Powerpoint Templates and Google slides for Cyber Security Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Addressing cyber threats various industries cyber security risk management
Addressing cyber threats various industries cyber security risk managementThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Introducing Addressing Cyber Threats Various Industries Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Industry, Healthcare, Manufacturing, Government, Energy, using this template. Grab it now to reap its full benefits.
-
 Addressing ways to handling financial threats cyber security risk management
Addressing ways to handling financial threats cyber security risk managementThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Financial Threats Cyber Security Risk Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Abundant Cash Requirement, Key Financial Statements, Preparing Aged Debtors Trial Balance, using this template. Grab it now to reap its full benefits.
-
 Budget for effective threat management workplace cyber security risk management
Budget for effective threat management workplace cyber security risk managementFirm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Present the topic in a bit more detail with this Budget For Effective Threat Management Workplace Cyber Security Risk Management. Use it as a tool for discussion and navigation on Incident Management, Risk Management, Client Onboarding Process, Document Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber security risk management addressing indicators associated to insider threats
Cyber security risk management addressing indicators associated to insider threatsThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Introducing Cyber Security Risk Management Addressing Indicators Associated To Insider Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Demeanor, goals, Traits, Data Exfiltration, Financial Stress, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management addressing natural calamities posing threat organization
Cyber security risk management addressing natural calamities posing threat organizationThis slide provides details regarding natural calamities posing as threat to organization and threat management checklist during nature crisis. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Addressing Natural Calamities Posing Threat Organization. Dispense information and present a thorough explanation of Various Nature Threats, Hurricanes, Earthquake, Temporary Water Sources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber security risk management addressing threat management team training schedule
Cyber security risk management addressing threat management team training scheduleThe threat management team needs to have strong critical and creative thinking skills so that they become capable in taking key decisions without complete or conflicting information under immense tensed situations. The team will be trained by experts who will also use scenario based activities and costing will be per employee basis. Present the topic in a bit more detail with this Cyber Security Risk Management Addressing Threat Management Team Training Schedule. Use it as a tool for discussion and navigation on Hypotheticals, Workshops, Field Exercises, Audience,Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber security risk management comparative assessment various threat agents
Cyber security risk management comparative assessment various threat agentsThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Comparative Assessment Various Threat Agents. Dispense information and present a thorough explanation of Insider Threat, Social Engineering, Threat Agents, Cyber Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber security risk management contingency plan for cyber threat handling
Cyber security risk management contingency plan for cyber threat handlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Cyber Security Risk Management Contingency Plan For Cyber Threat Handling to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, System Backups, Vendors Coordination, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management determine sequence phases for threat attack
Cyber security risk management determine sequence phases for threat attackThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Increase audience engagement and knowledge by dispensing information using Cyber Security Risk Management Determine Sequence Phases For Threat Attack. This template helps you present information on four stages. You can also present information on Reconnaissance, Weaponization, Exploitation, Delivery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber security risk management determine several threat actors profile
Cyber security risk management determine several threat actors profileThis slide provides details regarding several threat actors profile such as cyber criminal and hacktivists and addressing them on parameters such as motive, intent, capability, action, target victim, etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Determine Several Threat Actors Profile. Dispense information and present a thorough explanation of Cyber Criminal, Targeted Asset, Objective using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber security risk management determine threat management team
