key elements are generate threat reports, analyze threat intelligence data and answer threat related queries. Introducing How ChatGPT Can Strengthen Threat How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Reports, Intelligence, Queries, using this template. Grab it now to reap its full benefits.
-
 Overview And Importance Of Threat How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
Overview And Importance Of Threat How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases threat intelligence overview which can help organization to tackle the cyber attack. It also highlights key importance of threat intelligence that are tackle ongoing attacks, make informed decisions, formulate threat mitigation strategies etc. Present the topic in a bit more detail with this Overview And Importance Of Threat How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS. Use it as a tool for discussion and navigation on Security, Behavior, Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building Security Awareness To Minimize Cybersecurity Threats Illustration
Building Security Awareness To Minimize Cybersecurity Threats IllustrationThis colourful PowerPoint icon is a great visual aid for building security awareness among the workforce to minimize cybersecurity threats. It is designed to help educate employees on the importance of cybersecurity and how to protect their data and systems from malicious attacks.
-
 Cybersecurity Threats Vulnerabilities In Powerpoint And Google Slides Cpb
Cybersecurity Threats Vulnerabilities In Powerpoint And Google Slides CpbPresenting Cybersecurity Threats Vulnerabilities In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cybersecurity Threats Vulnerabilities. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Healthcare Cloud Cybersecurity Threat Mitigation Plan
Healthcare Cloud Cybersecurity Threat Mitigation PlanThis slide presents healthcare cloud cybersecurity threat mitigation plan, helpful in protecting medical records and lab results from potential threats. It includes threat level, threat and solutions for facilitating technological advancement and security. Presenting our well structured Healthcare Cloud Cybersecurity Threat Mitigation Plan. The topics discussed in this slide are Healthcare Cloud Security, Threat Level, Algorithmic Process. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Solutions For Insider Threats In Healthcare Cybersecurity
Solutions For Insider Threats In Healthcare CybersecurityThis slide presents healthcare cybersecurity plan for insider threats, helpful in highlighting main concerns and appropriate solutions for tackling risks. It includes risks, type of insider threats faced, indicators of such risks and appropriate solutions. Presenting our well structured Solutions For Insider Threats In Healthcare Cybersecurity. The topics discussed in this slide are Reputational Damage, Business Operations, Patient Trust. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cybersecurity Kpi Icon Showcasing Threat Protection
Cybersecurity Kpi Icon Showcasing Threat ProtectionIntroducing our Cybersecurity Kpi Icon Showcasing Threat Protection set of slides. The topics discussed in these slides are Cybersecurity Kpi Showcasing, Threat Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cybersecurity Kpis Used By Threat Analysts
Cybersecurity Kpis Used By Threat AnalystsThis slide showcases the cybersecurity KPIs used by threat analysts which helps an organization to drive strategic decision making particularly in regard to long term objectives. It include details such as cost per incident, uptime, regulatory requirements, etc. Presenting our set of slides with Cybersecurity Kpis Used By Threat Analysts. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cost Per Incident, Regulatory Requirements.
-
 Blockchain And Cybersecurity Performing Threat Assessment For Cause Identification BCT SS V
Blockchain And Cybersecurity Performing Threat Assessment For Cause Identification BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Present the topic in a bit more detail with this Blockchain And Cybersecurity Performing Threat Assessment For Cause Identification BCT SS V Use it as a tool for discussion and navigation on Security Threats, Attack Vectors, Causes This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Blockchain And Cybersecurity Threats Imposed By Sybil Attack On Blockchain Network BCT SS V
Blockchain And Cybersecurity Threats Imposed By Sybil Attack On Blockchain Network BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Introducing Blockchain And Cybersecurity Threats Imposed By Sybil Attack On Blockchain Network BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Block Users From Network, Foster 51percent Attack, Breach Of Privacy using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V
Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction, blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V Dispense information and present a thorough explanation of Introduction To Blockchain, Blockchain Security Risks, Smart Contracts Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
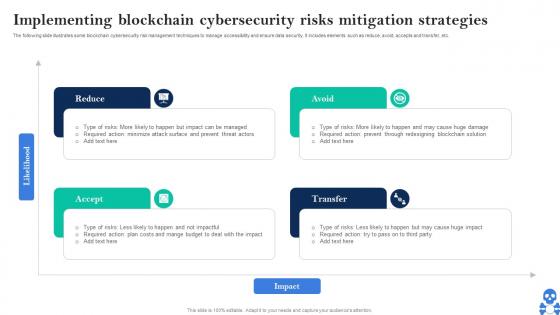 Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V
Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Introducing Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Avoid, Transfer, Accept using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SS V
Cyber Threats In Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SS V This template helps you present information on Four stages. You can also present information on Decentralized Architecture, Public Key Cryptography, Smart Contracts using this PPT design. This layout is completely editable so personaize it now
-
 Cyber Threats In Blockchain Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS V
