Powerpoint Templates and Google slides for Securing Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Big data it security of information in big data
Big data it security of information in big dataThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Introducing Big Data It Security Of Information In Big Data to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Information, Companies, Professionals, using this template. Grab it now to reap its full benefits.
-
 Building organizational security strategy plan selecting data centre management solution
Building organizational security strategy plan selecting data centre management solutionThis slide will help firm in choosing the suitable data center management solution by analyzing on various parameters such as server health management, firmware update, ghost server detection, equipment scheduling, etc. Deliver an outstanding presentation on the topic using this Building Organizational Security Strategy Plan Selecting Data Centre Management Solution. Dispense information and present a thorough explanation of Equipment, Management, Solution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Planning And Implementation Of Crm Software Securing Our Data With Crm
Planning And Implementation Of Crm Software Securing Our Data With CrmThis slide highlights the CRM data security model which includes the user based, profile based, group based, record sharing and login based security. Deliver an outstanding presentation on the topic using this Planning And Implementation Of Crm Software Securing Our Data With Crm. Dispense information and present a thorough explanation of User Role Based Security, Profile Based Security, Record Sharing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Securing Our Data With Crm Planning And Implementation Of Crm Software
Securing Our Data With Crm Planning And Implementation Of Crm SoftwareThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security. Present the topic in a bit more detail with this Securing Our Data With Crm Planning And Implementation Of Crm Software. Use it as a tool for discussion and navigation on Securing Our Data With CRM. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 F41 Data Privacy It Data Privacy Vs Data Security
F41 Data Privacy It Data Privacy Vs Data SecurityThis slide compares data privacy with data security, indicating that security is concerned with safeguarding data, and privacy is about responsible data usage. Deliver an outstanding presentation on the topic using this F41 Data Privacy It Data Privacy Vs Data Security. Dispense information and present a thorough explanation of Information, Unauthorized, Dangerous using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Manage Sensitive Data Securely Ppt Powerpoint Presentation Infographics Files Cpb
Manage Sensitive Data Securely Ppt Powerpoint Presentation Infographics Files CpbPresenting Manage Sensitive Data Securely Ppt Powerpoint Presentation Infographics Files Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase nine stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Manage Sensitive Data Securely. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security Of Data And Networks In Edge Computing Distributed Information Technology
Security Of Data And Networks In Edge Computing Distributed Information TechnologyThis slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable. Deliver an outstanding presentation on the topic using this Security Of Data And Networks In Edge Computing Distributed Information Technology. Dispense information and present a thorough explanation of Security Of Data And Networks In Edge Computing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Architecture Of Cloud Security Cloud Data Protection
Architecture Of Cloud Security Cloud Data ProtectionThis slide represents the architecture of the cloud security system and how data is organized and secured under a cloud system. Deliver an outstanding presentation on the topic using this Architecture Of Cloud Security Cloud Data Protection. Dispense information and present a thorough explanation of Infrastructure Security, Monitoring, Processing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Implement Cloud Security In Business Cloud Data Protection
Checklist To Implement Cloud Security In Business Cloud Data ProtectionThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Checklist To Implement Cloud Security In Business Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Logging And Monitoring, Networking, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Cloud Data Protection Tools Used In Cloud Security
Cloud Data Protection Tools Used In Cloud SecurityThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud. Increase audience engagement and knowledge by dispensing information using Cloud Data Protection Tools Used In Cloud Security. This template helps you present information on one stage. You can also present information on Cloud Solutions, Security, Networks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Data Protection What Are The Downsides Of A Cloud Security
Cloud Data Protection What Are The Downsides Of A Cloud SecurityThis slide describes the downsides of the cloud security system, including loss of control over data, data loss, insider theft, and data breaches. Introducing Cloud Data Protection What Are The Downsides Of A Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Data Security, Organizations, Data Breaches, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Best Practices Cloud Data Protection
Cloud Security Best Practices Cloud Data ProtectionThis slide defines the best practices of cloud security, including understanding cloud utilization and risk, protection of cloud, and responding to cloud protection issues. Deliver an outstanding presentation on the topic using this Cloud Security Best Practices Cloud Data Protection. Dispense information and present a thorough explanation of Cloud Protection Issues, Cloud Service, Infrastructure As A Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Security Threats Malware Attacks Cloud Data Protection
Cloud Security Threats Malware Attacks Cloud Data ProtectionThis slide represents the malware threat of cloud security and how it can affect data stored on the cloud, further leading to company loss. Introducing Cloud Security Threats Malware Attacks Cloud Data Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Frameworks, Targets, Technology, using this template. Grab it now to reap its full benefits.
