Powerpoint Templates and Google slides for Secured Network
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Icon of wireless security for wifi networks with smart lock
Icon of wireless security for wifi networks with smart lockIntroducing our premium set of slides with Icon Of Wireless Security For WIFI Networks With Smart Lock. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon Of Wireless Security For WIFI Networks With Smart Lock. So download instantly and tailor it with your information.
-
 A3 Table Of Contents For Network Security Ppt Guidelines
A3 Table Of Contents For Network Security Ppt GuidelinesIntroducing A3 Table Of Contents For Network Security Ppt Guidelines to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Requirement, Organization, Information, using this template. Grab it now to reap its full benefits.
-
 Elements Of Network Security Application Security Ppt Slides Model
Elements Of Network Security Application Security Ppt Slides ModelThis slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Introducing Elements Of Network Security Application Security Ppt Slides Model to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Required, Information, Customers, Obstruction, using this template. Grab it now to reap its full benefits.
-
 Elements Of Network Security Cloud Security Ppt Slides Background Image
Elements Of Network Security Cloud Security Ppt Slides Background ImageThis slide defines the cloud security element of network security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. Increase audience engagement and knowledge by dispensing information using Elements Of Network Security Cloud Security Ppt Slides Background Image. This template helps you present information on one stages. You can also present information on Safeguards, Technology, Protect, Resources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Elements Of Network Security Operational Security Ppt Styles Example File
Elements Of Network Security Operational Security Ppt Styles Example FileThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Introducing Elements Of Network Security Operational Security Ppt Styles Example File to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Sensitive, Administration, Operations, using this template. Grab it now to reap its full benefits.
-
 Network Security How Is Automation Used In Networksecurity
Network Security How Is Automation Used In NetworksecurityThis slide depicts the network protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Increase audience engagement and knowledge by dispensing information using Network Security How Is Automation Used In Networksecurity. This template helps you present information on three stages. You can also present information on Threat Detection, Threat Response, Human Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Key Elements Of Network Security
Network Security Key Elements Of Network SecurityThis slide represents the different elements of Network security such as application security, network security, information security, etc.Increase audience engagement and knowledge by dispensing information using Network Security Key Elements Of Network Security. This template helps you present information on seven stages. You can also present information on Elements, Network, Security, Planning, Recovery, Operational Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Minimize Administrative And Staff Privileges
Network Security Minimize Administrative And Staff PrivilegesThis slide shows the importance of minimizing the administrative and staff privilege by showing its benefits for the company. Introducing Network Security Minimize Administrative And Staff Privileges to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Administrative, Employees, Minimize, Prevent, Employees, using this template. Grab it now to reap its full benefits.
-
 Network Security What Is Network Security And How Does It Work
Network Security What Is Network Security And How Does It WorkThis slide defines the meaning of network security and how it helps to prevent data through different methods and techniques. Increase audience engagement and knowledge by dispensing information using Network Security What Is Network Security And How Does It Work. This template helps you present information on five stages. You can also present information on Approach, Methods, Techniques, Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Network Security Ppt layout
Table Of Contents For Network Security Ppt layoutIntroducing Table Of Contents For Network Security Ppt layout to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Security, Implementation, Network, Budget, using this template. Grab it now to reap its full benefits.
-
 Pillars Of Cloud Security Network Security Cloud Data Protection
Pillars Of Cloud Security Network Security Cloud Data ProtectionThis slide defines the network security pillar of cloud security and what precautions are taken to protect networks from attacks. Introducing Pillars Of Cloud Security Network Security Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Micro Segmentation, Operations, Security, using this template. Grab it now to reap its full benefits.
-
 Network Security Risks In Powerpoint And Google Slides Cpb
Network Security Risks In Powerpoint And Google Slides CpbPresenting Network Security Risks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Network Security Risks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security Gateway For Extranet Network Application Icon
Security Gateway For Extranet Network Application IconIntroducing our premium set of slides with Security Gateway For Extranet Network Application Icon. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Gateway, Network Application Icon. So download instantly and tailor it with your information.
