Powerpoint Templates and Google slides for Securing Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data security framework ppt powerpoint presentation ideas graphic images cpb
Data security framework ppt powerpoint presentation ideas graphic images cpbPresenting this set of slides with name Data Security Framework Ppt Powerpoint Presentation Ideas Graphic Images Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Data Security Framework to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Types data security ppt powerpoint presentation summary styles cpb
Types data security ppt powerpoint presentation summary styles cpbPresenting this set of slides with name Types Data Security Ppt Powerpoint Presentation Summary Styles Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Types Data Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Data security architecture ppt powerpoint presentation pictures layouts cpb
Data security architecture ppt powerpoint presentation pictures layouts cpbPresenting this set of slides with name Data Security Architecture Ppt Powerpoint Presentation Pictures Layouts Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Data Security Architecture to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Customer data security ppt powerpoint presentation model objects cpb
Customer data security ppt powerpoint presentation model objects cpbPresenting this set of slides with name Customer Data Security Ppt Powerpoint Presentation Model Objects Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Customer Data Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Project objective security of data
Project objective security of dataPresenting this set of slides with name Project Objective Security Of Data. This is a three stage process. The stages in this process are General Outcomes Framework, Practical Level Platform, Implementation Level Toolkit And Prototypes. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Big data security ppt powerpoint presentation icon background images
Big data security ppt powerpoint presentation icon background imagesPresenting this set of slides with name Big Data Security Ppt Powerpoint Presentation Icon Background Images. The topics discussed in these slides are Minimize Data Movement, Existing Skills, Attend Data Security, Analysis Requirements. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Data security breach response plan
Data security breach response planFollowing slide exhibits data security breach response plan. It includes major elements such as-developing containment plan, hardware requirement assessment and so on. Introducing our Data Security Breach Response Plan set of slides. The topics discussed in these slides are Response Stage, Response Team, Key Questions And Tasks. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data security breach steps with customer centric approach
Data security breach steps with customer centric approachData security breach steps with customer centric approach. It includes 5 steps such as- proactive and preventive analysis, data protection as the default and so on. Presenting our set of slides with Data Security Breach Steps With Customer Centric Approach. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Minimization, Security, Data Protection, Proactive And Preventive.
-
 Process for responding to security data breach
Process for responding to security data breachThis slide exhibits process for responding to security data breach. It includes multiple steps such as- analyzing the current damage, keeping record how much damage is caused and so on. Introducing our Process For Responding To Security Data Breach set of slides. The topics discussed in these slides are Survey, Limit, Learn, Engage, Record. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security and data breach incident assessment
Security and data breach incident assessmentThis slide exhibits security and data breach incidence assessment model. It includes multiple sections such as- rules and regulations sharing with third parties, communication with incidence response team and so on. Presenting our set of slides with Security And Data Breach Incident Assessment. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Survey, Limit, Learn, Engage, Record.
-
 Security and data breach report chart
Security and data breach report chartFollowing slide exhibits security and data breach report chart it includes major statistics such as- loss or theft of data, failure to redirect data and data posting to incorrect recipient. Introducing our Security And Data Breach Report Chart set of slides. The topics discussed in these slides are Security And Data Breach Report Chart. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security data breach incident report
Security data breach incident reportThis slide exhibits security data breach incident report. It includes multiple steps such as- report the number of personal data record lost, analyze the possible effects of personal data breaches and so on. Introducing our Security Data Breach Incident Report set of slides. The topics discussed in these slides are Consequences, Measures, Data Breach Details. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security data breach process by backdoor
Security data breach process by backdoorFollowing slide showcase how a data breach process is performed by hacker to collect and utilize company data. It includes following activities such as- code integration with company software, so on. Introducing our Security Data Breach Process By Backdoor set of slides. The topics discussed in these slides are Execution Persistence, Defense Evasion, Supply Chain Attack, Exfiltration, Backdoor Activates. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Steps for minimizing security and data breach
