Powerpoint Templates and Google slides for Computers.
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Detailed SWOT Analysis For A Computer Software Business Plan BP SS
Detailed SWOT Analysis For A Computer Software Business Plan BP SSThe slide includes the strengths, weaknesses, opportunities, and threats analysis of the computer shop. It helps in building what the company does well, and what it lacks, seizing new openings, and minimizing risks. Introducing Detailed SWOT Analysis For A Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, using this template. Grab it now to reap its full benefits.
-
 Determining Growth Drivers For A Computer Software Business Plan BP SS
Determining Growth Drivers For A Computer Software Business Plan BP SSThis slide caters to details about various growth drivers resulting in the firms progress in terms of technological advancements, e commerce popularity, cloud computing and mobile devices etc. Increase audience engagement and knowledge by dispensing information using Determining Growth Drivers For A Computer Software Business Plan BP SS. This template helps you present information on four stages. You can also present information on Technological, Computing, Devices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Discounted Cash Flow Valuation Of The Computer Software Business Plan BP SS
Discounted Cash Flow Valuation Of The Computer Software Business Plan BP SSThe purpose of this slide is to calculate the amount of money an investor would get from an investment after adjusting for the time value of money. It covers things like risk free return, free cash flow to the company, NPV value of FCFF and terminal year, and so on. Deliver an outstanding presentation on the topic using this Discounted Cash Flow Valuation Of The Computer Software Business Plan BP SS. Dispense information and present a thorough explanation of Discounted, Valuation, Computer using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Effective Revenue Generation Model Computer Software Business Plan BP SS
Effective Revenue Generation Model Computer Software Business Plan BP SSThe slide shows the effective revenue model of the computer shop, which displays the cost incurred and the various sources of income. The revenue is calculated on the basis of the number of customers visited and the churn rate. Introducing Effective Revenue Generation Model Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Effective, Revenue, Generation, using this template. Grab it now to reap its full benefits.
-
 Evaluating Client Journey Through A Sales Computer Software Business Plan BP SS
Evaluating Client Journey Through A Sales Computer Software Business Plan BP SSThis slide highlights customer journey mapping to track users actions and key touch points across levels such as awareness, consideration, conversion, loyalty. It enables organizations to see how well each step of the sales process is working. Increase audience engagement and knowledge by dispensing information using Evaluating Client Journey Through A Sales Computer Software Business Plan BP SS. This template helps you present information on five stages. You can also present information on Awareness, Interest, Conversion using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
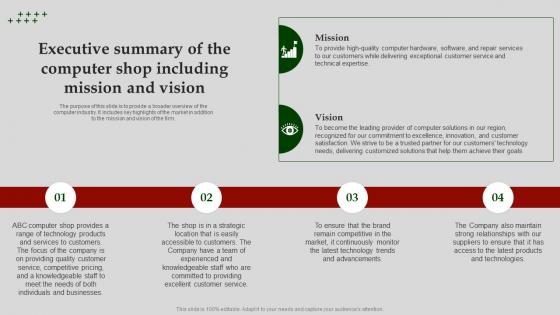 Executive Summary Of The Computer Shop Computer Software Business Plan BP SS
Executive Summary Of The Computer Shop Computer Software Business Plan BP SSThe purpose of this slide is to provide a broader overview of the computer industry. It includes key highlights of the market in addition to the mission and vision of the firm. Introducing Executive Summary Of The Computer Shop Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Computer, Location, Continuously, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Computer Software Business Plan BP SS
Icons Slide For Computer Software Business Plan BP SSIntroducing our well researched set of slides titled Icons Slide For Computer Software Business Plan BP SS. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Implementing Yearly Milestones For Computer Software Business Plan BP SS
Implementing Yearly Milestones For Computer Software Business Plan BP SSThe purpose of this slide is to facilitate managers to convey project progress updates to stakeholders and get their approvals. The slide portrays key milestones of the computer shop to be achieved in the year 1, year 3, and years 5 onwards. Introducing Implementing Yearly Milestones For Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Implementing, Successful, Growth, using this template. Grab it now to reap its full benefits.
