Powerpoint Templates and Google slides for Security Assessments
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Home security system market analysis in assessment findings
Home security system market analysis in assessment findingsPresenting this set of slides with name Home Security System Market Analysis In Assessment Findings. The topics discussed in these slides are Home Security System Market Analysis In Assessment Findings. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Technology assessment scorecard with device security ppt slides deck
Technology assessment scorecard with device security ppt slides deckThis graph or chart is linked to excel, and changes automatically based on data. Just left click on it and select Edit Data. Deliver an outstanding presentation on the topic using this Technology Assessment Scorecard With Device Security Ppt Slides Deck. Dispense information and present a thorough explanation of Compromised, Not Encrypted, Mention Security Feature, Last Seen Overview, Ownership using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Technology assessment scorecard with security incidents ppt slides graphics
Technology assessment scorecard with security incidents ppt slides graphicsThis graph or chart is linked to excel, and changes automatically based on data. Just left click on it and select Edit Data. Present the topic in a bit more detail with this Technology Assessment Scorecard With Security Incidents Ppt Slides Graphics. Use it as a tool for discussion and navigation on Criminal Activity, Investigation, Denial Service, Data Breach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Assessing Cost Of Information Breach In Different Countries Information Security Risk Management
Assessing Cost Of Information Breach In Different Countries Information Security Risk ManagementDeliver an outstanding presentation on the topic using this Assessing Cost Of Information Breach In Different Countries Information Security Risk Management. Dispense information and present a thorough explanation of Assessing, Information Breach, Different Countries using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Assessment And Management Dashboard Ppt Portrait
Cyber Security Risk Assessment And Management Dashboard Ppt PortraitThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Management Dashboard Ppt Portrait. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment
Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies DeploymentThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Present the topic in a bit more detail with this Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Accounts, Globally, Unresolved. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard
Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management DashboardThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Network Security Vulnerabilities Assessment Approach
Network Security Vulnerabilities Assessment ApproachThis slide illustrates network security vulnerabilities assessment results that help the organization to secure network security loop holes to mitigate vulnerabilities. It key components are unpatched security, patched security and total number of vulnerabilities. Introducing our Network Security Vulnerabilities Assessment Approach set of slides. The topics discussed in these slides are Sion And Configuration. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
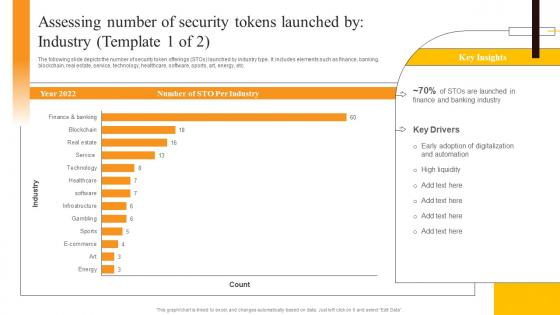 Assessing Number Of Security Tokens Launched By Industry Security Token Offerings BCT SS
Assessing Number Of Security Tokens Launched By Industry Security Token Offerings BCT SSThe following slide depicts the number of security token offerings STOs launched by industry type. It includes elements such as finance, banking, blockchain, real estate, service, technology, healthcare, software, sports, art, energy, etc. Present the topic in a bit more detail with this Assessing Number Of Security Tokens Launched By Industry Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Assessing Number, Security Tokens, Industry. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
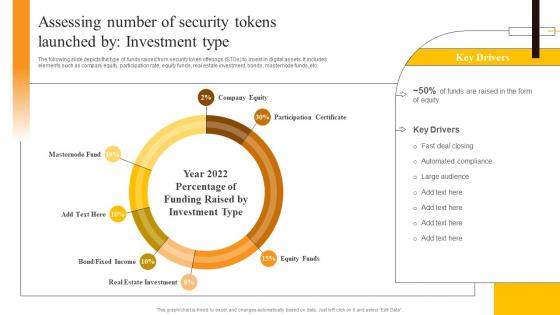 Assessing Number Of Security Tokens Launched By Investment Security Token Offerings BCT SS
Assessing Number Of Security Tokens Launched By Investment Security Token Offerings BCT SSThe following slide depicts the type of funds raised from security token offerings STOs to invest in digital assets. It includes elements such as company equity, participation rate, equity funds, real estate investment, bonds, masternode funds, etc. Deliver an outstanding presentation on the topic using this Assessing Number Of Security Tokens Launched By Investment Security Token Offerings BCT SS. Dispense information and present a thorough explanation of Real Estate Investment, Participation Certificate, Company Equity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
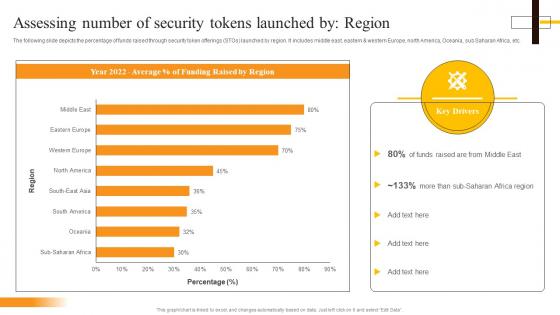 Assessing Number Of Security Tokens Launched By Region Security Token Offerings BCT SS