-
 Security Peer Computer Network In Powerpoint And Google Slides Cpb
Security Peer Computer Network In Powerpoint And Google Slides CpbPresenting our Security Peer Computer Network In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Peer Computer Network This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Network Cloud Computing Security Analysis Icon
Network Cloud Computing Security Analysis IconPresenting our set of slides with Network Cloud Computing Security Analysis Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network, Cloud Computing, Security Analysis Icon
-
 Maintain Security Internal Network In Powerpoint And Google Slides Cpb
Maintain Security Internal Network In Powerpoint And Google Slides CpbPresenting our Maintain Security Internal Network In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Maintain Security Internal Network. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Network Security Methodologies In Powerpoint And Google Slides Cpb
Network Security Methodologies In Powerpoint And Google Slides CpbPresenting Network Security Methodologies In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Network Security Methodologies. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Server Network Security In Powerpoint And Google Slides Cpb
Server Network Security In Powerpoint And Google Slides CpbPresenting Server Network Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Server Network Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Various Kpi For Tracking Network Security
Various Kpi For Tracking Network SecurityThis slide showcases key performance indicators for detecting network security. The main purpose of this template is enhancing protection and performance of network. This includes total security incidents, employee interaction, and cost per incidents Presenting our set of slides with Various Kpi For Tracking Network Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Total Security Incidents, Cost Per Incident.
-
 Cloud Network Security Development Icon
Cloud Network Security Development IconIntroducing our premium set of slides with Cloud Network Security Development Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Network Security Development. So download instantly and tailor it with your information.
-
 Security Measures For Protecting Wireless Networks
Security Measures For Protecting Wireless NetworksThis slide highlights security methods for wireless network protection. The purpose of this slide is to establish security tactics for protecting data transmission and functioning seamlessly in interconnected world. It includes elements such as encryption, firewall, etc. Introducing our premium set of slides with Security Measures For Protecting Wireless Networks. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Intrusion Detection, Regular Firmware Updates. So download instantly and tailor it with your information.
-
 How Does Secure Blockchain Network Operates Complete Guide To Understand BCT SS
How Does Secure Blockchain Network Operates Complete Guide To Understand BCT SSThis slide covers steps to increase operational security of blockchain networks. It includes steps such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Introducing How Does Secure Blockchain Network Operates Complete Guide To Understand BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Representing The Transaction, Network Nodes, Transaction Is Performed using this template. Grab it now to reap its full benefits.
-
 Establish Digital Transformation Network Icon For Cloud Security
Establish Digital Transformation Network Icon For Cloud SecurityPresenting our set of slides with Establish Digital Transformation Network Icon For Cloud Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Digital Transformation, Network Cloud Security.
-
 Secure Access Service Edge Architecture Characteristics SASE Network Security
Secure Access Service Edge Architecture Characteristics SASE Network SecurityThis slide represents the architectural characteristics of a secure access service edge. The purpose of this slide is to showcase the features of SASE architecture that include identity driven, cloud native, support for all edges, and global distribution. Introducing Secure Access Service Edge Architecture Characteristics SASE Network Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Native, Support, Globally, using this template. Grab it now to reap its full benefits.
-
 Secure Access Service Edge Use Cases SASE Network Security
Secure Access Service Edge Use Cases SASE Network SecurityThis slide represents the use cases of secure access service edge within an organization. The purpose of this slide is to demonstrate the various use cases of the SASE model, including rapid response to network demand, support for IoT and edge computing, VPN replacement, performance assurance and so on. Increase audience engagement and knowledge by dispensing information using Secure Access Service Edge Use Cases SASE Network Security. This template helps you present information on six stages. You can also present information on Network, Computing, Replacement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Challenges And Potential Solutions To Manage Network Security
Challenges And Potential Solutions To Manage Network SecurityThis slide showcases the challenges and pote ntial solutions to manage network security which helps an organization to align and continuously adjust their activities. It include details such as access control, antivirus software, application security. Presenting our set of slides with Challenges And Potential Solutions To Manage Network Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Access Control, Antivirus Software, Application Security.
-
 Key Elements Of Network Security Management
Key Elements Of Network Security ManagementThis slide showcases the key elements of network security management which helps an organization to analyze data and dive deep into the insights of particular devices. It include details such as policy, enforcement, auditing. Presenting our set of slides with Key Elements Of Network Security Management. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Policy, Enforcement, Auditing.
-
 Parameters To Secure Network Security Management System
Parameters To Secure Network Security Management SystemThis slide showcases the safe security management system parameters which helps an organization to protect critical data and prevents unauthorized access to applications. It include details such as control removable media, smartly surf webpages, etc. Presenting our set of slides with Parameters To Secure Network Security Management System. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Control Removable Media, Smartly Surf Webpages, Ensure Time Backups.
-
 Potential Benefits Of Network Security Management
Potential Benefits Of Network Security ManagementThis slide showcases the potential benefits of network security management which helps an organization to provide centralized solutions to ensure making simpler updates. It include details such as threat tracking, data recovery, etc. Introducing our premium set of slides with Potential Benefits Of Network Security Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Robust Endpoint Security, Effective Security Compliance, Threat Tracking. So download instantly and tailor it with your information.