-
 Key Abbreviations Used In The Plan Computer Software Business Plan BP SS
Key Abbreviations Used In The Plan Computer Software Business Plan BP SSThe purpose of this slide is to highlight the shorter version of existing words to save time and take up less space. Introducing Key Abbreviations Used In The Plan Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Growth, Resource, Director, using this template. Grab it now to reap its full benefits.
-
 Key Financial Assumptions Of The Computer Software Business Plan BP SS
Key Financial Assumptions Of The Computer Software Business Plan BP SSThis slide provides a glimpse of important financial assumptions that are to be made while setting up the firm in terms of income, expense, and balance sheet. The computations are based on market trends and conditions prevailing in the computer industry. Increase audience engagement and knowledge by dispensing information using Key Financial Assumptions Of The Computer Software Business Plan BP SS. This template helps you present information on one stages. You can also present information on Financial, Organization, Assumptions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Restraints Hampering The Growth Computer Software Business Plan BP SS
Major Restraints Hampering The Growth Computer Software Business Plan BP SSThe purpose of this slide is to guide stakeholders about the problems prevailing in the industry. It covers various challenges such as cost overrun Introducing Major Restraints Hampering The Growth Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Disruptions, Competition, Technological, using this template. Grab it now to reap its full benefits.
-
 Porters Framework A Detailed Five Forces Computer Software Business Plan BP SS
Porters Framework A Detailed Five Forces Computer Software Business Plan BP SSThe slide highlights porters framework and its implications in the computer industry. The key points included are the threat of new entrants and substitutes, rivalry among the competitors, and the bargaining power of the suppliers and buyers. Introducing Porters Framework A Detailed Five Forces Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Entrants, Suppliers, Substitutes, using this template. Grab it now to reap its full benefits.
-
 TAM SAM SOM Of The Target Segment Computer Software Business Plan BP SS
TAM SAM SOM Of The Target Segment Computer Software Business Plan BP SSThe purpose of this slide is to depict the market potential of the computer industry in terms of TAM, SAM, and SOM to assist startups and enterprise firms alike in evaluating the feasibility of their service and giving them the capacity to solicit investors with a high degree of confidence in return. Introducing TAM SAM SOM Of The Target Segment Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Available, Serviceable, Market, using this template. Grab it now to reap its full benefits.
-
 Unique Value Proposition Of A Computer Software Business Plan BP SS
Unique Value Proposition Of A Computer Software Business Plan BP SSThe purpose of this slide is to highlight the key success factors of the computer which leverage them with a competitive edge in the market. It covers expertise and knowledge, customer service, quality products and services, competitive pricing etc. Introducing Unique Value Proposition Of A Computer Software Business Plan BP SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Knowledge, Services, Convenience, using this template. Grab it now to reap its full benefits.
-
 Computation Capital Gains Tax In Powerpoint And Google Slides Cpb
Computation Capital Gains Tax In Powerpoint And Google Slides CpbPresenting our Computation Capital Gains Tax In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Computation Capital Gains Tax. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Taxes Capital Gains Computed In Powerpoint And Google Slides Cpb
Taxes Capital Gains Computed In Powerpoint And Google Slides CpbPresenting our Taxes Capital Gains Computed In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Taxes Capital Gains Computed. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Saved Credit Cards Computer In Powerpoint And Google Slides Cpb
Saved Credit Cards Computer In Powerpoint And Google Slides CpbPresenting Saved Credit Cards Computer In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Saved Credit Cards Computer. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Computer Chip Manufacturer Stocks In Powerpoint And Google Slides Cpb
Computer Chip Manufacturer Stocks In Powerpoint And Google Slides CpbPresenting Computer Chip Manufacturer Stocks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Computer Chip Manufacturer Stocks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Application Of Computer Vision In Impact Of Ai Tools In Industrial AI SS V
Application Of Computer Vision In Impact Of Ai Tools In Industrial AI SS VThis slide represents key computer vision applications in healthcare, manufacturing retail and automotive industries. It covers use cases such as quality control automation, supply chain optimization, etc.Increase audience engagement and knowledge by dispensing information using Application Of Computer Vision In Impact Of Ai Tools In Industrial AI SS V. This template helps you present information on four stages. You can also present information on Manufacturing Automate, Computer Vision, Pedestrian Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Introduction To Computer Vision Impact Of Ai Tools In Industrial AI SS V
Introduction To Computer Vision Impact Of Ai Tools In Industrial AI SS VThis slide represents introduction to machine learning in different industries that enable use of AI for different processes. It also covers benefits such as increase in efficiency, improved accuracy etc.Introducing Introduction To Computer Vision Impact Of Ai Tools In Industrial AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Increased Efficiency, Improved Safety, Cost Savings, using this template. Grab it now to reap its full benefits.