Cyber Threats In Blockchain Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS VThe following slide showcases major cryptocurrency and blockchain cybersecurity scams throughout the globe. It includes elements such as decentralized autonomous organization DAO attack, GOX attack, plus token scams, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS V This template helps you present information on Four stages. You can also present information on DAO Hack, Quadrigacx Attack, Plus Token Scam using this PPT design. This layout is completely editable so personaize it now
-
 Cyber Threats In Blockchain Major Cybersecurity Challenges In Blockchain Technology BCT SS V
Cyber Threats In Blockchain Major Cybersecurity Challenges In Blockchain Technology BCT SS VThe following slide illustrates various issues faced by blockchain users. It includes elements such as smart contract vulnerabilities, privacy, confidentiality, weak consensus mechanism, private key management, phishing, along with its impact, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Major Cybersecurity Challenges In Blockchain Technology BCT SS V Use it as a tool for discussion and navigation on Challenges, Details, Impact This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Threats In Blockchain Overview And Workflow Of Blockchain Cybersecurity Technology BCT SS V
Cyber Threats In Blockchain Overview And Workflow Of Blockchain Cybersecurity Technology BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Overview And Workflow Of Blockchain Cybersecurity Technology BCT SS V This template helps you present information on One stages. You can also present information on Node Validates Transaction, Existing Blockchain, Transaction Completed using this PPT design. This layout is completely editable so personaize it now
-
 Cybersecurity Tips While Using Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Cybersecurity Tips While Using Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various cybersecurity tips that can be used while using ChatGPT for generating responses. Its key elements are avoid inserting sensitive data, awareness of potential bias and beware of fake applications Increase audience engagement and knowledge by dispensing information using Cybersecurity Tips While Using Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Avoid Inserting Sensitive Data, Awareness Of Potential Bias, Beware Of Fake Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How In Cybersecurity Penetration Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How In Cybersecurity Penetration Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT use cases for penetration testing which can help to prevent cyber attacks in organization. Its key elements are establish penetration testing environment, gain knowledge about testing tools, writing code for testing etc. Introducing How In Cybersecurity Penetration Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Penetration, Testing Environment, Penetration, using this template. Grab it now to reap its full benefits.
-
 Key Importance Of Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Key Importance Of Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various statistics that highlights the importance of cybersecurity in organization. It highlights stats related to malware attacks, DDos attacks, cybersecurity spending, ransomware attacks, malicious mining software etc. Present the topic in a bit more detail with this Key Importance Of Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Cybersecurity, Statistics, Importance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview And Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview And Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases cybersecurity overview that can help organization to safeguard data from different types of cyber attacks. It also highlights various benefits of cybersecurity such as safeguard data, timely incident response, reduce monetary damage etc. Deliver an outstanding presentation on the topic using this Overview And Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Dispense information and present a thorough explanation of Organization, Cybersecurity, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Cybersecurity Incident Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview Cybersecurity Incident Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases overview of incident management that can help organization in tackling cyber attacks. It also highlights various importance of incident management that are reduction in cyber attacks, decrease in system downtime, improved incident response etc. Present the topic in a bit more detail with this Overview Cybersecurity Incident Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Management, Overview, Cybersecurity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Real Time Analysis For Cybersecurity Threat Detection
Real Time Analysis For Cybersecurity Threat DetectionThis slide highlights real time analysis for identifying security issues. The purpose of this template is to assist organizations in safeguarding sensitive data and maintaining system reliability. It includes elements such as anomaly detection, threat intelligence, etc. Presenting our set of slides with Real Time Analysis For Cybersecurity Threat Detection This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Use Case, Benefits, Example
-
 Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats
Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost Deliver an outstanding presentation on the topic using this Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cloud Security, Information Security, Disaster Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 CRM Software Features To Monitor Cybersecurity Threat
CRM Software Features To Monitor Cybersecurity ThreatFollowing slide showcases monitoring cybersecurity threat CRM software features for network performance optimization. It further covers security monitoring, respond to suspicious activity and stay compliant. Introducing our premium set of slides with CRM Software Features To Monitor Cybersecurity Threat Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Monitoring, Suspicious Activity, Stay Compliant. So download instantly and tailor it with your information.
