Powerpoint Templates and Google slides for Security Assessments
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Assessment matrix of cyber risks cyber security it ppt powerpoint presentation slide
Assessment matrix of cyber risks cyber security it ppt powerpoint presentation slideThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Increase audience engagement and knowledge by dispensing information using Assessment Matrix Of Cyber Risks Cyber Security IT Ppt Powerpoint Presentation Slide. This template helps you present information on one stages. You can also present information on Multifamily, Industrial, Health Care, Data Center, Retail using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security assessment matrix of cyber risks ppt grid
Computer system security assessment matrix of cyber risks ppt gridThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Increase audience engagement and knowledge by dispensing information using Computer System Security Assessment Matrix Of Cyber Risks Ppt Grid. This template helps you present information on one stages. You can also present information on Industrial, Data Center, Multifamily, Retail, Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security System Audit And Risk Assessment
Information Security System Audit And Risk AssessmentThe following slide highlights the information security system audit and risk assessment illustrating key headings which includes security risk assessment, security auditing, security incident monitoring, security incident response Presenting our set of slides with name Information Security System Audit And Risk Assessment. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Risk Assessment, Security Auditing, Security Incident Monitoring.
-
 F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance Assessment
F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance AssessmentThis slide provides information regarding the strategies to enhance retail store security such as integrate access control technology, deploy video surveillance, utilizes electronic article surveillance, install monitored alarms. Increase audience engagement and knowledge by dispensing information using F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance Assessment. This template helps you present information on four stages. You can also present information on Technology, Surveillance, Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 F397 Mitigation Strategies To Avoid Information Risk Assessment And Management Plan For Information Security
F397 Mitigation Strategies To Avoid Information Risk Assessment And Management Plan For Information SecurityThis slide showcases startegies that can help organization to avoid information breach. Key strategies include impelment antivirus software, monitor network traffic, incident reponse plan, patch management schedule and establish network access controls Increase audience engagement and knowledge by dispensing information using F397 Mitigation Strategies To Avoid Information Risk Assessment And Management Plan For Information Security. This template helps you present information on five stages. You can also present information on Incident Response Plan, Monitor Network Traffic, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Impact Of Information Security Loss Risk Assessment And Management Plan For Information Security
Impact Of Information Security Loss Risk Assessment And Management Plan For Information SecurityIntroducing Impact Of Information Security Loss Risk Assessment And Management Plan For Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Loss, Business Continuity, Loss Of Productivity, using this template. Grab it now to reap its full benefits.
-
 Risk Assessment And Management Plan For Information Security Table Of Contents
Risk Assessment And Management Plan For Information Security Table Of ContentsIntroducing Risk Assessment And Management Plan For Information Security Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Departments, Organization, Information, using this template. Grab it now to reap its full benefits.
-
 Roadmap Of Cyber Security Asset Assessment And Security Policy Development
Roadmap Of Cyber Security Asset Assessment And Security Policy DevelopmentThe following slide highlights the roadmap of cyber security asset assessment and security policy development for organisation to draft system security policy which describes assessment, build, select, deployment, awareness and audit. Presenting our set of slides with name Roadmap Of Cyber Security Asset Assessment And Security Policy Development. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Audit, Awareness, Assessment, Build, Deployment.
-
 Comparative Assessment Of Cyber Security Incident Response Tools
Comparative Assessment Of Cyber Security Incident Response ToolsThis slide covers comparative assessment of cyber security incident response tools. It involves features such as advanced threat hunting ability, net flow analysis, user behavior analytics and superior forensic analysis. Introducing our premium set of slides with name Comparative Assessment Of Cyber Security Incident Response Tools. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Comparative Assessment, Cyber Security, Incident Response Tools. So download instantly and tailor it with your information.
