Powerpoint Templates and Google slides for Secure Endpoints
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Endpoint security threats ppt powerpoint presentation pictures templates cpb
Endpoint security threats ppt powerpoint presentation pictures templates cpbPresenting this set of slides with name Endpoint Security Threats Ppt Powerpoint Presentation Pictures Templates Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Endpoint Security Threats to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Difference endpoint network security ppt powerpoint presentation inspiration clipart cpb
Difference endpoint network security ppt powerpoint presentation inspiration clipart cpbPresenting this set of slides with name Difference Endpoint Network Security Ppt Powerpoint Presentation Inspiration Clipart Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Difference Endpoint Network Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Endpoint security management ppt powerpoint presentation gallery deck cpb
Endpoint security management ppt powerpoint presentation gallery deck cpbPresenting this set of slides with name Endpoint Security Management Ppt Powerpoint Presentation Gallery Deck Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Endpoint Security Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Unified endpoint security ppt powerpoint presentation gallery inspiration cpb
Unified endpoint security ppt powerpoint presentation gallery inspiration cpbPresenting this set of slides with name Unified Endpoint Security Ppt Powerpoint Presentation Gallery Inspiration Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Unified Endpoint Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Unified endpoint security ppt powerpoint presentation summary sample cpb
Unified endpoint security ppt powerpoint presentation summary sample cpbPresenting this set of slides with name Unified Endpoint Security Ppt Powerpoint Presentation Summary Sample Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Unified Endpoint Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Types endpoint security ppt powerpoint presentation layouts templates cpb
Types endpoint security ppt powerpoint presentation layouts templates cpbPresenting Types Endpoint Security Ppt Powerpoint Presentation Layouts Templates Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Types Endpoint Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Endpoint security tools ppt powerpoint presentation gallery maker cpb
Endpoint security tools ppt powerpoint presentation gallery maker cpbPresenting Endpoint Security Tools Ppt Powerpoint Presentation Gallery Maker Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Endpoint Security Tools. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Network endpoint security ppt powerpoint presentation layouts graphics tutorials cpb
Network endpoint security ppt powerpoint presentation layouts graphics tutorials cpbPresenting our Network Endpoint Security Ppt Powerpoint Presentation Layouts Graphics Tutorials Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Network Endpoint Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Endpoint security controls checklist ppt powerpoint presentation infographic template cpb
Endpoint security controls checklist ppt powerpoint presentation infographic template cpbPresenting our Endpoint Security Controls Checklist Ppt Powerpoint Presentation Infographic Template Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Endpoint Security Controls Checklist This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Endpoint Security Antivirus Ppt Powerpoint Presentation Infographics Graphics Download Cpb
Endpoint Security Antivirus Ppt Powerpoint Presentation Infographics Graphics Download CpbPresenting Endpoint Security Antivirus Ppt Powerpoint Presentation Infographics Graphics Download Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Endpoint Security Antivirus. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
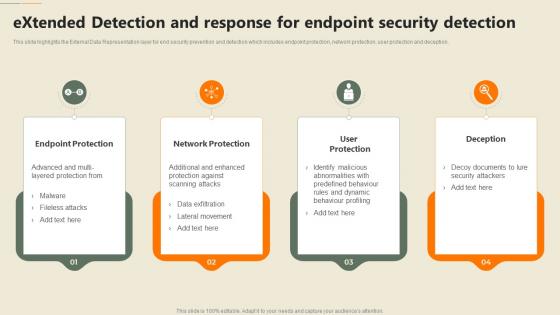 Extended Detection And Response For Endpoint Security Detection Security Automation In Information Technology
Extended Detection And Response For Endpoint Security Detection Security Automation In Information TechnologyThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deception. Increase audience engagement and knowledge by dispensing information using Extended Detection And Response For Endpoint Security Detection Security Automation In Information Technology. This template helps you present information on four stages. You can also present information on Endpoint Protection, Network Protection, Deception using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
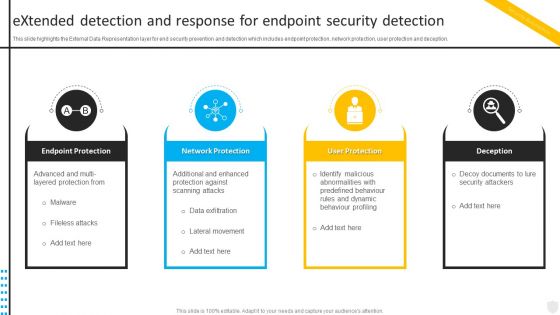 Extended Detection And Response For Endpoint Security Automation To Investigate And Remediate Cyberthreats
Extended Detection And Response For Endpoint Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deception. Introducing Extended Detection And Response For Endpoint Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Endpoint Protection, Network Protection, User Protection, using this template. Grab it now to reap its full benefits.