-
 Key Application Of Edge Computing Impact Of Ai Tools In Industrial AI SS V
Key Application Of Edge Computing Impact Of Ai Tools In Industrial AI SS VThis slide represents key computer vision applications in various industries smart homes, autonomous vehicle augmented reality and energy. It covers use cases such as real time automation, optimization of energy grid performance, etc.Introducing Key Application Of Edge Computing Impact Of Ai Tools In Industrial AI SS V to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Autonomous Vehicles, Augmented Reality, Enables Immersive, using this template. Grab it now to reap its full benefits.
-
 Overview Of Computer Vision In Different Industries Impact Of Ai Tools In Industrial AI SS V
Overview Of Computer Vision In Different Industries Impact Of Ai Tools In Industrial AI SS VThis slide represents the introduction to computer vision in different industries that enable use of AI for different processes. It also covers benefits such as increase in efficiency, improved accuracy etc. Present the topic in a bit more detail with this Overview Of Computer Vision In Different Industries Impact Of Ai Tools In Industrial AI SS V. Use it as a tool for discussion and navigation on Computer Vision, Understand Visual, Enabling Computers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Edge Computing In Different Industries Impact Of Ai Tools In Industrial AI SS V
Overview Of Edge Computing In Different Industries Impact Of Ai Tools In Industrial AI SS VThis slide represents the introduction to computer vision in different industries that enable use of AI for different processes. It also covers benefits such as reduction in latency, improvement in information security etc. Increase audience engagement and knowledge by dispensing information using Overview Of Edge Computing In Different Industries Impact Of Ai Tools In Industrial AI SS V. This template helps you present information on one stage. You can also present information on Improve Information, Improve Reliability, Computing Include using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing V2 ACK TEE 2 0 Architecture And Workflow
Confidential Computing V2 ACK TEE 2 0 Architecture And WorkflowThis slide outlines the architecture of Container Service for Kubernetes trusted execution environment version 2. The purpose of this slide is to demonstrate the features, date of launch and target users. It also covers the architecture and working of ACK - TEE 2.0. Present the topic in a bit more detail with this Confidential Computing V2 ACK TEE 2 0 Architecture And Workflow. Use it as a tool for discussion and navigation on Architecture Of Container Service, Kubernetes Trusted, Execution Environment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 ACK TEE Introduction And Version 1 0 Ppt Inspiration Themes
Confidential Computing V2 ACK TEE Introduction And Version 1 0 Ppt Inspiration ThemesThis slide talks about the introduction of Container Service for Kubernetes trusted execution environment and its version 1.0. The purpose of this slide is to showcase its features, data of launch, objective and target users. It also includes the architecture and workflow of ACK - TEE. Deliver an outstanding presentation on the topic using this Confidential Computing V2 ACK TEE Introduction And Version 1 0 Ppt Inspiration Themes. Dispense information and present a thorough explanation of Hardware Encryption Technology, Strict Security Needs, Delivering And Maintaining Trusted using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Agenda For Confidential Computing Ppt Inspiration Sample
Confidential Computing V2 Agenda For Confidential Computing Ppt Inspiration SampleIntroducing Confidential Computing V2 Agenda For Confidential Computing Ppt Inspiration Sample to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Computing, Consortium, Architecture, Confidential Computing Environment, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Applications In Different Sectors Ppt Ideas Backgrounds
Confidential Computing V2 Applications In Different Sectors Ppt Ideas BackgroundsThis slide represents the applications of confidential computing in different sectors. This slide aims to demonstrate the confidential computing applications in healthcare and research, finance, engineering and manufacturing, and automobile sectors. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Applications In Different Sectors Ppt Ideas Backgrounds. Dispense information and present a thorough explanation of Healthcare And Research, Engineering And Manufacturing, Protect Patient Data, Customer Data Privacy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Architecture And Realms Working Ppt Inspiration Example
Confidential Computing V2 Architecture And Realms Working Ppt Inspiration ExampleThis slide outlines the architecture of confidential computing and the working of realms. The purpose of this slide is to demonstrate the confidential computing architecture, including its components such as realm, applications, operating system, realm manager, hypervisor, and so on. Present the topic in a bit more detail with this Confidential Computing V2 Architecture And Realms Working Ppt Inspiration Example. Use it as a tool for discussion and navigation on Confidential Computing Architecture, Realms Working, Operating System, Working Of Realms. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Architecture Based On Azure Services Ppt Inspiration Gridlines
