Powerpoint Templates and Google slides for Security And Authenticity
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User Authentication
Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User AuthenticationThis slide represents the improved user authentication method in Cloud Access Security Broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User Authentication. Dispense information and present a thorough explanation of Authentication Solutions, Creating Adaptive Authentication, Businesses To Dynamically using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Authentication Failed In Powerpoint And Google Slides Cpb
Secure Authentication Failed In Powerpoint And Google Slides CpbPresenting Secure Authentication Failed In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secure Authentication Failed. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Authentication Information Security In Powerpoint And Google Slides Cpb
Authentication Information Security In Powerpoint And Google Slides CpbPresenting Authentication Information Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Authentication Information Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Authentication Network Security In Powerpoint And Google Slides Cpb
Authentication Network Security In Powerpoint And Google Slides CpbPresenting our Authentication Network Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Authentication Network Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Secure Your Digital Assets Overview And Working Of Two Factor Authentication
Secure Your Digital Assets Overview And Working Of Two Factor AuthenticationThis slide represents an overview and working of 2-factor authentication 2FA. The purpose of this slide is to outline a 2FA overview, how it works, and why we need 2FA. 2FA is a two-step verification for protection and security, it is user-friendly, etc. Deliver an outstanding presentation on the topic using this Secure Your Digital Assets Overview And Working Of Two Factor Authentication. Dispense information and present a thorough explanation of Phishing, Social Engineering, Password Brute Force Attacks, Prevents Attackers, Stolen Credentials using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker And User Authentication Next Generation CASB
Cloud Access Security Broker And User Authentication Next Generation CASBThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Present the topic in a bit more detail with this Cloud Access Security Broker And User Authentication Next Generation CASB Use it as a tool for discussion and navigation on Cloud Apps, Transaction Detail, User Threat Data This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Methods For Deploying Strong Device Authentication IoT Security And Privacy Safeguarding IoT SS
Methods For Deploying Strong Device Authentication IoT Security And Privacy Safeguarding IoT SSThis slide exhibits several IoT device authentication models for secure communication between machines. It includes methods such as digital certificates, hardware security module, trusted platform module and symmetric keys. Increase audience engagement and knowledge by dispensing information using Methods For Deploying Strong Device Authentication IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on four stages. You can also present information on Digital Certificates, Certificates Contains, Protect Cryptographic using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker And User Authentication CASB Cloud Security
Cloud Access Security Broker And User Authentication CASB Cloud SecurityThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Present the topic in a bit more detail with this Cloud Access Security Broker And User Authentication CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Access Security Broker, User Authentication, Multifactor Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Difference Between Authentication And Authorization In Application Security
Difference Between Authentication And Authorization In Application SecurityThis slide showcase the difference between authentication and authorization in application security on aspects such as purpose, operation, etc. Deliver an outstanding presentation on the topic using this Difference Between Authentication And Authorization In Application Security. Dispense information and present a thorough explanation of Confirms Credentials, Authentication, Authorization, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Email Authentication And Security Working Process
Email Authentication And Security Working ProcessThis slide highlights the email authentication and security working process which includes sender establishes authentication rules, and sender configuration. Presenting our set of slides with Email Authentication And Security Working Process. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Email Infrastructure, Authentication Rules, Authentication Results.
-
 Email Security Encryption And Authentication Icon
Email Security Encryption And Authentication IconIntroducing our premium set of slides with Email Security Encryption And Authentication Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Email Security, Encryption And Authentication, Icon. So download instantly and tailor it with your information.
-
 Data Encryption And Authentication In Automotive Cyber Security
Data Encryption And Authentication In Automotive Cyber SecurityThis slide highlights data privacy and encryption in automotive cybersecurity. The purpose of this slide is to aid organizations in implementing measures for securing sensitive data from possible manipulation. It includes various measures for authentication and data encryption. Presenting our set of slides with Data Encryption And Authentication In Automotive Cyber Security This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication, Data Encryption, Authenticity Of Software
-
 Voice Recognition For Enhancing Security And Authentication Next Gen Business Transformation With Voice TC SS
Voice Recognition For Enhancing Security And Authentication Next Gen Business Transformation With Voice TC SSThis slide presents various use case of voice recognition technology for security and authentication in various areas. It includes mobile applications, call centers and IVR systems,and web applications. Increase audience engagement and knowledge by dispensing information using Voice Recognition For Enhancing Security And Authentication Next Gen Business Transformation With Voice TC SS. This template helps you present information on four stages. You can also present information on Mobile Applications, Web Applications, Voice Commands using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 IAM Authentication And Authorization Workflow Process Securing Systems With Identity
IAM Authentication And Authorization Workflow Process Securing Systems With IdentityThis slide showcases the workflow of IAM authentication and authorization. The purpose of this slide is to explain the process, starting with user authentication and authorization, that often uses a single sign-on solution that incorporates multi-factor authentication and assigns access rights to resources. Increase audience engagement and knowledge by dispensing information using IAM Authentication And Authorization Workflow Process Securing Systems With Identity This template helps you present information on Two stages. You can also present information on Authentication, Authorization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mobile Data Security Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Data Security Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Mobile data security authentication colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Mobile Data Security Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Data Security Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Mobile data security authentication monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 User Authentication And Authorization Security Technology
User Authentication And Authorization Security TechnologyThis slide provides the use of multiple authentication and authorization technology which are used to protect systems and user information. Key categories are password based, multi factor, certificate based, biometrics and token based. Presenting our set of slides with name User Authentication And Authorization Security Technology. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Password Based, Multi Factor, Certificate Based, Biometrics, Token Based.