-
 Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Introducing Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Direct Sybil Attack, Indirect Sybil Attack, using this template. Grab it now to reap its full benefits.
-
 Establish Effective Internet Security Protocols In Network Layer
Establish Effective Internet Security Protocols In Network LayerThis slide exhibits network layer security architecture for providing virtual private network between two locations. It includes protocols such as encapsulating security payload, authentication header and internet key exchange. Presenting our set of slides with Establish Effective Internet Security Protocols In Network Layer. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication Header, Authentication Methods, Encapsulating Security Payload.
-
 Agenda For Ethical Hacking And Network Security Ppt Icon Master Slide
Agenda For Ethical Hacking And Network Security Ppt Icon Master SlideIntroducing Agenda For Ethical Hacking And Network Security Ppt Icon Master Slide to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Ethical Hacking, Network Security, Ethical Hacking Training Program, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Ethical Hacking Phase 2 Scanning
Ethical Hacking And Network Security Ethical Hacking Phase 2 ScanningThis slide describes the scanning phase of ethical hacking, and the four types of scans are running in this phase such as pre-attack, port scanning, vulnerability scanning, and data extraction. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Ethical Hacking Phase 2 Scanning. This template helps you present information on five stages. You can also present information on Scanning Phase Of Ethical Hacking, Port Scanning, Vulnerability Scanning, Data Extraction using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security Ethical Hacking Phase 5 Clearing Tracks
Ethical Hacking And Network Security Ethical Hacking Phase 5 Clearing TracksThis slide depicts the clearing tracks phase of ethical hacking and how experienced hackers remove their traces from the system so that no one can follow them. Introducing Ethical Hacking And Network Security Ethical Hacking Phase 5 Clearing Tracks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Delete The Cache And Cookies, Changing Registry Values, Getting Rid Of Sent Emails, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Ethical Hacking Vs Penetration Testing
Ethical Hacking And Network Security Ethical Hacking Vs Penetration TestingThis slide depicts a comparison between ethical hacking and penetration testing based on required skills, time is taken to complete paperwork, and so on. Introducing Ethical Hacking And Network Security Ethical Hacking Vs Penetration Testing to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Ethical Hacking, Penetration Testing, Extensive Paperwork, Mandatory Ethical Hacking Certification, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Five Phases Of Ethical Hacking
Ethical Hacking And Network Security Five Phases Of Ethical HackingThis slide represents the five phases of ethical hacking such as reconnaissance, scanning, gaining access, maintaining access, and clearing the track of system hacking. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Five Phases Of Ethical Hacking. This template helps you present information on five stages. You can also present information on Reconnaissance, Scanning, Maintaining Access, Clearing Track using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security For Table Of Contents Ppt Icon Graphics Pictures
Ethical Hacking And Network Security For Table Of Contents Ppt Icon Graphics PicturesIntroducing Ethical Hacking And Network Security For Table Of Contents Ppt Icon Graphics Pictures to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Reconnaissance, Ethical Hacking, Scanning, Gaining Access, Maintaining Access, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Fundamental Concepts Of Ethical Hacking
Ethical Hacking And Network Security Fundamental Concepts Of Ethical HackingThis slide represents the fundamental concepts of ethical hacking, such as staying legal, defining the scope, reporting vulnerabilities, and respecting data sensitivity. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Fundamental Concepts Of Ethical Hacking. This template helps you present information on four stages. You can also present information on Fundamental Concepts, Ethical Hacking, Staying Legal, Reporting Vulnerabilities, Respecting Data Sensitivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security Key Vulnerabilities That Ethical Hackers Check
Ethical Hacking And Network Security Key Vulnerabilities That Ethical Hackers CheckThis slide describes the critical vulnerabilities that ethical hackers check, such as injection attacks, modification in security configuration, exposure of critical information, and so on. Introducing Ethical Hacking And Network Security Key Vulnerabilities That Ethical Hackers Check to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Modification In Security Configurations, Exposure Of Critical Information, Authentication Standard Breach, Ethical Hackers Check, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Need For Ethical Hacking
Ethical Hacking And Network Security Need For Ethical HackingThis slide depicts the reasons to describe the need for ethical hacking, including identification and correction of security flaws, aid in development and quality control, and evaluation of the company security and regulatory compliance. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Need For Ethical Hacking. This template helps you present information on three stages. You can also present information on Identifying And Correcting Security Flaws, Development And Quality Control, Security And Regulatory Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security Netsparker Ethical Hacking Tool
Ethical Hacking And Network Security Netsparker Ethical Hacking ToolThis slide depicts the Netsparker tool used for ethical hacking and its features such as less configuration, proof-based scanning, smooth interface, and so on. Introducing Ethical Hacking And Network Security Netsparker Ethical Hacking Tool to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Ethical Hacking, Less Configuration, Proof Based Scanning, Smooth Interface, Simple Online Application, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Roles And Responsibilities Of Ethical Hacker
