Powerpoint Templates and Google slides for Secure Endpoints
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Business endpoint security ppt powerpoint presentation pictures example introduction cpb
Business endpoint security ppt powerpoint presentation pictures example introduction cpbPresenting this set of slides with name - Business Endpoint Security Ppt Powerpoint Presentation Pictures Example Introduction Cpb. This is an editable five stages graphic that deals with topics like Business Endpoint Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Endpoint security platform ppt powerpoint presentation portfolio gallery cpb
Endpoint security platform ppt powerpoint presentation portfolio gallery cpbPresenting this set of slides with name Endpoint Security Platform Ppt Powerpoint Presentation Portfolio Gallery Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Endpoint Security Platform to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Elements endpoint security ppt powerpoint presentation layouts layout ideas cpb
Elements endpoint security ppt powerpoint presentation layouts layout ideas cpbPresenting this set of slides with name Elements Endpoint Security Ppt Powerpoint Presentation Layouts Layout Ideas Cpb. This is an editable Powerpoint nine stages graphic that deals with topics like Elements Endpoint Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Endpoint security threats ppt powerpoint presentation pictures templates cpb
Endpoint security threats ppt powerpoint presentation pictures templates cpbPresenting this set of slides with name Endpoint Security Threats Ppt Powerpoint Presentation Pictures Templates Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Endpoint Security Threats to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Difference endpoint network security ppt powerpoint presentation inspiration clipart cpb
Difference endpoint network security ppt powerpoint presentation inspiration clipart cpbPresenting this set of slides with name Difference Endpoint Network Security Ppt Powerpoint Presentation Inspiration Clipart Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Difference Endpoint Network Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Endpoint security platform ppt powerpoint presentation inspiration samples cpb
Endpoint security platform ppt powerpoint presentation inspiration samples cpbPresenting this set of slides with name Endpoint Security Platform Ppt Powerpoint Presentation Inspiration Samples Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Endpoint Security Platform to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Unified endpoint security ppt powerpoint presentation gallery inspiration cpb
Unified endpoint security ppt powerpoint presentation gallery inspiration cpbPresenting this set of slides with name Unified Endpoint Security Ppt Powerpoint Presentation Gallery Inspiration Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Unified Endpoint Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Unified endpoint security ppt powerpoint presentation summary sample cpb
Unified endpoint security ppt powerpoint presentation summary sample cpbPresenting this set of slides with name Unified Endpoint Security Ppt Powerpoint Presentation Summary Sample Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Unified Endpoint Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Types endpoint security ppt powerpoint presentation layouts templates cpb
Types endpoint security ppt powerpoint presentation layouts templates cpbPresenting Types Endpoint Security Ppt Powerpoint Presentation Layouts Templates Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Types Endpoint Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Endpoint security tools ppt powerpoint presentation gallery maker cpb
Endpoint security tools ppt powerpoint presentation gallery maker cpbPresenting Endpoint Security Tools Ppt Powerpoint Presentation Gallery Maker Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Endpoint Security Tools. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Network endpoint security ppt powerpoint presentation layouts graphics tutorials cpb
Network endpoint security ppt powerpoint presentation layouts graphics tutorials cpbPresenting our Network Endpoint Security Ppt Powerpoint Presentation Layouts Graphics Tutorials Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Network Endpoint Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Endpoint Security Antivirus Ppt Powerpoint Presentation Infographics Graphics Download Cpb
Endpoint Security Antivirus Ppt Powerpoint Presentation Infographics Graphics Download CpbPresenting Endpoint Security Antivirus Ppt Powerpoint Presentation Infographics Graphics Download Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Endpoint Security Antivirus. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Addressing Mobile Device Management Model For Enterprise Unified Endpoint Security
Addressing Mobile Device Management Model For Enterprise Unified Endpoint SecurityThis slide provides information regarding various mobile device management models such as BYOD, COPE, COBO, COSU that can be selected by vendor based on requirement. Increase audience engagement and knowledge by dispensing information using Addressing Mobile Device Management Model For Enterprise Unified Endpoint Security. This template helps you present information on four stages. You can also present information on Equipment Personal, Devices Professional, Employees Personal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing Staff Training Schedule With Cost Unified Endpoint Security
Addressing Staff Training Schedule With Cost Unified Endpoint SecurityThe employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Introducing Addressing Staff Training Schedule With Cost Unified Endpoint Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Advanced Software, Fundamentals Information, Threat Vulnerability, using this template. Grab it now to reap its full benefits.