Cyber security risk management determine threat management teamThe threat management team generally comprise of senior management personnel that have authority and resources to accelerate the companys internal incident response. They will be responsible in managing human impacts both employees and community, company reputation, share values, and corporate assets. Introducing Cyber Security Risk Management Determine Threat Management Team to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Management Head, Security Manager, Crisis Management Advisor, Medical Advisor, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management determine threat scenario analysis
Cyber security risk management determine threat scenario analysisThis slide provides details regarding threat scenario assessment by understanding various phases of threat actor attack on victim. Increase audience engagement and knowledge by dispensing information using Cyber Security Risk Management Determine Threat Scenario Analysis. This template helps you present information on two stages. You can also present information on Threat Scenario, Threat Campaign, Exploitation, Command And Control, Actions And Objectives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber security risk management different kinds of insider digital threats
Cyber security risk management different kinds of insider digital threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Cyber Security Risk Management Different Kinds Of Insider Digital Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Insider, Negligent Or Careless Insider, Third Party Insider, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management impact analysis of successful threat management
Cyber security risk management impact analysis of successful threat managementThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Increase audience engagement and knowledge by dispensing information using Cyber Security Risk Management Impact Analysis Of Successful Threat Management. This template helps you present information on four stages. You can also present information on Focus Area, Past State, Present State, Benefit, Customer Satisfaction Rate using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber security risk management key activities checklist associated to insider threat
Cyber security risk management key activities checklist associated to insider threatThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Key Activities Checklist Associated To Insider Threat. Dispense information and present a thorough explanation of Plan And Collet, Review And Analyze, Develop Strategic Framework, Track Present Inventory using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber security risk management selecting secured threat management software
Cyber security risk management selecting secured threat management softwareThis slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Present the topic in a bit more detail with this Cyber Security Risk Management Selecting Secured Threat Management Software. Use it as a tool for discussion and navigation on Centralized Platform, Security Incident Forms, Access Rights, API Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber security risk management statistics associated to workplace threats
Cyber security risk management statistics associated to workplace threatsThis slide provides details regarding statistics associated to workplace threats that firms face in terms of data records theft, workplace violence, financial phishing, etc. Introducing Cyber Security Risk Management Statistics Associated To Workplace Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Attacks Costs, Organizations Face, Data Records, Business, Financial, using this template. Grab it now to reap its full benefits.
-
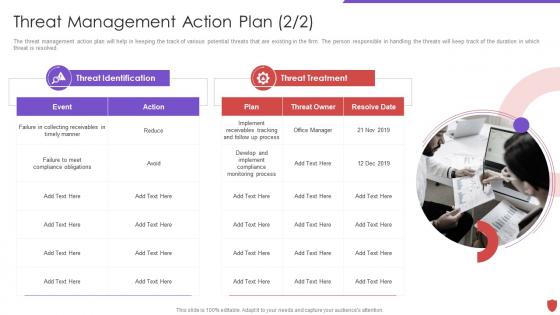 Cyber security risk management threat management action plan
Cyber security risk management threat management action planThe threat management action plan will help in keeping the track of various potential threats that are existing in the firm. The person responsible in handling the threats will keep track of the duration in which threat is resolved. Introducing Cyber Security Risk Management Threat Management Action Plan to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Threat Identification, Threat Treatment, Plan, Threat Owner, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management various types of workplace violence and threats
Cyber security risk management various types of workplace violence and threatsThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Introducing Cyber Security Risk Management Various Types Of Workplace Violence And Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Threats Or Threatening Behavior, Physical Assault, Property Damage, using this template. Grab it now to reap its full benefits.
-
 Determine sequence phases for threat attack contd cyber security risk management
Determine sequence phases for threat attack contd cyber security risk managementThis slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. Introducing Determine Sequence Phases For Threat Attack Contd Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Installation, Command And Control, Actions And Objectives, Covering Tracks, using this template. Grab it now to reap its full benefits.
-
 Impact analysis for effective threat management in cyber security risk management
Impact analysis for effective threat management in cyber security risk managementThis slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Introducing Impact Analysis For Effective Threat Management In Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Focus Areas, Actual Access Violations, Access Rights Authorized, using this template. Grab it now to reap its full benefits.
