Powerpoint Templates and Google slides for Algorithmic
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Natural language processing it applications of deep learning algorithms in nlp
Natural language processing it applications of deep learning algorithms in nlpThis slide shows the applications of deep learning algorithms such as neural network NN, recurrent neutral networks RNN, recursive neural networks, and convolutional neural network CNN in NLP. Present the topic in a bit more detail with this Natural Language Processing IT Applications Of Deep Learning Algorithms In NLP. Use it as a tool for discussion and navigation on Deep Learning Algorithms, NLP Usage, Neural Network, Recurrent Neural Networks, Recursive Neural Networks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Memcached distributed algorithms ppt powerpoint presentation layouts
Memcached distributed algorithms ppt powerpoint presentation layoutsThis slide depicts the Memcached distribution algorithms, including distribute, residual distributed, and consistent hashing. Present the topic in a bit more detail with this Memcached Distributed Algorithms Ppt Powerpoint Presentation Layouts. Use it as a tool for discussion and navigation on Consistent Hashing, Residual Distributed Algorithms, Memcached Distributed. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Natural Language AI Applications Of Deep Learning Algorithms In NLP Ppt Pictures Slideshow
Natural Language AI Applications Of Deep Learning Algorithms In NLP Ppt Pictures SlideshowThis slide shows the applications of deep learning algorithms such as neural network NN, recurrent neutral networks RNN, recursive neural networks, and convolutional neural network CNN in NLP. Present the topic in a bit more detAIl with this Natural Language AI Applications Of Deep Learning Algorithms In NLP Ppt Pictures Slideshow. Use it as a tool for discussion and navigation on Part Of Speech Tagging, Tokenization, Named Entity Recognition, Intent Extraction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Applications Of Filtering Techniques Amazon Recommender System Types And Algorithms
Applications Of Filtering Techniques Amazon Recommender System Types And AlgorithmsThis slide represents the working of Amazons recommendation system. The purpose of this slide is to outline the factors on which Amazons recommender works. This slide also includes the algorithms used by Amazon to provide suggestions to the users. Present the topic in a bit more detail with this Applications Of Filtering Techniques Amazon Recommender System Types And Algorithms. Use it as a tool for discussion and navigation on Collaborative Filtering, Content Based Filtering, Causal Inference In Recommendations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps For Setting Up Apache Lucene For Accurate Search Algorithms Tech Stack SS
Steps For Setting Up Apache Lucene For Accurate Search Algorithms Tech Stack SSThis slide represents process involved in setting up Apache Lucene to carryout searches as per user requirement. It includes various steps such as adding required dependencies to get started lucene and use given code for parsing search queries. Presenting our well structured Steps For Setting Up Apache Lucene For Accurate Search Algorithms Tech Stack SS. The topics discussed in this slide are Required Dependencies, Dependency, Search Algorithms. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Algorithms Used In Netflix Recommender System Recommendations Based On Machine Learning
Algorithms Used In Netflix Recommender System Recommendations Based On Machine LearningThis slide talks about various algorithms used in Netflixs recommendation system. The purpose of this slide is to explain how different approaches are validated by Netflix recommender. This slide also shows the process followed by all algorithms. Present the topic in a bit more detail with this Algorithms Used In Netflix Recommender System Recommendations Based On Machine Learning. Use it as a tool for discussion and navigation on Analyse Candidates, Evidence, Deduplicate And Filter Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Amazon Recommender System Algorithms Recommendations Based On Machine Learning
Amazon Recommender System Algorithms Recommendations Based On Machine LearningThis slide represents the working of Amazons recommendation system. The purpose of this slide is to outline the factors on which Amazons recommender works. This slide also includes the algorithms used by Amazon to provide suggestions to the users. Deliver an outstanding presentation on the topic using this Amazon Recommender System Algorithms Recommendations Based On Machine Learning. Dispense information and present a thorough explanation of Algorithms, Recommendations, Collaborative using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Hybrid Algorithms Bandit And Casual Interference Recommendations Based On Machine Learning
Hybrid Algorithms Bandit And Casual Interference Recommendations Based On Machine LearningThis slide talks about the hybrid algorithms used by Amazons recommender system. The purpose of this slide is to represent the working of Amazons hybrid algorithms. These algorithms are Bandit inference and casual inference. Present the topic in a bit more detail with this Hybrid Algorithms Bandit And Casual Interference Recommendations Based On Machine Learning. Use it as a tool for discussion and navigation on Interference, Recommended, Products. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Mining A Complete Guide Types Of Machine Algorithms In Data Mining AI SS
