Powerpoint Templates and Google slides for Securing Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Architectural Big Data In Cyber Security
Architectural Big Data In Cyber SecurityThis slide depicts the tactics used to protect cyber security network using big data analytics. Its aim is to use various tactics and secure the cyber network against the threats. This slide includes performance, accuracy, scalability, reliability, security, usability, etc. Introducing our Architectural Big Data In Cyber Security set of slides. The topics discussed in these slides are Performance, Accuracy, Scalability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Benefits Of Big Data In Cyber Security
Benefits Of Big Data In Cyber SecurityThis slide showcases the benefits of including big data in the organisation for cyber security. Its purpose is to use identify risk and optimise cost while managing cyber security. This slide includes business innovation tools, optimise cost, customer retention, etc. Presenting our set of slides with Benefits Of Big Data In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Customer, Optimise, Business.
-
 Big Data Attack Detection Model In Cyber Security
Big Data Attack Detection Model In Cyber SecurityThis slide visualises the detection models used in defending cyber security in big data. Its aim is to detect any malicious attack. This slide includes training data, data preparation, testing, attack detection model, etc. Introducing our Big Data Attack Detection Model In Cyber Security set of slides. The topics discussed in these slides are Network, Activity, Application. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Big Data Tactics In Cyber Security
Big Data Tactics In Cyber SecurityThis slide showcases the big data tactics to deal in cyber security. Its aim is to process the data and send alerts to secure the network. This slide includes information sharing, alert notification, user action, verification, etc. Presenting our well structured Big Data Tactics In Cyber Security. The topics discussed in this slide are Activity, Data, Correlation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Components Of Big Data Analytics In Cyber Security
Components Of Big Data Analytics In Cyber SecurityThis slide showcases the components of big data analytics in cyber security. Its objective is to improve performance and security tactics in cyber security using big data. This includes data collection, data pre processing, data analysis, visualisation. Presenting our well structured Components Of Big Data Analytics In Cyber Security. The topics discussed in this slide are Collection, Storage, Analysis. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Fortify Cyber Security By Using Big Data Strategies
Fortify Cyber Security By Using Big Data StrategiesThis slide contains strategies to fortify cyber security using big data. Its aim is to predict future anomalies and detect frauds in cyber security. This slide includes automated monitoring, real time protection. Presenting our set of slides with Fortify Cyber Security By Using Big Data Strategies. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Predict, Detection, Monitoring.
-
 Improve Cyber Security By Big Data In Companies
Improve Cyber Security By Big Data In CompaniesThis slide helps you identify and improve cyber security by integrating big data in companies. Its aim is to prevent attacks and security breaches. This slide consists of prevention of malware attacks, monitor logs, assess risk, integrate big data, etc. Introducing our premium set of slides with Improve Cyber Security By Big Data In Companies. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Attacks, Monitor, Integrate. So download instantly and tailor it with your information.
-
 Leverage Big Data In Cyber Security Application
Leverage Big Data In Cyber Security ApplicationThis slide showcases the various applications of big data in cybersecurity. Its objective is to tackle different situation for processing big set of data. This slide includes intrusion detection, malware, social media, code security, lightweight cyber security, etc. Presenting our set of slides with Leverage Big Data In Cyber Security Application. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detection, Social, security.
-
 Using Big Data In Cyber Security Against Attacks
Using Big Data In Cyber Security Against AttacksThis slide informs about using big data again cyber security attacks. Its aim is to protect against cyber attacks and provide solutions to the company. This slide includes access control, encryption based attack, DDoS, false data, etc. Presenting our well structured Using Big Data In Cyber Security Against Attacks. The topics discussed in this slide are Security, Cyber, Attacks. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Applications Of Big Data Infrastructure Security
Applications Of Big Data Infrastructure SecurityThis slide represents the application infrastructure security in big data. Its objective is to manage application and examine the system for better efficiency. This slide includes network traffic examination, study of behaviour and cloud monitoring. Introducing our Applications Of Big Data Infrastructure Security set of slides. The topics discussed in these slides are Network, Behaviour, Evaluation. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Infrastructure Security In Big Data Analysis
Infrastructure Security In Big Data AnalysisThis slide represents the big data analysis and infrastructure security importance. Its aim is to provide valuable insights and enhance protection against breaches. This slide includes predictive analysis, prescriptive analytics, cyber analytics and diagnostic analytics. Presenting our set of slides with Infrastructure Security In Big Data Analysis. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prescriptive, Analysis, Cyber.