-
 Best Practices For Assessing Cyber Security Risk Scenario
Best Practices For Assessing Cyber Security Risk ScenarioThis slide depicts the best practices for assessing cybersecurity risk scenario which includes defining threat scenario, assessing inherent risk, evaluating impact of controls, assessing residual risks, actionable steps to improve, feedback loop, etc. Introducing our premium set of slides with Best Practices For Assessing Cyber Security Risk Scenario. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Feedback Loop, Define Threat Scenario, Assess Inherent Risk. So download instantly and tailor it with your information.
-
 IT Security Assessment Method Framework
IT Security Assessment Method FrameworkThe following slide represents the security assessment of technological assets to assist IT team in improving the data structure. It includes key elements such as risk identification, security threat, vulnerabilities, impact analysis, risk level, controllable actions etc. Presenting our set of slides with IT Security Assessment Method Framework. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Identification, Security Threat, Impact Analysis.
-
 Process For Information Security Risk Assessment Formulating Cybersecurity Plan
Process For Information Security Risk Assessment Formulating Cybersecurity PlanThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identifying Internal, Information Security Threats, Information Assets, using this template. Grab it now to reap its full benefits.
-
 Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training
Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness TrainingThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Describes Spam, Cyberbullying, Protect The Confidential Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 It Security Risk Assessment Framework
It Security Risk Assessment FrameworkThe following slide highlights the structure to identify best practices to fix risk tolerances. It constitutes of activities such as identify, protect, detect, respond and recover. Presenting our set of slides with It Security Risk Assessment Framework. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Protect, Detect .
-
 It Security Risk Assessment Grid
It Security Risk Assessment GridThe following slide depicts the analysis of IT security to prevent loss of confidentiality and integrity. The matrix constitutes of elements such as risk, likelihood, its impact and overall threat level. Introducing our premium set of slides with It Security Risk Assessment Grid. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Likelihood, Risk, Impact. So download instantly and tailor it with your information.
-
 Data Security Governance Tool Assessment Matrix
Data Security Governance Tool Assessment MatrixThis slide highlights a tools comparison matrix for data security governance and management. It includes key components such as threat intelligence, advanced data governance, source score, data helpdesk, price and customer satisfaction. Introducing our premium set of slides with Data Security Governance Tool Assessment Matrix. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Intelligence, Advanced Data Governance. So download instantly and tailor it with your information.
-
 Cloud Security Maturity Model Assessment To Improve Business Operations
Cloud Security Maturity Model Assessment To Improve Business OperationsThis slide represents cloud security maturity assessment model which helps improve cloud optimization and flexibility. It provides information regarding automation, manual scripts, managed stage and optimization. Introducing our premium set of slides with Cloud Security Maturity Model Assessment To Improve Business Operations. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Automation Optimized, Minimal Automation, Minimal Automation. So download instantly and tailor it with your information.
-
 Cloud Security Audit Assessment Process
Cloud Security Audit Assessment ProcessThe slide exhibits various steps of cloud security audit for getting an excellent performance. Various steps included are understand the model, analyse, validate controls and calculate score. Introducing our premium set of slides with Cloud Security Audit Assessment Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Calculate Score, Validate Controls, Understand The Model . So download instantly and tailor it with your information.
-
 Table Of Contents For Cybersecurity Risk Assessment Program To Strengthen Organization Security
Table Of Contents For Cybersecurity Risk Assessment Program To Strengthen Organization SecurityIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Cybersecurity Risk Assessment Program To Strengthen Organization Security. This template helps you present information on nine stages. You can also present information on Cyber Attacks Risk Assessment, Cyber Attacks Risk Mitigation, Dashboards, Cyber Attack Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 K56 Cybersecurity Risk Assessment Program To Strengthen Organization Security For Table Of Contents
K56 Cybersecurity Risk Assessment Program To Strengthen Organization Security For Table Of ContentsIntroducing K56 Cybersecurity Risk Assessment Program To Strengthen Organization Security For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity, Risk Assessment Program, Strengthen Organization Security, using this template. Grab it now to reap its full benefits.