-
 Key Steps Involved In Mobile Device Management Deployment Unified Endpoint Security
Key Steps Involved In Mobile Device Management Deployment Unified Endpoint SecurityThis slide provides information regarding key steps involved in deploying mobile device management system. Increase audience engagement and knowledge by dispensing information using Key Steps Involved In Mobile Device Management Deployment Unified Endpoint Security. This template helps you present information on five stages. You can also present information on Profile Configuration, Device Enrollment, Successful Configuration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS
Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SSThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business owned devices, and installation maintenance of operating systems.Increase audience engagement and knowledge by dispensing information using Best Practices For Effective Endpoint Security Implementation Of ICT Strategic Plan Strategy SS. This template helps you present information on three stages. You can also present information on Such Business, Operating System, Frequent Basis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices For Effective Endpoint Security Delivering ICT Services For Enhanced Business Strategy SS V
Best Practices For Effective Endpoint Security Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business-owned devices, and installation maintenance of operating systems. Increase audience engagement and knowledge by dispensing information using Best Practices For Effective Endpoint Security Delivering ICT Services For Enhanced Business Strategy SS V. This template helps you present information on three stages. You can also present information on Educate Users, Find And Track Devices, Operating System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies To Ensure Endpoint Cyber Security
Strategies To Ensure Endpoint Cyber SecurityThis slide covers common endpoint cyber security risks and various strategies to minimize threat effects. The purpose of this slide is to assist businesses in overcoming compliance vulnerabilities and security risks. It includes strategies such as outdated patches, phishing attacks, software vulnerabilities exploits, etc. Presenting our set of slides with Strategies To Ensure Endpoint Cyber Security This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Track Connected Devices, Strategies, Manage USB Port Access
-
 Endpoint Security Approaches To Implement Effective Endpoint Security
Endpoint Security Approaches To Implement Effective Endpoint SecurityThis slide showcases the techniques of deploying effective endpoint security which include on-location, cloud, hybrid endpoint security, etc. Introducing Endpoint Security Approaches To Implement Effective Endpoint Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Agent Based Security, Remote Device Connection, Effective Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Emerging Trends And Technologies In Endpoint Security
Endpoint Security Emerging Trends And Technologies In Endpoint SecurityThis slide outlines the technologies and trends in end point security with involvement of technologies such as Artificial Intelligence AI, ML, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Emerging Trends And Technologies In Endpoint Security. This template helps you present information on four stages. You can also present information on Emerging Trends, Technologies In Endpoint Security, Artificial Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Functions Of Firewall In Endpoint Security Solutions
Endpoint Security Functions Of Firewall In Endpoint Security SolutionsThis slide represents the objectives of second component of endpoint security that is firewall which is used to monitor traffic of devices. Increase audience engagement and knowledge by dispensing information using Endpoint Security Functions Of Firewall In Endpoint Security Solutions. This template helps you present information on six stages. You can also present information on Decides Traffic Allowance, Creates Network Barrier, Applies Security Rules, Monitors Traffic using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Goals Of Device Control In Endpoint Security
Endpoint Security Goals Of Device Control In Endpoint SecurityThis slide represents the objectives of one of the components of endpoint security which is device control technique to strengthens secure endpoint. Introducing Endpoint Security Goals Of Device Control In Endpoint Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Customizable Device Access Rules, Goals Of Device Control, Endpoint Security, Strengthens Secure Endpoint, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Key Types Of Endpoint Security Risks
Endpoint Security Key Types Of Endpoint Security RisksThis slide highlights the various types of endpoint security risks such as phishing, device loss, outdated patches, malware ads, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Key Types Of Endpoint Security Risks. This template helps you present information on seven stages. You can also present information on Device Loss, Outdated Patches, Drive By Download, Ransomware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Major Types Of Endpoint Security Solutions
