Powerpoint Templates and Google slides for Strategies Implement
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyberterrorism Framework In Digital Age Strategic Guide To Implement Strategy SS
Cyberterrorism Framework In Digital Age Strategic Guide To Implement Strategy SSIncrease audience engagement and knowledge by dispensing information using Cyberterrorism Framework In Digital Age Strategic Guide To Implement Strategy SS. This template helps you present information on one stages. You can also present information on Threat Actors, Targeted Servers, Legitimate User, Obfuscate Their Identities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Dark Web And Encrypted Communications In Cyberterrorism Strategic Guide To Implement Strategy SS
Dark Web And Encrypted Communications In Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the Dark web and encrypted communications in cyber terrorism. It includes elements such as definition, characteristics, implications and use cases.Introducing Dark Web And Encrypted Communications In Cyberterrorism Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Implications, Use Cases, Characteristics, Define, using this template. Grab it now to reap its full benefits.
-
 Denial Of Service Dos And Distributed Denial Of Service Ddos Strategic Guide To Implement Strategy SS
Denial Of Service Dos And Distributed Denial Of Service Ddos Strategic Guide To Implement Strategy SSThis slide showcases the Denial-of-Service DoS and Distributed Denial-of-Service DDoS Attacks. It also includes mitigation measures such as firewalls that used to determine inbound requests to website are legitimate.Present the topic in a bit more detail with this Denial Of Service Dos And Distributed Denial Of Service Ddos Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Mitigation Measures, Example, Firewalls, Handle Legitimate Service Requests. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 DNS Spoofing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
DNS Spoofing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the DNS spoofing attack with mitigation strategies and example. It also includes mitigation strategies such as use DNSSEC, use trusted DNS servers and frequent monitoring DNS software.Introducing DNS Spoofing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Description, Mitigation Strategies, Example, using this template. Grab it now to reap its full benefits.
-
 Eavesdropping Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
Eavesdropping Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the Eavesdropping attack with mitigation strategies and example. It also includes mitigation strategies such as secure networks and endpoint security.Increase audience engagement and knowledge by dispensing information using Eavesdropping Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS. This template helps you present information on three stages. You can also present information on Description, Mitigation Strategies, Example using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Economic Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SS
Economic Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the economic motivations and goals of cyber terrorism. It includes goals such as financial gain, stock manipulation, black market activities and extortion.Introducing Economic Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Financial Gain, Stock Manipulation, Black Market Activities, Extortion, using this template. Grab it now to reap its full benefits.
-
 Education And Awareness Campaigns For Cyber Terrorism Strategic Guide To Implement Strategy SS
Education And Awareness Campaigns For Cyber Terrorism Strategic Guide To Implement Strategy SSThis slide showcases the Education and Awareness Campaigns for cyber terrorism. It includes best practices such as Government and Industry Partnership, Interactive Training, Public-Private Partnerships and Online Resources.Increase audience engagement and knowledge by dispensing information using Education And Awareness Campaigns For Cyber Terrorism Strategic Guide To Implement Strategy SS. This template helps you present information on four stages. You can also present information on Interactive Training, Government And Industry Partnerships, Public Private Partnerships, Online Resources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Emerging Threats Quantum Computing And Ai Strategic Guide To Implement Strategy SS
Emerging Threats Quantum Computing And Ai Strategic Guide To Implement Strategy SSThis slide showcases the Emerging Threats Quantum Computing and AI. It includes elements such as defining Quantum computers and AI and its implications.Introducing Emerging Threats Quantum Computing And Ai Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Quantum Computers, Secure Communication, Quantum Computing, Artificial Intelligence, using this template. Grab it now to reap its full benefits.