Confidential Computing V2 Architecture Based On Azure Services Ppt Inspiration GridlinesThis slide represents the architecture of confidential computing based on Azure confidential computing services. The purpose of this slide is to showcase the problems with typical approaches and confidential computing solutions. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Architecture Based On Azure Services Ppt Inspiration Gridlines. Dispense information and present a thorough explanation of Architecture Of Confidential Computing, Azure Confidential, Computing Services, Typical Approaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Architecture Implementation Roadmap
Confidential Computing V2 Architecture Implementation RoadmapThis slide represents the implementation roadmap for confidential computing architecture. The purpose of this slide is to demonstrate the various steps to be taken to deploy confidential computing in a cloud environment, such as executing an existing Redis database unprotected, running within a confidential cloud, etc. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 Architecture Implementation Roadmap. This template helps you present information on five stages. You can also present information on Execute Within Confidential Cloud, Redis Database Unprotected, Confidential Computing Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing V2 Architecture Implementation Timeline
Confidential Computing V2 Architecture Implementation TimelineThis slide outlines the implementation timeline for confidential computing architecture. The purpose of this slide is to demonstrate the various steps to be taken to deploy confidential computing in a cloud environment, such as executing an existing Redis database unprotected, running within a confidential cloud, etc. Introducing Confidential Computing V2 Architecture Implementation Timeline to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Redis Database Unprotected, Execute Within Confidential Cloud, Breach Data Perimeter, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Benefits Of Confidential Computing For Businesses
Confidential Computing V2 Benefits Of Confidential Computing For BusinessesThis slide depicts the benefits of confidential computing for organizations, including protecting crucial data while processing, securing valuable intellectual resources, partnership with stakeholders to develop new cloud solutions, securing information processing at the edge and so on. Present the topic in a bit more detail with this Confidential Computing V2 Benefits Of Confidential Computing For Businesses. Use it as a tool for discussion and navigation on Confidential Computing For Organizations, Protecting Crucial Data, Securing Valuable Intellectual Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Budget For Implementing Confidential Computing Architecture
Confidential Computing V2 Budget For Implementing Confidential Computing ArchitectureThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Budget For Implementing Confidential Computing Architecture. Dispense information and present a thorough explanation of Confidential Computing Architecture, Cost Of Confidential Computing, Hardware And Software Costs using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Business Scenarios Of Confidential Computing Platform
Confidential Computing V2 Business Scenarios Of Confidential Computing PlatformThis slide represents the business scenarios of confidential computing platform and it includes blockchain, key management, finance, artificial intelligence, multi-party computing, data leasing, and edge computing. Organizations can use confidential computing to secure their data while generating high economic value. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 Business Scenarios Of Confidential Computing Platform. This template helps you present information on seven stages. You can also present information on Confidential Computing Platform, Artificial Intelligence, Multi Party Computing, Key Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing V2 Case Study Irene Energy Ppt Infographics Graphics Template
Confidential Computing V2 Case Study Irene Energy Ppt Infographics Graphics TemplateThis slide talks about the case study carried out at Irene Energy organization. The purpose of this slide is to demonstrate how this corporation uses confidential computing technologies to provide electricity to remote American areas. The case study includes issues experienced, objectives, provided solutions and impact. Present the topic in a bit more detail with this Confidential Computing V2 Case Study Irene Energy Ppt Infographics Graphics Template. Use it as a tool for discussion and navigation on Irene Energy Organization, Confidential Computing Technologies, Frictionless Energy Trades. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Checklist To Implement Confidential Computing Architecture