-
 Threat management action plan cyber security risk management
Threat management action plan cyber security risk managementThe threat management action plan will help in keeping the track of potential threats that are existing and what are their level, what are the resources required to handle them. The person responsible in handling the threat will keep track of the threat resolve duration and will check whether the threat is treated or not. Present the topic in a bit more detail with this Threat Management Action Plan Cyber Security Risk Management. Use it as a tool for discussion and navigation on Potential Risk, Risk Level, Action, Responsible Person, Risk Treated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Network Security Cyber Threat Landscape In Network Security
Network Security Cyber Threat Landscape In Network SecurityThis slide depicts the cyber threat landscape based on cybercriminal roles actors and the impacts of successful cyberattacks on business. Deliver an outstanding presentation on the topic using this Network Security Cyber Threat Landscape In Network Security. Dispense information and present a thorough explanation of Cyber Threat Landscape In Network Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Cyber Threat Landscape In Information Technology Security
Information Technology Security Cyber Threat Landscape In Information Technology SecurityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Deliver an outstanding presentation on the topic using this Information Technology Security Cyber Threat Landscape In Information Technology Security. Dispense information and present a thorough explanation of Landscape, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Small Business Cyber Security Threats Ppt Powerpoint Presentation Inspiration Themes Cpb
Small Business Cyber Security Threats Ppt Powerpoint Presentation Inspiration Themes CpbPresenting our Small Business Cyber Security Threats Ppt Powerpoint Presentation Inspiration Themes Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Small Business Cyber Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Agenda For Building A Security Awareness Program To Educate Employees About Cyber Threats
Agenda For Building A Security Awareness Program To Educate Employees About Cyber ThreatsIntroducing Agenda For Building A Security Awareness Program To Educate Employees About Cyber Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Amongst Employees, Awareness Program, Department Plan, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Building A Security Awareness Program To Educate Employees About Cyber Threats
Icons Slide For Building A Security Awareness Program To Educate Employees About Cyber ThreatsIntroducing our well researched set of slides titled Icons Slide For Building A Security Awareness Program To Educate Employees About Cyber Threats. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Various Cyber Security Threats And Strategies To Manage Network Service
Various Cyber Security Threats And Strategies To Manage Network ServiceThis slide highlights different types of cybersecurity threat such as malware, phishing, trojan horse and rootkit. The template also provides information about various strategies which will assist IT department to manage its network services. Introducing our premium set of slides with Various Cyber Security Threats And Strategies To Manage Network Service. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strategies Overcome Threats, IT Security Services, Provide Security Awareness. So download instantly and tailor it with your information.
-
 Cyber Security Threat Assessment Checklist With Solution
Cyber Security Threat Assessment Checklist With SolutionThe following slide highlights the cyber security threat assessment checklist with solution to assist management in decision making, id depicts threat, vulnerability, asset, consequences, risks and solution to control the risk. Introducing our Cyber Security Threat Assessment Checklist With Solution set of slides. The topics discussed in these slides are System Threat, Data Threat, Cloud Security Threat. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Threat Intelligence Cycle
Cyber Security Threat Intelligence CycleThe following slide highlights the cyber security threat intelligence cycle illustrating direction, collection, processing, analysis, reporting and action for quick fix of cyber threat and incident of breach to minimize the downtime of system. Introducing our premium set of slides with name Cyber Security Threat Intelligence Cycle. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Direction, Collection, Processing, Analysis, Reporting. So download instantly and tailor it with your information.
-
 Cyber Security Threat Mitigation Strategies
Cyber Security Threat Mitigation StrategiesThe following slide highlights the six strategies for cyber security threat mitigation illustrating risk assessment, access control, security solution, patch management, traffic monitoring and incident response. Presenting our set of slides with name Cyber Security Threat Mitigation Strategies. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Assessment, Patch Management, Traffic Monitoring.
