Powerpoint Templates and Google slides for Blockchain Cybersecurity
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Blockchain cybersecurity ppt powerpoint presentation inspiration gallery cpb
Blockchain cybersecurity ppt powerpoint presentation inspiration gallery cpbPresenting this set of slides with name Blockchain Cybersecurity Ppt Powerpoint Presentation Inspiration Gallery Cpb. This is an editable Powerpoint nine stages graphic that deals with topics like Blockchain Cybersecurity to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Ultimate Guide For Blockchain Implementing Blockchain Cybersecurity Risks Mitigation BCT SS
Ultimate Guide For Blockchain Implementing Blockchain Cybersecurity Risks Mitigation BCT SSThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Implementing Blockchain Cybersecurity Risks Mitigation BCT SS This template helps you present information on Four stages. You can also present information on Reduce, Avoid, Accept, Transfer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ultimate Guide For Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SS
Ultimate Guide For Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SSIncrease audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SS This template helps you present information on Four stages. You can also present information on Decentralized Architecture, Public Key Cryptography using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Introducing Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, using this template. Grab it now to reap its full benefits.
-
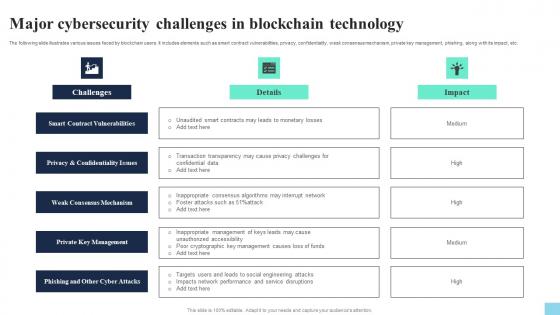 Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various issues faced by blockchain users. It includes elements such as smart contract vulnerabilities, privacy, confidentiality, weak consensus mechanism, private key management, phishing, along with its impact, etc. Introducing Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Smart Contract Vulnerabilities, Weak Consensus Mechanism, Private Key Management, using this template. Grab it now to reap its full benefits.
-
 Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Increase audience engagement and knowledge by dispensing information using Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, Immutable Records using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS V
Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Increase audience engagement and knowledge by dispensing information using Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS V This template helps you present information on four stages. You can also present information on Reduce, Avoid, Transfer, Accept using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Importance Of Cybersecurity In Blockchain Technology Guide For Blockchain BCT SS V
Importance Of Cybersecurity In Blockchain Technology Guide For Blockchain BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Introducing Importance Of Cybersecurity In Blockchain Technology Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Architecture, Key Cryptography, Smart Contracts using this template. Grab it now to reap its full benefits.
-
 Major Cryptocurrency And Blockchain Cybersecurity Scams Guide For Blockchain BCT SS V
Major Cryptocurrency And Blockchain Cybersecurity Scams Guide For Blockchain BCT SS VThe following slide showcases major cryptocurrency and blockchain cybersecurity scams throughout the globe. It includes elements such as Decentralized autonomous organization DAO attack, gox attack, plus token scams, etc. Increase audience engagement and knowledge by dispensing information using Major Cryptocurrency And Blockchain Cybersecurity Scams Guide For Blockchain BCT SS V This template helps you present information on four stages. You can also present information on Major Cryptocurrency, Blockchain Cybersecurity Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Adopt Two Factor Authentication To Reduce Hacking BCT SS V
Blockchain And Cybersecurity Adopt Two Factor Authentication To Reduce Hacking BCT SS VThe following slide illustrates some tips and practices to ensure two factor authentication and safeguard blaockchain network. It includes elements such as restricting unauthorized access, safeguarding personal keys, sending unique codes, extending user authentication, etc. Introducing Blockchain And Cybersecurity Adopt Two Factor Authentication To Reduce Hacking BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Restricts Unauthorized Access, Extends User Authentication, Sending Unique Codes using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Analyzing Risk Probabilities With Impact Matrix BCT SS V
Blockchain And Cybersecurity Analyzing Risk Probabilities With Impact Matrix BCT SS VThe following slide showcases blockchain cybersecurity risk probabilities matrix. It includes elements such as likelihood, impact, loss of private key, accessibility to digital wallets, sensitive data loss, misuse of smart contracts, breakdown of servers, data breach, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Analyzing Risk Probabilities With Impact Matrix BCT SS V This template helps you present information on Three stages. You can also present information on Private Key, Digital Wallets, Sensitive Data Loss using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Backing Up Data To Enhance Security And Efficiency BCT SS V
Blockchain And Cybersecurity Backing Up Data To Enhance Security And Efficiency BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Blockchain And Cybersecurity Backing Up Data To Enhance Security And Efficiency BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Automated Backup, Track Backup using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Best Practices To Create Strong Passwords BCT SS V