Confidential Computing V2 Checklist To Implement Confidential Computing ArchitectureThis slide depicts the checklist to implement confidential computing architecture in a cloud environment. The purpose of this slide is to showcase the various steps to be taken to deploy confidential computing, including its status and the responsible person. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Checklist To Implement Confidential Computing Architecture. Dispense information and present a thorough explanation of Confidential Computing Architecture, Responsible Person, Cloud Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Client Signature And Server Signature In Inclavare Containers
Confidential Computing V2 Client Signature And Server Signature In Inclavare ContainersThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Confidential Computing V2 Client Signature And Server Signature In Inclavare Containers. Use it as a tool for discussion and navigation on Client Signature, Server Signature, Inclavare Containers, Sensitive Applications And Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Companies Paving The Path For Confidential Computing
Confidential Computing V2 Companies Paving The Path For Confidential ComputingThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Confidential Computing V2 Companies Paving The Path For Confidential Computing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Hub Security, Microsoft Azure, Confidential Computing, Companies Paving The Path, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Components Of Inclavare Containers Architecture
Confidential Computing V2 Components Of Inclavare Containers ArchitectureThis slide outlines the primary components of inclavare containers architecture. The purpose of this slide is to demonstrate the different elements of inclavare containers and their working. The main components include Kubelet, shim-rune, language runtime, liberpal.so, containerd, rune, SGX libOS, and PAL-API. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 Components Of Inclavare Containers Architecture. This template helps you present information on eight stages. You can also present information on Language Runtime, Platform Abstraction Layer, Robustness And Portability, Communication Connection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing V2 Consortium Membership Levels Ppt Inspiration Structure
Confidential Computing V2 Consortium Membership Levels Ppt Inspiration StructureThis slide represents the confidential computing consortium membership and participation levels. The purpose of this slide is to demonstrate the various partnership levels, annual fees, board seats, technical advisory committee seats, outreach committees, and notes. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Consortium Membership Levels Ppt Inspiration Structure. Dispense information and present a thorough explanation of Confidential Computing Consortium, Membership And Participation Levels, Technical Advisory Committee Seats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Consortium Overview And Benefits
Confidential Computing V2 Consortium Overview And BenefitsThis slide represents the overview of the confidential computing consortium and its benefits. The purpose of this slide is to showcase the overview, objective and projects lead by the confidential computing consortium. It also includes the benefits for the members to participate in the confidential computing consortium. Introducing Confidential Computing V2 Consortium Overview And Benefits to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Invitation To Consortium Meetings, Consortium For Business, Consortium Logo For Business, Confidential Computing Resources, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Critical Functions Of Confidential Computing Technology
Confidential Computing V2 Critical Functions Of Confidential Computing TechnologyThis slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 Critical Functions Of Confidential Computing Technology. This template helps you present information on three stages. You can also present information on Code Integrity, Data Integrity, Data Confidentially, Confidential Computing Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing V2 Executive Summary Of Key Findings
Confidential Computing V2 Executive Summary Of Key FindingsThis slide outlines the executive summary of key findings of confidential computing. The purpose of this slide is to showcase the key findings such as market expansion rate, hardware and software segments drive rate, industries that will dominate implementation, and so on. Introducing Confidential Computing V2 Executive Summary Of Key Findings to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Primed For Rapid Expansion, Hardware And Software Segments, Dominate Implementation, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Financial Services And Healthcare Industry Scenario Analysis
Confidential Computing V2 Financial Services And Healthcare Industry Scenario AnalysisThis slide represents the comparative analysis of financial services and healthcare industries based on different scenarios. The purpose of this slide is to demonstrate the different scenarios of financial services and healthcare industries. The different scenarios include best case, median case and worst case scenario. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 Financial Services And Healthcare Industry Scenario Analysis. This template helps you present information on four stages. You can also present information on Suppliers And Pharmaceuticals, Strict Data Security, Nationality Regulations, Industry Scenario Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing V2 For Table Of Contents Ppt Infographics Graphics Download