Steps for minimizing security and data breachFollowing slide exhibits steps for minimizing security and data breach. It includes major steps such as- malware protection and monitoring, source code assessment etc. Introducing our Steps For Minimizing Security And Data Breach set of slides. The topics discussed in these slides are Vulnerability Management, Infrastructure Management, Cyber Analysis, Incident Response, Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data management security tools with major segments
Data management security tools with major segmentsThis slide showcase data management security tools with major segments. It includes major outcomes such as-privacy design and development, beardless identity administration etc. Presenting our well-structured Data Management Security Tools With Major Segments. The topics discussed in this slide are Security Segment, Expected Enterprise Outcomes, Required Security Controls. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Detail impact security awareness training can reduce the risk of a data breach misconfiguration ppt icons
Detail impact security awareness training can reduce the risk of a data breach misconfiguration ppt iconsThis slide covers the impact of data breaching threats such as phishing breakdown, network intrusion breakdown, system misconfiguration, stolen lost devices or records and inadvertent disclosure. Present the topic in a bit more detail with this Detail Impact Security Awareness Training Can Reduce The Risk Of A Data Breach Misconfiguration Ppt Icons. Use it as a tool for discussion and navigation on System Misconfiguration, Stolen Lost Device Or Records, Inadvertent Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Accounting security data ppt powerpoint presentation pictures format cpb
Accounting security data ppt powerpoint presentation pictures format cpbPresenting Accounting Security Data Ppt Powerpoint Presentation Pictures Format Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Accounting Security Data. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Banking data security standards ppt powerpoint presentation slides outfit cpb
Banking data security standards ppt powerpoint presentation slides outfit cpbPresenting Banking Data Security Standards Ppt Powerpoint Presentation Slides Outfit Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Banking Data Security Standards. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Securing data over google cloud google cloud it ppt brochure
Securing data over google cloud google cloud it ppt brochureThis slide represents what measures are taken to secure the data stored on the Google Cloud, including IAM, data encryption, authentication, and bucket lock. Deliver an outstanding presentation on the topic using this Securing Data Over Google Cloud Google Cloud IT Ppt Brochure. Dispense information and present a thorough explanation of Data Encryption, Authentication, Bucket Lock, Identity, Access Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Detail data backup and data loss recovery plan steps set up advanced security management plan
Detail data backup and data loss recovery plan steps set up advanced security management planThis slide provides information about the eighth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Data Backup and Data Loss Recovery Plan. Increase audience engagement and knowledge by dispensing information using Detail Data Backup And Data Loss Recovery Plan Steps Set Up Advanced Security Management Plan. This template helps you present information on four stages. You can also present information on Categories Of Application Threats, Application Security Tools, Data Backup Frequency using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security data management maturity process to mitigate attacks
Security data management maturity process to mitigate attacksPresenting our set of slides with Security Data Management Maturity Process To Mitigate Attacks. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Analytics, Investigate, Qualify.
-
 Architecture of cloud security data cloud security it ppt ideas
Architecture of cloud security data cloud security it ppt ideasThis slide defines the architecture of the cloud security system and how data is kept, managed, and secured based on customer and service providers responsibilities.Introducing Architecture Of Cloud Security Data Cloud Security IT Ppt Ideas to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Cloud Security, using this template. Grab it now to reap its full benefits.
-
 Cloud security checklist data encryption cloud security it ppt topics
Cloud security checklist data encryption cloud security it ppt topicsThis slide represents the importance of data encryption in cloud security and what type of data should always be encrypted through private keys.Introducing Cloud Security Checklist Data Encryption Cloud Security IT Ppt Topics to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Security Checklist Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Cloud security it cloud security checklist backup and data recovery ppt grid
Cloud security it cloud security checklist backup and data recovery ppt gridThis slide represents the importance of data backup and data recovery in cloud security. It also shows how organizations should know about the data backup policies of service providers before investing in them. Introducing Cloud Security IT Cloud Security Checklist Backup And Data Recovery Ppt Grid to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Restoration In Case, Follows Effective, Physical Location, using this template. Grab it now to reap its full benefits.
-
 Cloud security threats loss of data cloud security it ppt professional
Cloud security threats loss of data cloud security it ppt professionalThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups.Introducing Cloud Security Threats Loss Of Data Cloud Security IT Ppt Professional to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Security Threats Loss Of Data, using this template. Grab it now to reap its full benefits.