-
 Determine Current Scenario Of Unified Endpoint Security
Determine Current Scenario Of Unified Endpoint SecurityThis slide covers details regarding the current scenario of mobile devices usage at workplace with mobile device usage frequency per day, employees considering tablet PCs as personal and work device. Present the topic in a bit more detail with this Determine Current Scenario Of Unified Endpoint Security. Use it as a tool for discussion and navigation on Determine Frequency, Employees Consider, Employee Consider. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine Standard Mobile Device Management Components Unified Endpoint Security
Determine Standard Mobile Device Management Components Unified Endpoint SecurityThis slide provides information regarding essential standard mobile device management components terms of central management console, registry.Increase audience engagement and knowledge by dispensing information using Determine Standard Mobile Device Management Components Unified Endpoint Security. This template helps you present information on two stages. You can also present information on Components Comprise, Devices Workplace, Provide Performance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine Various Configuration Profiles Using MDM Technology Unified Endpoint Security
Determine Various Configuration Profiles Using MDM Technology Unified Endpoint SecurityThis slide provides information regarding various configuration profiles using MDM technology such as basics, email accounts, internet and additional settings. Present the topic in a bit more detail with this Determine Various Configuration Profiles Using MDM Technology Unified Endpoint Security. Use it as a tool for discussion and navigation on Internet Settings, Processes Configuration, Profile Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determining Roles And Responsibilities For Risk Handling Unified Endpoint Security
Determining Roles And Responsibilities For Risk Handling Unified Endpoint SecurityThis slide provides information regarding the roles and responsibilities of management in handling mobile device security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers. Introducing Determining Roles And Responsibilities For Risk Handling Unified Endpoint Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Chief Information, Executive Management, Development Implementation, using this template. Grab it now to reap its full benefits.
-
 Ensuring Mobile Device Compliance And Policy Enforcement Unified Endpoint Security
Ensuring Mobile Device Compliance And Policy Enforcement Unified Endpoint SecurityThis slide provides information regarding mobile device compliance and policy enforcement with automated device setup, dynamic workflows and policies, etc.Increase audience engagement and knowledge by dispensing information using Ensuring Mobile Device Compliance And Policy Enforcement Unified Endpoint Security. This template helps you present information on three stages. You can also present information on Enforcement Automation, Dynamic Workflows, Device Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slides For Unified Endpoint Security Management
Icons Slides For Unified Endpoint Security ManagementPresenting our premium Icons Slides For Unified Endpoint Security Management set of slides with flexible icons. The icons are designed by our group of professionals. Add these Icons Slides For Unified Endpoint Security Management to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
 Implementing Mobile Device Security Framework Roadmap Unified Endpoint Security
Implementing Mobile Device Security Framework Roadmap Unified Endpoint SecurityThis slide portrays information regarding optimization of current mobile device security framework. The IT department will require to fulfill crucial activities in specific timeframe. Deliver an outstanding presentation on the topic using this Implementing Mobile Device Security Framework Roadmap Unified Endpoint Security. Dispense information and present a thorough explanation of Control Environment, Security Processes, Security Program using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Mobile Device Management Action Plan Unified Endpoint Security
Mobile Device Management Action Plan Unified Endpoint SecurityThe risk management action plan will help in keeping the track of various potential risks that are existing in the firm in context to mobile device management. The person responsible in handling the risk will keep track of the duration in which risk is resolved.Deliver an outstanding presentation on the topic using this Mobile Device Management Action Plan Unified Endpoint Security. Dispense information and present a thorough explanation of Compliance Obligations, Develop Implement, Implement Receivables using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
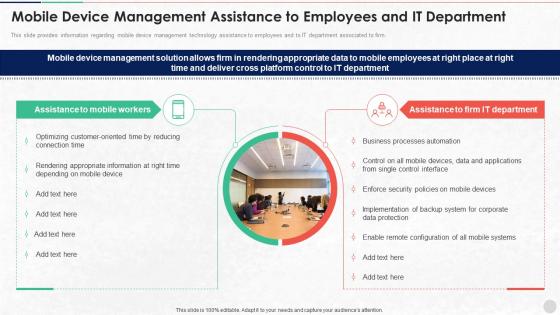 Mobile Device Management Assistance To Employees Unified Endpoint Security
Mobile Device Management Assistance To Employees Unified Endpoint SecurityThis slide provides information regarding mobile device management technology assistance to employees and to IT department associated to firm. Introducing Mobile Device Management Assistance To Employees Unified Endpoint Security to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Rendering Appropriate, Processes Automation, Enforce Security, using this template. Grab it now to reap its full benefits.