-
 Maritime Cybersecurity For Detecting Cyber Threats
Maritime Cybersecurity For Detecting Cyber ThreatsThis slide showcases training and awareness of maritime cybersecurity. The main purpose of this template is to train managers in cybersecurity. This includes cyber threats, detection capabilities, and implementation aspects. Presenting our well structured Maritime Cybersecurity For Detecting Cyber Threats. The topics discussed in this slide are Detection Capabilities, Implementation Aspects, Operational Technology. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cybersecurity Data Threat Detection Icon
Cybersecurity Data Threat Detection IconPresenting our well structured Cybersecurity Data Threat Detection Icon. The topics discussed in this slide are Cybersecurity Data, Threat Detection, Icon. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 BCP Cybersecurity Icon To Address Information Threats Effectively
BCP Cybersecurity Icon To Address Information Threats EffectivelyPresenting our set of slides with BCP Cybersecurity Icon To Address Information Threats Effectively This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on BCP Cybersecurity, Address Information, Threats Effectively
-
 Strategies To Mitigate SCADA Network Cybersecurity Threats
Strategies To Mitigate SCADA Network Cybersecurity ThreatsThis slide represents various strategies that assist companies to mitigate various SCADA network threats for enhancing data cybersecurity. It includes various threats such as hackers, malware, and employees. In Presenting our well structured Strategies To Mitigate SCADA Network Cybersecurity Threats The topics discussed in this slide are Hackers, Malware, Employees. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Impact Analysis Of Cybersecurity Threats In Retail Industry
Impact Analysis Of Cybersecurity Threats In Retail IndustryThis slide highlights impact assessment of cyber safety concerns in retail sector. The purpose of this template is to aid businesses in assessing potential consequences for protecting against threats with highest impact in timely manner. It includes elements such as payment data breach, supply chain disruption, etc. Introducing our Impact Analysis Of Cybersecurity Threats In Retail Industry set of slides. The topics discussed in these slides are Payment Data Breach, Supply Chain, Customer Data Compromise This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Potential Insider Threats In Retail Cybersecurity
Potential Insider Threats In Retail CybersecurityThis slide highlights insider cyber security vulnerabilities in retail sector. The purpose of this template is to aid businesses in identifying and managing risks for preserving the integrity of retail systems. It includes elements such as vendors, employees, collaborators, etc. Presenting our set of slides with Potential Insider Threats In Retail Cybersecurity This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vendors, Collaborators, Non Responders
-
 Threats To Cybersecurity Infrastructure In Education
Threats To Cybersecurity Infrastructure In EducationThis slide depicts the threats to cybersecurity infrastructure in education. The purpose of this slide is to help the business ensure the organization is able to prevent attacks such insider threats, phishing, ransomware, etc. Presenting our set of slides with Threats To Cybersecurity Infrastructure In Education. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Insider Threats, Malware, Phishing, Ransomware
-
 Comparison Of Cybersecurity Apps For Threat Detection
Comparison Of Cybersecurity Apps For Threat DetectionThis slide represents comparison table for cybersecurity applications for online risk mitigation including Wireshark, Metasploit, and Entersoft apps. Introducing our premium set of slides with Comparison Of Cybersecurity Apps For Threat Detection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Protocol Analysis, Security Assessment, Infrastructure Security Analysis. So download instantly and tailor it with your information.