Data Mining A Complete Guide Types Of Machine Algorithms In Data Mining AI SSThis slide showcases various types of machine learning algorithms often used by experts in the field of data mining. It provides information about supervised and un-supervised machine learning ML algorithms. Increase audience engagement and knowledge by dispensing information using Data Mining A Complete Guide Types Of Machine Algorithms In Data Mining AI SS. This template helps you present information on three stages. You can also present information on Supervised Ml Algorithms, Un Supervised Ml Algorithms, Unlabeled Data Sets using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 About Asymmetric Algorithm Overview And Benefits Cloud Cryptography
About Asymmetric Algorithm Overview And Benefits Cloud CryptographyThis slide represents the asymmetric algorithm for cloud cryptography. The purpose of this slide is to discuss about the basic concept and advantages of asymmetric technique. These include allows message authentication, practical approach, etc. Present the topic in a bit more detail with this About Asymmetric Algorithm Overview And Benefits Cloud Cryptography. Use it as a tool for discussion and navigation on Overview, Asymmetric, Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Symmetric Algorithm Overview And Benefits Cloud Cryptography
About Symmetric Algorithm Overview And Benefits Cloud CryptographyThis slide represents the symmetric algorithm for cloud cryptography. The purpose of this slide is to discuss about the advantages of symmetric algorithm. These include remarkably secure, speed, acceptance, requires low computer resources, etc. Deliver an outstanding presentation on the topic using this About Symmetric Algorithm Overview And Benefits Cloud Cryptography. Dispense information and present a thorough explanation of Overview, Automatically, Environments using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cryptographic Algorithms Used In Data Security Cloud Cryptography
Cryptographic Algorithms Used In Data Security Cloud CryptographyThis slide talks about algorithms used for implementing cryptography in data security. The purpose of this slide is to explain the different implementation steps. The techniques discussed are RSA Rivest, Shamir, Adleman cryptographic algorithm and Data Encryption Standard algorithm. Deliver an outstanding presentation on the topic using this Cryptographic Algorithms Used In Data Security Cloud Cryptography. Dispense information and present a thorough explanation of Cryptographic, Algorithms, Data Encryption Standard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Elliptic Curve Cryptography Ecc Asymmetric Algorithm Cloud Cryptography
Elliptic Curve Cryptography Ecc Asymmetric Algorithm Cloud CryptographyThis slide talks about the Elliptic Curve Cryptography algorithm. The purpose of this slide is to elaborate the different applications of ECC algorithm. The uses of this algorithm are key agreement, mobile devices, cryptocurrency, etc. Present the topic in a bit more detail with this Elliptic Curve Cryptography Ecc Asymmetric Algorithm Cloud Cryptography. Use it as a tool for discussion and navigation on Overview, Applications, Cryptocurrency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 F1636 Working Process Of Asymmetric Cryptographic Algorithm Cloud Cryptography
F1636 Working Process Of Asymmetric Cryptographic Algorithm Cloud CryptographyThis slide demonstrates the working structure of asymmetric technique of cloud cryptography with the help of an illustrative diagram. The key components included are normal text, cipher text, encryption, decryption, secret key, public key, etc. Present the topic in a bit more detail with this F1636 Working Process Of Asymmetric Cryptographic Algorithm Cloud Cryptography. Use it as a tool for discussion and navigation on Process, Asymmetric, Cryptographic Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Rivest Shamir Adleman Rsa Asymmetric Algorithm Cloud Cryptography
Rivest Shamir Adleman Rsa Asymmetric Algorithm Cloud CryptographyThis slide talks about the Rivest Shamir Adleman RSA asymmetric algorithm. The purpose of this slide is to represent the benefits and applications of RSA algorithm. The uses of RSA algorithm includes hybrid encryption, digital signatures, etc. Present the topic in a bit more detail with this Rivest Shamir Adleman Rsa Asymmetric Algorithm Cloud Cryptography. Use it as a tool for discussion and navigation on Asymmetric, Communication, Transactions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Working Of Common Data Encryption Des Algorithm Cloud Cryptography
Working Of Common Data Encryption Des Algorithm Cloud CryptographyThis slide represents the working flow of Common Data Encryption DES algorithm. The purpose of this slide is to outline the algorithm steps. This slide also explains the DES modes of operation, which include Digital Codebook, Cipher Block Chaining, etc. Deliver an outstanding presentation on the topic using this Working Of Common Data Encryption Des Algorithm Cloud Cryptography. Dispense information and present a thorough explanation of Pseudorandom, Initialization, Independent using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Green Cloud Computing Algorithms Overview Green IT