-
 Difference Between Cloud Security Solutions And Traditional Cloud Data Protection
Difference Between Cloud Security Solutions And Traditional Cloud Data ProtectionThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses. Deliver an outstanding presentation on the topic using this Difference Between Cloud Security Solutions And Traditional Cloud Data Protection. Dispense information and present a thorough explanation of Opportunity, Low Efficiency, Cloud Security, Expense using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 What Is Cloud Security Cloud Data Protection
What Is Cloud Security Cloud Data ProtectionThis slide depicts the meaning of cloud security, and parties involve in a cloud security framework, such as customers and service providers. Increase audience engagement and knowledge by dispensing information using What Is Cloud Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Organizations, Cloud Security, Ensure Business, Threats, Cloud Computing Systems using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Why Cloud Security Is Important Cloud Data Protection
Why Cloud Security Is Important Cloud Data ProtectionThis slide defines why cloud security is essential based on data centralization, cost, diminished control, and data reliability. Present the topic in a bit more detail with this Why Cloud Security Is Important Cloud Data Protection. Use it as a tool for discussion and navigation on Centralized Security, Cost Effective, Cloud Security. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Incident Response Playbook Best Work From Home Data Security Practices
Incident Response Playbook Best Work From Home Data Security PracticesPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Increase audience engagement and knowledge by dispensing information using Incident Response Playbook Best Work From Home Data Security Practices. This template helps you present information on six stages. You can also present information on System Update, Avoid Using External Device, Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Incident Response Playbook Checklist For Work From Home Data Security
Incident Response Playbook Checklist For Work From Home Data SecurityIncrease audience engagement and knowledge by dispensing information using Incident Response Playbook Checklist For Work From Home Data Security. This template helps you present information on one stages. You can also present information on Training, Policies, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Benefit Of Block Chain Technology For Securing Confidential Data Icon
Benefit Of Block Chain Technology For Securing Confidential Data IconPresenting our set of slides with Benefit Of Block Chain Technology For Securing Confidential Data Icon. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Block Chain Technology, Securing Confidential Data.
-
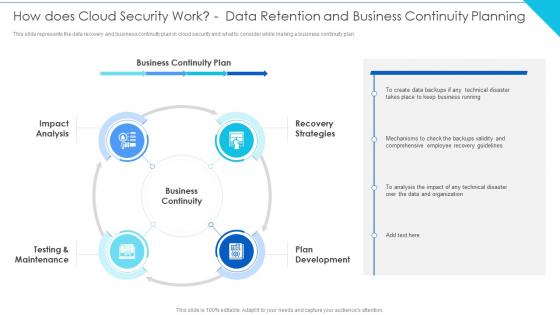 Cloud Information Security How Does Cloud Security Work Data Planning
Cloud Information Security How Does Cloud Security Work Data PlanningThis slide represents the data recovery and business continuity plan in cloud security and what to consider while making a business continuity plan.Increase audience engagement and knowledge by dispensing information using Cloud Information Security How Does Cloud Security Work Data Planning This template helps you present information on five stages. You can also present information on Implement Information, Authentication Process, Data Encryption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Checklist Data Encryption Cloud Information Security
Cloud Security Checklist Data Encryption Cloud Information SecurityThis slide represents the importance of data encryption in cloud security and what type of data should always be encrypted through private keys.Introducing Cloud Security Checklist Data Encryption Cloud Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Future Evaluation, Device Is Detected, Change Activities using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Information Security
Cloud Security Threats Loss Of Data Cloud Information SecurityThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Information Security This template helps you present information on four stages. You can also present information on Cloud Administrations, Protection Frameworks, Technology Advances using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Assessment And Management Plan For Information Security Current Information And Data Security
Risk Assessment And Management Plan For Information Security Current Information And Data SecurityThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating Present the topic in a bit more detail with this Risk Assessment And Management Plan For Information Security Current Information And Data Security. Use it as a tool for discussion and navigation on Information, Capabilities, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Multi Level Security Database In Powerpoint And Google Slides Cpb
Multi Level Security Database In Powerpoint And Google Slides CpbPresenting Multi Level Security Database In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Multi Level Security Database. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Implementation Steps Enable Data Security Crm System Implementation Guide For Businesses
Implementation Steps Enable Data Security Crm System Implementation Guide For BusinessesThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Implementation Steps Enable Data Security Crm System Implementation Guide For Businesses. Use it as a tool for discussion and navigation on Implementation, Compliance, Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 3 Step Cyber Security Plan For Data Protection
3 Step Cyber Security Plan For Data ProtectionThis slide signifies the three stage cyber security program to improve data protection. It covers information about steps like prevention, response and remediation. Presenting our set of slides with 3 Step Cyber Security Plan For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevention, Response, Remediation.
