Powerpoint Templates and Google slides for Strategies Implement
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Deploying QMS Benefits Of Implementing Effective Quality Strategy In Business Strategy SS V
Deploying QMS Benefits Of Implementing Effective Quality Strategy In Business Strategy SS VThis slide covers key advantages of integrating effective quality strategy in business to enhance overall efficiency. It involves benefits such as improved customer satisfaction, reduces costs and enhanced organizational reputation. Introducing Deploying QMS Benefits Of Implementing Effective Quality Strategy In Business Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Improved Customer Satisfaction, Reduces Costs, Enhanced Reputation, using this template. Grab it now to reap its full benefits.
-
 Deploying QMS Implementing Quality Assurance To Create Cost Efficiency Strategy SS V
Deploying QMS Implementing Quality Assurance To Create Cost Efficiency Strategy SS VThis slide covers implementing quality assurance strategy to improve production and cost efficiency. It involves key tasks such as conduct process review, create project status report and perform compliance review. Introducing Deploying QMS Implementing Quality Assurance To Create Cost Efficiency Strategy SS V to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Conduct Process, Project Status Report, Perform Compliance, using this template. Grab it now to reap its full benefits.
-
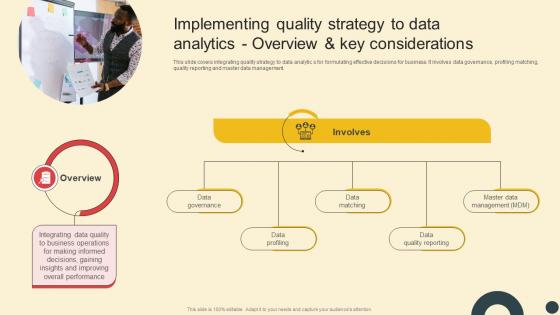 Deploying QMS Implementing Quality Strategy To Data Analytics Overview Strategy SS V
Deploying QMS Implementing Quality Strategy To Data Analytics Overview Strategy SS VThis slide covers integrating quality strategy to data analytic s for formulating effective decisions for business. It involves data governance, profiling matching, quality reporting and master data management. Increase audience engagement and knowledge by dispensing information using Deploying QMS Implementing Quality Strategy To Data Analytics Overview Strategy SS V. This template helps you present information on one stage. You can also present information on Overview, Quality Strategy, Data Analytics, Overview using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Deploying QMS Introduction To Implementing Quality Strategy In Manufacturing Strategy SS V
Deploying QMS Introduction To Implementing Quality Strategy In Manufacturing Strategy SS VThis slide covers overview to implementing quality management strategy in manufacturing process. It highlights four key components such quality planning, control and quality assurance. Increase audience engagement and knowledge by dispensing information using Deploying QMS Introduction To Implementing Quality Strategy In Manufacturing Strategy SS V. This template helps you present information on two stages. You can also present information on Introduction, Quality Planning, Quality Control, Quality Assurance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices Of Email Marketing Strategy Complete Guide To Implement Email
Best Practices Of Email Marketing Strategy Complete Guide To Implement EmailMentioned slide outlines various best practices which can be implemented by business in email marketing for enhancing customer satisfaction. It includes key points such as welcome email, casual conversation, optimize subject line and email consistent management. Increase audience engagement and knowledge by dispensing information using Best Practices Of Email Marketing Strategy Complete Guide To Implement Email. This template helps you present information on four stages. You can also present information on Email Address, Optimize Subject Line, Casual Conversation Email using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Email List Development Strategies To Improve Customized Complete Guide To Implement Email
Email List Development Strategies To Improve Customized Complete Guide To Implement EmailMentioned slide provides information about key strategies which can be used by businesses for developing and growing email list. It includes key strategies such as pop up offers on homepage, opt-in forms, social media signup and newsletters letter signup. Present the topic in a bit more detail with this Email List Development Strategies To Improve Customized Complete Guide To Implement Email. Use it as a tool for discussion and navigation on Social Media Signup, Newsletters Signup At Checkout. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide Complete Guide To Implement Email Promotion Strategy
Icons Slide Complete Guide To Implement Email Promotion StrategyIntroducing our well researched set of slides titled Icons Slide Complete Guide To Implement Email Promotion Strategy. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Key Trends Of Email Marketing Strategy Complete Guide To Implement Email
Key Trends Of Email Marketing Strategy Complete Guide To Implement EmailMentioned slide showcases key trends associates with email marketing strategy which can be leveraged by business to connect with customers. It includes key trends related to Artificial intelligence, hyper personalisation, interactivity, automation mobile optimization, and customer appreciation email. Introducing Key Trends Of Email Marketing Strategy Complete Guide To Implement Email to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Optimization, Customer Appreciation Emails, Interactivity, using this template. Grab it now to reap its full benefits.