Green Cloud Computing Algorithms Overview Green ITThis slide represents the overview of algorithms used in green cloud computing. The purpose of this slide is to showcase the Green IT algorithms and their working. The main algorithms include the green generic algorithm, improved clonal selection algorithm, and green algorithm. Deliver an outstanding presentation on the topic using this Green Cloud Computing Algorithms Overview Green IT. Dispense information and present a thorough explanation of Algorithms, Computing, Cloud using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Green Cloud Computing V2 Algorithms Overview Ppt Infographics Layouts
Green Cloud Computing V2 Algorithms Overview Ppt Infographics LayoutsThis slide represents the overview of algorithms used in green cloud computing. The purpose of this slide is to showcase the Green IT algorithms and their working. The main algorithms include the green generic algorithm, improved clonal selection algorithm, and green algorithm. Deliver an outstanding presentation on the topic using this Green Cloud Computing V2 Algorithms Overview Ppt Infographics Layouts. Dispense information and present a thorough explanation of Green Cloud Computing, Green IT Algorithms, Green Generic Algorithm, Clonal Selection Algorithm using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 How Deep Learning Algorithms Explore Natural Language Processing NLP AI SS V
How Deep Learning Algorithms Explore Natural Language Processing NLP AI SS VThis slide provides information regarding the usage of deep learning technology algorithms in NLP. Such algorithms include neural network, recurrent neural network, recursive neural network and convolutional neural network. Present the topic in a bit more detail with this How Deep Learning Algorithms Explore Natural Language Processing NLP AI SS V. Use it as a tool for discussion and navigation on Recurrent, Recursive, Convolutional. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Triple Data Encryption Algorithm Tdea Encryption For Data Privacy In Digital Age It
About Triple Data Encryption Algorithm Tdea Encryption For Data Privacy In Digital Age ItThis slide discusses the Triple data Encryption Algorithm TDEA which utilizes three keys. The purpose of this slide is to provide simplified illustration of the procedure to demonstrate how the TDEA encrypts plain text data into unreadable ciphertext. Present the topic in a bit more detail with this About Triple Data Encryption Algorithm Tdea Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Computational, Processing, Illustration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Asymmetric Cryptography Using Digital Signature Algorithm Encryption For Data Privacy In Digital Age It
Asymmetric Cryptography Using Digital Signature Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the working of Digital Signature Algorithm. The purpose of this slide is to outline the benefits of DSA asymmetric cryptography. The advantages of DSA are message authentication, identity verification and non-repudiation. Present the topic in a bit more detail with this Asymmetric Cryptography Using Digital Signature Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Message Authentication, Integrity Verification, Non Repudiation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Data Encryption Standard DES algorithm. The benefits include secure against brute-force attacks, robust level of encryption, suitable for resource-constrained devices and applications, etc. Present the topic in a bit more detail with this Benefits Of Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Encryption, Demonstrates, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Standard For Advanced Encryption Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Standard For Advanced Encryption Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Standard for Advanced Encryption AES algorithm. The benefits include most reliable security protocol, longer key sizes, used for commercial and open-source solutions for many businesses, etc. Present the topic in a bit more detail with this Benefits Of Standard For Advanced Encryption Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Algorithm, Commercial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Triple Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Triple Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the advantages and disadvantages of Triple Data Encryption Standard TDES algorithm. The benefits include strong security, compatibility, simplicity and disadvantages are performance, key length limitation, vulnerability to attacks etc. Deliver an outstanding presentation on the topic using this Benefits Of Triple Data Encryption Standard Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Data Encryption, Compatibility, Performance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age It
Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the differences between Standard for Advanced Encryption AES and Data Encryption Standard DES algorithm. The comparison is carried out based on different factors such as algorithm type, key size, security strength, key expansion, etc. Deliver an outstanding presentation on the topic using this Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Key Expansion, Symmetric Algorithm using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It
Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the differences between RSA Rivest-Shamir-Adleman and DSA Digital Signature Algorithm. The comparison is carried out based on different factors such as algorithm type, key size, security strength, key generation, performance, etc. Present the topic in a bit more detail with this Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric Algorithm, Comparison, Performance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age It
Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age ItThis slide discusses about Data Encryption Standard DES algorithm. The purpose of this slide is to demonstrate the various applications of DES algorithm such as secure data transmission, Automated teller machines, smart cards, etc. Present the topic in a bit more detail with this Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Overview, Applications, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Different Key Encryption Algorithms Encryption For Data Privacy In Digital Age It
Different Key Encryption Algorithms Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various algorithms used to achieve asymmetric key cryptography to secure data transmission. The algorithms outlined are Elliptic Curve Cryptography ECC, RSA Rivest Shamir Adleman, Digital Signature Standard DSS, etc. Present the topic in a bit more detail with this Different Key Encryption Algorithms Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric, Encryption, Algorithms. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Different Symmetric Key Encryption Algorithms Encryption For Data Privacy In Digital Age It
Different Symmetric Key Encryption Algorithms Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various algorithms used to achieve symmetric key encryption to secure data transmission. The algorithms outlined are AES Advanced Encryption Standard, DES Data Encryption Standard, IDEA International Data Encryption Algorithm, Blowfish, etc. Deliver an outstanding presentation on the topic using this Different Symmetric Key Encryption Algorithms Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Symmetric, Encryption, Algorithms using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Disadvantages Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It
Disadvantages Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the drawbacks of using Elliptic Curve Cryptography ECC algorithm. The disadvantages of ECC algorithm are complicated implementation, random number generator, patents, signature verification, etc. Deliver an outstanding presentation on the topic using this Disadvantages Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Cryptography, Algorithm, Disadvantages using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Elliptic Curve Cryptography Ecc Asymmetric Algorithm Encryption For Data Privacy In Digital Age It
Elliptic Curve Cryptography Ecc Asymmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide discusses the Elliptic Curve Cryptography algorithm. The purpose of this slide is to elaborate the different uses of ECC algorithm. The uses of this algorithm are key agreement, mobile devices, cryptocurrency, etc. Present the topic in a bit more detail with this Elliptic Curve Cryptography Ecc Asymmetric Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Algorithms, Asymmetric, Cryptography. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Rivest Shamir Adleman Rsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It
Rivest Shamir Adleman Rsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide discusses the Rivest Shamir Adleman RSA asymmetric algorithm. The purpose of this slide is to represent the benefits and applications of RSA algorithm. The uses of RSA algorithm includes hybrid encryption, digital signatures, etc. Present the topic in a bit more detail with this Rivest Shamir Adleman Rsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Overview, Asymmetric, Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Working Of Common Data Encryption Des Algorithm Encryption For Data Privacy In Digital Age It
Working Of Common Data Encryption Des Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the working flow of Data Encryption Standard DES algorithm. The purpose of this slide is to outline the algorithm steps. This slide also explains the DES modes of operation, which include Digital Codebook, Cipher Block Chaining, etc. Present the topic in a bit more detail with this Working Of Common Data Encryption Des Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Encryption, Independent, Initialization Vector. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Working Steps Of Triple Data Encryption Algorithm Tdea Encryption For Data Privacy In Digital Age It
Working Steps Of Triple Data Encryption Algorithm Tdea Encryption For Data Privacy In Digital Age ItThis slide discusses the procedure of Triple Data Encryption Algorithm TDEA. The purpose of this slide is to explain the TDES encryption and decryption process using Data Encryption algorithm DEA and three keys named as K1, K2 and K3. Present the topic in a bit more detail with this Working Steps Of Triple Data Encryption Algorithm Tdea Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Algorithm, Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Other Popular Blockchain Consensus Algorithms Consensus Mechanisms In Blockchain BCT SS V
Other Popular Blockchain Consensus Algorithms Consensus Mechanisms In Blockchain BCT SS VThis slide covers a brief introduction to various other common blockchain consensus mechanisms. It includes the benefits of proof of identity, delegated PoI, Delegated Byzantine Fault Tolerance dBFT, Leased Proof of Stake LPoS, Directed Acyclic Graph DAG, etc. Present the topic in a bit more detail with this Other Popular Blockchain Consensus Algorithms Consensus Mechanisms In Blockchain BCT SS V Use it as a tool for discussion and navigation on Description, Advantage, Delegated Byzantine This template is free to edit as deemed fit for your organization. Therefore download it now.