-
 Crm Implementation Process Implementation Steps Enable Data Security
Crm Implementation Process Implementation Steps Enable Data SecurityThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Crm Implementation Process Implementation Steps Enable Data Security. Use it as a tool for discussion and navigation on Implementation, Authentication, Restrictions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Approaches Of Cloud Disaster Recovery For Data Security
Approaches Of Cloud Disaster Recovery For Data SecurityThis slide shows four approaches of cloud disaster recovery that can be used by an organization to create a data secure environment. It includes backup and restore, warm study, pilot light and multi site active or active approach. Introducing our premium set of slides with Approaches Of Cloud Disaster Recovery For Data Security. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Backup And Restore, Warm Standby, Pilot Light. So download instantly and tailor it with your information.
-
 Implementation Steps Enable Data Security Crm Software Deployment Guide
Implementation Steps Enable Data Security Crm Software Deployment GuideThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Implementation Steps Enable Data Security Crm Software Deployment Guide. Use it as a tool for discussion and navigation on Implementation, Authentication, Restrictions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Steps Enable Data Security Crm Platform Implementation Plan
Implementation Steps Enable Data Security Crm Platform Implementation PlanThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Deliver an outstanding presentation on the topic using this Implementation Steps Enable Data Security Crm Platform Implementation Plan. Dispense information and present a thorough explanation of Authentication, Implementation, Security Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Customer Relationship Management System Implementation Steps Enable Data Security
Customer Relationship Management System Implementation Steps Enable Data SecurityThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Deliver an outstanding presentation on the topic using this Customer Relationship Management System Implementation Steps Enable Data Security. Dispense information and present a thorough explanation of Implementation, Authentication, Restrictions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Security Handled By Cdn Delivery Network Ppt Slides Infographics
Data Security Handled By Cdn Delivery Network Ppt Slides InfographicsThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults. Deliver an outstanding presentation on the topic using this Data Security Handled By Cdn Delivery Network Ppt Slides Infographics. Dispense information and present a thorough explanation of Resources, Location, Certificates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Work From Home Data Security Practices Security Incident Response Playbook
Best Work From Home Data Security Practices Security Incident Response PlaybookPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Introducing Best Work From Home Data Security Practices Security Incident Response Playbook to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on System Update, Communication, External Devices, using this template. Grab it now to reap its full benefits.