-
 Strategies For Enhancing Email Marketing Campaign Complete Guide To Implement Email
Strategies For Enhancing Email Marketing Campaign Complete Guide To Implement EmailFollowing slide provides information about various email marketing campaign improvement strategies which can be used by businesses for product promotion. It includes key strategies such as message customization, subscriber segmentation, mobile friendly email design, routine testing, and email campaign automation. Introducing Strategies For Enhancing Email Marketing Campaign Complete Guide To Implement Email to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Message Customization, Multiple Device Friendly Emails, Routine Testing, using this template. Grab it now to reap its full benefits.
-
 Impact Of Influencer Marketing Pre And Post Implementation Social Media Influencer Strategy SS V
Impact Of Influencer Marketing Pre And Post Implementation Social Media Influencer Strategy SS VThis slide represents the comparison between current and past scenario of business operations to analyze the impact of implemented influencer marketing techniques on business operations. It includes analysis of KPIs such as brand awareness, social engagement rate etc. Present the topic in a bit more detail with this Impact Of Influencer Marketing Pre And Post Implementation Social Media Influencer Strategy SS V. Use it as a tool for discussion and navigation on Brand Awareness, Social Engagement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Solutions Offered By Implemented Influencer Marketing Tool Social Media Influencer Strategy SS V
Solutions Offered By Implemented Influencer Marketing Tool Social Media Influencer Strategy SS VThis slide represents the key benefits offered by the influencer marketing platform deployed by the enterprise to streamline the procedure of collaborating with influencers. It includes solutions such as contact relationship management etc. Introducing Solutions Offered By Implemented Influencer Marketing Tool Social Media Influencer Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Contact Relationship Management, Integration With Other Channels, using this template. Grab it now to reap its full benefits.
-
 Major Benefits Of Implementing Transnational Strategy Worldwide Approach Strategy SS V
Major Benefits Of Implementing Transnational Strategy Worldwide Approach Strategy SS VThis slide covers the key advantages of following a transnational expansion strategy, such as global efficiency, local responsiveness, innovation, risk management, and talent development. Increase audience engagement and knowledge by dispensing information using Major Benefits Of Implementing Transnational Strategy Worldwide Approach Strategy SS V. This template helps you present information on five stages. You can also present information on Global Efficiency, Local Responsiveness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Checklist To Implement Data Encryption Technology
Encryption Implementation Strategies Checklist To Implement Data Encryption TechnologyThis slide outlines the steps to be taken to protect the organizations data using encryption. The key approaches include identify sensitive data, assess requirements, select method, implement encryption, test functionality, establish monitoring, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Checklist To Implement Data Encryption Technology. Dispense information and present a thorough explanation of Assess Requirements, Implement Encryption, Establish Monitoring, Test Functionality using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Comparison Between Column Level And Whole Database Encryption
Encryption Implementation Strategies Comparison Between Column Level And Whole Database EncryptionThe purpose of this slide is to outline the differences between column level and whole database encryption technologies. This slide compares the mentioned techniques based on several parameters such as scope, level of encryption, flexibility, compliance, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Comparison Between Column Level And Whole Database Encryption. Dispense information and present a thorough explanation of Whole Database Encryption, Flexibility, Compliance, Mentioned Techniques, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Comparison Between Digital Rights Management Software
Encryption Implementation Strategies Comparison Between Digital Rights Management SoftwareThis slide outlines the available Digital Rights Management DRM software for several industries, such as information technology and services, marketing and advertising, consumer goods, automotive, civil engineering, architecture and planning, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Comparison Between Digital Rights Management Software. Use it as a tool for discussion and navigation on Marketing And Advertising, Architecture And Planning, Information Technology And Services. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Comparison Between Full Disk And File Level Encryption