Blockchain And Cybersecurity Best Practices To Create Strong Passwords BCT SS VThe following slide illustrates some tips to develop strong passwords to manage and ensure secure blockchain transactions. It includes elements such as long and strong passwords, never reusing keys, leveraging password managers, avoiding personal information, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Best Practices To Create Strong Passwords BCT SS V This template helps you present information on Four stages. You can also present information on Complex Passwords, Reuse Passwords, Password Managers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Comparative Analysis Of Various Types Of Blockchain Network BCT SS V
Blockchain And Cybersecurity Comparative Analysis Of Various Types Of Blockchain Network BCT SS VThe following slide depicts the comparative assessment of major types of blockchain network to analyze the level of security. It includes elements such as decentralization, accessibility, security, transparency, scalability, etc. Introducing Blockchain And Cybersecurity Comparative Analysis Of Various Types Of Blockchain Network BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Public Blockchain, Private Blockchain, Consortium Blockchain using this template. Grab it now to reap its full benefits.
-
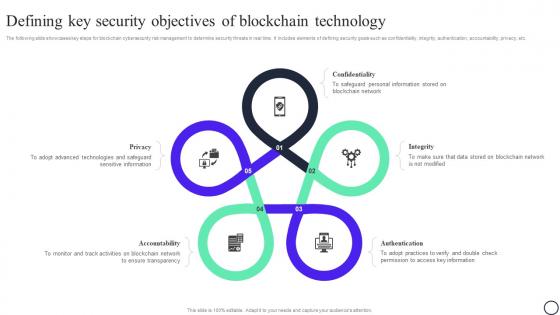 Blockchain And Cybersecurity Defining Key Security Objectives Of Blockchain Technology BCT SS V
Blockchain And Cybersecurity Defining Key Security Objectives Of Blockchain Technology BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Defining Key Security Objectives Of Blockchain Technology BCT SS V This template helps you present information on Five stages. You can also present information on Privacy, Confidentiality, Integrity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Discovery Identifying Potential Vulnerabilities In System BCT SS V
Blockchain And Cybersecurity Discovery Identifying Potential Vulnerabilities In System BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Introducing Blockchain And Cybersecurity Discovery Identifying Potential Vulnerabilities In System BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Functional Testing Checklist To Review Key Components BCT SS V
Blockchain And Cybersecurity Functional Testing Checklist To Review Key Components BCT SS VThe following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Functional Testing Checklist To Review Key Components BCT SS V This template helps you present information on Three stages. You can also present information on Parameters, Description, Status using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity How Does Phishing Attack Works On Blockchain Network BCT SS V
Blockchain And Cybersecurity How Does Phishing Attack Works On Blockchain Network BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity How Does Phishing Attack Works On Blockchain Network BCT SS V This template helps you present information on Seven stages. You can also present information on Phishing Email, Internet Network, Dispense Email using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS V
Blockchain And Cybersecurity Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS VThe following slide depicts the key effect of 51percent attack on bitcoin and blockchain technology to plan actions and minimize its impact. It includes element such as delayed transactions, network disruption, low miner rewards, market volatility, reputation, credibility, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS V This template helps you present information on Five stages. You can also present information on Network Disruption, Low Miner Rewards, Market Volatility using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Impact Of Ddos Attack On Targeted Servers BCT SS V
Blockchain And Cybersecurity Impact Of Ddos Attack On Targeted Servers BCT SS VThe following slide depicts the adverse impact of denial of service DDoS attack to determine malicious attempt to hamper targeted server. It includes elements such as software crashes, node failure, network congestion, bloated ledger, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Impact Of Ddos Attack On Targeted Servers BCT SS V This template helps you present information on Four stages. You can also present information on Software Crashes, Network Congestion, Bloated Ledger using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Impact Of Eclipse Attack On Peer To Peer Network BCT SS V
Blockchain And Cybersecurity Impact Of Eclipse Attack On Peer To Peer Network BCT SS VThe following slide illustrates the impact of eclipse attack on functioning of blockchain network to plan strategies and action steps. It includes elements such as leading to double spending, centralization, disrupting mining power, network instability, monetary loss, etc. Introducing Blockchain And Cybersecurity Impact Of Eclipse Attack On Peer To Peer Network BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Leads To Double Spending, Centralization, Disrupts Mining Power using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V
Blockchain And Cybersecurity Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V This template helps you present information on Two stages. You can also present information on Reduce, Avoid, Transfer, Accept using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Importance Of Cybersecurity In Blockchain Technology BCT SS V
Blockchain And Cybersecurity Importance Of Cybersecurity In Blockchain Technology BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Importance Of Cybersecurity In Blockchain Technology BCT SS V This template helps you present information on Four stages. You can also present information on Decentralized Architecture, Public Key Cryptography, Smart Contracts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Key Approaches To Protect From Honeypot Scams BCT SS V