Ethical Hacking And Network Security Roles And Responsibilities Of Ethical HackerThis slide depicts the roles and responsibilities of ethical hackers, including preventing future attacks by recognizing open ports, repairing the vulnerabilities of the system, etc. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Roles And Responsibilities Of Ethical Hacker. This template helps you present information on five stages. You can also present information on Roles And Responsibilities, Ethical Hacker, Vulnerabilities Of The System, Preventing Future Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security Some Limitations Of Ethical Hacking
Ethical Hacking And Network Security Some Limitations Of Ethical HackingIntroducing Ethical Hacking And Network Security Some Limitations Of Ethical Hacking to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Resource Constraints, Restricted Methods, Ethical Hacking, Computing Power And Funding, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Techniques Used In Ethical Hacking
Ethical Hacking And Network Security Techniques Used In Ethical HackingThis slide represents the techniques of ethical hacking such as port scanning, analyzing and sniffing network traffic, detection of SQL injections, an inspection of patch installation. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Techniques Used In Ethical Hacking. This template helps you present information on six stages. You can also present information on Techniques Of Ethical Hacking, Port Scanning, Sniffing Network Traffic, Patch Installation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security What Is Ethical Hacking
Ethical Hacking And Network Security What Is Ethical HackingThis slide depicts ethical hacking and how ethical hackers could be an asset to a company that can prevent malicious attacks on a computer system or network. Introducing Ethical Hacking And Network Security What Is Ethical Hacking to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security Professionals, Security Flaws, Ethical Hacking, Computer System, Application, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security What Is Hacking Ppt Icon Format Ideas
Ethical Hacking And Network Security What Is Hacking Ppt Icon Format IdeasThis slide illustrates what hacking is and how businesses are getting affected by it every year, and to prevent this, they hire white hat hackers or ethical hackers. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security What Is Hacking Ppt Icon Format Ideas. This template helps you present information on five stages. You can also present information on Computer System Or Network, Circumvent Security, Personal Or Corporate Data, Password Cracking Technique using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security What Is Phishing Attack
Ethical Hacking And Network Security What Is Phishing AttackThis slide represents what phishing attacks are and how phishers hoax people through emails, SMS, phone calls, and social media platforms. Introducing Ethical Hacking And Network Security What Is Phishing Attack to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Phishers Hoax, Social Media Platforms, System Hacking, Corporate Or Personal Data, using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Table Of Contents
Firewall Network Security Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Firewall Network Security Table Of Contents This template helps you present information on One stages. You can also present information on Next Generation Firewall, Network Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Working Functions Of Cloud Firewall System
Firewall Network Security Working Functions Of Cloud Firewall SystemThis slide talks about the different working functions that help cloud-based firewall systems to protect the user network and devices from malicious activities. The purpose of this slide is to showcase the various tasks of cloud firewalls, including packet filtering, stateful inspection, and proxy service. Introducing Firewall Network Security Working Functions Of Cloud Firewall System to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Stateful Inspection, Proxy Service, Packet Filtering using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Working Of Next Generation Firewall Systems
Firewall Network Security Working Of Next Generation Firewall SystemsThis slide gives architectures of traditional firewalls and Next Generation Firewall systems, including their working. The purpose of this slide is to showcase how Next Generation Firewall works in comparison with conventional firewall systems. Introducing Firewall Network Security Working Of Next Generation Firewall Systems to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Traffic, Reaches A Network, Security Posture using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security About Distributed Firewall Overview Features And Benefits
Firewall Network Security About Distributed Firewall Overview Features And BenefitsThis slide gives an overview of distributed firewalls, including their features. It also includes the architecture and advantages of distributed firewall systems, such as protection from insider attacks, intrusion detection, and service exposure and port scanning. Introducing Firewall Network Security About Distributed Firewall Overview Features And Benefits to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Have Become Blockages, Unauthorized Infiltration using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security About Firewall Introduction Benefits And Types
Firewall Network Security About Firewall Introduction Benefits And TypesThis slide gives an overview of firewalls, including their introduction, benefits, and various types. The purpose of this slide is to introduce firewalls, and their different types, such as host-based firewalls and network-based firewalls. It also includes the graphical representation of firewall placement between public and private networks. Introducing Firewall Network Security About Firewall Introduction Benefits And Types to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on External Networks, Benefits And Types using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Key Factors To Contribute Firewall Failures
Firewall Network Security Key Factors To Contribute Firewall FailuresThis slide describes the prominent causes of firewall system failures. The purpose of this slide is to showcase the four main factors that contribute the firewall failures, such as misconfiguration, software vulnerabilities, missing firewall policy, and hardware bottlenecks. Introducing Firewall Network Security Key Factors To Contribute Firewall Failures to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Protect The Firewall, Firewall Configuration Testing using this template. Grab it now to reap its full benefits.