-
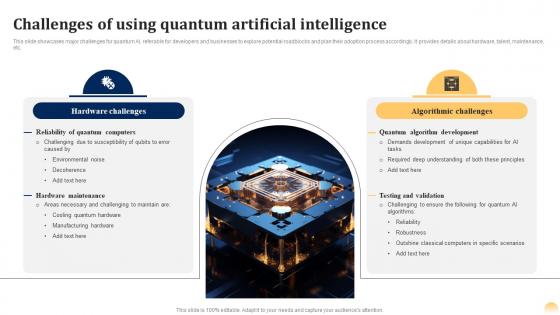 Challenges Of Using Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Challenges Of Using Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases major challenges for quantum AI, referable for developers and businesses to explore potential roadblocks and plan their adoption process accordingly. It provides details about hardware, talent, maintenance, etc. Deliver an outstanding presentation on the topic using this Challenges Of Using Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Dispense information and present a thorough explanation of Artificial Intelligence, Algorithmic Challenges, Hardware Challenges using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
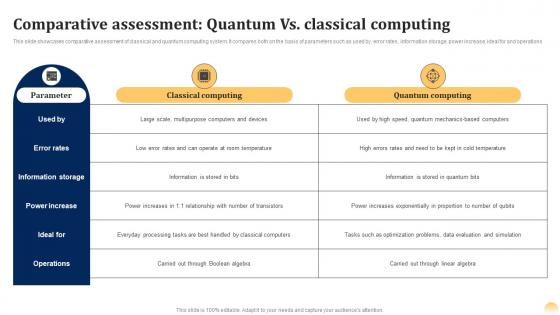 Comparative Assessment Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Comparative Assessment Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases comparative assessment of classical and quantum computing system. It compares both on the basis of parameters such as used by, error rates, information storage, power increase, ideal for and operations Present the topic in a bit more detail with this Comparative Assessment Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Use it as a tool for discussion and navigation on Comparative, Assessment, Classical Computing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Investment Technology By Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Investment Technology By Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide introduction of quantum technology investment ecosystem, guiding futuristic businesses in grabbing opportunities. It provides details about company, country, technology, quantum sensing, communication, etc. Deliver an outstanding presentation on the topic using this Investment Technology By Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Dispense information and present a thorough explanation of Investment, Quantum Computing, Quantum Communications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
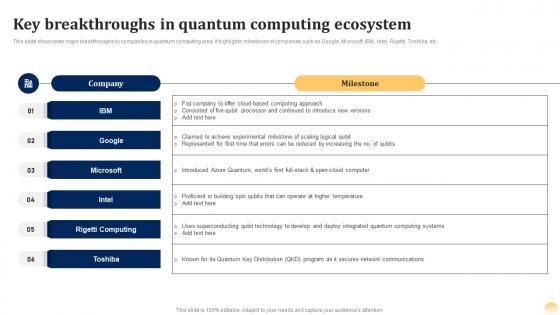 Key Breakthroughs Ecosystem Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Key Breakthroughs Ecosystem Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases major breakthroughs by companies in quantum computing area. It highlights milestones of companies such as Google, Microsoft, IBM, Intel, Rigetti, Toshiba, etc Deliver an outstanding presentation on the topic using this Key Breakthroughs Ecosystem Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Dispense information and present a thorough explanation of Quantum, Computing, Ecosystem using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
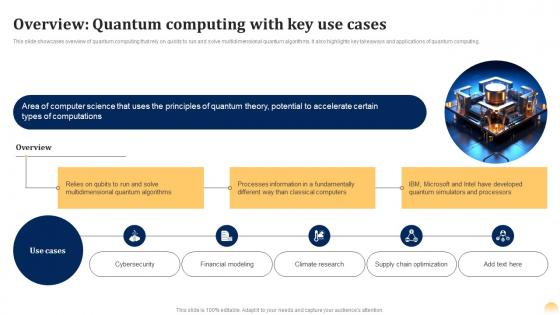 Overview Key Use Cases Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Overview Key Use Cases Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases overview of quantum computing that rely on qubits to run and solve multidimensional quantum algorithms. It also highlights key takeaways and applications of quantum computing. Deliver an outstanding presentation on the topic using this Overview Key Use Cases Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Dispense information and present a thorough explanation of Overview, Computations, Processors using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
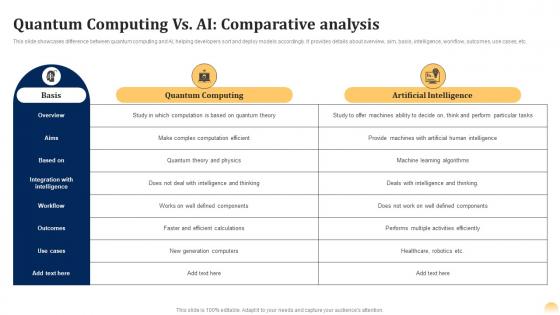 Quantum Computing Vs Ai Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Quantum Computing Vs Ai Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases difference between quantum computing and AI, helping developers sort and deploy models accordingly. It provides details about overview, aim, basis, intelligence, workflow, outcomes, use cases, etc. Deliver an outstanding presentation on the topic using this Quantum Computing Vs Ai Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Dispense information and present a thorough explanation of Artificial Intelligence, Comparative, Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