-
 Global Historical Evolution Of Cyberterrorism Strategic Guide To Implement Strategy SS
Global Historical Evolution Of Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the global historical evolution od cyber terrorism. It includes some events such as start of hacking era, 414s group arrested, worm spread globally, WannaCry and NotPetya ransom ware attacks.Increase audience engagement and knowledge by dispensing information using Global Historical Evolution Of Cyberterrorism Strategic Guide To Implement Strategy SS. This template helps you present information on six stages. You can also present information on Supply Chain Attacks, Cyber Threats, University Systems, Hacking Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Hacktivists Actors With Characteristics And Aspects Strategic Guide To Implement Strategy SS
Hacktivists Actors With Characteristics And Aspects Strategic Guide To Implement Strategy SSThis slide showcases the Hacktivists actors. It includes its characteristics and activities such as motivation, protest and awareness, tactics and techniques, targets and impact.Introducing Hacktivists Actors With Characteristics And Aspects Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Motivation, Protest And Awareness, Tactics And Techniques, Impact, Targets, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SS
Icons Slide For Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SSIntroducing our well researched set of slides titled Icons Slide For Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SS. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Ideological Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SS
Ideological Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the Ideological motivations and goals of cyber terrorism. It includes goals such as anti-globalization, environmental activism, extremist ideologies and anti-corporate movements.Introducing Ideological Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Environmental Activism, Extremist Ideologies, Anti Corporate Movements, using this template. Grab it now to reap its full benefits.
-
 Incident Response And Recovery Strategies For Cyber Terrorism Strategic Guide To Implement Strategy SS
Incident Response And Recovery Strategies For Cyber Terrorism Strategic Guide To Implement Strategy SSThis slide showcases the Incident Response and Recovery Strategies for cyber terrorism. It includes strategies such as Incident Identification, Containment and Mitigation, Data Restoration and Resilience.Present the topic in a bit more detail with this Incident Response And Recovery Strategies For Cyber Terrorism Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Containment And Mitigation, Incident Identification, Eradication, Forensics And Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Insiders In Cyber Activities With Characteristics And Aspects Strategic Guide To Implement Strategy SS
Insiders In Cyber Activities With Characteristics And Aspects Strategic Guide To Implement Strategy SSThis slide showcases the insiders overview. It includes malicious insiders who intentionally misuse their authorized access for personal profit and negligent insiders who inadvertently endanger a company.Introducing Insiders In Cyber Activities With Characteristics And Aspects Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Insiders, Negligent Insiders, Financial Crimes, Engages In Espionage, using this template. Grab it now to reap its full benefits.
-
 International Agreements And Treaties Of Cyberterrorism Strategic Guide To Implement Strategy SS
International Agreements And Treaties Of Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the International Agreements and Treaties of cyberterrorism. It includes agreements and treaties such as Budapest convention on cybercrime, united nations GGE reports, Tallinn manual, CCDCOE and US-EU privacy shield.Present the topic in a bit more detail with this International Agreements And Treaties Of Cyberterrorism Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Tallinn Manual, Budapest Convention, Privacy Shield, Addressing Cyber Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Introduction To Cyber Terrorism And Its Impact Strategic Guide To Implement Strategy SS
Introduction To Cyber Terrorism And Its Impact Strategic Guide To Implement Strategy SSThis slide showcases the introduction to cyber terrorism. It includes its impact such as financial losses, economic impact, data breaches, political instability and social disruption.Deliver an outstanding presentation on the topic using this Introduction To Cyber Terrorism And Its Impact Strategic Guide To Implement Strategy SS. Dispense information and present a thorough explanation of Economic Impact, Data Breaches, Social Disruption, Political Instability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Introduction To Types Of Cyber Threat Actors Strategic Guide To Implement Strategy SS
Introduction To Types Of Cyber Threat Actors Strategic Guide To Implement Strategy SSThis slide showcases the market scenario of global automobile industry. It includes elements such as top worlds vehicle producers, number of cars sold worldwide and preference for type of engine in next vehicle.Introducing Introduction To Types Of Cyber Threat Actors Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Thrill Seekers, Cybercriminal Actors, Insiders, Hacktivists Actors, using this template. Grab it now to reap its full benefits.
-
 Major Categories Of Cyberterrorism For Data Protection Strategic Guide To Implement Strategy SS
Major Categories Of Cyberterrorism For Data Protection Strategic Guide To Implement Strategy SSThis slide showcases the major categories of cyber terrorism for data protection. It includes categories such as simple and unstructured, advanced-structure and complex-coordinated.Present the topic in a bit more detail with this Major Categories Of Cyberterrorism For Data Protection Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Advanced Structure, Complex Coordinated, Categories, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Man In The Middle Mitm Attacks In Cyberterrorism Strategic Guide To Implement Strategy SS
Man In The Middle Mitm Attacks In Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the Man-in-the-Middle MITM Attacks in cyber terrorism. It includes mitigation startegies such as encryption, PKI, network security, 2FA and secure Wi-Fi.Introducing Man In The Middle Mitm Attacks In Cyberterrorism Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation Strategies, Account Security, Network Security, Encryption, using this template. Grab it now to reap its full benefits.