Blockchain And Cybersecurity Key Approaches To Protect From Honeypot Scams BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Introducing Blockchain And Cybersecurity Key Approaches To Protect From Honeypot Scams BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Audits, No Dead Coins, Scrutinize Website using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Key Statistics Associated With Blockchain Scams BCT SS V
Blockchain And Cybersecurity Key Statistics Associated With Blockchain Scams BCT SS VThe following slide depicts key facts related with blockchain frauds to ensure secure transactions. It includes elements such as hacking of decentralized finance, stolen funds, fraudulent schemes, cryptocurrency scams, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Key Statistics Associated With Blockchain Scams BCT SS V This template helps you present information on Six stages. You can also present information on Digital Assets, Stolen Through Frauds using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Leverage Cryptography To Boost Privacy And Confidentiality BCT SS V
Blockchain And Cybersecurity Leverage Cryptography To Boost Privacy And Confidentiality BCT SS VThe following slide showcases how cryptography assists in securing blockchain transactions and maintaining confidentiality. It includes elements such as data confidentiality, data integrity, digital signatures, consensus mechanism, etc. Introducing Blockchain And Cybersecurity Leverage Cryptography To Boost Privacy And Confidentiality BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Data Confidentiality, Digital Signatures, Consensus Mechanisms using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS V
Blockchain And Cybersecurity Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS VThe following slide showcases major cryptocurrency and blockchain cybersecurity scams throughout the globe. It includes elements such as Decentralized autonomous organization DAO attack, gox attack, plus token scams, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS V This template helps you present information on Four stages. You can also present information on DAO Hack, Quadrigacx Attack, Plus Token Scam using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V
Blockchain And Cybersecurity Methods To Avoid Sybil Attack For Protecting Tokens BCT SS VThe following slide illustrates various ways to minimize and prevent Sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Introducing Blockchain And Cybersecurity Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Identity Validation, Establishing Hierarchical System, Defense System using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Methods To Ensure Smart Contract Security BCT SS V
Blockchain And Cybersecurity Methods To Ensure Smart Contract Security BCT SS VThe following slide showcases some tips and practices to ensure smart contract security. It includes elements such as careful rollouts, keeping them simple, updating and monitoring new developments, reviewing fundamental tradeoffs, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Methods To Ensure Smart Contract Security BCT SS V This template helps you present information on Four stages. You can also present information on New Advancements, Careful Rolloutsm Review Fundamental Tradeoffs using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Methods To Identify Crypto Phishing Scams BCT SS V
Blockchain And Cybersecurity Methods To Identify Crypto Phishing Scams BCT SS VThe following slide illustrates various methods to determine blockchain phishing attack and safeguard confidential information. It includes elements such as copycatting, spellings, ambiguous links, using public email ID, disordered content etc. Introducing Blockchain And Cybersecurity Methods To Identify Crypto Phishing Scams BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Copycatting, Spelling, Ambiguous Links using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V
Blockchain And Cybersecurity Overview And Categories Of Sybil Attack On Blockchain Network BCT SS VThe following slide illustrates brief introduction of Sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V This template helps you present information on Four stages. You can also present information on Direct Sybil Attack, Indirect Sybil Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Overview And Impact Of Blockchain Routing Attacks BCT SS V
Blockchain And Cybersecurity Overview And Impact Of Blockchain Routing Attacks BCT SS VThe following slide illustrates the brief introduction of routing attacks to reduce leakage of information. It includes elements such as interrupting communication between nodes, delaying blockchain delivery, breaking network into two or more parts, etc. Introducing Blockchain And Cybersecurity Overview And Impact Of Blockchain Routing Attacks BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Internet Service Providers, Partial Proceedings, Impact Of Routing Attack using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Overview And Key Levels Of Honeypot Crypto Frauds BCT SS V
Blockchain And Cybersecurity Overview And Key Levels Of Honeypot Crypto Frauds BCT SS VThe following slide illustrates brief introduction of honeypot scams to determine malicious activities and mitigate risks. It includes elements such as etheruem virtual machine, solidity compiler, etherscan blockchain explorer, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Overview And Key Levels Of Honeypot Crypto Frauds BCT SS V This template helps you present information on Three stages. You can also present information on Solidity Compiler, Etherscan Blockchain Explorer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Overview And Working Process Of Ddos Attack BCT SS V