-
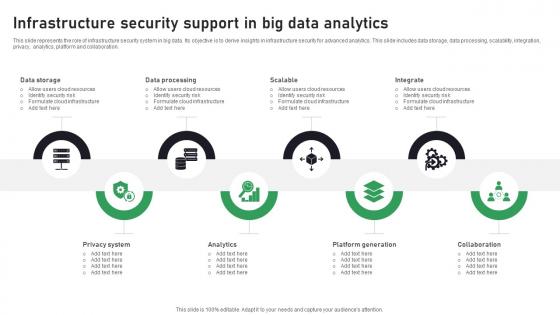 Infrastructure Security Support In Big Data Analytics
Infrastructure Security Support In Big Data AnalyticsThis slide represents the role of infrastructure security system in big data. Its objective is to derive insights in infrastructure security for advanced analytics. This slide includes data storage, data processing, scalability, integration, privacy, analytics, platform and collaboration. Presenting our set of slides with Infrastructure Security Support In Big Data Analytics. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Storage, Processing, Scalable.
-
 Cyber Security KPIS To Measure Data Security
Cyber Security KPIS To Measure Data SecurityThe mentioned slide emphasizes critical key performance indicators KPIs such as the level of preparedness, unidentified devices, intrusion attempts, security incidents, and mean time to detect. These metrics serve as valuable benchmarks for measuring and improving data security, enabling organizations to assess their cybersecurity posture effectively. Introducing our Cyber Security KPIS To Measure Data Security set of slides. The topics discussed in these slides are Level Of Preparedness, Intrusion Attempts, Security Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Measures To Protect Business Data
Cyber Security Measures To Protect Business DataThe highlighted slide underscores essential measures, including robust passwords, regular software updates, antivirus protection, multi factor authentication, and access control. These steps collectively enhance cybersecurity, fortifying defenses to safeguard critical business data against potential threats. Presenting our set of slides with Cyber Security Measures To Protect Business Data. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strong And Complex Passwords, Software Updates, Enhance Security.
-
 Cyber Security Strategies For Data Management
Cyber Security Strategies For Data ManagementThe mentioned slide underscores critical strategies, including updated software, firewall protection, awareness of phishing scams, safeguarding sensitive information, and securing mobile devices. These cybersecurity measures collectively contribute to effective data management and protection against potential threats. Introducing our premium set of slides with Cyber Security Strategies For Data Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Keep Software Up To Date, Reduced Data Breach Risk, Empowered User Vigilance. So download instantly and tailor it with your information.
-
 Cybersecurity Framework For Ensuring Data Security
Cybersecurity Framework For Ensuring Data SecurityThe mentioned slide emphasizes crucial components such as identify, protect, detect, respond, and recover, outlining a comprehensive cybersecurity framework. This framework is instrumental in ensuring robust data security by covering key aspects of risk management and incident response throughout the data lifecycle. Introducing our premium set of slides with Cybersecurity Framework For Ensuring Data Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regularly Schedule, Restrict Employee Access, Mandate Individual User. So download instantly and tailor it with your information.
-
 Prevention Techniques For Cyber Security Data Attacks
Prevention Techniques For Cyber Security Data AttacksThe highlighted slide identifies critical types of cybersecurity attacks on data, including malware, phishing, password attacks, man in the middle attacks, and SQL injection. This information is essential for understanding and preparing against various threats, contributing to a more robust defense strategy for safeguarding data. Introducing our Prevention Techniques For Cyber Security Data Attacks set of slides. The topics discussed in these slides are Malware Attack, Phishing Attack, Password Attack. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SS
Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SSThis slide covers key use cases of Oracle Database Crypto-Secure Data Management such as healthcare data protection, financial transactions, government data security, retail customer privacy, and intellectual property protection. Deliver an outstanding presentation on the topic using this Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SS Dispense information and present a thorough explanation of Healthcare Data, Financial Transactions, Customer Privacy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS V
Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS V. Dispense information and present a thorough explanation of Data Usage Policy, Data Encryption, Endpoint Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats
Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Increase audience engagement and knowledge by dispensing information using Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Time Consuming Process, Speedy Process, Incremental Backup using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Aerospace Big Data Security Metrics Checklist
Aerospace Big Data Security Metrics ChecklistThis slide represents checklist for security metrics of aerospace big data. It aims to help organization to effectively engage with different departments of organization by determining risk and threats. It includes various elements such as risks signed off, adequate resolution of internal compliance, etc. Presenting our set of slides with Aerospace Big Data Security Metrics Checklist. This exhibits information on nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risks Signed Off, Post Awareness Initiatives, Security Occurrences.