Endpoint Security Major Types Of Endpoint Security SolutionsThis slide showcases the different techniques of endpoint security which include email gateway, network access control, browser isolation, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Major Types Of Endpoint Security Solutions. This template helps you present information on eight stages. You can also present information on Endpoint Detection And Response, Network Access Control, Email Gateway, Endpoint Security Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Objectives Of Endpoint Security Encryption Technique
Endpoint Security Objectives Of Endpoint Security Encryption TechniqueThis slide outlines the functions of encryption technique in endpoint security for safeguarding data on devices such as laptops, computers, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Objectives Of Endpoint Security Encryption Technique. This template helps you present information on six stages. You can also present information on Restricts Unauthorized Access, Protects Valuable Corporate Data, Makes Data Unreadable, Safeguards Data On Devices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Timeline For Implementing Efficient Endpoint Security
Endpoint Security Timeline For Implementing Efficient Endpoint SecurityThis slide outlines the different steps performed while deploying endpoint security, including planning phase, solution selection, etc. Introducing Endpoint Security Timeline For Implementing Efficient Endpoint Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Testing And Optimization, Solution Selection, Deployment, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Upgradation Proposal Offerings For Modern Endpoint
Endpoint Security Upgradation Proposal Offerings For Modern EndpointThis slide represents the services offered by the endpoint security service provider company, including solution offer by the company and its different services. Introducing Endpoint Security Upgradation Proposal Offerings For Modern Endpoint to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Cloud-Based Management, Security Measures, Advanced Threat Detection, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Upgradation Proposal Why Replacing Traditional
Endpoint Security Upgradation Proposal Why Replacing TraditionalThis slide gives an overview of why organizations need to replace their traditional endpoint security with modern endpoint security. Introducing Endpoint Security Upgradation Proposal Why Replacing Traditional to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Advanced Threat Detection, Adaptability, Centralized Cloud-Based Management, using this template. Grab it now to reap its full benefits.
-
 Next Steps For Endpoint Security Upgradation Proposal
Next Steps For Endpoint Security Upgradation ProposalThis slide covers the next step after the proposal has been accepted. It highlights the various terms that should be followed to lay a solid foundation for collaboration. Introducing Next Steps For Endpoint Security Upgradation Proposal to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Discuss Requirements And Changes, Acceptance Of Proposal, Finalization Of Proposal Signature From Parties, using this template. Grab it now to reap its full benefits.
-
 Introduction Of Endpoint Layer In Web Security Solution
Introduction Of Endpoint Layer In Web Security SolutionThis slide discusses the introduction of endpoint layer in web security for security of devices connected to the network. Introducing Introduction Of Endpoint Layer In Web Security Solution to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Specialized Software Is Employed, Protects The Overall Network, Secures All Devices Connected To Network, using this template. Grab it now to reap its full benefits.
-
 Endpoint Security Least Privilege Approach Building Next Generation Endpoint Security Cybersecurity SS
Endpoint Security Least Privilege Approach Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases least privilege approach for endpoint security. It includes steps such as granular access control, regular access reviews, whitelisting, etc.Introducing Endpoint Security Least Privilege Approach Building Next Generation Endpoint Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Granular Access Control, Regular Access Reviews, App Control And Whitelisting, using this template. Grab it now to reap its full benefits.
-
 Impact Analysis Of Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS
Impact Analysis Of Endpoint Security Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases current scenario of improvements w.r.t traditional endpoint security. It includes details such as false positives, privileges, anti-virus, etc.Introducing Impact Analysis Of Endpoint Security Building Next Generation Endpoint Security Cybersecurity SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Improvements, Vulnerabilities Solved, Modern Attacks Missed, using this template. Grab it now to reap its full benefits.