-
 Mobile Device Management For Android Platform Unified Endpoint Security
Mobile Device Management For Android Platform Unified Endpoint SecurityThe risk management action plan will help in keeping the track of various potential risks that are existing in the firm in context to mobile device management. The person responsible in handling the risk will keep track of the duration in which risk is resolved.Present the topic in a bit more detail with this Mobile Device Management For Android Platform Unified Endpoint Security. Use it as a tool for discussion and navigation on Device Security, Remote Management, Mandatary Installed. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Selecting Suitable Mobile Device Management Solutions Unified Endpoint Security
Selecting Suitable Mobile Device Management Solutions Unified Endpoint SecurityThis slide provides information regarding selection of suitable mobile device management solution with various features such as user self registration, remote lock, remote wipe, mobile experience management. Deliver an outstanding presentation on the topic using this Selecting Suitable Mobile Device Management Solutions Unified Endpoint Security. Dispense information and present a thorough explanation of Experience Management, Geofencing, Platforms Supported using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents For Unified Endpoint Security Management
Table Of Contents For Unified Endpoint Security ManagementIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Unified Endpoint Security Management. This template helps you present information on one stage. You can also present information on Device Management, Policy Enforcement, Management Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
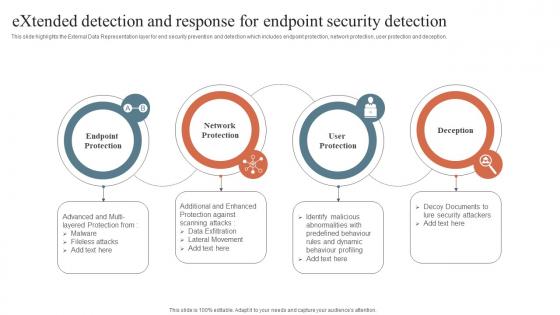 Security Orchestration Automation Extended Detection And Response For Endpoint Security Detection
Security Orchestration Automation Extended Detection And Response For Endpoint Security DetectionThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deception. Introducing Security Orchestration Automation Extended Detection And Response For Endpoint Security Detection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Protection, Endpoint Protection, User Protection, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS
Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SSThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business owned devices, and installation maintenance of operating systems.Increase audience engagement and knowledge by dispensing information using Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS. This template helps you present information on three stages. You can also present information on Such Business, Operating System, Frequent Basis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 CASB As A Streamline Endpoint Protection Solution Cloud Access Security Broker CASB
CASB As A Streamline Endpoint Protection Solution Cloud Access Security Broker CASBThis slide outlines how cloud access security broker 2.0 streamlines endpoint protection. The purpose of this slide is to showcase how CASB 2.0 improves endpoint security for streamlined deployment. It also includes the features of CASB 2.0 and endpoint security integration. Deliver an outstanding presentation on the topic using this CASB As A Streamline Endpoint Protection Solution Cloud Access Security Broker CASB. Dispense information and present a thorough explanation of Cloud Apps, Endpoint Manager, Roaming Users using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices For Effective Endpoint Security ICT Strategic Framework Strategy SS V
Best Practices For Effective Endpoint Security ICT Strategic Framework Strategy SS VThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business-owned devices, and installation maintenance of operating systems. Increase audience engagement and knowledge by dispensing information using Best Practices For Effective Endpoint Security ICT Strategic Framework Strategy SS V. This template helps you present information on three stages. You can also present information on Educate Users, Find And Track Devices, Installation And Maintenance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Contact Us For Endpoint Security Upgradation Proposal
Contact Us For Endpoint Security Upgradation ProposalIntroducing Contact Us For Endpoint Security Upgradation Proposal to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Contact Us, using this template. Grab it now to reap its full benefits.