-
 Data Backup Evaluation Sheet Security Incident Response Playbook Ppt Slides Background Image
Data Backup Evaluation Sheet Security Incident Response Playbook Ppt Slides Background ImageMentioned slide addresses evaluation sheet which can be used for assessing data backup activities. Sections covered in the sheet are backup testing frequency, type of backup solution and responsible person details. Present the topic in a bit more detail with this Data Backup Evaluation Sheet Security Incident Response Playbook Ppt Slides Background Image. Use it as a tool for discussion and navigation on Evaluation, Responsible, Solution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Incident Response Playbook Checklist For Work From Home Data Security
Security Incident Response Playbook Checklist For Work From Home Data SecurityDeliver an outstanding presentation on the topic using this Security Incident Response Playbook Checklist For Work From Home Data Security. Dispense information and present a thorough explanation of Remote, Workstations, Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Security Handled By Cdn Cdn Edge Server Ppt Styles Graphics Design
Data Security Handled By Cdn Cdn Edge Server Ppt Styles Graphics DesignThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults. Present the topic in a bit more detail with this Data Security Handled By Cdn Cdn Edge Server Ppt Styles Graphics Design. Use it as a tool for discussion and navigation on Certificates, Server, Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Protection Multi Cloud Data Encryption Cloud Architecture And Security Review
Data Protection Multi Cloud Data Encryption Cloud Architecture And Security ReviewThis slide covers data protection and encryption framework in multi cloud with multi layer protection and data management. Increase audience engagement and knowledge by dispensing information using Data Protection Multi Cloud Data Encryption Cloud Architecture And Security Review. This template helps you present information on one stages. You can also present information on Object Store Appliance, Spectrum Protect, Multi Cloud Data Encryption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Data Analysis With Reported Incident Metrics
Cyber Security Data Analysis With Reported Incident MetricsThis slide shows the scorecard of the data security with key performance indicators. It also includes the progress status of data readiness and security audits with their value and targets that has to be achieved during the period. Presenting our well structured Cyber Security Data Analysis With Reported Incident Metrics. The topics discussed in this slide are Data Production Readdress, Data Production Officer Nominated, Explicit Consent Tracking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Applications Of Data Masking Security Technology
Applications Of Data Masking Security TechnologyThis slide illustrates the multiple applications of data masking technology which helps to protect sensitive data by providing a functional alternative. Major elements include encryption, scrambling, nulling out, substitution, shuffling etc. Introducing our premium set of slides with Applications Of Data Masking Security Technology. Elucidate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Date Aging, Encryption, Scrambling, Nulling Out, Substitution. So download instantly and tailor it with your information.
-
 Business Data Encryption Security Technology
Business Data Encryption Security TechnologyThis slide highlights the role of encryption technology which is used by business and organisation to protect the confidentiality of digital data storage and transmission. Key components are authentication, privacy, regulatory compliance and security. Presenting our set of slides with name Business Data Encryption Security Technology. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Privacy, Authentication, Regulatory Compliance, Security.
-
 Access Control In Secured Database Management System
Access Control In Secured Database Management SystemThis slide represents the block diagram representing the access control in secured database management system. It includes details related to database and security administrator, authorization system, database schemas, application programs etc. Presenting our well structured Access Control In Secured Database Management System. The topics discussed in this slide are Access Control, Secured Database, Management System. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data Security Handled By CDN Content Distribution Network Ppt Powerpoint Presentation File Example
Data Security Handled By CDN Content Distribution Network Ppt Powerpoint Presentation File ExampleThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults.Present the topic in a bit more detail with this Data Security Handled By CDN Content Distribution Network Ppt Powerpoint Presentation File Example. Use it as a tool for discussion and navigation on Defending Against, Perfect For Stopping, Dispersed Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Protection And Information Security Policy And Procedure Corporate Induction Program For New Staff
Data Protection And Information Security Policy And Procedure Corporate Induction Program For New StaffThis slide highlights the data protection and information security policy which includes policy and procedures of IT policy and it is applicable to all the employees and enforcement of the policy. Introducing Data Protection And Information Security Policy And Procedure Corporate Induction Program For New Staff to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Protection, Information, Procedure, using this template. Grab it now to reap its full benefits.