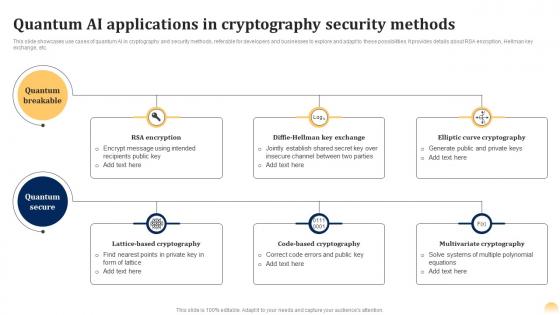 Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases use cases of quantum AI in cryptography and security methods, referable for developers and businesses to explore and adapt to these possibilities. It provides details about RSA encryption, Hellman key exchange, etc. Present the topic in a bit more detail with this Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Use it as a tool for discussion and navigation on Elliptic Curve Cryptography, Code Based Cryptography, Multivariate Cryptography. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
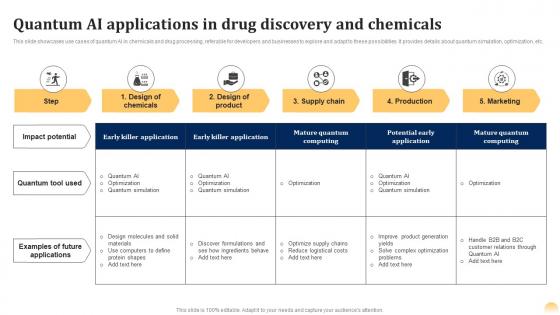 Quantum Discovery And Chemicals Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Quantum Discovery And Chemicals Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases use cases of quantum AI in chemicals and drug processing, referable for developers and businesses to explore and adapt to these possibilities. It provides details about quantum simulation, optimization, etc. Deliver an outstanding presentation on the topic using this Quantum Discovery And Chemicals Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Dispense information and present a thorough explanation of Applications, Production, Product using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
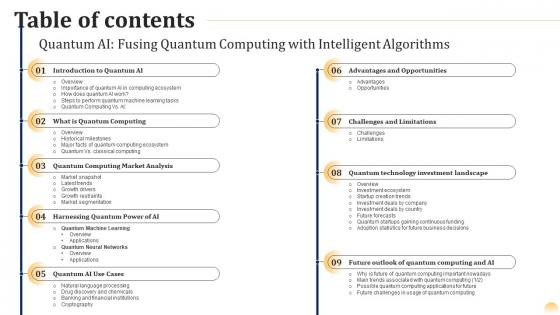 Table Of Contents Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Table Of Contents Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSDeliver an outstanding presentation on the topic using this Table Of Contents Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Dispense information and present a thorough explanation of Harnessing Quantum Power Of AI, Challenges And Limitations, Advantages And Opportunities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
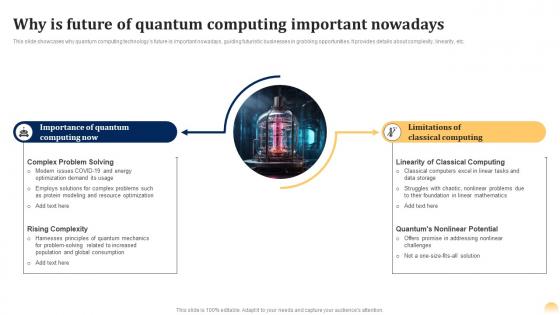 Why Is Quantum Computing Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Why Is Quantum Computing Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases why quantum computing technologys future is important nowadays, guiding futuristic businesses in grabbing opportunities. It provides details about complexity, linearity, etc. Present the topic in a bit more detail with this Why Is Quantum Computing Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Use it as a tool for discussion and navigation on Quantum, Computing, Limitations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Of Operating System Schedulers For Managing Algorithms
Comparison Of Operating System Schedulers For Managing AlgorithmsThis slide demonstrates difference between operating system schedulers to select jobs to be submitted into system and deciding which process to run. It includes aspects such as purpose, speed, control, time sharing system and process. Presenting our well structured Comparison Of Operating System Schedulers For Managing Algorithms. The topics discussed in this slide are Consists Of Job Scheduler, Reduces Degree Of Multiprogramming, Time Sharing System. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Dbscan Clustering Algorithm In Learning Unsupervised Learning Guide For Beginners AI SS
Dbscan Clustering Algorithm In Learning Unsupervised Learning Guide For Beginners AI SSThis slide showcases basic understanding to unsupervised learning algorithm i.e. Density based spatial clustering of applications with Noise DBSCAN, useful for developers in understanding backend process and use cases. It provides details about core points, neighbors, etc. Present the topic in a bit more detail with this Dbscan Clustering Algorithm In Learning Unsupervised Learning Guide For Beginners AI SS. Use it as a tool for discussion and navigation on Cluster Expansion, Border Points, Noise And Outliers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Isolation Forests Algorithm In Unsupervised Learning Unsupervised Learning Guide For Beginners AI SS