-
 Cost Summary For Endpoint Security Upgradation Proposal
Cost Summary For Endpoint Security Upgradation ProposalThis slide represents the estimated cost of implementing a endpoint security project in an organization, the cost categories are Infrastructure, etc. Present the topic in a bit more detail with this Cost Summary For Endpoint Security Upgradation Proposal. Use it as a tool for discussion and navigation on Infrastructure Costs, Software Costs, Internet Cost, Maintenance Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Endpoint Security Upgradation Proposal Endpoint Security Case
Endpoint Security Upgradation Proposal Endpoint Security CaseThis slide highlights the overview of Hitachi consulting company, problems faced, and their related solutions in the case study. Present the topic in a bit more detail with this Endpoint Security Upgradation Proposal Endpoint Security Case. Use it as a tool for discussion and navigation on Problems, Solutions, Real-Time Visibility, Weakness In Endpoint Security Posture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Endpoint Security Upgradation Proposal Offerings For Modern Endpoint
Endpoint Security Upgradation Proposal Offerings For Modern EndpointThis slide represents the services offered by the endpoint security service provider company, including solution offer by the company and its different services. Introducing Endpoint Security Upgradation Proposal Offerings For Modern Endpoint to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Cloud-Based Management, Security Measures, Advanced Threat Detection, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Upgradation Proposal Our Process For Endpoint
Endpoint Security Upgradation Proposal Our Process For EndpointThis slide discusses the key steps for implementing the endpoint security for an organization, these are find known malicious activities, remove privileges, etc. Introducing Endpoint Security Upgradation Proposal Our Process For Endpoint to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Activities, Sensible Application Control, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Upgradation Proposal Why Replacing Traditional
Endpoint Security Upgradation Proposal Why Replacing TraditionalThis slide gives an overview of why organizations need to replace their traditional endpoint security with modern endpoint security. Introducing Endpoint Security Upgradation Proposal Why Replacing Traditional to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Advanced Threat Detection, Adaptability, Centralized Cloud-Based Management, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Endpoint Security Upgradation Proposal
Icons Slide For Endpoint Security Upgradation ProposalIntroducing our well researched set of slides titled Icons Slide For Endpoint Security Upgradation Proposal. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Next Steps For Endpoint Security Upgradation Proposal
Next Steps For Endpoint Security Upgradation ProposalThis slide covers the next step after the proposal has been accepted. It highlights the various terms that should be followed to lay a solid foundation for collaboration. Introducing Next Steps For Endpoint Security Upgradation Proposal to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Discuss Requirements And Changes, Acceptance Of Proposal, Finalization Of Proposal Signature From Parties, using this template. Grab it now to reap its full benefits.
-
 Terms And Conditions For Endpoint Security Upgradation Proposal
Terms And Conditions For Endpoint Security Upgradation ProposalThis slide illustrates terms and conditions based on which the organization will sign a contract with the agreement party which covers service and payment, etc. Introducing Terms And Conditions For Endpoint Security Upgradation Proposal to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Service And Payments, Contract Cancellation, Notice And Renewal, Liability, using this template. Grab it now to reap its full benefits.