-
 Nation State Actors With Characteristics And Activities Strategic Guide To Implement Strategy SS
Nation State Actors With Characteristics And Activities Strategic Guide To Implement Strategy SSThis slide showcases the nation-state actors. It includes its characteristics and activities such as government backing, activities, objectives and techniques.Increase audience engagement and knowledge by dispensing information using Nation State Actors With Characteristics And Activities Strategic Guide To Implement Strategy SS. This template helps you present information on four stages. You can also present information on Government Backing, Activities, Objectives, Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Need For Vigilance And Adaptation In Cybersecurity Strategic Guide To Implement Strategy SS
Need For Vigilance And Adaptation In Cybersecurity Strategic Guide To Implement Strategy SSThis slide showcases the Need for vigilance and adaptation in cyber security. It includes key points such as evolving threat landscape, pervasive cyber attacks, data as a target, adaptive strategies and resilience building.Present the topic in a bit more detail with this Need For Vigilance And Adaptation In Cybersecurity Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Pervasive Cyberattacks, Adaptive Strategies, Resilience Building, Evolving Threat Landscape. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Objectives Of Cyber Terrorist To Increase Activities Strategic Guide To Implement Strategy SS
Objectives Of Cyber Terrorist To Increase Activities Strategic Guide To Implement Strategy SSThis slide showcases the main objectives of cyber terrorist to enhance activities. It includes objectives such as political goals, making money, causing fear, revenge and payback and stealing secrets.Deliver an outstanding presentation on the topic using this Objectives Of Cyber Terrorist To Increase Activities Strategic Guide To Implement Strategy SS. Dispense information and present a thorough explanation of Political Goals, Making Money, Revenge And Payback, Stealing Secrets using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Offensive Cyber Operations And Deterrence Strategic Guide To Implement Strategy SS
Offensive Cyber Operations And Deterrence Strategic Guide To Implement Strategy SSThis slide showcases the Offensive Cyber Operations and Deterrence. It includes elements such as definition, objective and examples.Present the topic in a bit more detail with this Offensive Cyber Operations And Deterrence Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Define, Objective, Examples, Deterrence Cyber Operations, Offensive Cyber Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ongoing Threat Of Cyberterrorism In Digital Age Strategic Guide To Implement Strategy SS
Ongoing Threat Of Cyberterrorism In Digital Age Strategic Guide To Implement Strategy SSThis slide showcases the Ongoing Threat of Cyber terrorism in digital age. It includes key aspects such as constant evolution of tactics, wide-ranging targets, legislation and regulation and future perspectives.Deliver an outstanding presentation on the topic using this Ongoing Threat Of Cyberterrorism In Digital Age Strategic Guide To Implement Strategy SS. Dispense information and present a thorough explanation of Wide Ranging Targets, Legislation And Regulation, Future Perspectives using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the Phishing attack with mitigation strategies and its example. It also includes mitigation strategies such as user education, email filtering, MFA and incident reaction strategies.Introducing Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation Strategies, Example, Phishing Attack, Ideological Purposes, using this template. Grab it now to reap its full benefits.
-
 Political Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SS
Political Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the political motivation and goals of cyber terrorism. It includes goals such as nationalism and separatism, conflict and warfare, influence elections and revenge and retaliation.Increase audience engagement and knowledge by dispensing information using Political Motivations And Goals Of Cyberterrorism Strategic Guide To Implement Strategy SS. This template helps you present information on four stages. You can also present information on Conflict And Warfare, Nationalism And Separatism, Influence Elections using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Psychological Factors Of Cyberterrorism Identify Potential Risks Strategic Guide To Implement Strategy SS
Psychological Factors Of Cyberterrorism Identify Potential Risks Strategic Guide To Implement Strategy SSThis slide showcases the Psychological Factors of cyber terrorism identify potential risks. It includes goals such as revenge and grudges, mental helath isuues, desire for power and frustration and alienation.Present the topic in a bit more detail with this Psychological Factors Of Cyberterrorism Identify Potential Risks Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Mental Health Issues, Frustration And Alienation, Revenge And Grudges. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ransomware Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
Ransomware Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the Ransomware attack with mitigation strategies and example. It also includes mitigation strategies such as regular backups, email security and antivirus and anti-malware.Increase audience engagement and knowledge by dispensing information using Ransomware Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS. This template helps you present information on three stages. You can also present information on Description, Mitigation Strategies, Example, Encrypts Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Role Of Interpol And Europol In Cyberterrorism Strategic Guide To Implement Strategy SS
Role Of Interpol And Europol In Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the Role of Interpol and Europol in cyber terrorism. It also includes role such as global network, digital forensics, coordination and EC3, investigation support, operational coordination and public awareness.Introducing Role Of Interpol And Europol In Cyberterrorism Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Global Network, Capacity Building, Digital Forensics, Coordination, using this template. Grab it now to reap its full benefits.