-
 Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V
Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting Blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Threats, Attack Vectors, Causes, using this template. Grab it now to reap its full benefits.
-
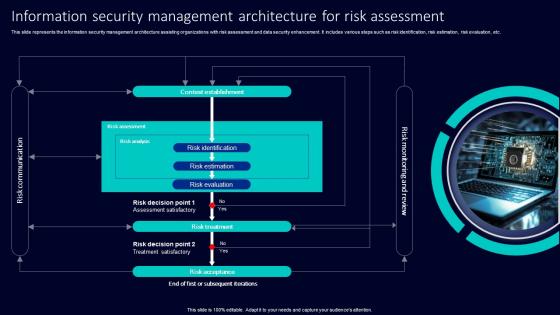 Information Security Management Architecture For Risk Assessment
Information Security Management Architecture For Risk AssessmentThis slide represents the information security management architecture assisting organizations with risk assessment and data security enhancement. It includes various steps such as risk identification, risk estimation, risk evaluation, etc. Presenting our set of slides with Information Security Management Architecture For Risk Assessment. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Identification, Risk Estimation, Risk Evaluation.
-
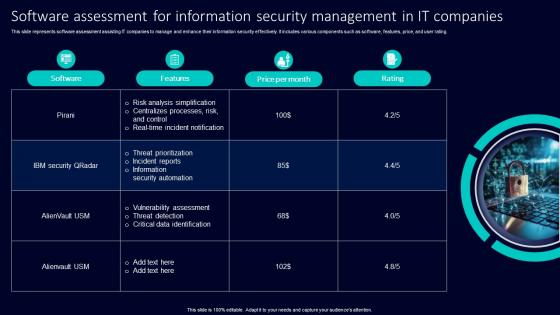 Software Assessment For Information Security Management In It Companies
Software Assessment For Information Security Management In It CompaniesThis slide represents software assessment assisting IT companies to manage and enhance their information security effectively. It includes various components such as software, features, price, and user rating. Presenting our set of slides with Software Assessment For Information Security Management In It Companies. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Analysis Simplification, Centralizes Processes, Risk Control, Real Time Incident Notification.
-
 Determine Cyber Security Risks And Threats Cyber Risk Assessment
Determine Cyber Security Risks And Threats Cyber Risk AssessmentThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Increase audience engagement and knowledge by dispensing information using Determine Cyber Security Risks And Threats Cyber Risk Assessment This template helps you present information on three stages. You can also present information on Malware, Phishing, Ransomware, Weak Credentials using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Select Tools To Reduce Cyber Security Failure Cyber Risk Assessment
Select Tools To Reduce Cyber Security Failure Cyber Risk AssessmentThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Introducing Select Tools To Reduce Cyber Security Failure Cyber Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Suspicious Activities, Select Tools, Cyber Security Failure using this template. Grab it now to reap its full benefits.
-
 Information Security Audit Icon For Vulnerability Assessment
Information Security Audit Icon For Vulnerability AssessmentPresenting our set of slides with Information Security Audit Icon For Vulnerability Assessment. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security Audit, Icon For Vulnerability Assessment
-
 Proactively Assess The Impact Of Potential Security Internet Of Things IoT Security Cybersecurity SS
Proactively Assess The Impact Of Potential Security Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of impact assessment on internet of things IoT device security events, referable for businesses in developing mitigation process. It provides details about threat model, security layers, etc. Introducing Proactively Assess The Impact Of Potential Security Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Comprehensive Security, Assessment And Security Layers, Credential Provisioning, using this template. Grab it now to reap its full benefits.
-
 Mobile Application Security Risk Assessment
Mobile Application Security Risk AssessmentThis slide demonstrates mobile application security to assess risks and includes improper platform usage, insecure data storage, and insecure communication. Presenting our set of slides with name Mobile Application Security Risk Assessment. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Improper Platform Usage, Insecure Data Storage, Insecure Communication.