-
 IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan
IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Increase audience engagement and knowledge by dispensing information using IT Risk Management Strategies Prioritized Cyber Security Threats With Risk Mitigation Plan. This template helps you present information on one stages. You can also present information on Threat, Risk, Risk Priority, Risk Reduction Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation Plan
Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation PlanThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Enterprise Risk Management Prioritized Cyber Security Threats With Risk Mitigation Plan. Use it as a tool for discussion and navigation on Threat, Risk, Risk Priority, Risk Reduction Timeline. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Threats In Powerpoint And Google Slides Cpb
Cyber Security Threats In Powerpoint And Google Slides CpbPresenting our Cyber Security Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Cyber Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems
Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Threat Risk, Risk Mitigation Plan, Risk Owner. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Threats And Key Performance Indicators
Cyber Security Threats And Key Performance IndicatorsThis slide covers the information related to the various types of cyber threats and the key performance indicators used by the organization for dealing with these security breaches. Introducing our Cyber Security Threats And Key Performance Indicators set of slides. The topics discussed in these slides are Security Incidents, Intrusion Attempts, Unidentified Devices. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Threat Facts Figures And Statistics Security Incident Response Playbook
Cyber Threat Facts Figures And Statistics Security Incident Response PlaybookThis slide portrays statistical information about cyber threats. Information covered is related data breach, ransomware attacks, cyberthreat complaints and phishing attack. Increase audience engagement and knowledge by dispensing information using Cyber Threat Facts Figures And Statistics Security Incident Response Playbook. This template helps you present information on six stages. You can also present information on Cyberattacks, Ransomware, Statistics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems
Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Mitigation Plan, Prioritized, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Threats Challenges In Powerpoint And Google Slides Cpb
Cyber Security Threats Challenges In Powerpoint And Google Slides CpbPresenting Cyber Security Threats Challenges In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Threats Challenges. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Future Cyber Security Threats In Powerpoint And Google Slides Cpb
Future Cyber Security Threats In Powerpoint And Google Slides CpbPresenting Future Cyber Security Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Future Cyber Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Business Cyber Security Program For Threat Prevention
Business Cyber Security Program For Threat PreventionThis slide covers business cyber security program for threat prevention which includes identify, protect, detect, respond and recover. Presenting our well structured Business Cyber Security Program For Threat Prevention. The topics discussed in this slide are Business Cyber, Security Program, Threat Prevention. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 New Cyber Security Threats In Powerpoint And Google Slides Cpb
New Cyber Security Threats In Powerpoint And Google Slides CpbPresenting our New Cyber Security Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on New Cyber Security Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Threats Detection Techniques Ppt Powerpoint Presentation Professional Background
Cyber Security Threats Detection Techniques Ppt Powerpoint Presentation Professional BackgroundThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Introducing Cyber Security Threats Detection Techniques Ppt Powerpoint Presentation Professional Background to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Threat Intelligence, Intruder Traps, Threat Hunting, using this template. Grab it now to reap its full benefits.
-
 Cyber Threat Prevention And Security Process
Cyber Threat Prevention And Security ProcessThis slide shows four steps to provide and assure protection against cyber threats. It includes steps secure perimeter, protect users, network segmentation, determine and control risks. Introducing our premium set of slides with name Cyber Threat Prevention And Security Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Secure Perimeter, Smart Network Segmentation, Determine And Control. So download instantly and tailor it with your information.
-
 Threat Modelling Process Of Cyber Security Program
Threat Modelling Process Of Cyber Security ProgramThis slide shows threat modelling process to identify gaps and improve efficiency of cyber security program. It contains five steps select digital asset, identify attack scenarios, evaluate existing controls, assess residual risks and construct business case. Presenting our set of slides with name Threat Modelling Process Of Cyber Security Program. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Modelling, Cyber Security, Assess Residual Risk .
-
 Cyber Security Strategy Best Practices To Defend Against Threats
Cyber Security Strategy Best Practices To Defend Against ThreatsThis slide represents cyber security strategy best practices to defend against threats such a development of insider threat program, training employees, maintaining compliance etc. Presenting our set of slides with name Cyber Security Strategy Best Practices To Defend Against Threats. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Training Employees, Initiating Phishing Stimulations, Maintaining Compliance.
-
 Emerging Cyber Security Threats In Powerpoint And Google Slides Cpb
Emerging Cyber Security Threats In Powerpoint And Google Slides CpbPresenting Emerging Cyber Security Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Emerging Cyber Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Security Checklist To Mitigate Threats Of Attack
Cyber Security Checklist To Mitigate Threats Of AttackThe given slide provides the key activities to be done to alleviate the effects of cyber threats. It includes managing social media profiles, backing up the data, crosschecking privacy and security settings etc. Introducing our premium set of slides with Cyber Security Checklist To Mitigate Threats Of Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Checklist, Mitigate Threats Attack. So download instantly and tailor it with your information.