-
 Three Secure Authentication In Powerpoint And Google Slides Cpb
Three Secure Authentication In Powerpoint And Google Slides CpbPresenting our Three Secure Authentication In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Three Secure Authentication. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 WIFI Security Network Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Security Network Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a visual representation of WIFI security. It features a shield with a lock to represent the protection of your WIFI network. It is a great visual aid for presentations on WIFI security and can be used to highlight the importance of keeping your network secure.
-
 WIFI Security Network Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Security Network Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for illustrating the concept of WIFI Security. It features a simple, modern design that is sure to make your presentation stand out. It is perfect for any project related to WIFI Security, from educational materials to corporate presentations.
-
 Enrolled Secure Authentication In Powerpoint And Google Slides Cpb
Enrolled Secure Authentication In Powerpoint And Google Slides CpbPresenting our Enrolled Secure Authentication In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Enrolled Secure Authentication This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Authentication Security In Powerpoint And Google Slides Cpb
Authentication Security In Powerpoint And Google Slides CpbPresenting our Authentication Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Authentication Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Most Secure Way Authenticating In Powerpoint And Google Slides Cpb
Most Secure Way Authenticating In Powerpoint And Google Slides CpbPresenting our Most Secure Way Authenticating In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Most Secure Way Authenticating. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Most Secure Way Authentication In Powerpoint And Google Slides Cpb
Most Secure Way Authentication In Powerpoint And Google Slides CpbPresenting our Most Secure Way Authentication In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Most Secure Way Authentication. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SS
Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. Present the topic in a bit more detail with this Two Factor Authentication Process Security Mobile Banking For Convenient And Secure Online Payments Fin SS. Use it as a tool for discussion and navigation on Authentication, Process, Possession Verification . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Encryption Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Encryption Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured icon is perfect for illustrating security features in presentations. It features a padlock and shield in blue, green and yellow hues on a white background. Ideal for emphasizing the importance of safety and security.
-
 Security Encryption Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Encryption Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is perfect for presentations and documents related to security features. It features a shield with a keyhole, symbolizing protection and security. It is a simple, yet powerful design that conveys the message of safety and security.
-
 Authentication Security Risks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Authentication Security Risks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis PowerPoint icon depicts a shield with a red warning sign, representing the security risks associated with digital data. It is a great visual aid for presentations on cyber security, risk management, and data protection.
-
 Authentication Security Risks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Authentication Security Risks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon on Security Risks is a great visual aid for presentations on cyber security and data protection. It features a silhouette of a person in a protective stance, illustrating the need to be aware of potential risks.
-
 Cloud Access Security Broker And User Authentication Ppt Ideas Infographic Template
Cloud Access Security Broker And User Authentication Ppt Ideas Infographic TemplateThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker And User Authentication Ppt Ideas Infographic Template. Dispense information and present a thorough explanation of Sensitive Content, Transaction Detail, User Threat Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Mobile Security Authentication Measures Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Security Authentication Measures Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts a shield with a lock, representing security measures. Its perfect for presentations on data protection, cyber security, and other related topics. The icon is bright and vibrant, making it stand out and draw attention to your message.
-
 Mobile Security Authentication Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Security Authentication Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is the perfect visual representation of security measures, providing a simple and effective way to communicate the importance of safety and security to any audience. It is an essential tool for any presentation on security topics.
-
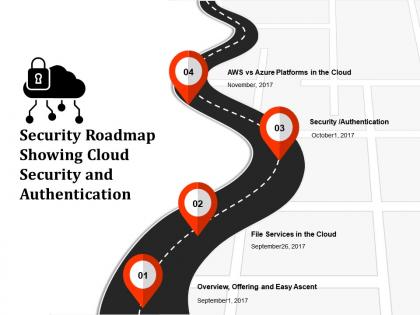 Security roadmap showing cloud security and authentication
Security roadmap showing cloud security and authenticationPresenting this set of slides with name - Security Roadmap Showing Cloud Security And Authentication. This is a four stage process. The stages in this process are Security Roadmap, Security Timeline, Safer Roadmap.
-
 Identification and authentication in network security ppt powerpoint presentation infographics layouts cpb
Identification and authentication in network security ppt powerpoint presentation infographics layouts cpbPresenting Identification And Authentication In Network Security Ppt Powerpoint Presentation Infographics Layouts Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Identification And Authentication In Network Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.