-
 Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among
Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness AmongThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Introducing Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Email Attachments, Systems, Employees using this template. Grab it now to reap its full benefits.
-
 Applications Of Digital Solution For Ensuring Data Security
Applications Of Digital Solution For Ensuring Data SecurityThis slide showcases use cases of digital solution. The main purpose of this template is to showcase methods for optimizing resources in business. This includes streamlining operations, improving decision making, enabling remote work, etc. Presenting our set of slides with Applications Of Digital Solution For Ensuring Data Security This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Streamlining Operations, Enhancing Customer Experience, Improve Decision Making
-
 Strategic Approach For Effective Data Migration Case Study Data Security And Compliance In Cloud Migration
Strategic Approach For Effective Data Migration Case Study Data Security And Compliance In Cloud MigrationThe following slide showcases a case study on data security and compliance in cloud migration. It includes various elements such as company details, challenges, and solutions. Increase audience engagement and knowledge by dispensing information using Strategic Approach For Effective Data Migration Case Study Data Security And Compliance In Cloud Migration. This template helps you present information on three stages. You can also present information on Data Security, Cloud Migration, Security And Confidentiality, Customer Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategic Approach For Effective Data Migration Checklist For Ensuring Secure Data Migration
Strategic Approach For Effective Data Migration Checklist For Ensuring Secure Data MigrationThe purpose of this slide is to showcase a checklist for ensuring safe migration of data from one source to another. It includes various tactics such as data protection impact assessment, data security and encryption, data retention and deletion, etc. Deliver an outstanding presentation on the topic using this Strategic Approach For Effective Data Migration Checklist For Ensuring Secure Data Migration. Dispense information and present a thorough explanation of Legal Limitations, Compliance Requirements, Legacy Database Schema, Intrusion Detection Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies
Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By CompaniesThe purpose of this slide is to assess security and privacy challenges, and their impact on data migration process. It includes challenges and need for ensuring data privacy. Introducing Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Data Security And Privacy Challenges, Loss Of Customers, Sensitive Data, Poses Security And Privacy Concerns, using this template. Grab it now to reap its full benefits.
-
 Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process
Strategic Approach For Effective Data Migration Steps For A Secure Data Migration ProcessThe purpose of this slide is to represent the process of secure and safe data migration from one platform to another. It includes various stages such as assessing data sources, choosing method, designing architecture, etc. Introducing Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Design Architecture, Validate And Verify Results, Assess Data Sources, Data Migration Process, using this template. Grab it now to reap its full benefits.
-
 Securing Online Payments Through Big Data Analytics In E Commerce
Securing Online Payments Through Big Data Analytics In E CommerceThis slide showcases securing online payments through big data analytics in e-commerce which helps an organization to protect customers against cyber threat. It include details such as identify fraudulent transactions, analyze trending payment methods, etc. Introducing our premium set of slides with Securing Online Payments Through Big Data Analytics In E Commerce. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Fraudulent Transactions, Introduce EMI Payments, Track Payment Address. So download instantly and tailor it with your information.
-
 Action Plan To Enhance Data Security Management
Action Plan To Enhance Data Security ManagementThis slide showcases the action plan assisting businesses to train their employees on data security management to increase knowledge and awareness. It includes various elements such as courses, modules, duration, rating, and deadlines. Introducing our Action Plan To Enhance Data Security Management set of slides. The topics discussed in these slides are Execute Access Control, Responsible Leader, Reduce System Vulnerability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices To Enhance Data Security Management
Best Practices To Enhance Data Security ManagementThis slide represents the best practices assisting companies to enhance data security management implications. It includes various practices such as data access policy audit, use of data security tools, providing training, etc. Presenting our well structured Best Practices To Enhance Data Security Management. The topics discussed in this slide are Implement Data Access, Security Management Tools, Outside Company Storage. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Comparative Assessment For Data Security Management Tools
Comparative Assessment For Data Security Management ToolsThis slide represents the comparative analysis assisting businesses to choose correct tools to enhance data security management. It includes various tools such as oracle data safe, satori data security platform, etc. Introducing our Comparative Assessment For Data Security Management Tools set of slides. The topics discussed in these slides are Oracle Data Safe, Data Security Platform, Manager For Databases. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Employee Training Action Plan On Data Security Management
Employee Training Action Plan On Data Security ManagementThis slide showcases the action plan assisting businesses to train their employees on data security management to increase knowledge and awareness. It includes various elements such as courses, modules, duration, rating and deadlines. Introducing our Employee Training Action Plan On Data Security Management set of slides. The topics discussed in these slides are Cloud Data Security, Security And Privacy, Cloud Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 External Threats To Data Security Management With Solutions
External Threats To Data Security Management With SolutionsThis slide showcases various external threats that affect the data security management of businesses with solutions to mitigate those risks. It includes various threats such as SQL injection, ransomware, phishing, and accidental exposure. Introducing our premium set of slides with External Threats To Data Security Management With Solutions. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Accidental Exposure, Unwanted Operations, Secure Mechanism. So download instantly and tailor it with your information.