-
 Best Practices For Integrating Threat Intelligence With Cybersecurity
Best Practices For Integrating Threat Intelligence With CybersecurityThis slide depicts the best practices for integrating cyber threat intelligence with cybersecurity. The purpose of this slide is to help the business successfully integrate threat intelligence with cybersecurity. It includes automation of data processing,, establishment of threat intelligence sharing policies, etc. Presenting our set of slides with Best Practices For Integrating Threat Intelligence With Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ensure Integration, Current System, Automate Data Processing
-
 Cyber Threat Intelligence Icon To Enhance Cybersecurity
Cyber Threat Intelligence Icon To Enhance CybersecurityPresenting our set of slides with Cyber Threat Intelligence Icon To Enhance Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Threat Intelligence Icon, Enhance Cybersecurity
-
 Sources For Cyber Threat Intelligence During Cybersecurity
Sources For Cyber Threat Intelligence During CybersecurityThis slide showcases the sources for cyber threat intelligence during cyber security. The purpose of this slide is to establish rigid security through the use of cyber threat intelligence. It includes open source intelligence, internal intelligence, etc. Presenting our well structured Sources For Cyber Threat Intelligence During Cybersecurity The topics discussed in this slide are CTI Information Source, Description, Examples This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Use Cases Of Cyber Threat Intelligence Framework To Establish Cybersecurity
Use Cases Of Cyber Threat Intelligence Framework To Establish CybersecurityThis slide depicts the use cases of cyber threat intelligence framework to establish cybersecurity. The purpose of this slide is to help the business appropriately utilize cyber threat intelligence framework in order to enhance its network security. It includes cyber risk management, security operations center, etc. Introducing our premium set of slides with Use Cases Of Cyber Threat Intelligence Framework To Establish Cybersecurity Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Risk Management, Vulnerability Management, Security Operations Center So download instantly and tailor it with your information.
-
 Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SS
Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SSThis slide showcases vulnerability assessment disclosure and threat intelligence on internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about continuous monitoring, correlation, disclosure, etc. Introducing Monitor Vulnerability Disclosure And Threat Intelligence Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Continuous Monitoring, Correlation With Metadata, Disclosure Implementation, using this template. Grab it now to reap its full benefits.
-
 Bfsi Sector Cybersecurity Threats In Big Data Analytics
Bfsi Sector Cybersecurity Threats In Big Data AnalyticsThis slide highlights cybersecurity in BFSI sector big data analytics threats. This includes phishing attacks, cyber physical attacks, internet of things attacks and threats by third party involved. Introducing our premium set of slides with name Bfsi Sector Cybersecurity Threats In Big Data Analytics. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Physical Attacks, Internet Of Things Attacks, Threats By Third Party Involved. So download instantly and tailor it with your information.
-
 Operation Continuity Plan For Cybersecurity Threats
Operation Continuity Plan For Cybersecurity ThreatsThis slide represents an operation continuity plan for businesses including cybersecurity threats such as injections, broken authentication, and cross-site scripting. Presenting our well structured Operation Continuity Plan For Cybersecurity Threats. The topics discussed in this slide are Supervisors, Broken Authentication, Cross-Site Scripting. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 4 Threats To Cybersecurity In Automobile Industry
4 Threats To Cybersecurity In Automobile IndustryThis slide highlights cyber safety concerns in automotive sector. The purpose of this slide is to provide businesses with the required knowledge regarding various malware attacks in vehicles. It includes elements such as software, unauthorized access, etc. Presenting our set of slides with 4 Threats To Cybersecurity In Automobile Industry This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Unauthorized Access, Supply Chain, Software
-
 Cybersecurity Policy Icon Showcasing Threat Protection
Cybersecurity Policy Icon Showcasing Threat ProtectionIntroducing our Cybersecurity Policy Icon Showcasing Threat Protection set of slides. The topics discussed in these slides are Cybersecurity Policy Icon Showcasing Threat ProtectionThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SS
Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding impact of data loss due to threat agents such as insider threat, social engineering, malware, specific enterprise cyber threats, etc.Present the topic in a bit more detail with this Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SS. Use it as a tool for discussion and navigation on Insider Threat, Social Engineering, Maintenance Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Mitigating Cybersecurity Threats With Data Loss Prevention Solutions
Mitigating Cybersecurity Threats With Data Loss Prevention SolutionsThis slide represents various data loss prevention strategies that assist companies in mitigating multiple cybersecurity threats to enhance information protection. It includes threats such as extrusion, insider threats, and unintended exposure. Introducing our Mitigating Cybersecurity Threats With Data Loss Prevention Solutions set of slides. The topics discussed in these slides are Extrusion, Insider Threats, Unintended Exposure. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices For Minimizing Risks Of Insider Threats IT Security Awareness Training Cybersecurity SS
Best Practices For Minimizing Risks Of Insider Threats IT Security Awareness Training Cybersecurity SSThis slide represents best practices for mitigating threats that originate from within the targeted organization. It includes best practices such as perform enterprise-wide risk assessment etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Minimizing Risks Of Insider Threats IT Security Awareness Training Cybersecurity SS. This template helps you present information on four stages. You can also present information on Enforce Policies And Controls, Establish Physical Security, Harden Network Perimeter Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.