-
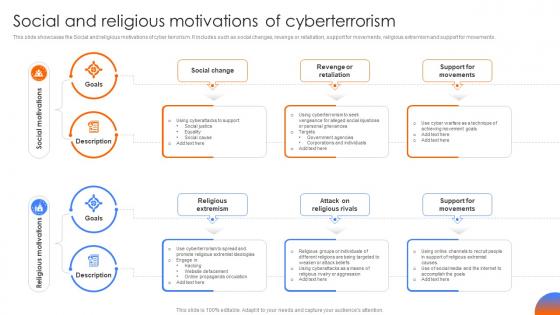 Social And Religious Motivations Of Cyberterrorism Strategic Guide To Implement Strategy SS
Social And Religious Motivations Of Cyberterrorism Strategic Guide To Implement Strategy SSThis slide showcases the Social and religious motivations of cyber terrorism. It includes such as social changes, revenge or retaliation, support for movements, religious extremism and support for movements.Present the topic in a bit more detail with this Social And Religious Motivations Of Cyberterrorism Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Description, Goals, Social Change, Social Motivations, Religious Motivations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Spear Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
Spear Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the Spear phishing attack with mitigation strategies and its example. It also includes mitigation strategies such as email filtering, Multi-factor authentication MFA and network segmentation.Increase audience engagement and knowledge by dispensing information using Spear Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS. This template helps you present information on three stages. You can also present information on Description, Mitigation Strategies, Example, Presidential Election using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SQL Injection Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
SQL Injection Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the SQL injection attack with mitigation strategies and example. It also includes mitigation strategies such as parameterized SQL statements, install a WAF and restrict the database users privileges.Introducing SQL Injection Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Description, Mitigation Strategies, Example, Seize System Control, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SS
Table Of Contents For Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SS. This template helps you present information on eight stages. You can also present information on Motivations And Goals, Cyberterrorist Actors, Conclusion, Future Trends using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SS
Table Of Contents Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SSIntroducing Table Of Contents Strategic Guide To Implement Strategies To Prevent Cyberterrorism Strategy SS to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Intelligence Agencies, Cyber Security Initiatives, International Agreements, using this template. Grab it now to reap its full benefits.
-
 Techniques To Prevent Employee Personal Accounts Strategic Guide To Implement Strategy SS
Techniques To Prevent Employee Personal Accounts Strategic Guide To Implement Strategy SSThis slide showcases the Techniques to prevent employee personal accounts. It includes strategies such as education and training, device security, two-factor authentication 2FA and secure Wi-Fi and networks.Increase audience engagement and knowledge by dispensing information using Techniques To Prevent Employee Personal Accounts Strategic Guide To Implement Strategy SS. This template helps you present information on four stages. You can also present information on Device Security, Education And Training, Two Factor Authentication, Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Thrill Seekers In Cyber Activities With Characteristics And Aspects Strategic Guide To Implement Strategy SS
Thrill Seekers In Cyber Activities With Characteristics And Aspects Strategic Guide To Implement Strategy SSThis slide showcases an overview of thrill seekers. It includes its characteristics and activities such as motivation, intent, skill and knowledge, targets and impact.Introducing Thrill Seekers In Cyber Activities With Characteristics And Aspects Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Motivation, Intent, Skill And Knowledge, Targets, Impact, using this template. Grab it now to reap its full benefits.