-
 Framework To Manage Data Security Center Effectively
Framework To Manage Data Security Center EffectivelyThis slide showcases the framework that assist companies to manage and monitor their data center security effectively against threats. It includes various elements such as security operations, application security, security architecture, etc. Presenting our well structured Framework To Manage Data Security Center Effectively. The topics discussed in this slide are Application Platform, Access Management, Application Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Fundamentals To Enhance Data Security Management
Fundamentals To Enhance Data Security ManagementThis slide represents the fundamentals that help businesses to enhance and scale their data security management planning. It includes various elements such as visibility, security as code, automation, monitoring, and assessment. Presenting our set of slides with Fundamentals To Enhance Data Security Management. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Collaborated Protection, Data Security, External Assessment.
-
 Leveraging Technologies To Enhance Data Security Management
Leveraging Technologies To Enhance Data Security ManagementThis slide represents the multiple technologies that assist companies to upgrade and enhance their data security management from threats. It includes technologies such as encryption, data masking, access control, data loss prevention, etc. Introducing our Leveraging Technologies To Enhance Data Security Management set of slides. The topics discussed in these slides are Data Loss Prevention, Access Control, Data Masking. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Management Framework For Enhancing Data Protection
Security Management Framework For Enhancing Data ProtectionThis slide presents the framework that helps businesses to manage data security against modern attack vectors and network vulnerabilities. It includes various elements such as govern, discover, insights, protect and monitor. Presenting our well structured Security Management Framework For Enhancing Data Protection. The topics discussed in this slide are Privacy Readiness, Risk And Security Analytics, Data Driven Outcomes. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Management Policies To Mitigate Internal Data Threats
Security Management Policies To Mitigate Internal Data ThreatsThis slide focuses on the policies for security management helping companies to mitigate internal data threats efficiently. It includes policies for metadata, backup, internal protocol, emails, etc. Introducing our premium set of slides with Security Management Policies To Mitigate Internal Data Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protocol For Visitors, Internet Protocol, Security Audit. So download instantly and tailor it with your information.
-
 Strategies And Tools To Enhance Big Data Security Management
Strategies And Tools To Enhance Big Data Security ManagementThis slide showcases the strategies and tools helping companies to effectively manage and monitor big data security from cyber threats. It includes strategies such as cloud security monitoring, centralized key management, incident investigation, etc. Introducing our Strategies And Tools To Enhance Big Data Security Management set of slides. The topics discussed in these slides are Cloud Security Monitoring, Centralized Key Management, Network Traffic Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Tokenization Working Process For Data Security Implementing Effective Tokenization
Tokenization Working Process For Data Security Implementing Effective TokenizationThis slide represents the process of tokenization which includes downloading a mobile payment application, generating tokens, etc. Deliver an outstanding presentation on the topic using this Tokenization Working Process For Data Security Implementing Effective Tokenization. Dispense information and present a thorough explanation of Tokenization Working Process, Data Security, Mobile Payment Application, Generating Tokens using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Storage Practices For Data Security And Management
Cloud Storage Practices For Data Security And ManagementThis slide highlights ways for managing cloud storage to ensure data protection. The purpose of this slide is to aid businesses in implementing measures for protecting sensitive information from potential threats. It includes elements such as encryption, access control, etc. Presenting our set of slides with Cloud Storage Practices For Data Security And Management. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Encryption, Access Control, Security Training.