-
 E Security Steps To Mitigate Cyber Threats
E Security Steps To Mitigate Cyber ThreatsThis slide mentions the e-security steps implemented to mitigate cyber threats and protect user data. It includes using strong password, device protection, additional authentication, storing essential data and reviewing third party integrations. Introducing our premium set of slides with E Security Steps To Mitigate Cyber Threats. Elucidate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Additional Authentication, Device Protection, Store Essential Data. So download instantly and tailor it with your information.
-
 Security Against Cyber Threats In Healthcare Sector
Security Against Cyber Threats In Healthcare SectorThis slide covers the details related to the healthcare assets and its security measures. The purpose of this template is to define cyber security in healthcare sector which involves the protection of electronic information and assets from unauthorized access, use and disclosure. It also includes elements such as emails, physical security and legal systems. Introducing our premium set of slides with name Security Against Cyber Threats In Healthcare Sector. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Emails, Physical Security, Legacy Systems. So download instantly and tailor it with your information.
-
 Cyber Security Threats Detection Techniques Incident Response Strategies Deployment
Cyber Security Threats Detection Techniques Incident Response Strategies DeploymentThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Introducing Cyber Security Threats Detection Techniques Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Threat, Analytics, Intruder, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident Management
Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident ManagementThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Present the topic in a bit more detail with this Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident Management. Use it as a tool for discussion and navigation on Intruder Traps, Attacker And User Behavior Analytics, Threat Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Cyber Security Threats Detection Techniques
Cyber Security Attacks Response Plan Cyber Security Threats Detection TechniquesThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Security Threats Detection Techniques. Dispense information and present a thorough explanation of Cyber Security Threats, Detection Techniques, Compromised Credentials using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Threats Detection Techniques Deploying Computer Security Incident Management
Cyber Security Threats Detection Techniques Deploying Computer Security Incident ManagementThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc.Present the topic in a bit more detail with this Cyber Security Threats Detection Techniques Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Threat Intelligence, Access Regularly, Undercovers Intruders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Infra Security Icon For Eliminating Cyber Threats
Infra Security Icon For Eliminating Cyber ThreatsIncrease audience engagement and knowledge by dispensing information using Infra Security Icon For Eliminating Cyber Threats. This template helps you present information on four stages. You can also present information on Infra Security, Icon Eliminating, Cyber Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing Asset Security Categorization Cyber Threats Management To Enable Digital Assets Security
Addressing Asset Security Categorization Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Present the topic in a bit more detail with this Addressing Asset Security Categorization Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Categorization, Confidentiality, Availability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing Cyber Threats In Various Cyber Threats Management To Enable Digital Assets Security
Addressing Cyber Threats In Various Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Deliver an outstanding presentation on the topic using this Addressing Cyber Threats In Various Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Manufacturing, Government, Healthcare using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing Indicators Associated Cyber Threats Management To Enable Digital Assets Security
Addressing Indicators Associated Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Present the topic in a bit more detail with this Addressing Indicators Associated Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Unauthorized, Business, Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing Internal And External Sources Cyber Threats Management To Enable Digital Assets Security
Addressing Internal And External Sources Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Deliver an outstanding presentation on the topic using this Addressing Internal And External Sources Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Targeted Intelligence, Malware Intelligence, Reputation Intelligence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Categorizing System Risk Associated With Cyber Threats Management To Enable Digital Assets Security
Categorizing System Risk Associated With Cyber Threats Management To Enable Digital Assets SecurityThis slide portrays information regarding system risk categorizations to enable cyber security. The categories assigned to system category is based on system confidentiality, integrity and availability. Deliver an outstanding presentation on the topic using this Categorizing System Risk Associated With Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Categorizing, Confidentiality, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.