-
 How does cloud security work data retention and business continuity planning cloud security it
How does cloud security work data retention and business continuity planning cloud security itThis slide represents the data recovery and business continuity plan in cloud security and what to consider while making a business continuity plan.Increase audience engagement and knowledge by dispensing information using How Does Cloud Security Work Data Retention And Business Continuity Planning Cloud Security IT. This template helps you present information on four stages. You can also present information on Impact Analysis, Recovery Strategies, Plan Development using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How does cloud security work data security cloud security it ppt slides
How does cloud security work data security cloud security it ppt slidesThis slide represents the data security under the cloud security work process, and it also shows the various factors that cover data security.Introducing How Does Cloud Security Work Data Security Cloud Security IT Ppt Slides to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Application Security, Network Security, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Quality control kpi dashboard slide for data confidentiality information security powerpoint template
Quality control kpi dashboard slide for data confidentiality information security powerpoint templateYou can use this Quality Control Kpi Dashboard Slide For Data Confidentiality Information Security Powerpoint Template to showcase the most crucial verticals of your organization or a project. This dashboard template comes with graphical representations to make the depiction of insights, data, reports, etc, very easy. It is useful in simplifying complex business concepts, allowing the viewers to make better decisions and judgments. This PowerPoint layout is specially designed for different department heads to display diverse sets of information on the topic and help make the viewers become better analysts. Therefore, this PowerPoint layout is not only resourceful, but it is also attention-grabbing and high-quality. Everything from the content and graphics used in this slide can be modified and adjusted as per your needs. It can also be reproduced in PNG, JPG, and PDF formats, which increases the user-friendliness of this layout.
-
 Security management plan steps in detail data backup and data loss recovery plan ppt professional
Security management plan steps in detail data backup and data loss recovery plan ppt professionalThis slide provides information about the eighth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e Data Backup and Data Loss Recovery Plan. Introducing Security Management Plan Steps In Detail Data Backup And Data Loss Recovery Plan Ppt Professional to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Storage, Data Category, Storage Location, Data Restoration, Data Backup, using this template. Grab it now to reap its full benefits.
-
 Some data security overcome challenge cyber security healthcare ppt infographics inspiration
Some data security overcome challenge cyber security healthcare ppt infographics inspirationThe slide shows some measures that can be adopted by the company in order to ensure data protection and restrict access such Get Customized security programs, Inculcate organizations with healthcare threat intelligence softwares, get updated with latest security management softwares, ensure insider Threat protection etc. Increase audience engagement and knowledge by dispensing information using Some Data Security Overcome Challenge Cyber Security Healthcare Ppt Infographics Inspiration. This template helps you present information on six stages. You can also present information on Data, Programs, Security, Organizations, Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
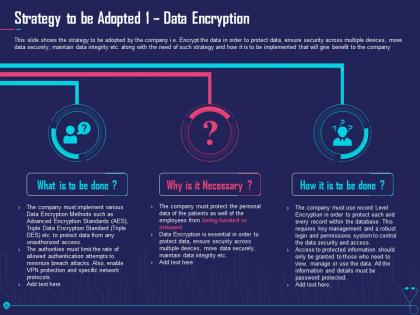 Strategy to be adopted 1 data encryption overcome challenge cyber security healthcare ppt tips
Strategy to be adopted 1 data encryption overcome challenge cyber security healthcare ppt tipsThis slide shows the strategy to be adopted by the company i.e. Encrypt the data in order to protect data, ensure security across multiple devices, move data securely, maintain data integrity etc. along with the need of such strategy and how it is to be implemented that will give benefit to the company. Increase audience engagement and knowledge by dispensing information using Strategy To Be Adopted 1 Data Encryption Overcome Challenge Cyber Security Healthcare Ppt Tips. This template helps you present information on three stages. You can also present information on Implement, Security, Patients, System, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Some data security measures to overcome cybersecurity threats by abs healthcare com
Some data security measures to overcome cybersecurity threats by abs healthcare comThe slide shows some measures that can be adopted by the company in order to ensure data protection and restrict access such Get Customized security programs, Inculcate organizations with healthcare threat intelligence softwares, get updated with latest security management softwares, ensure insider Threat protection etc. Increase audience engagement and knowledge by dispensing information using Some Data Security Measures To Overcome Cybersecurity Threats By Abs Healthcare Com. This template helps you present information on four stages. You can also present information on Data, Softwares, Organizations, Management, Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Some data security measures reduce cloud threats healthcare company
Some data security measures reduce cloud threats healthcare companyThe slide shows some measures that can be adopted by the company in order to ensure data protection and restrict access such Get Customized security programs, Inculcate organizations with healthcare threat intelligence softwares, get updated with latest security management softwares, ensure insider Threat protection etc. Introducing Some Data Security Measures Reduce Cloud Threats Healthcare Company to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Program, Softwares, Organizations, Techniques, Management, using this template. Grab it now to reap its full benefits.