-
 Train Employees On Cyber Attack Prevention Strategic Guide To Implement Strategy SS
Train Employees On Cyber Attack Prevention Strategic Guide To Implement Strategy SSThis slide showcases the Train employees on cyber attack prevention. It includes techniques such as email impersonation, vigilance in clicking links, verification of email addresses and use of common sense.Present the topic in a bit more detail with this Train Employees On Cyber Attack Prevention Strategic Guide To Implement Strategy SS. Use it as a tool for discussion and navigation on Threat Scenario, Description, Employee Awareness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Trojan Horses Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
Trojan Horses Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the Trojan horses attack with mitigation strategies and example. It includes mitigation strategies such as use updated version of antivirus and regular updates of operating systems.Introducing Trojan Horses Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Description, Mitigation Strategies, Example, using this template. Grab it now to reap its full benefits.
-
 United Nations And Cyber Security Initiatives Strategic Guide To Implement Strategy SS
United Nations And Cyber Security Initiatives Strategic Guide To Implement Strategy SSThis slide showcases the United nations and cyber security initiatives. It includes initiatives such as UN general assembly resolutions, UNODA, UNIDIR, CTC and UNODC.Increase audience engagement and knowledge by dispensing information using United Nations And Cyber Security Initiatives Strategic Guide To Implement Strategy SS. This template helps you present information on five stages. You can also present information on General Assembly Resolutions, Disarmament Affairs, Disarmament Research using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 User Based Security Training Model Strategic Guide To Implement Strategy SS
User Based Security Training Model Strategic Guide To Implement Strategy SSIntroducing User Based Security Training Model Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Compromised System, Compromised Network, Critical Assets, Exfiltrate Sensitive Data, using this template. Grab it now to reap its full benefits.
-
 Whale Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
Whale Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases Whale phishing attack with mitigation strategies and its example. It includes mitigation strategies such as email filtering, Multi-factor authentication MFA and updates and patching.Increase audience engagement and knowledge by dispensing information using Whale Phishing Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS. This template helps you present information on three stages. You can also present information on Mitigation Strategies, Description, Example, Email Filtering using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SS
Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SSThis slide showcases the Wi-Fi security to protect network and connected devices. It includes strategies such as strong passwords, encryption, firewall and intrusion detection systems IDS and two-factor authentication 2FA.Introducing Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Two Factor Authentication, Intrusion Detection Systems, Encryption, Strong Passwords, using this template. Grab it now to reap its full benefits.
-
 XSS Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS
XSS Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SSThis slide showcases the XSS attack with mitigation strategies and example. It includes mitigation strategies such as content security policy and web application firewalls.Increase audience engagement and knowledge by dispensing information using XSS Attack With Mitigation Strategies And Example Strategic Guide To Implement Strategy SS. This template helps you present information on three stages. You can also present information on Description, Mitigation Strategies, Example, Content Security Policy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies For Implementing Holacracy In Powerpoint And Google Slides CPP
Strategies For Implementing Holacracy In Powerpoint And Google Slides CPPPresenting Strategies For Implementing Holacracy In Powerpoint And Google Slides CPP slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Strategies For Implementing Holacracy. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Agenda Implementing Strategies For Mitigating Network Vulnerabilities Cybersecurity SS
Agenda Implementing Strategies For Mitigating Network Vulnerabilities Cybersecurity SSIntroducing Agenda Implementing Strategies For Mitigating Network Vulnerabilities Cybersecurity SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network Security Loopholes, Security Vulnerabilities, Vulnerabilities Mitigation Strategies, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Deploying Patch Management Implementing Strategies For Mitigating Cybersecurity SS
Best Practices For Deploying Patch Management Implementing Strategies For Mitigating Cybersecurity SSThis slide provides best practices for integrating patch management. It includes automating patch management, setting clear expectations, and scheduling auto-deployments.Increase audience engagement and knowledge by dispensing information using Best Practices For Deploying Patch Management Implementing Strategies For Mitigating Cybersecurity SS. This template helps you present information on three stages. You can also present information on Set Clear Expectations, Automate Patch Management, Schedule Auto Deployments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Comparative Analysis Of End To End Encryption Tools Implementing Strategies For Mitigating Cybersecurity SS
Comparative Analysis Of End To End Encryption Tools Implementing Strategies For Mitigating Cybersecurity SSThis slide compares the best end-to-end encryption software solutions based on different parameters such as password management, on-the-fly decryption, and enterprise-grade decryption.Deliver an outstanding presentation on the topic using this Comparative Analysis Of End To End Encryption Tools Implementing Strategies For Mitigating Cybersecurity SS. Dispense information and present a thorough explanation of Offers Support, Password Management, Enterprise Grade Decryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cost Benefit Analysis For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SS
Cost Benefit Analysis For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SSThis slide shows the cost-benefit analysis of implementing network vulnerability management strategies, including the costs incurred in end-to-end encryption and phishing awareness training, etc.Deliver an outstanding presentation on the topic using this Cost Benefit Analysis For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SS. Dispense information and present a thorough explanation of Costs, Benefits, Description, Initial Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 First Line Of Defense Device Attestation Implementing Strategies For Mitigating Cybersecurity SS
First Line Of Defense Device Attestation Implementing Strategies For Mitigating Cybersecurity SSThis slide represents details related to first line of defense offered by implemented end to end encryption solution. It includes details related to process for device attestation.Introducing First Line Of Defense Device Attestation Implementing Strategies For Mitigating Cybersecurity SS to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Device Management, Certificate Authority, Automatic Certificate Management Environment, using this template. Grab it now to reap its full benefits.