Encryption Implementation Strategies Comparison Between Full Disk And File Level EncryptionThis slide discusses the two main types of encryption used for computers, known as full-disk encryption FDE and file-level encryption FLE. The purpose of this slide is to compare both encryption techniques based on different parameters. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Comparison Between Full Disk And File Level Encryption. This template helps you present information on two stages. You can also present information on Full Disk Encryption, File Level Encryption, Operating System And System Files using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Comparison Between Various VPN Protocols
Encryption Implementation Strategies Comparison Between Various VPN ProtocolsThis slide discusses different Virtual Private Network VPN protocols based on several factors, such as encryption, algorithms used, security level and speed. These protocols are IKEv2, OpenVPN, L2TP, WireGuard, SSTP Secure Socket Tunnelling Protocol, and PPTP. Present the topic in a bit more detail with this Encryption Implementation Strategies Comparison Between Various VPN Protocols. Use it as a tool for discussion and navigation on Virtual Private Network, Algorithms Used, Security Level And Speed, Secure Socket Tunnelling Protocol. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Data Security Concerns Faced By Company
Encryption Implementation Strategies Data Security Concerns Faced By CompanyThis slide discusses the security issues faced by the organization due to a lack of encryption and data protection technologies. These concerns are unauthorized access, data breaches, insider threats, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Security Concerns Faced By Company. Dispense information and present a thorough explanation of Data Security Concerns, Phishing Attacks, Data Protection Technologies, Compliance And Regulations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Database Encryption Methods For Business Security
Encryption Implementation Strategies Database Encryption Methods For Business SecurityThis slide discusses the database encryption methods used to encrypt the data of different departments, such as finance, sales, and human resources. The database encryption levels are application-level encryption, plug-in method, TDE, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Database Encryption Methods For Business Security. Use it as a tool for discussion and navigation on Database Encryption Methods, Business Security, Sales And Human Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Encryption As A Service Overview And Features
Encryption Implementation Strategies Encryption As A Service Overview And FeaturesThis slide discusses the Encryption-as-a-Service model of securing data using cryptographic techniques. This slide also outlines the characteristics of Encryption-as-a-Service, such as confidentiality, authentication, integrity, nonrepudiation, etc. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Encryption As A Service Overview And Features. This template helps you present information on six stages. You can also present information on Text Message Encoding, Encryption Services, Subscription Packages, Data Encryption Security Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Encryption As A Service Providers To Safeguard Network
Encryption Implementation Strategies Encryption As A Service Providers To Safeguard NetworkThis slide outlines the companies which provide EaaS services to secure data in a network. The purpose of this slide is to demonstrate the services and benefits of several EaaS providers such as CloudHesive, FortKnoxter, Hashicrop, Identos, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption As A Service Providers To Safeguard Network. Dispense information and present a thorough explanation of Encryption As A Service, Safeguard Network Communication, Internal Revocation System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Encryption Key Management Software For Byoe
Encryption Implementation Strategies Encryption Key Management Software For ByoeThe purpose of this slide is to demonstrate the importance of encryption key management EKM software. The key components included are encryption algorithm, customer master key, plaintext data key, encrypted data key, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Encryption Key Management Software For Byoe. Use it as a tool for discussion and navigation on Encryption Algorithm, Customer Master Key, Encrypted Data Key, Key Management Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest
Encryption Implementation Strategies Encryption Technologies To Secure Data At RestThis slide compares different data protection methods, highlighting their advantages and limitations. These methods are full disk encryption, file-level encryption, database encryption, information rights management IRM, data leak prevention DLP,etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Full Disk Encryption, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation
Encryption Implementation Strategies Estimated Budget Of Data Encryption ImplementationThis slide represents the budget for securing data using encryption techniques. The purpose of this slide is to showcase the estimated and actual cost for installing cryptographic solutions. The components include hardware and software, maintenance and support, training, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation. Use it as a tool for discussion and navigation on Maintenance And Support, Deployment Team, Data Encryption, Estimated Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies For Table Of Contents Ppt Ideas Templates
Encryption Implementation Strategies For Table Of Contents Ppt Ideas TemplatesIntroducing Encryption Implementation Strategies For Table Of Contents Ppt Ideas Templates to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Safeguard Network Communication, Encryption Key Management Software, Applications Of Encryption As A Service, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Hardware And Software Tools For Full Disk Encryption
Encryption Implementation Strategies Hardware And Software Tools For Full Disk EncryptionThis slide demonstrates the two tools available for full disk encryption. These are hardware based full disk encryption such as self-encrypting drives SEDs and software based full disk encryption, which include Microsoft BitLocker or Apple FileVault. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Hardware And Software Tools For Full Disk Encryption. This template helps you present information on two stages. You can also present information on Hardware And Software Tools, Full Disk Encryption, Microsoft Bitlocker, Apple Filevault using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle
Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric CleThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Introducing Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Method, Asymmetric Method, Asymmetric Column Level Encryption, Symmetric Column Level Encryption, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security
Encryption Implementation Strategies Impact Of Encryption Implementation On Application SecurityThis slide represents the various factors which showcase the improvement of application security after adopting encryption. The parameters discussed are data privacy, confidentiality, authentication, compliance, trust and reputation, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security. Dispense information and present a thorough explanation of Confidentiality, Data Privacy, Trust And Reputation, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Introduction To Fully Homomorphic Encryption Technology
Encryption Implementation Strategies Introduction To Fully Homomorphic Encryption TechnologyThe purpose of this slide is to provide a summary of the outcomes of regulatory compliance management strategies, such as avoid unnecessary legal issues, foster healthy competition, etc. It highlights their business impact and advantages to organizations. Present the topic in a bit more detail with this Encryption Implementation Strategies Introduction To Fully Homomorphic Encryption Technology. Use it as a tool for discussion and navigation on Encrypted Program Input Data, Encrypted Program Output, Decrypted Program Output, Trusted Data Storage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Key Components Of Internet Protocol Security
Encryption Implementation Strategies Key Components Of Internet Protocol SecurityThe purpose of this slide is to discuss the main components of internet protocol security IPsec architecture. These three components are encapsulating security payload ESP, authentication header AH, and internet key exchange IKE. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Key Components Of Internet Protocol Security. Dispense information and present a thorough explanation of Data Integrity, Encryption, Anti Replay, Payload Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Key Considerations For Selecting File Encryption Software
Encryption Implementation Strategies Key Considerations For Selecting File Encryption SoftwareThis slide represents a guide for selecting a file encryption software based on several key factors. These considerations are threat analysis, encryption layers, training needs, compatibility, encryption scope, vendors incident response plan, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Key Considerations For Selecting File Encryption Software. Use it as a tool for discussion and navigation on Encryption Software, Training Needs, Compatibility, Encryption Scope, Training Timelines. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms
Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption AlgorithmsThis slide outlines several data encryption algorithms. The purpose of this slide is to divide all available cryptographic algorithms into two types of encryption, namely symmetric and asymmetric. These algorithms are 3DES encryption, Twofish encryption, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms. Dispense information and present a thorough explanation of Data Encryption Standard, Triple Data Encryption Standard, Digital Signature Algorithm, Elliptic Curve Cryptography using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Microsoft Full Disk Encryption Bitlocker