Confidential Computing V2 For Table Of Contents Ppt Infographics Graphics DownloadIntroducing Confidential Computing V2 For Table Of Contents Ppt Infographics Graphics Download to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Architecture And Realms Working, Trust Boundary Across Azure, Primary Approaches, Technologies Overview, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 For Total Privacy Assurance Ppt Infographics Show
Confidential Computing V2 For Total Privacy Assurance Ppt Infographics ShowThis slide showcases how confidential computing provides total privacy assurance through technical assurance. It also includes the hyper-protect crypto service architecture, including its components such as application user, user interface, application, data service, and data at rest. Present the topic in a bit more detail with this Confidential Computing V2 For Total Privacy Assurance Ppt Infographics Show. Use it as a tool for discussion and navigation on Confidential Servers For Workloads, Confidential Containers For Microservices, Confidential Databases. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Functional Comparison Of Different Tee Environments
Confidential Computing V2 Functional Comparison Of Different Tee EnvironmentsThis slide talks about the functional comparison between different TEE environments available in the market. The purpose of this slide is to demonstrate the comparison and challenges with TEE environments. The main TEE environment provider includes Intel SGX, AMD SEV-ES, and IBM SE. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Functional Comparison Of Different Tee Environments. Dispense information and present a thorough explanation of Software Updates Not Needed, Enclave Secret Support, Memory Overcommit Support, Memory Integrity Or Confidentiality using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Future Of Confidential Computing Technology
Confidential Computing V2 Future Of Confidential Computing TechnologyThis slide represents the future of confidential computing technology. The purpose of this slide is to demonstrate the state of confidential computing in the coming years. It also includes how it will protect sensitive data from malicious attacks in the cloud environment. Introducing Confidential Computing V2 Future Of Confidential Computing Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on European Nations Currently, Mandate Healthcare Firms, Secure Computing Systems, Protect Personally Identifiable Information, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 HI Tech And Manufacturing Industry Scenario Case Analysis
Confidential Computing V2 HI Tech And Manufacturing Industry Scenario Case AnalysisThis slide outlines the difference between hi-tech and manufacturing industries based on the best, median, and worst-case scenarios. The purpose of this slide is to showcase the hi-tech and manufacturing confidential computing market, and it also includes the change agent for best, and worst case. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 HI Tech And Manufacturing Industry Scenario Case Analysis. This template helps you present information on four stages. You can also present information on Skepticism About Transferring, Significant Quantities, Manufacturing Confidential Computing Market using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Confidential Computing V2 Ppt infographic template professional
Icons Slide For Confidential Computing V2 Ppt infographic template professionalIntroducing our well researched set of slides titled Icons Slide For Confidential Computing V2 Ppt infographic template professional. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Confidential Computing V2 In And Out Scope Threat Vectors For Confidential Computing
Confidential Computing V2 In And Out Scope Threat Vectors For Confidential ComputingThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Introducing Confidential Computing V2 In And Out Scope Threat Vectors For Confidential Computing to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Software Attacks, Sophisticated Physical Attacks, Protocol Attacks, Cryptographic Attacks, Physical Attacks, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Inclavare Confidential Containers Architecture In TEE
Confidential Computing V2 Inclavare Confidential Containers Architecture In TEEThis slide represents the architecture of inclavare confidential containers in the TEE environment. The purpose of this slide is to showcase the various components and features of inclavare containers. The primary components include Kubelet, containerd, shim-rune, rune, PAL API, Pod and so on. Present the topic in a bit more detail with this Confidential Computing V2 Inclavare Confidential Containers Architecture In TEE. Use it as a tool for discussion and navigation on Obtains Seamless Collaboration, Kubernetes Ecosystem, Container Initiative Runtime, Enclave Container Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Intel Sgx With A Smaller Trusted Computing Base TCB
