Powerpoint Templates and Google slides for Cyber Security Apps
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Icon of mobile app protected with cyber security software
Icon of mobile app protected with cyber security softwarePresenting this set of slides with name Icon Of Mobile App Protected With Cyber Security Software. This is a three stage process. The stages in this process are Icon Of Mobile App Protected With Cyber Security Software. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Elements of cyber security application security ppt powerpoint presentation diagrams
Elements of cyber security application security ppt powerpoint presentation diagramsThis slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Increase audience engagement and knowledge by dispensing information using Elements Of Cyber Security Application Security Ppt Powerpoint Presentation Diagrams. This template helps you present information on five stages. You can also present information on Input Validation, Authorization, Session Management, Parameter Tampering, Encryption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Cyber Security Icon
Information Technology Cyber Security IconIntroducing our premium set of slides with Information Technology Cyber Security Icon. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Technology, Cyber Security. So download instantly and tailor it with your information.
-
 Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt Brochure
Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt BrochureThis slide outlines the tools used to achieve cyber security goals such as confidentiality, integrity, and availability. The tools for confidentiality include encryption, access control, authentication, authentication, authorization, and physical security. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Tools Used For Cyber Security Goals Ppt Brochure. This template helps you present information on one stage. You can also present information on Tools For Confidentiality, Tools For Integrity, Tools For Availability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Comparative Assessment Of Cyber Security Incident Response Tools
Comparative Assessment Of Cyber Security Incident Response ToolsThis slide covers comparative assessment of cyber security incident response tools. It involves features such as advanced threat hunting ability, net flow analysis, user behavior analytics and superior forensic analysis. Introducing our premium set of slides with name Comparative Assessment Of Cyber Security Incident Response Tools. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Comparative Assessment, Cyber Security, Incident Response Tools. So download instantly and tailor it with your information.
-
 Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt Structure
Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt StructureThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc. Increase audience engagement and knowledge by dispensing information using Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt Structure. This template helps you present information on one stage. You can also present information on Fights Vulnerabilities, Implementing, Application Firewall using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Operational Technology Cyber Security In Powerpoint And Google Slides Cpb
Operational Technology Cyber Security In Powerpoint And Google Slides CpbPresenting our Operational Technology Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Operational Technology Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Applications Of ML In Cyber Security Analytics
Applications Of ML In Cyber Security AnalyticsThe following slide highlights threat identification, antivirus software, modeling, AI threats, and email monitoring to showcase the applications of ML in cybersecurity analytics. It helps organizations enhance cyber threat detection and mitigation capabilities through advanced machine learning techniques. Presenting our set of slides with Applications Of ML In Cyber Security Analytics. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identification, Antivirus, Behavior.
-
 Emerging Technologies Objectives Of Cyber Security Technology
Emerging Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing Emerging Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, using this template. Grab it now to reap its full benefits.
-
 Current Trending Technologies Objectives Of Cyber Security Technology
Current Trending Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing Current Trending Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Cyber Security Technology, Data Protection, Integrity And Availability, using this template. Grab it now to reap its full benefits.
-
 Select Tools To Reduce Cyber Security Failure Cyber Risk Assessment
Select Tools To Reduce Cyber Security Failure Cyber Risk AssessmentThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Introducing Select Tools To Reduce Cyber Security Failure Cyber Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Suspicious Activities, Select Tools, Cyber Security Failure using this template. Grab it now to reap its full benefits.
-
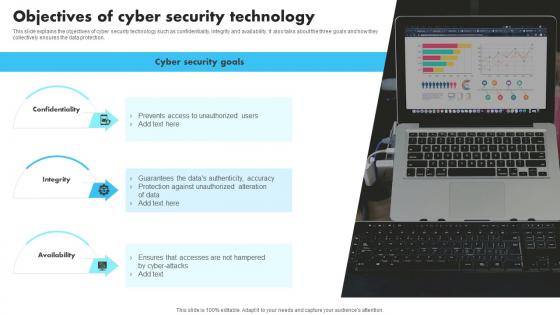 New Technologies Objectives Of Cyber Security Technology
New Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing New Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Technology, Availability, using this template. Grab it now to reap its full benefits.
-
 Role Of Saas Applications In Cyber Security
Role Of Saas Applications In Cyber SecurityThis slide represents SaaS apps significance to cyber security. It aims to ensure continuous monitoring and updates to mitigate risks and protect sensitive data within applications. It includes various aspects such as authentication, leveraging data, etc. Introducing our premium set of slides with Role Of Saas Applications In Cyber Security Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication, Enhanced Security, High Scalability, Strong Encryption. So download instantly and tailor it with your information.
-
 Icon For Role Of 5g Technology In Automotive Cyber Security
Icon For Role Of 5g Technology In Automotive Cyber SecurityIntroducing our premium set of slides with Icon For Role Of 5g Technology In Automotive Cyber Security Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Role, 5G Technology In Automotive, Cyber Security So download instantly and tailor it with your information.
-
 Advantage Of Triage Technology In Cyber Security
Advantage Of Triage Technology In Cyber SecurityThis slide represents advantage of triage technology which assists to prioritize levels to task and determine most effective order to deal with them. It includes advantage of triage technology in cyber security such as efficient utilization of resources, prioritize critical data, etc Presenting our set of slides with name Advantage Of Triage Technology In Cyber Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Utilization Of Resources, Prioritize Critical Data, Resolve Threats Speedily
-
 Cyber Security Mesh Applications For Business
Cyber Security Mesh Applications For BusinessThe following slide features key elements like IAM support, MSSPS, identity-proofing tools, standards, and demographic bias in illustrating the diverse applications of cybersecurity mesh for business. This aids in understanding its potential impact on security and operations. Presenting our set of slides with Cyber Security Mesh Applications For Business This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mesh Supporting Iam Requests, Identity Life Cycle, Decentralized Identity Standards
-
 ATP Cyber Technology Security Icon
ATP Cyber Technology Security IconPresenting our set of slides with name ATP Cyber Technology Security Icon. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on ATP Cyber Technology, Security Icon.
-
 Ai Technology Implementation Icon For Robust OT Cyber Security
Ai Technology Implementation Icon For Robust OT Cyber SecurityPresenting our set of slides with Ai Technology Implementation Icon For Robust OT Cyber Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on AI Technology Implementation Icon, Robust OT Cyber Security
-
 Types Of Endpoint Cyber Security Tools Building Next Generation Endpoint Security Cybersecurity SS
Types Of Endpoint Cyber Security Tools Building Next Generation Endpoint Security Cybersecurity SSPresent the topic in a bit more detail with this Types Of Endpoint Cyber Security Tools Building Next Generation Endpoint Security Cybersecurity SS. Use it as a tool for discussion and navigation on Mobile Threat Defense, Endpoint Protection Platform, Advanced Threat Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.