Encryption Implementation Strategies Microsoft Full Disk Encryption BitlockerThis slide discusses the full disk windows encryption technique provided by Microsoft, known as BitLocker. The purpose of this slide is to outline the step-by-step process to enable the BitLocker encryption in computer system. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Microsoft Full Disk Encryption Bitlocker. This template helps you present information on nine stages. You can also present information on Microsoft Full Disk Encryption, Disc Characteristics, Trusted Platform Module, Automatically Be Encrypted using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Organizational Compliance Regulations For Information Security
Encryption Implementation Strategies Organizational Compliance Regulations For Information SecurityThe purpose of this slide is to summarize the most common regulations that organizations need to comply with, and their requirements. These regulations are HIPAA Health Insurance Portability and Accountability Act, SOX, PCI DSS, breach laws in all US states, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Organizational Compliance Regulations For Information Security. Use it as a tool for discussion and navigation on Health Insurance Portability, Accountability Act, Payment Card Industry, Data Security Standard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Outcomes Of Regulatory Compliance Management Strategies
Encryption Implementation Strategies Outcomes Of Regulatory Compliance Management StrategiesThe purpose of this slide is to provide a summary of the outcomes of regulatory compliance management strategies, such as avoid unnecessary legal issues, foster healthy competition, etc. It highlights their business impact and advantages to organizations. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Outcomes Of Regulatory Compliance Management Strategies. Dispense information and present a thorough explanation of Foster Healthy Competition, Gain Better Branding, Regulatory Compliance, Management Strategies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Roadmap To Encrypt Application Data Of Organization
Encryption Implementation Strategies Roadmap To Encrypt Application Data Of OrganizationThis slide represents the roadmap to implement encryption security in an organization. The main components included are are identify sensitive data, assess encryption requirements, choose encryption algorithms, implement data encryption at rest, etc. Introducing Encryption Implementation Strategies Roadmap To Encrypt Application Data Of Organization to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Security, Identify Sensitive Data, Assess Encryption Requirements, Encryption Algorithms, Implement Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Steps For Quantum Safe Certificate Migration
Encryption Implementation Strategies Steps For Quantum Safe Certificate MigrationThis slide demonstrates the process of replicating the old certificates with quantum-safe certificates. The steps included are quantum-safe PKI, update servers cryptography, update clients cryptography, install QS roots, install QS certificates, and deprecate old cryptography. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Steps For Quantum Safe Certificate Migration. Dispense information and present a thorough explanation of Quantum Safe Certificate Migration, Deprecate Old Cryptography, Support Recent Algorithms using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Steps Involved In Working Of Cloud Storage Encryption
Encryption Implementation Strategies Steps Involved In Working Of Cloud Storage EncryptionThis slide demonstrates the working process of cloud encryption technique to secure data stored in the cloud. The purpose of this slide is to discuss two main components of cloud cryptography, known as data-in-transit and data-at-rest. Present the topic in a bit more detail with this Encryption Implementation Strategies Steps Involved In Working Of Cloud Storage Encryption. Use it as a tool for discussion and navigation on Cloud Storage Encryption, Data In Transit, Cloud Cryptography, Cloud Encryption Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Steps To Implement Regulatory Compliance Plan
Encryption Implementation Strategies Steps To Implement Regulatory Compliance PlanThe purpose of this slide is to outline the critical steps involved in implementing a compliance plan to ensure data protection and privacy. These steps include auditing the environment, hiring a compliance officer, maintaining policies, providing employee training, etc. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Steps To Implement Regulatory Compliance Plan. This template helps you present information on six stages. You can also present information on Maintain Policies, Regulatory Compliance Plan, Continuous Improvement, Audit Existing Environment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Steps To Set Up Field Level Encryption
Encryption Implementation Strategies Steps To Set Up Field Level EncryptionThis slide represents the process of setting up field level encryption technology. The key steps involved in this procedure are identify sensitive fields and select encryption method, get encryption keys, make a profile for field-level encryption, etc. Introducing Encryption Implementation Strategies Steps To Set Up Field Level Encryption to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Identify Sensitive Fields, Select Encryption Method, Get Encryption Keys, Symmetric Or Asymmetric, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Symmetric Key Data Encryption Technique