-
 Asymmetric Data Encryption For Web Security
Asymmetric Data Encryption For Web SecurityThis slide showcases the workflow of asymmetric data encryption for security of web which includes components such as public key, private key, original text, etc. Introducing our Asymmetric Data Encryption For Web Security set of slides. The topics discussed in these slides are Asymmetric Data Encryption, Web Security, Private Key, Original Text. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Steps To Integrate Wireless Internet For Data Security
Steps To Integrate Wireless Internet For Data SecurityThe following slide outlines crucial steps, including strong passwords, firmware updates, encryption, remote management, firewall protection, and data backup, to demonstrate the integration of wireless internet for enhanced data security. Presenting our set of slides with Steps To Integrate Wireless Internet For Data Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Backup, Firewall Protection, Disable Remote Management.
-
 Types Of Wireless Internet Security For Data Protection
Types Of Wireless Internet Security For Data ProtectionThe following slide highlights key points such as WEP, WPA, WPA2, and WPA3 protocols to show types of wireless internet security for privacy protection. It helps in understanding and comparing different safety procedures for effective data protection. Introducing our premium set of slides with Types Of Wireless Internet Security For Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Wireless Internet. So download instantly and tailor it with your information.
-
 Wireless Internet Security Measures To Prevent Data Theft
Wireless Internet Security Measures To Prevent Data TheftThe outlined slide comprehensively addresses crucial elements such as encryption, authentication, access control, device security, and intrusion detection prevention, offering a holistic perspective on wireless internet security to effectively prevent data theft. It serves as a valuable resource for understanding and implementing robust security measures in the wireless environment. Introducing our premium set of slides with Wireless Internet Security Measures To Prevent Data Theft. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Encryption, Access Control, Intrusion Detection And Prevention Systems. So download instantly and tailor it with your information.
-
 Data Center Facility Security Plan
Data Center Facility Security PlanThe purpose of this slide is to ensure comprehensive protection against unauthorized access, physical threats, and data breaches including security aspects such as data center layout, environmental controls, etc. Introducing our premium set of slides with name Data Center Facility Security Plan. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Environmental Controls, Data Center Layout, Network Security, Vendor And Contractor Access. So download instantly and tailor it with your information.
-
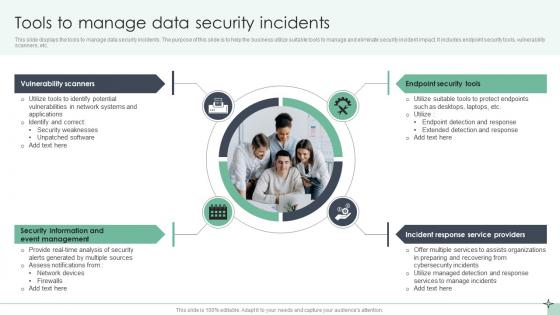 Tools To Manage Data Security Incidents
Tools To Manage Data Security IncidentsThis slide displays the tools to manage data security incidents. The purpose of this slide is to help the business utilize suitable tools to manage and eliminate security incident impact. It includes endpoint security tools, vulnerability scanners, etc. Presenting our set of slides with Tools To Manage Data Security Incidents. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Scanners, Endpoint Security Tools, Incident Response.
-
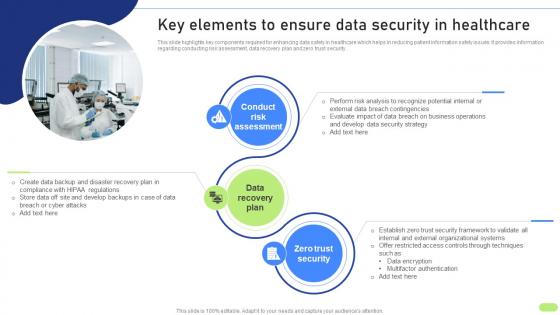 Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SS
Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SSThis slide highlights key components required for enhancing data safety in healthcare which helps in reducing patient information safety issues. It provides information regarding conducting risk assessment, data recovery plan and zero trust security. Introducing Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Conduct Risk Assessment, Data Recovery Plan, Zero Trust Security, using this template. Grab it now to reap its full benefits.