-
 Agenda implementing security management plan reduce threats protect sensitive company data
Agenda implementing security management plan reduce threats protect sensitive company dataIncrease audience engagement and knowledge by dispensing information using Agenda Implementing Security Management Plan Reduce Threats Protect Sensitive Company Data. This template helps you present information on six stages. You can also present information on Management, Security, Plan, Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing security management plan reduce threats protect sensitive company data icons slide
Implementing security management plan reduce threats protect sensitive company data icons slidePresenting our well crafted Implementing Security Management Plan Reduce Threats Protect Sensitive Company Data Icons Slide set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Big data security threats ppt powerpoint presentation pictures aids cpb
Big data security threats ppt powerpoint presentation pictures aids cpbPresenting Big Data Security Threats Ppt Powerpoint Presentation Pictures Aids Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Big Data Security Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Enabling data security risk management action plan management to improve project safety it
Enabling data security risk management action plan management to improve project safety itThis slide provide details about data security risk management action plan which will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them. Present the topic in a bit more detail with this Enabling Data Security Risk Management Action Plan Management To Improve Project Safety IT. Use it as a tool for discussion and navigation on Potential Risk, Risk Level, Reason For Risk Rating, Action, Duration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information security process to manage firms sensitive data contd management to improve project safety it
Information security process to manage firms sensitive data contd management to improve project safety itThis slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Introducing Information Security Process To Manage Firms Sensitive Data Contd Management To Improve Project Safety IT to increase your presentation threshold. Encompassed with Firewall Audit Checklist, VPN Configuration, Penetrating Testing stages, this template is a great option to educate and entice your audience. Dispence information on Firewall Audit Checklist,VPN Configuration,Penetrating Testing, using this template. Grab it now to reap its full benefits.
-
 Information security process to manage firms sensitive data management to improve project safety it
Information security process to manage firms sensitive data management to improve project safety itThis slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Increase audience engagement and knowledge by dispensing information using Information Security Process To Manage Firms Sensitive Data Management To Improve Project Safety IT. This template helps you present information on three stages. You can also present information on Privileged Password Management, Daily Tasks Performed By Network Administrator, Network Security Audit Checklist using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security of data and networks in edge computing edge computing it
Security of data and networks in edge computing edge computing itThis slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable. Introducing Security Of Data And Networks In Edge Computing Edge Computing IT to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Of Data And Networks In Edge Computing, using this template. Grab it now to reap its full benefits.
-
 Icons slide for effective security monitoring plan to eliminate cyber threats and data breaches
Icons slide for effective security monitoring plan to eliminate cyber threats and data breachesIntroducing our well researched set of slides titled Icons Slide For Effective Security Monitoring Plan To Eliminate Cyber Threats And Data Breaches. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Some data security measures to abs healthcare company overcome the it security
Some data security measures to abs healthcare company overcome the it securityThe slide shows some measures that can be adopted by the company in order to ensure data protection and restrict access such Get Customized security programs, Inculcate organizations with healthcare threat intelligence softwares, get updated with latest security management softwares, ensure insider Threat protection etc. Increase audience engagement and knowledge by dispensing information using Some Data Security Measures To Abs Healthcare Company Overcome The It Security. This template helps you present information on six stages. You can also present information on Customized Security, Security Management, Ensure Insider using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategy to be adopted 1 data encryption overcome the it security
Strategy to be adopted 1 data encryption overcome the it securityThis slide shows the strategy to be adopted by the company i.e. Encrypt the data in order to protect data, ensure security across multiple devices, move data securely, maintain data integrity etc. along with the need of such strategy and how it is to be implemented that will give benefit to the company Increase audience engagement and knowledge by dispensing information using Strategy To Be Adopted 1 Data Encryption Overcome The It Security. This template helps you present information on three stages. You can also present information on Implement Various Data, Encryption Methods Such, Hacked Or Misused using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Back up essential data systems security ppt powerpoint presentation file infographics cpb
Back up essential data systems security ppt powerpoint presentation file infographics cpbPresenting our Back Up Essential Data Systems Security Ppt Powerpoint Presentation File Infographics Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Back Up Essential Data Systems Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Pitchbook for security underwriting deal consolidated financial data income statement
Pitchbook for security underwriting deal consolidated financial data income statementThe slide provides the post acquisition consolidated financials of acquiring company and acquired company. Key heading include, revenue, operating and Selling, general, and administration expenses, operating income, and net income Deliver an outstanding presentation on the topic using this Pitchbook For Security Underwriting Deal Consolidated Financial Data Income Statement. Dispense information and present a thorough explanation of Gross Profit, Operating Expenses, Selling Expenses, Advertising Expenses, Administration Expenses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Administrator updating data system security
Administrator updating data system securityPresenting our set of slides with Administrator Updating Data System Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Administrator Updating Data System Security.