Encryption Implementation Strategies Symmetric Key Data Encryption TechniqueThis slide illustrates the steps involved in transferring data using symmetric encryption. The purpose of this slide is to demonstrate how symmetric key encryption works. The critical components included are the sender, symmetric key, encrypted data, etc. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Symmetric Key Data Encryption Technique. This template helps you present information on five stages. You can also present information on Encrypted Data, Symmetric Key, Data Encryption Technique, Non Understandable Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Timeline To Implement Data Encryption In Organization
Encryption Implementation Strategies Timeline To Implement Data Encryption In OrganizationThe purpose of this slide is to represent the timeline to implement data encryption in an organization. The main phases highlighted in this slide are planning, research and evaluation, development, testing and quality assurance, deployment, etc. Introducing Encryption Implementation Strategies Timeline To Implement Data Encryption In Organization to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Development Phase, Testing And Quality Assurance Phase, Research And Evaluation Phase, Planning Phase, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data Protection
Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data ProtectionThe purpose of this slide is to summarize several relevant regulations. These are GDPR General Data Protection Regulation, CCPA California Consumer Privacy Act, PCI DSS Payment Card Industry Data Security Standard, NIST, and HIPAA, along with their descriptions and scopes. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data Protection. Dispense information and present a thorough explanation of General Data Protection Regulation, California Consumer Privacy Act, Health Insurance Portability And Accountability Act using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Training Program For Data Encryption Implementation
Encryption Implementation Strategies Training Program For Data Encryption ImplementationThis slide describes the training program for employees to implement data encryption in an organization. The main components of training program are agenda, system requirements, mode such as online, offline or recorded videos, and cost. Present the topic in a bit more detail with this Encryption Implementation Strategies Training Program For Data Encryption Implementation. Use it as a tool for discussion and navigation on Symmetric And Asymmetric Cryptography, Data Encryption Best Practices, Case Studies And Practical, Implementing Cryptographic Techniques. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Transport Layer Security Implementation Using Handshake
Encryption Implementation Strategies Transport Layer Security Implementation Using HandshakeThis slide discusses a cryptographic system known as transport layer security TLS. The purpose of this slide is to explain how TLS enables safe communication over computer networks using handshake protocol and record protocol. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Transport Layer Security Implementation Using Handshake. This template helps you present information on two stages. You can also present information on Transport Layer Security Implementation, Handshake And Record Protocol, Computer Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Understanding Virtual Private Network Protocols
Encryption Implementation Strategies Understanding Virtual Private Network ProtocolsThis slide discusses Virtual Private Network VPN to enable secure and private communication over public networks by creating an encrypted tunnel between users device and the VPN server. It also highlights remote access and site-to-site VPN. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Understanding Virtual Private Network Protocols. Dispense information and present a thorough explanation of Virtual Private Network Protocols, Secure And Private Communication, Support Its Configuration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Understanding Working Of Quantum Encryption Technology
Encryption Implementation Strategies Understanding Working Of Quantum Encryption TechnologyThis slide demonstrates the steps involved in encrypting and decrypting the keys using quantum cryptography. The steps involved are passing the photon to receiver, receive the photon, set the kay by analysing correct streams and verify the authenticity of data. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Understanding Working Of Quantum Encryption Technology. This template helps you present information on four stages. You can also present information on Passing The Photon To Receiver, Verify Authenticity Of Data, Working Of Quantum, Encryption Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Implementation Strategies Virtual Private Networks Configuration And Implementation