-
 Project Data Security And Privacy Checklist Matrix
Project Data Security And Privacy Checklist MatrixThe purpose of this slide is to introduce project data security and privacy checklist matrix, which systematically ensures and enhances data and privacy protection measures throughout the project lifecycle. Introducing our Project Data Security And Privacy Checklist Matrix set of slides. The topics discussed in these slides are Data Encryption, Access Controls, Security Audits, User Authentication. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cloud Access Security Broker Pillar Data Security CASB Cloud Security
Cloud Access Security Broker Pillar Data Security CASB Cloud SecurityThis slide talks about the data security pillar of the cloud access security broker pillar. This slide highlights how CASB data security can help organizations improve their IT requirements and business operations and detect security breaches before they happen. Introducing Cloud Access Security Broker Pillar Data Security CASB Cloud Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Business Operations, Risk Assessments, using this template. Grab it now to reap its full benefits.
-
 Comparison Between CASB And Data Loss Prevention DLP CASB Cloud Security
Comparison Between CASB And Data Loss Prevention DLP CASB Cloud SecurityThis slide describes the difference between cloud access security broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Present the topic in a bit more detail with this Comparison Between CASB And Data Loss Prevention DLP CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Data Loss Prevention, Focus Area, Implementation And Relationship. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Big Data Security Technology To Enhance Systems Efficiency
Big Data Security Technology To Enhance Systems EfficiencyThis slide represents big data security technology which enhances security of non relational databases and boosts endpoint security. It includes big data security technology to enhance systems efficiency such as encryption, user access control etc. Presenting our set of slides with name Big Data Security Technology To Enhance Systems Efficiency. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Centralized Key Management, Physical Security, User Access Control, Encryption.
-
 Checklist For Holistic Data Security And Privacy In Big Data Technology
Checklist For Holistic Data Security And Privacy In Big Data TechnologyThis slide represents checklist for data security and privacy in big data technology which assists to prevent unauthorized access and provides safeguard against cyber threat. It includes key steps such as secure and monitor, find and classify, etc. Introducing our Checklist For Holistic Data Security And Privacy In Big Data Technology set of slides. The topics discussed in these slides are Find And Classify, Secure And Monitor, Harden, Protect And Remain Vigilant. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Privacy And Security Issues Faced In Big Data Technology
Privacy And Security Issues Faced In Big Data TechnologyThis slide represents privacy and security issues faced in big data technology which provides greater insight into data and assists to make better business decisions. It includes privacy and security issues faced in big data technology such as secure computations, access control, etc. Presenting our set of slides with name Privacy And Security Issues Faced In Big Data Technology. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secure Computations, Access Control, Protecting Data And Transaction Logs, Real Time Security Monitoring.
-
 Migration Testing For Secure Customer Database
Migration Testing For Secure Customer DatabaseThe purpose of this slide is to showcase secure customer database migration, which helps in enduring protection of sensitive customer data and bolsters trust. Introducing our Migration Testing For Secure Customer Database set of slides. The topics discussed in these slides are Migration Script, Details Transactions. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Different Encryption Methods To Secure Business Data
Different Encryption Methods To Secure Business DataThis slide represents various types of encryption method which assists businesses to protect data and maintain regulatory compliances. It includes different encryption methods to secure business data such as advance encryption standards, rivest shamir adleman, etc. Introducing our premium set of slides with name Different Encryption Methods To Secure Business Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Format Preserving Encryption, Blowfish, Advance Encryption Standards. So download instantly and tailor it with your information.
-
 Emerging Encryption Trends For Enhancing Data Security
Emerging Encryption Trends For Enhancing Data SecurityThis slide represents latest trends in encryption which assists to scramble data into a secret code which can be unlocked with unique digital key. It includes latest trends in encryption such as homomorphic encryption, quantum encryption, etc. Presenting our set of slides with name Emerging Encryption Trends For Enhancing Data Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Quantum Cryptography, Homomorphic Encryption, Moving Target Defense.
-
 Cyber Hazard Mitigation Plan For Data Security
Cyber Hazard Mitigation Plan For Data SecurityThis slide represents hazard mitigation plan to enhance cybersecurity and data protection including risks such as malware, phishing attack, and DDoS attack. Presenting our well structured Cyber Hazard Mitigation Plan For Data Security. The topics discussed in this slide are Malware, Phishing Attack, Ddos Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SS
Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SSThis slide provides glimpse about utilizing secure multi-party computation SMPC approach that can help businesses in boosting data confidentiality. It includes stages such as input sharing, secure computation, output reconstruction, etc. Present the topic in a bit more detail with this Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SS. Use it as a tool for discussion and navigation on Secure Computation, Output Reconstruction, Input Sharing. This template is free to edit as deemed fit for your organization. Therefore download it now.