-
 Data Protection And Information Security Policy New Employee Induction Programme
Data Protection And Information Security Policy New Employee Induction ProgrammeThis slide highlights the data protection and information security policy which includes policy and procedures of IT policy and it is applicable to all the employees and enforcement of the policy.Increase audience engagement and knowledge by dispensing information using Data Protection And Information Security Policy New Employee Induction Programme. This template helps you present information on two stages. You can also present information on Information Confidentiality, Security Program, Ensure Necessary using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Securities Trading Platform Data Flow Diagram
Securities Trading Platform Data Flow DiagramThis slide displays a thorough data flow diagram that graphically illustrates the operations of a securities trading platform, as well as the sources and recipients of the information. It includes five processes such as open account, verify transaction, deposit cash, withdraw cash and place order. Presenting our well-structured Securities Trading Platform Data Flow Diagram. The topics discussed in this slide are Client, Broker, Place Order, Withdraw Cash. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Business Data Security Management Model
Business Data Security Management ModelThis slide covers business data security management model which includes Defining, executing and measuring security controls. Introducing our Business Data Security Management Model set of slides. The topics discussed in these slides are Business Data, Security, Management Model. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Business Database Application Security Management
Business Database Application Security ManagementThis slide covers business database application security management which includes secure devices, data protection, safeguard application and managing access fraud. Presenting our well structured Business Database Application Security Management. The topics discussed in this slide are Business Database, Application, Security Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Current Information And Data Security Cybersecurity Risk Analysis And Management Plan
Current Information And Data Security Cybersecurity Risk Analysis And Management PlanThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating Present the topic in a bit more detail with this Current Information And Data Security Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Capabilities, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
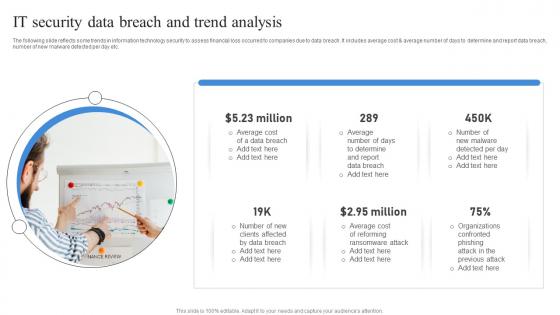 It Security Data Breach And Trend Analysis
It Security Data Breach And Trend AnalysisThe following slide reflects some trends in information technology security to assess financial loss occurred to companies due to data breach. It includes average cost and average number of days to determine and report data breach, number of new malware detected per day etc. Presenting our set of slides with It Security Data Breach And Trend Analysis. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Data, Breach, Analysis.
-
 Key Statistics Of It Security And Data Breach
Key Statistics Of It Security And Data BreachThe following slide depicts some statistical insights of IT security to prevent data breaches and financial loss. It includes facts such as annual cost incurred due to malware, threats due to ransomware, previous year records of data breach etc. Presenting our well structured Key Statistics Of It Security And Data Breach. The topics discussed in this slide are Mobile, Data, Breach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cloud Security Testing Framework With Database
Cloud Security Testing Framework With DatabaseThis slide showcase cloud base testing with service level agreement and testing the code performing of software. Introducing our Cloud Security Testing Framework With Database set of slides. The topics discussed in these slides are Output Repository, Result Analyzer, Synthetic Load Generator. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Work From Home Data Security Practices Cybersecurity Incident And Vulnerability
Best Work From Home Data Security Practices Cybersecurity Incident And VulnerabilityPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Introducing Best Work From Home Data Security Practices Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Configure WIFI Encryption, Avoid Using External Devices, System Update, using this template. Grab it now to reap its full benefits.
-
 Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability
Checklist For Work From Home Data Security Cybersecurity Incident And VulnerabilityDeliver an outstanding presentation on the topic using this Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Data Security, Reporting Process, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda Preventing Data Breaches Through Cyber Security Awareness
Agenda Preventing Data Breaches Through Cyber Security AwarenessIntroducing Agenda Preventing Data Breaches Through Cyber Security Awareness to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Awareness Campaign, Security Threats, Employees, using this template. Grab it now to reap its full benefits.
-
 Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security
Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Cyberbullying, Confidential Data, Training Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security
Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Course Description, Instructor, Rating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Security Reporting, Phishing Simulations, Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber Security
Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Introducing Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Data Breach, Operating System, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Awareness Trends In 2023 Preventing Data Breaches Through Cyber Security
Cyber Security Awareness Trends In 2023 Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase security awareness trends which the organization has to look out for in 2023. increase in malware and ransomware attack, more employees will be targeted by mobile malware attack and advancement of phishing attack are some of the major trends mentioned in the slide. Increase audience engagement and knowledge by dispensing information using Cyber Security Awareness Trends In 2023 Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Mobile Malware Attack, Get More Advanced, Ransomware Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Dos And Donts Of Prevention From Ransomware Attack Preventing Data Breaches Through Cyber Security
Dos And Donts Of Prevention From Ransomware Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the Dos and donts of ransomware prevention attack. The slide covers information about updating the software, installing a firewall software, using reliable website and sources etc. Introducing Dos And Donts Of Prevention From Ransomware Attack Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Online Criminals, Foreign Government Officials, Malicious Insiders, using this template. Grab it now to reap its full benefits.