Isolation Forests Algorithm In Unsupervised Learning Unsupervised Learning Guide For Beginners AI SSThis slide showcases basic understanding to unsupervised learning algorithm i.e. isolation forests, useful for developers in understanding backend process and use cases. It provides details about random subsampling, tree building, etc. Present the topic in a bit more detail with this Isolation Forests Algorithm In Unsupervised Learning Unsupervised Learning Guide For Beginners AI SS. Use it as a tool for discussion and navigation on Random Subsampling, Path Length Calculation, Anomaly Identification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 K Means Clustering Algorithm In Unsupervised Learning Guide For Beginners AI SS
K Means Clustering Algorithm In Unsupervised Learning Guide For Beginners AI SSThis slide showcases basic understanding to unsupervised learning algorithm i.e. K-means clustering, useful for developers in understanding backend process and use cases. It provides details about centroids, convergence, data points, etc. Deliver an outstanding presentation on the topic using this K Means Clustering Algorithm In Unsupervised Learning Guide For Beginners AI SS. Dispense information and present a thorough explanation of Initiation, Assignment, Update Centroids using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Pca Dimensionality Algorithm In Unsupervised Learning Guide For Beginners AI SS
Pca Dimensionality Algorithm In Unsupervised Learning Guide For Beginners AI SSThis slide showcases basic understanding to unsupervised learning algorithm i.e. Principal Component Analysis PCA, useful for developers in understanding backend process and use cases. It provides details about data centering, covariance, etc. Present the topic in a bit more detail with this Pca Dimensionality Algorithm In Unsupervised Learning Guide For Beginners AI SS. Use it as a tool for discussion and navigation on Data Centering, Covariance Matrix, Eigenvalue Decomposition. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Unsupervised Learning Guide For Beginners Svd Dimensionality Algorithm In Unsupervised Learning AI SS
Unsupervised Learning Guide For Beginners Svd Dimensionality Algorithm In Unsupervised Learning AI SSThis slide showcases basic understanding to unsupervised learning algorithm i.e. Singular Value Decomposition SVD, useful for developers in understanding backend process and use cases. It provides details about matrix, singular values, etc. Deliver an outstanding presentation on the topic using this Unsupervised Learning Guide For Beginners Svd Dimensionality Algorithm In Unsupervised Learning AI SS. Dispense information and present a thorough explanation of Dimensionality, Algorithm, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cryptomining Innovations And Trends Steps To Perform Mining In Proof Of Activity Poa Algorithm
Cryptomining Innovations And Trends Steps To Perform Mining In Proof Of Activity Poa AlgorithmThis slide illustrates the workings of Proof of Activity PoA. The purpose is to showcase the step-by-step procedure followed by PoA, such as PoW mining, transitioning to PoS, selecting validators, and determining validators based on coin ownership, among others. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Steps To Perform Mining In Proof Of Activity Poa Algorithm. Use it as a tool for discussion and navigation on Validation And Signing, Selecting Validators, Rewards Distribution, Handling Unavailable Signers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Green Cloud Computing Algorithms Overview Carbon Free Computing
Green Cloud Computing Algorithms Overview Carbon Free ComputingThis slide represents the overview of algorithms used in green cloud computing. The purpose of this slide is to showcase the Green IT algorithms and their working. The main algorithms include the green generic algorithm, improved clonal selection algorithm, and green algorithm. Deliver an outstanding presentation on the topic using this Green Cloud Computing Algorithms Overview Carbon Free Computing. Dispense information and present a thorough explanation of Green Genetic Algorithm, Improved Clonal Selection Algorithm, Green Algorithm using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative Assessment Of Hashing And Encryption Algorithm