Confidential Computing V2 Intel Sgx With A Smaller Trusted Computing Base TCBThis slide describes the deployment of applications in Intel SGX with smaller TCB. The purpose of this slide is to showcase the difference between standard deployment and deployment in TEE. The main components include the operating system, virtual machine monitor, applications and hardware. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Intel Sgx With A Smaller Trusted Computing Base TCB. Dispense information and present a thorough explanation of Operating System, Virtual Machine Monitor, Applications And Hardware, Virtual Machine Monitor using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Introduction To Confidential Computing Technology
Confidential Computing V2 Introduction To Confidential Computing TechnologyThis slide represents the introduction to confidential computing, including its overview and objectives. Confidential computing is a cloud computing method to secure data while processing and gives business confidence to migrate their information and valuable assets to the cloud. Present the topic in a bit more detail with this Confidential Computing V2 Introduction To Confidential Computing Technology. Use it as a tool for discussion and navigation on Confidential Computing Technology, Cloud Computing Method, Encrypted Connections, Hardware Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Key Features Of Confidential Computing Platform
Confidential Computing V2 Key Features Of Confidential Computing PlatformThis slide depicts the key features of confidential computing platform, including confidential virtual machines, confidential space, confidential dataproc, and confidential Google Kubernetes Engine node. Increase audience engagement and knowledge by dispensing information using Confidential Computing V2 Key Features Of Confidential Computing Platform. This template helps you present information on four stages. You can also present information on Confidential Computing Platform, Confidential Computing Cloud Services, Google Kubernetes Engine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Confidential Computing V2 Market Segments Overview Ppt Ideas Infographic Template
Confidential Computing V2 Market Segments Overview Ppt Ideas Infographic TemplateThis slide represents the overview of market segments of confidential computing. The purpose of this slide is to showcase confidential computing market segments such as hardware, software and services. It also caters to the components of each segment along with its description. Present the topic in a bit more detail with this Confidential Computing V2 Market Segments Overview Ppt Ideas Infographic Template. Use it as a tool for discussion and navigation on Application Development Services, Confidential Computing, Market Segments Overview, Attestation Services. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Multi Team Construction And Cooperation In Inclavare Containers
Confidential Computing V2 Multi Team Construction And Cooperation In Inclavare ContainersThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Multi Team Construction And Cooperation In Inclavare Containers. Dispense information and present a thorough explanation of Efficient Multitasking, Multiple File System Support, Memory Safety, Multi Team Construction using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Confidential Computing V2 Multiparty Privacy Preserving Computation Architecture Design
Confidential Computing V2 Multiparty Privacy Preserving Computation Architecture DesignThis slide represents the overview of the architecture design of multiparty computing used in confidential computing. This slide aims to demonstrate the different attributes, benefits and technology options available such as blockchain with Azure virtual machine, blockchain as a service, and so on. Present the topic in a bit more detail with this Confidential Computing V2 Multiparty Privacy Preserving Computation Architecture Design. Use it as a tool for discussion and navigation on Ledger Templates, Custom Deployment, Azure Kubernetes Service, Confidential Computing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing V2 Need For Confidential Computing In Cloud Environment
Confidential Computing V2 Need For Confidential Computing In Cloud EnvironmentThis slide depicts the need for confidential computing in a cloud environment and by showcasing the security concerns with early data processing system and confidential computing solutions to overcome those problems. Introducing Confidential Computing V2 Need For Confidential Computing In Cloud Environment to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Environment, Data Processing System, Confidential Computing Solutions, Early Data Processing, using this template. Grab it now to reap its full benefits.
-
 Confidential Computing V2 Occlum System Architecture And Features
Confidential Computing V2 Occlum System Architecture And FeaturesThis slide depicts the features and architecture of the Occlum system in confidential computing. The purpose of this slide is to showcase the features, architecture and process of the trusted and untrusted environment. The components include the build command, Occlum CLI tool, deployment environment, and so on. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Occlum System Architecture And Features. Dispense information and present a thorough explanation of Efficient Multi Process Support, Memory Security Guarantee, Deployment Environment, Occlum System Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.