Blockchain And Cybersecurity Overview And Working Process Of Ddos Attack BCT SS VThe following slide illustrates brief introduction of distributed denial of service DDoS attack to prevent user from leveraging key information. It includes elements such as hampering website with excessive internet traffic, minimizing website downtime, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Overview And Working Process Of Ddos Attack BCT SS V This template helps you present information on Four stages. You can also present information on Attacker Controls Website Hostage, Perform Operations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Overview Of Phishing Attack In Blockchain Technology BCT SS V
Blockchain And Cybersecurity Overview Of Phishing Attack In Blockchain Technology BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting blockchian to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Blockchain And Cybersecurity Overview Of Phishing Attack In Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Attached Fake Links, Investment Opportunities, Fake Website using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Reviewing Consensus Mechanism To Manage Decentralized Network BCT SS V
Blockchain And Cybersecurity Reviewing Consensus Mechanism To Manage Decentralized Network BCT SS VThe following slide showcases some tips for consensus mechanism to ensure record of legitimate transactions. It includes elements such as proof of work PoW, proof of stake PoS, delegated PoS, resolving complicated puzzles, verifying transactions, sharing monetary risks, etc. Introducing Blockchain And Cybersecurity Reviewing Consensus Mechanism To Manage Decentralized Network BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Proof Of Work, Proof Of Stake, Delegated POS using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V
Blockchain And Cybersecurity Techniques To Prevent Eclipse Attack And Secure Funds BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V This template helps you present information on Four stages. You can also present information on Increased Node Connections, Deterministic Node Selection, New Node Restrictions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Threats Imposed By Sybil Attack On Blockchain Network BCT SS V
Blockchain And Cybersecurity Threats Imposed By Sybil Attack On Blockchain Network BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Introducing Blockchain And Cybersecurity Threats Imposed By Sybil Attack On Blockchain Network BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Block Users From Network, Foster 51percent Attack, Breach Of Privacy using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Various Types Of Crypto Phishing Attacks BCT SS V
Blockchain And Cybersecurity Various Types Of Crypto Phishing Attacks BCT SS VThe following slide illustrates various types of phishing attacks to analyze how cryptocurrency funds are stolen from blockchain network. It includes elements such as spear, whaling, clone, spoof emails, accessibility to personal details, replacing original link with fake one, etc. Introducing Blockchain And Cybersecurity Various Types Of Crypto Phishing Attacks BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Whaling Phishing, Clone Phishing using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V
Blockchain And Cybersecurity Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS VThe following slide showcases various types of denial of service DDoS attack to reduce abnormal traffic and lessen the impact. It includes elements such as volumetric, applications, protocol, fragmentation attacks, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V This template helps you present information on Four stages. You can also present information on Volumetric Attacks, Protocol Attacks, Application Attacks, Fragmentation Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Ways To Minimize 51 Percent Attacks And Optimize Hash Rate BCT SS V
Blockchain And Cybersecurity Ways To Minimize 51 Percent Attacks And Optimize Hash Rate BCT SS VThe following slide illustrates various methods to reduce the impact of 51percent attacks and optimize hash rate. It includes elements such as restriction on single user, constant updates, establishing strong network system, leveraging proof of stake, performing security audits, etc. Introducing Blockchain And Cybersecurity Ways To Minimize 51 Percent Attacks And Optimize Hash Rate BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Single User, Constant Updates, Network System using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Ways To Prevent Blockchain Routing Attacks BCT SS V
Blockchain And Cybersecurity Ways To Prevent Blockchain Routing Attacks BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Ways To Prevent Blockchain Routing Attacks BCT SS V This template helps you present information on Four stages. You can also present information on Strong Passwords, Update Firmware, Manage Access Control List using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Ways To Prevent Crypto Phishing And Sensitive Information Leakage BCT SS V
Blockchain And Cybersecurity Ways To Prevent Crypto Phishing And Sensitive Information Leakage BCT SS VThe following slide illustrates some methods to minimize crypto phishing attacks and. It includes elements such as using VPN, cross checking browsers URL, emails, leveraging two factor authentication, avoid usage of protected wi-fi networks, etc. Introducing Blockchain And Cybersecurity Ways To Minimize 51 Percent Attacks And Optimize Hash Rate BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Cross Check Emails, Factor Authentication, Unprotected Wi-Fi-Networks using this template. Grab it now to reap its full benefits.