Comparative Assessment Of Hashing And Encryption AlgorithmThis slide represents analysis of hashing and encryption methods which assists to understand key differences among two algorithms. It includes comparative analysis of hashing and encryption algorithm on various parameters such as encoding process, encryption technique, objective, etc. Introducing our Comparative Assessment Of Hashing And Encryption Algorithm set of slides. The topics discussed in these slides are Parameters, Hashing, Encryption. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Wireless Mesh Networks Routing Algorithms Ppt Slides Visuals
Wireless Mesh Networks Routing Algorithms Ppt Slides VisualsThis slide outlines the different routing algorithms for wireless mesh networks that transmit data, such as round robin, congestion aware, backup path, etc. Deliver an outstanding presentation on the topic using this Wireless Mesh Networks Routing Algorithms Ppt Slides Visuals. Dispense information and present a thorough explanation of Strategies, Congestion Aware, Unequal Cost Scheme using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Algorithms Used To Boost Market Positioning
Algorithms Used To Boost Market PositioningThis slide depicts the algorithms used for market positioning by understanding various aspects. Its aim is to improve brand image, profits and customer loyalty. Introducing our Algorithms Used To Boost Market Positioning set of slides. The topics discussed in these slides are Positioning, Cluster Analysis, Conjoint Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Learning Algorithms In Finance Revolutionizing Finance Industry With Machine Learning ML SS
Learning Algorithms In Finance Revolutionizing Finance Industry With Machine Learning ML SSThis slide covers popular machine learning algorithms used in the finance industry according to learning types. It includes learning types such as supervised, unsupervised, and reinforcement. Present the topic in a bit more detail with this Learning Algorithms In Finance Revolutionizing Finance Industry With Machine Learning ML SS. Use it as a tool for discussion and navigation on Supervised Learning, Unsupervised Learning, Reinforcement Learning. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Training 3 Algorithm And Techniques Blockchain Training Program For Business Professionals DTE SS
Training 3 Algorithm And Techniques Blockchain Training Program For Business Professionals DTE SSMentioned slide provides information about covered concept under the module 3 algorithm and techniques which covers public key cryptography, hashing transaction integration, and securing blockchain. Deliver an outstanding presentation on the topic using this Training 3 Algorithm And Techniques Blockchain Training Program For Business Professionals DTE SS. Dispense information and present a thorough explanation of Asymmetric Cryptography, Transaction Integrity, Securing Blockchain using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Types Of Supervised Machine Learning Algorithms Supervised Machine Learning ML SS
Types Of Supervised Machine Learning Algorithms Supervised Machine Learning ML SSThis slide breaks down the two main types of supervised learning, classification and regression, highlighting their key features. Introducing Types Of Supervised Machine Learning Algorithms Supervised Machine Learning ML SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Categorical Values, Real Numbers, Continuous Output using this template. Grab it now to reap its full benefits.
-
 Data Encryption Algorithms For Security Solutions
Data Encryption Algorithms For Security SolutionsThe purpose of this slide is to demonstrate how data encryption algorithms for security solutions enhance protection. It encode data to prevent unauthorized access or manipulation. Introducing our Data Encryption Algorithms For Security Solutions set of slides. The topics discussed in these slides are Advanced Encryption Standard, Rivest Shamir Adleman, Elliptic Curve Cryptography. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.