-
 Icons Slide Implementing Strategies For Mitigating Network Vulnerabilities Cybersecurity SS
Icons Slide Implementing Strategies For Mitigating Network Vulnerabilities Cybersecurity SSPresenting our well crafted Icons Slide Implementing Strategies For Mitigating Network Vulnerabilities Cybersecurity SS set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Implementing Strategies For Mitigating Network Vulnerabilities Table Of Contents Cybersecurity SS
Implementing Strategies For Mitigating Network Vulnerabilities Table Of Contents Cybersecurity SSIntroducing Implementing Strategies For Mitigating Network Vulnerabilities Table Of Contents Cybersecurity SS to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Objectives, Best Practices, Training Plan For Identification, using this template. Grab it now to reap its full benefits.
-
 Investment Plan For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SS
Investment Plan For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SSThis slide details the costs associated with deploying network vulnerability management solutions for an enterprise. It includes expenses for implementing E2E software, IT talent acquisition costs etc.Deliver an outstanding presentation on the topic using this Investment Plan For Enhancing Network Security Implementing Strategies For Mitigating Cybersecurity SS. Dispense information and present a thorough explanation of Parameters, Forecasted Budget, Actual Costs, Variance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Factors For Selecting Robust Encryption Solution Implementing Strategies For Mitigating Cybersecurity SS
Key Factors For Selecting Robust Encryption Solution Implementing Strategies For Mitigating Cybersecurity SSThis slide presents essential considerations for choosing an E2EE solution, including asymmetric encryption, key verification, complex cryptography, and ephemeral messaging.Introducing Key Factors For Selecting Robust Encryption Solution Implementing Strategies For Mitigating Cybersecurity SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Asymmetric Encryption, Key Verification, Complex Cryptography, Ephemeral Messaging, using this template. Grab it now to reap its full benefits.
-
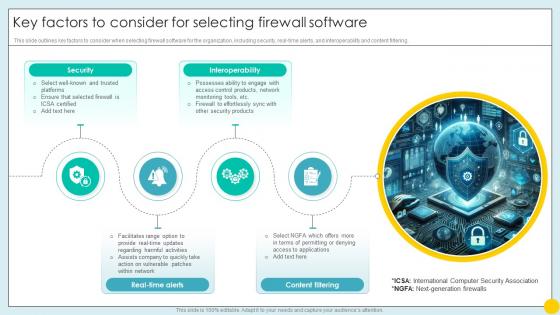 Key Factors To Consider For Selecting Firewall Software Implementing Strategies For Mitigating Cybersecurity SS
Key Factors To Consider For Selecting Firewall Software Implementing Strategies For Mitigating Cybersecurity SSThis slide outlines key factors to consider when selecting firewall software for the organization, including security, real-time alerts, and interoperability and content filtering.Increase audience engagement and knowledge by dispensing information using Key Factors To Consider For Selecting Firewall Software Implementing Strategies For Mitigating Cybersecurity SS. This template helps you present information on four stages. You can also present information on Security, Interoperability, Real Time Alerts, Content Filtering using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
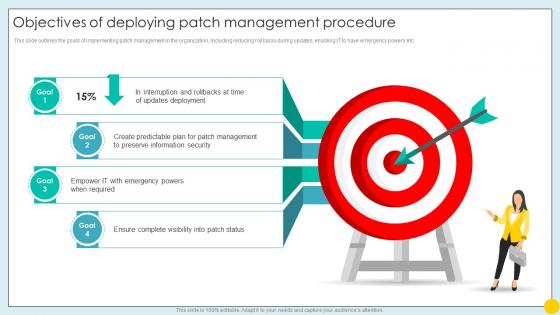 Objectives Of Deploying Patch Management Implementing Strategies For Mitigating Cybersecurity SS
Objectives Of Deploying Patch Management Implementing Strategies For Mitigating Cybersecurity SSThis slide outlines the goals of implementing patch management in the organization, including reducing rollbacks during updates, enabling IT to have emergency powers etc.Introducing Objectives Of Deploying Patch Management Implementing Strategies For Mitigating Cybersecurity SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Updates Deployment, Preserve Information Security, Ensure Complete Visibility, using this template. Grab it now to reap its full benefits.