Assessing Number Of Security Tokens Launched By Region Security Token Offerings BCT SSThe following slide depicts the percentage of funds raised through security token offerings STOs launched by region. It includes middle east, eastern and western Europe, north America, Oceania, sub Saharan Africa, etc. Present the topic in a bit more detail with this Assessing Number Of Security Tokens Launched By Region Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Assessing Number, Security Tokens, Region. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Assessing Number Of Security Beginners Guide To Successfully Launch Security Token BCT SS V
Assessing Number Of Security Beginners Guide To Successfully Launch Security Token BCT SS VThe following slide depicts the number of security token offerings STOs launched by industry type. It includes elements such as finance, banking, blockchain, real estate, service, technology, healthcare, software, sports, art, energy, etc. Present the topic in a bit more detail with this Assessing Number Of Security Beginners Guide To Successfully Launch Security Token BCT SS V. Use it as a tool for discussion and navigation on Sto Per Industry, Banking Industry, Key Insights. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
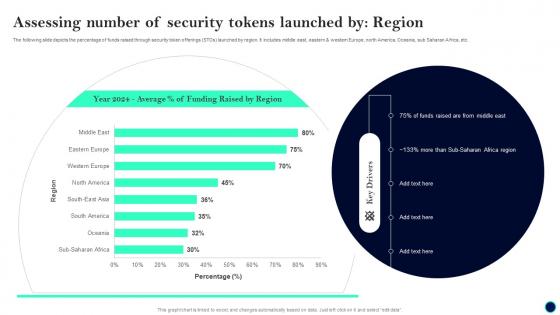 Assessing Number Of Security Tokens Beginners Guide To Successfully Launch Security Token BCT SS V
Assessing Number Of Security Tokens Beginners Guide To Successfully Launch Security Token BCT SS VThe following slide depicts the percentage of funds raised through security token offerings STOs launched by region. It includes middle east, eastern and western Europe, north America, Oceania, sub Saharan Africa, etc. Deliver an outstanding presentation on the topic using this Assessing Number Of Security Tokens Beginners Guide To Successfully Launch Security Token BCT SS V. Dispense information and present a thorough explanation of Assessing Number, Security Tokens Launched, Region using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
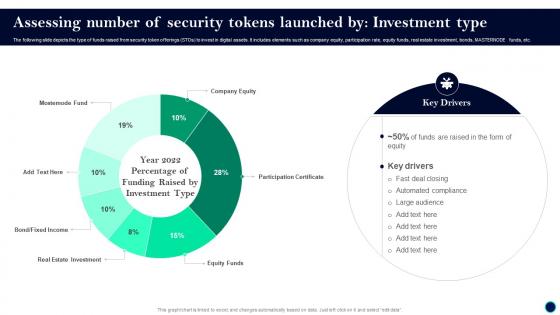 Beginners Guide To Successfully Launch Security Token Assessing Number Of Security BCT SS V
Beginners Guide To Successfully Launch Security Token Assessing Number Of Security BCT SS VThe following slide depicts the type of funds raised from security token offerings STOs to invest in digital assets. It includes elements such as company equity, participation rate, equity funds, real estate investment, bonds, MASTERNODE funds, etc. Present the topic in a bit more detail with this Beginners Guide To Successfully Launch Security Token Assessing Number Of Security BCT SS V. Use it as a tool for discussion and navigation on Key Drivers, Deal Closing, Automated Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Testing Assessment And Vulnerabilities Dashboard
Security Testing Assessment And Vulnerabilities DashboardThis slide depicts the security testing assessment components such as CVSS score, severity, current risk levels for security index, business impact, technical impacts, etc. Present the topic in a bit more detail with this Security Testing Assessment And Vulnerabilities Dashboard. Use it as a tool for discussion and navigation on Security Testing Assessment, Vulnerabilities Dashboard, Business Impact, Technical Impacts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Assessment Of SaaS Security Using KPI Dashboard
Assessment Of SaaS Security Using KPI DashboardThis slide showcases assessment of software as security to meet safety standards. This includes incidents, tasks, junctions, risk, risky incident analysis, quarterly incident status and several incidents. Introducing our Assessment Of SaaS Security Using KPI Dashboard set of slides. The topics discussed in these slides are Quarterly Incident Status, Risk Incidents Analysis, Several Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
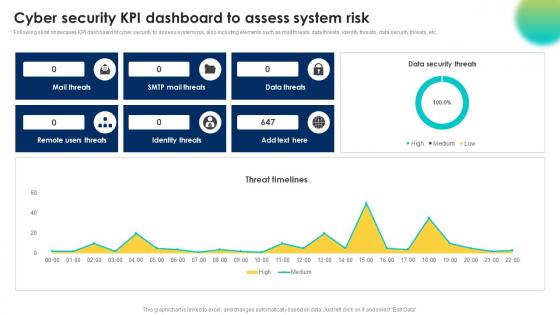 Cyber Security Kpi Dashboard To Assess System Risk
Cyber Security Kpi Dashboard To Assess System RiskFollowing slide showcases KPI dashboard of cyber security to assess system risk, also including elements such as mail threats, data threats, identity threats, data security threats, etc. Presenting our well structured Cyber Security Kpi Dashboard To Assess System Risk. The topics discussed in this slide are Identity Threats, Remote Users Threats, Data Threats. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Mobile Security Threat Assessment Dashboard
Mobile Security Threat Assessment DashboardThis slide illustrates KPI or Dashboard of mobile security threat assessment and includes security incidents log, security compromised users or devices, and highly targeted networks. Introducing our Mobile Security Threat Assessment Dashboard set of slides. The topics discussed in these slides are Security Compromised Users Devices, Highly Targeted Networks, Security Incidents Log. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Securing Food Safety In Online Statistics To Assess Need Of Outsourcing Food Delivery App
