Powerpoint Templates and Google slides for Attack Management
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Incident response reporting for management with attack suppression and impact status
Incident response reporting for management with attack suppression and impact statusIntroducing our Incident Response Reporting For Management With Attack Suppression And Impact Status set of slides. The topics discussed in these slides are Band Abuse, Cyber Attack, Attack Impact, Details, Attack Success Rate. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Incident response reporting for management with attack timeline
Incident response reporting for management with attack timelinePresenting our well-structured Incident Response Reporting For Management With Attack Timeline. The topics discussed in this slide are Attack Timeline, Initial Compromise Date, Improvement Desired. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Incident response reporting for management with overall attack impact details
Incident response reporting for management with overall attack impact detailsPresenting our well-structured Incident Response Reporting For Management With Overall Attack Impact Details. The topics discussed in this slide are Overall Attack Impact, Attack Enablers, Recommendations. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Enhanced security event management insider attacker method and behaviour assessment ppt rules
Enhanced security event management insider attacker method and behaviour assessment ppt rulesThis slide portrays information regarding the insider attacker assessment in security operations system by addressing the method they use to attack and analyzing insider behavior. Present the topic in a bit more detail with this Enhanced Security Event Management Insider Attacker Method And Behaviour Assessment Ppt Rules. Use it as a tool for discussion and navigation on Insider Attacker Method And Behaviour Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism Attacks
A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism AttacksThis slide demonstrates how the cyber security model would operate in the first 30 days and the duties that the company should concentrate on.Present the topic in a bit more detail with this A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Managing Cyber Terrorism 30 Days Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Managing Cyber Terrorism 60 Days Plan Cyber Terrorism Attacks
Managing Cyber Terrorism 60 Days Plan Cyber Terrorism AttacksThis slide depicts the plan for the next 60 days after the firm has implemented the cyber security model to tackle cyber terrorism. Deliver an outstanding presentation on the topic using this Managing Cyber Terrorism 60 Days Plan Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Managing Cyber Terrorism 60 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism Attacks
Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism AttacksThis slide demonstrates the cyber security models 90 day strategy in an enterprise, as well as training compliance and communication strategies. Deliver an outstanding presentation on the topic using this Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Managing Cyber Terrorism Attacks 90 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
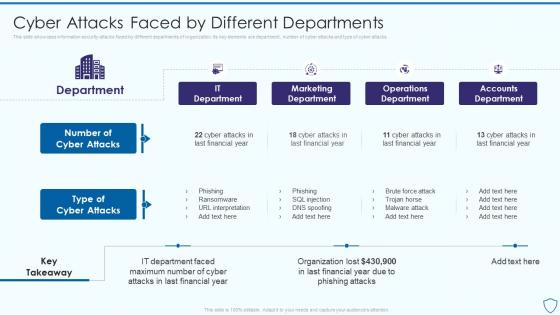 Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different
Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By DifferentThis slide showcase information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Deliver an outstanding presentation on the topic using this Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different. Dispense information and present a thorough explanation of Marketing Department, Operations Department, Accounts Department using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Attacks Faced By Risk Assessment And Management Plan For Information Security
Information Security Attacks Faced By Risk Assessment And Management Plan For Information SecurityThis slide showcases most common information attacks faced by organization. It includes malware, phishing, man in the middle attack, SQL injection, zero day exploit and DNS attack Deliver an outstanding presentation on the topic using this Information Security Attacks Faced By Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Malware, Phishing, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Financial Impact Of Information Security Attacks Information Security Risk Management
Financial Impact Of Information Security Attacks Information Security Risk ManagementThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type. Present the topic in a bit more detail with this Financial Impact Of Information Security Attacks Information Security Risk Management. Use it as a tool for discussion and navigation on Malicious Insiders, Social Engineering, Information Security Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments
Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different DepartmentsThis slide showcases information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Present the topic in a bit more detail with this Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments. Use it as a tool for discussion and navigation on Departments, Information, Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type Present the topic in a bit more detail with this Financial Impact Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Financial, Information, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Cyber Security Incident Management Team Roles And Responsibilities
Cyber Security Attacks Response Cyber Security Incident Management Team Roles And ResponsibilitiesPresent the topic in a bit more detail with this Cyber Security Attacks Response Cyber Security Incident Management Team Roles And Responsibilities. Use it as a tool for discussion and navigation on Cyber Security Incident, Management Team, Roles And Responsibilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Impact Of Implementing Cyber Security Incident Management
Cyber Security Attacks Response Impact Of Implementing Cyber Security Incident ManagementThis slide represents the comparison between current and past scenario to analyze the impact of cyber security incident management on business operations. It includes analysis of KPIs such engagement, satisfaction, turnover rate etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Impact Of Implementing Cyber Security Incident Management. Dispense information and present a thorough explanation of Cyber Security Incident, Management On Organization, Software Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Assessment And Management Matrix Cyber Security Attacks Response Plan
Cyber Security Risk Assessment And Management Matrix Cyber Security Attacks Response PlanThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution. Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Management Matrix Cyber Security Attacks Response Plan. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Management Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Analyse Impact Of Cyber Attack On Valuable Assets Implementing Cyber Risk Management Process
Analyse Impact Of Cyber Attack On Valuable Assets Implementing Cyber Risk Management ProcessThe following slide depicts the consequences of data breach threats to prevent information leakage. It mainly includes elements such as impact on revenue, protection cost, liability if lost, weightage criteria, asset importance etc. Present the topic in a bit more detail with this Analyse Impact Of Cyber Attack On Valuable Assets Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Criteria, Impact On Revenue, Protection Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process
Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management ProcessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Assets, Details, Comments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Attack And Readiness Assessment And Management Matrix
Cyber Attack And Readiness Assessment And Management MatrixFollowing slide highlights readiness evaluation to cyber security management for compliance with regulations. It further covers process, technology used, people target and basis such as basic, advanced and extended, etc. Introducing our Cyber Attack And Readiness Assessment And Management Matrix set of slides. The topics discussed in these slides are Process, Technology, People. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Supply Chain Attacks Affecting Smart Warehouse Management
Supply Chain Attacks Affecting Smart Warehouse ManagementThis slide represents various solutions that assist companies in mitigating various supply chain attacks affecting smart warehouse management for information protection. It includes various attacks such as malware injection, data theft, and ransomeware. Presenting our well structured Supply Chain Attacks Affecting Smart Warehouse Management. The topics discussed in this slide are Malware Injection, Data Theft, Ransomware. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.