-
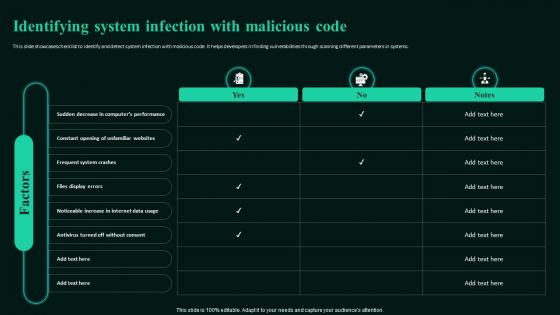 Identifying System Infection With Malicious Building Next Generation Endpoint Security Cybersecurity SS
Identifying System Infection With Malicious Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases checklist to identify and detect system infection with malicious code. It helps developers in finding vulnerabilities through scanning different parameters in systems.Deliver an outstanding presentation on the topic using this Identifying System Infection With Malicious Building Next Generation Endpoint Security Cybersecurity SS. Dispense information and present a thorough explanation of Frequent System Crashes, Files Display Errors, Unfamiliar Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Analysis Of Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS
Impact Analysis Of Endpoint Security Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases current scenario of improvements w.r.t traditional endpoint security. It includes details such as false positives, privileges, anti-virus, etc.Introducing Impact Analysis Of Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Improvements, Vulnerabilities Solved, Modern Attacks Missed, using this template. Grab it now to reap its full benefits.
-
 Least Privilege Implementation For Accidental Building Next Generation Endpoint Security Cybersecurity SS
Least Privilege Implementation For Accidental Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases implementation of least privilege principle for avoiding accidental misuses. It provides details about security controls, data discovery, etc.Deliver an outstanding presentation on the topic using this Least Privilege Implementation For Accidental Building Next Generation Endpoint Security Cybersecurity SS. Dispense information and present a thorough explanation of Action Steps, Real Problem Solved, Layering Security Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Mitigation Plan For Malicious Code Protection Building Next Generation Endpoint Security Cybersecurity SS
Mitigation Plan For Malicious Code Protection Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases mitigation plan for protection against malicious code. It can help detect malware, adware, etc. and plan action items accordingly.Present the topic in a bit more detail with this Mitigation Plan For Malicious Code Protection Building Next Generation Endpoint Security Cybersecurity SS. Use it as a tool for discussion and navigation on Malware Infection, Unauthorized Access, Adware Intrusion, Phishing Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Raci Matrix For Effective Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS
Raci Matrix For Effective Endpoint Security Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases endpoint security team responsible, accountable, consulted and informed RACI matrix. It provides details about endpoint detection and response, network security, etc.Deliver an outstanding presentation on the topic using this Raci Matrix For Effective Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS. Dispense information and present a thorough explanation of Monitor Security, Identity Strategic Risk, Perform Business Impact Assessments using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Removing Admin Rights For Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS
Removing Admin Rights For Endpoint Security Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases process to remove admin rights for increased endpoint security. It includes details about discover, analyze, remediate, etc. Introducing Removing Admin Rights For Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Analyze, Remediate, Discover, Improves Risk Mitigation, using this template. Grab it now to reap its full benefits.
-
 Siem Tool To Address Potential Security Threats Building Next Generation Endpoint Security Cybersecurity SS
Siem Tool To Address Potential Security Threats Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases security information and event management SIEM tools which can help endpoint security teams detect and address potential security threats.Present the topic in a bit more detail with this Siem Tool To Address Potential Security Threats Building Next Generation Endpoint Security Cybersecurity SS. Use it as a tool for discussion and navigation on Collection, Detection, Investigation, Response. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Smart Endpoint Application Control For Reduced Building Next Generation Endpoint Security Cybersecurity SS
Smart Endpoint Application Control For Reduced Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases smart endpoint app control process. It can help developers reduce attacks through blocklist rules, risk assessment, recommendation engine, etc.Deliver an outstanding presentation on the topic using this Smart Endpoint Application Control For Reduced Building Next Generation Endpoint Security Cybersecurity SS. Dispense information and present a thorough explanation of Symantec Application Control, Symantec Application Control, Recommendation Engine using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