-
 Password Authentication To Mitigate Threats Posed By Implementing Strategies For Mitigating Cybersecurity SS
Password Authentication To Mitigate Threats Posed By Implementing Strategies For Mitigating Cybersecurity SSThis slide outlines strategies to implement password authentication and mitigate threats from large-scale breaches. It includes strategies such as password hashing and salting.Introducing Password Authentication To Mitigate Threats Posed By Implementing Strategies For Mitigating Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Problem, Consequence, Reasons, Password Authentication, using this template. Grab it now to reap its full benefits.
-
 Password Authentication To Mitigate Threats Posed Implementing Strategies For Mitigating Cybersecurity SS
Password Authentication To Mitigate Threats Posed Implementing Strategies For Mitigating Cybersecurity SSThis slide outlines strategies for IT teams to implement secure password authentication, including deploying multi-factor authentication systems, scanning all newly created passwords etc.Present the topic in a bit more detail with this Password Authentication To Mitigate Threats Posed Implementing Strategies For Mitigating Cybersecurity SS. Use it as a tool for discussion and navigation on Add Additional Layers, Compromised Credentials, Lower Case Letters, Symbols. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
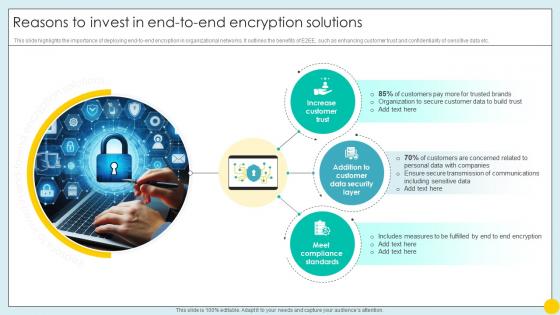 Reasons To Invest In End To End Encryption Solutions Implementing Strategies For Mitigating Cybersecurity SS
Reasons To Invest In End To End Encryption Solutions Implementing Strategies For Mitigating Cybersecurity SSThis slide highlights the importance of deploying end-to-end encryption in organizational networks. It outlines the benefits of E2EE, such as enhancing customer trust and confidentiality of sensitive data etc.Introducing Reasons To Invest In End To End Encryption Solutions Implementing Strategies For Mitigating Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Increase Customer Trust, Meet Compliance Standards, Customer Data Security Layer, using this template. Grab it now to reap its full benefits.
-
 Second Line Of Defense Certificate Authentication Implementing Strategies For Mitigating Cybersecurity SS
Second Line Of Defense Certificate Authentication Implementing Strategies For Mitigating Cybersecurity SSThis slide represents details related to second line of defense offered by implemented end to end encryption solution. It includes details related to process for certificate authentication.Increase audience engagement and knowledge by dispensing information using Second Line Of Defense Certificate Authentication Implementing Strategies For Mitigating Cybersecurity SS. This template helps you present information on five stages. You can also present information on Certificate Authority, Client, Server using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Statistics Highlighting Importance Of Patch Implementing Strategies For Mitigating Cybersecurity SS
Statistics Highlighting Importance Of Patch Implementing Strategies For Mitigating Cybersecurity SSThis slide presents statistical data highlighting the importance of patch management in organizational operations. It includes statistics related to breach detection time, prevention of cyber attacks, etc.Introducing Statistics Highlighting Importance Of Patch Implementing Strategies For Mitigating Cybersecurity SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Organizations Possess, Documented Process, Patch Management, using this template. Grab it now to reap its full benefits.