-
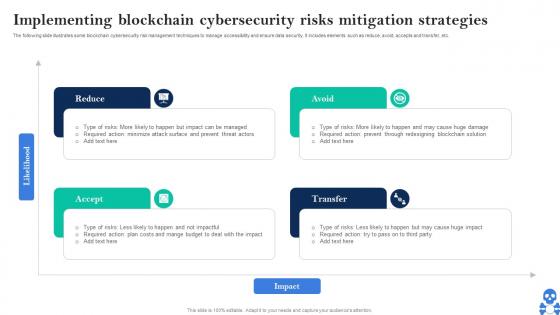 Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V
Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Introducing Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Avoid, Transfer, Accept using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS V
Cyber Threats In Blockchain Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS VThe following slide showcases major cryptocurrency and blockchain cybersecurity scams throughout the globe. It includes elements such as decentralized autonomous organization DAO attack, GOX attack, plus token scams, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Major Cryptocurrency And Blockchain Cybersecurity Scams BCT SS V This template helps you present information on Four stages. You can also present information on DAO Hack, Quadrigacx Attack, Plus Token Scam using this PPT design. This layout is completely editable so personaize it now
-
 Cybersecurity Challenges In Blockchain Technology For Security Enhancement
Cybersecurity Challenges In Blockchain Technology For Security EnhancementThis slide highlights cybersecurity challenges for working together to enhance security posture of blockchain community by developers and users.It includes issues such as scalability challenges, lack of governance, blockchain literacy, and reliance on private keys. Presenting our set of slides with Cybersecurity Challenges In Blockchain Technology For Security Enhancement This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Scalability Challenges, Blockchain Literacy, Lack Of Governance
-
 Use Cases Of Blockchain In Cybersecurity Decoding The Future Of Blockchain Technology BCT SS
Use Cases Of Blockchain In Cybersecurity Decoding The Future Of Blockchain Technology BCT SSThis slide highlights various use cases of integrating blockchain technology in cybersecurity. It includes edge computing with authentication, advance confidentiality, secured private messaging, improved PKI and intact domain systems. Increase audience engagement and knowledge by dispensing information using Use Cases Of Blockchain In Cybersecurity Decoding The Future Of Blockchain Technology BCT SS. This template helps you present information on five stages. You can also present information on Protected Edge Computing With Authentication, Advanced Confidentiality And Data Integrity, Secured Private Messaging using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Benefits Of Using Blockchain Technology In Cybersecurity
Benefits Of Using Blockchain Technology In CybersecurityThis slide discusses the benefits of using blockchain technology in cybersecurity which include ensures user confidentiality, data transparency, etc. Presenting our set of slides with Benefits Of Using Blockchain Technology In Cybersecurity. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ensures User Confidentiality, Safe Data Transfers, Data Transparency Traceability.
-
 Blockchain Technology Working For Organizational Cybersecurity
Blockchain Technology Working For Organizational CybersecurityThe below slide provides the working process for blockchain security technology used by organizations to enhance transaction privacy. The process involves steps such as initiation, validation, verification, etc. Presenting our set of slides with Blockchain Technology Working For Organizational Cybersecurity. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Transaction Initiated, Transaction Completed, Benefits Received.