-
 Essentials Of Information System Data And Application Security Audit
Essentials Of Information System Data And Application Security AuditThe following slide highlights the essentials of information system data and application security audit illustrating key headings which includes data confidentiality, information backup, application development and configuration management Introducing our premium set of slides with Essentials Of Information System Data And Application Security Audit. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Confidentiality, Application Development, Information Backup. So download instantly and tailor it with your information.
-
 Cyber Security Checklist For Historical Data Analysis
Cyber Security Checklist For Historical Data AnalysisThis slide represents cyber security analysis checklist for providing systematic and organized approach to evaluate, improve and maintain organizations security posture. It includes basis such as aspects, tasks, checkpoints, authorized head, status and notes. Presenting our well structured Cyber Security Checklist For Historical Data Analysis. The topics discussed in this slide are Authorized, Status, Analysis. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 User Behavior Analysis Considering Cyber Security Data
User Behavior Analysis Considering Cyber Security DataThis slide demonstrates cyber security about correlation analysis between downtime and organization size to guide service providers gaining insights from various factors. It includes aspects such as growth drivers, opportunities and contributing factors. Presenting our well structured User Behavior Analysis Considering Cyber Security Data. The topics discussed in this slide are Growth, Opportunities, Contributing. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Security Management Program To Protect Data
Information Security Management Program To Protect DataThis slide shows information security program checklist that helps toidentify potential weaknesses or vulnerabilities in system. It further includes metrics such as risk management, information security policy ,information security responsibility etc. Presenting our well structured Information Security Management Program To Protect Data The topics discussed in this slide are Risk Management, Information Security Policy. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 IT Security Audit Controls To Reduce Data Threats
IT Security Audit Controls To Reduce Data ThreatsThis slide covers various control measures to reduce the effect of data security threats. The purpose of this slide is to help businesses in formulating a strong security strategy for data protection. It provides security controls to threats such as malware attacks, ransomware, inadvertent insiders and phishing. Introducing our premium set of slides with IT Security Audit Controls To Reduce Data Threats. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Threats, Security Controls. So download instantly and tailor it with your information.
-
 Network Security Audit Framework Based On Log Data Mining
Network Security Audit Framework Based On Log Data MiningThis slide presents hierarchical framework for network security management in cloud computing environment. The purpose of this slide is to assess security risks of cloud platforms. It covers elements such as firewall log, network data, data collection, log library, association rule mining, rule formulation, audit assessment, etc. Introducing our Network Security Audit Framework Based On Log Data Mining set of slides. The topics discussed in these slides are Firewall Log, System Log, Association Rule Mining. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Managing Sensitive Data Through SaaS Security
Managing Sensitive Data Through SaaS SecurityThis slide illustrates some SaaS security threats to enhance security practices and eliminate them. It includes elements such as phishing, account takeovers, lack of transparency, etc. Presenting our well structured Managing Sensitive Data Through SaaS Security. The topics discussed in this slide are Data Access Risk, Lack Of Transparency, Identity Theft. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Process Of SaaS Security For Encrypting Sensitive Data
Process Of SaaS Security For Encrypting Sensitive DataThis slide depicts the SaaS security process to acknowledge the gap and have proactive approach. This includes phases of SaaS security such as discovering, monitoring and protecting. Presenting our set of slides with Process Of SaaS Security For Encrypting Sensitive Data. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Utility, Assess Risk, Review Log Activities.
-
 Data Protection Security In Powerpoint And Google Slides Cpp
Data Protection Security In Powerpoint And Google Slides CppPresenting Data Protection Security In Powerpoint And Google Slides Cpp slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Data Protection Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.