Securing Food Safety In Online Statistics To Assess Need Of Outsourcing Food Delivery AppThis slide covers statistics to assess need of integrating third party platform for delivering food. It involves features such as free and fast delivery or discounts. Present the topic in a bit more detail with this Securing Food Safety In Online Statistics To Assess Need Of Outsourcing Food Delivery App. Use it as a tool for discussion and navigation on Statistics To Assess, Need Outsourcing Food Delivery App. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Assessing Number Of Security Tokens Launched By Ultimate Guide Smart BCT SS V
Assessing Number Of Security Tokens Launched By Ultimate Guide Smart BCT SS VThe following slide depicts the type of funds raised from security token offerings STOs to invest in digital assets. It includes elements such as company equity, participation rate, equity funds, real estate investment, bonds, masternode funds, etc. Present the topic in a bit more detail with this Assessing Number Of Security Tokens Launched By Ultimate Guide Smart BCT SS V. Use it as a tool for discussion and navigation on Fast Deal Closing, Automated Compliance, Large Audience. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Region BCT SS V
Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Region BCT SS VThe following slide depicts the percentage of funds raised through security token offerings STOs launched by region. It includes middle east, eastern and western Europe, north America, Oceania, sub Saharan Africa, etc. Present the topic in a bit more detail with this Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Region BCT SS V. Use it as a tool for discussion and navigation on Funds Raised, Sub Saharan, Africa Region. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Operation Center Risk Assessment Dashboard
Security Operation Center Risk Assessment DashboardThe following slide illustrates a risk assessment dashboard helps to understand the risk rating breakdown, action plan, top vulnerabilities, etc. of a business. Introducing our Security Operation Center Risk Assessment Dashboard set of slides. The topics discussed in these slides are Risk Assessment Progress, Solved, Action Plan, Risk Rating Breakdown. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
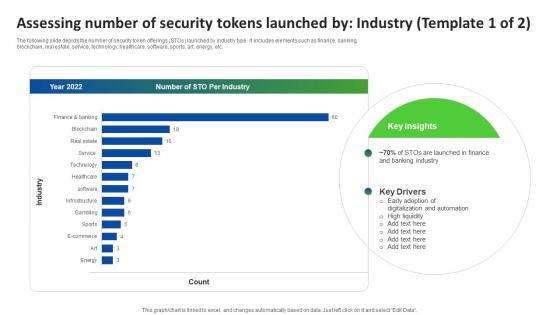 Q142 Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Industry BCT SS V
Q142 Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Industry BCT SS VThe following slide depicts the number of security token offerings STOs launched by industry type. It includes elements such as finance, banking, blockchain, real estate, service, technology, healthcare, software, sports, art, energy, etc. Deliver an outstanding presentation on the topic using this Q142 Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Industry BCT SS V. Dispense information and present a thorough explanation of Early Adoption, Digitalization And Automation, High Liquidity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Q143 Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Region BCT SS V
Q143 Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Region BCT SS VThe following slide depicts the percentage of funds raised through security token offerings STOs launched by region. It includes middle east, eastern and western Europe, north America, Oceania, sub Saharan Africa, etc. Present the topic in a bit more detail with this Q143 Ultimate Guide Smart Assessing Number Of Security Tokens Launched By Region BCT SS V. Use it as a tool for discussion and navigation on Funds Raised, Sub Saharan, Africa Region. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overall Security Score Assessment Report IT Security Awareness Training Cybersecurity SS
Overall Security Score Assessment Report IT Security Awareness Training Cybersecurity SSThis slide represents report for analyzing overall security or risk score related to facilitated IT security awareness training program. It includes details related to security score breakdown by category etc. Deliver an outstanding presentation on the topic using this Overall Security Score Assessment Report IT Security Awareness Training Cybersecurity SS. Dispense information and present a thorough explanation of Overall Security Score, Assessment Report, Security Or Risk Score, Awareness Training Program using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Assessment Dashboard
Information Technology Security Assessment DashboardThis slide represents dashboard for information technology security assessment which includes elements such as intrusion attempts, mean resolve time, mean detect time, etc. Introducing our Information Technology Security Assessment Dashboard set of slides. The topics discussed in these slides are Intrusion Attempts, IT Security Rating, Phishing Test Success Rate. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.