-
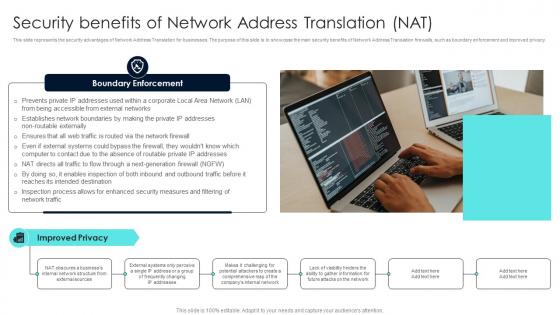 Firewall Network Security Security Benefits Of Network Address Translation NAT
Firewall Network Security Security Benefits Of Network Address Translation NATThis slide represents the security advantages of Network Address Translation for businesses. The purpose of this slide is to showcase the main security benefits of Network Address Translation firewalls, such as boundary enforcement and improved privacy. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Security Benefits Of Network Address Translation NAT This template helps you present information on One stages. You can also present information on Packet Filtering Router, Screened Host Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policies Safeguarding Network Infrastructure
Cyber Security Policies Safeguarding Network InfrastructureThis slide covers essential security policies. The purpose of this template is to provide a comprehensive overview of essential IT security policies, including Program, Issue-Specific, and System-Specific policies. Presenting our set of slides with Cyber Security Policies Safeguarding Network Infrastructure This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Program Policy, System-Specific Policy
-
 Use IoT Cryptographic Network Protocols Internet Of Things IoT Security Cybersecurity SS
Use IoT Cryptographic Network Protocols Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of cryptographic network protocols for internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about secure connectivity, updates, etc. Increase audience engagement and knowledge by dispensing information using Use IoT Cryptographic Network Protocols Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on three stages. You can also present information on Secure Connectivity, Network Protocols Usage, Continuous Updates, Cryptographic Network Protocols using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Technology Stack Icon
Network Security Technology Stack IconIntroducing our premium set of slides with name Network Security Technology Stack Icon Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Security Technology Stack Icon. So download instantly and tailor it with your information.
-
 ATP Cyber Network Security Icon
ATP Cyber Network Security IconPresenting our set of slides with name ATP Cyber Network Security Icon. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on ATP Cyber Network, Security Icon.
-
 Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SS
Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SSThis slide showcases the Wi-Fi security to protect network and connected devices. It includes strategies such as strong passwords, encryption, firewall and intrusion detection systems IDS and two-factor authentication 2FA.Introducing Wi Fi Security To Protect Network And Connected Devices Strategic Guide To Implement Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Two Factor Authentication, Intrusion Detection Systems, Encryption, Strong Passwords, using this template. Grab it now to reap its full benefits.
-
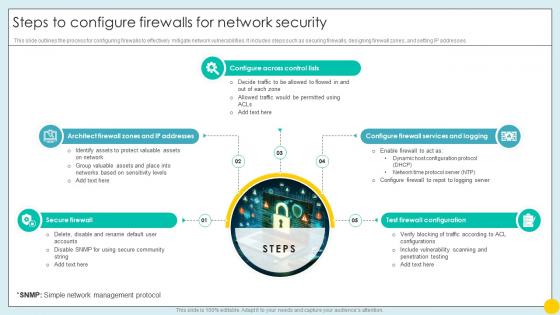 Steps To Configure Firewalls For Network Security Implementing Strategies For Mitigating Cybersecurity SS
Steps To Configure Firewalls For Network Security Implementing Strategies For Mitigating Cybersecurity SSThis slide outlines the process for configuring firewalls to effectively mitigate network vulnerabilities. It includes steps such as securing firewalls, designing firewall zones, and setting IP addresses.Increase audience engagement and knowledge by dispensing information using Steps To Configure Firewalls For Network Security Implementing Strategies For Mitigating Cybersecurity SS. This template helps you present information on five stages. You can also present information on Secure Firewall, Configure Across Control Lists, Test Firewall Configuration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