Encryption Implementation Strategies Virtual Private Networks Configuration And ImplementationThe purpose of this slide is to illustrate the process of tunnel creation between users device and the VPN server, which protects user data from interception. The key components include the user device, VPN client, VPN tunnel, server, and internet. Introducing Encryption Implementation Strategies Virtual Private Networks Configuration And Implementation to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Advertisers, Government Agencies, Virtual Private Networks, Configuration And Implementation Process, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Working Of Bring Your Own Encryption Model
Encryption Implementation Strategies Working Of Bring Your Own Encryption ModelThe purpose of this slide is to explain the importance of Bring Your Own Encryption BYOE approach. It also explains the deployment of encryption software and their applications hosted on a Cloud Service Provider CSP. The key components included are client apps, ciphertext, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Working Of Bring Your Own Encryption Model. Use it as a tool for discussion and navigation on Cloud Service Provider, Own Encryption Model, Secured Ciphertext, Clients Own Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies Working Of Client Slide Field Level Encryption
Encryption Implementation Strategies Working Of Client Slide Field Level EncryptionThis slide illustrates the process of client-side field level encryption CSFLE. The key components demonstrated in the working process of CSFLE are app code, plaintext, field level encryption library, key store, ciphertext, data store, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Working Of Client Slide Field Level Encryption. Dispense information and present a thorough explanation of Working Of Client Slide, Field Level Encryption, Ciphertext, Data Store using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Working Steps Of Asymmetric Key Encryption
Encryption Implementation Strategies Working Steps Of Asymmetric Key EncryptionThis slide demonstrates the steps included in the working process of asymmetric key cryptography. The purpose of this slide is to illustrate the flow diagram of public key encryption. The key components included are registration, lookup, encrypt, decode, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Working Steps Of Asymmetric Key Encryption. Use it as a tool for discussion and navigation on Working Steps Of Asymmetric, Encrypt, Public Key Encryption, Asymmetric Key Cryptography. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies
Encryption Technologies To Secure Data In Transit Encryption Implementation StrategiesThis slide compares different data in transit protection methods, including their working and associated cost. These methods are email encryption, Managed File Transfer MFT, Data Leak Prevention DLP, Cloud Access Security Brokers CASB, etc. Deliver an outstanding presentation on the topic using this Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Managed File Transfer, Cloud Access Security Brokers, Email Encryption, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies
Overview Of Encryption For Securing Data At Rest Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data at rest. The storage methods include file servers, network shares, document management systems, external storage, databases, endpoint devices, mobile devices, cloud storage, etc. Present the topic in a bit more detail with this Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies. Use it as a tool for discussion and navigation on Database Encryption, Information Rights Management, Data Leak Prevention, Mobile Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 How Adidas Implemented Digital Marketing Strategy Critical Evaluation Of Adidas Strategy SS
How Adidas Implemented Digital Marketing Strategy Critical Evaluation Of Adidas Strategy SSThis slide showcases various techniques how Adidas executes it sponsorship and endorsement strategy. It incorporates strategies such as sports team and event sponsorship, athlete endorsement, partnership with influencer, etc. Introducing How Adidas Implemented Digital Marketing Strategy Critical Evaluation Of Adidas Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Influencer Marketing, Content Marketing, Email Marketing using this template. Grab it now to reap its full benefits.
-
 How Adidas Implemented Experiential Marketing Strategy Critical Evaluation Of Adidas Strategy SS
How Adidas Implemented Experiential Marketing Strategy Critical Evaluation Of Adidas Strategy SSThis slide showcases various techniques how Adidas executes it sponsorship and endorsement strategy. It incorporates strategies such as sports team and event sponsorship, athlete endorsement, partnership with influencer, etc. Present the topic in a bit more detail with this How Adidas Implemented Experiential Marketing Strategy Critical Evaluation Of Adidas Strategy SS Use it as a tool for discussion and navigation on Pop Up And Events, Augmented Reality, Marketing Strategy This template is free to edit as deemed fit for your organization. Therefore download it now.




