Powerpoint Templates and Google slides for Secure Deployment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Ensuring Checklist For Mobile Security Deployment Contd Android Device Security Management
Ensuring Checklist For Mobile Security Deployment Contd Android Device Security ManagementThis slide provides information regarding mobile device security deployment checklist in terms of ensuring secure connections to corporate networks, prevent network based intrusion, centralized policies control and corporate directories. Introducing Ensuring Checklist For Mobile Security Deployment Contd Android Device Security Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Ensuring Checklist, Mobile Security Deployment, using this template. Grab it now to reap its full benefits.
-
 Managing Mobile Device Solutions For Workforce Ensuring Checklist For Mobile Security Deployment
Managing Mobile Device Solutions For Workforce Ensuring Checklist For Mobile Security DeploymentThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Present the topic in a bit more detail with this Managing Mobile Device Solutions For Workforce Ensuring Checklist For Mobile Security Deployment. Use it as a tool for discussion and navigation on Device Security, Protection Against, Malicious Codes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Managing Mobile Devices For Optimizing Ensuring Checklist For Mobile Security Deployment
Managing Mobile Devices For Optimizing Ensuring Checklist For Mobile Security DeploymentThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Present the topic in a bit more detail with this Managing Mobile Devices For Optimizing Ensuring Checklist For Mobile Security Deployment. Use it as a tool for discussion and navigation on Parameters, Protection, Malicious Codes, Mobile Security Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategies To Analyze Cyber Security Incidents Response Strategies Deployment
Strategies To Analyze Cyber Security Incidents Response Strategies DeploymentThis slide represents the techniques to be used by the organizations to analyze the impact of cyber security incidents on business operations. It includes strategies for analyzing cyber incidents such as profile network and systems etc. Introducing Strategies To Analyze Cyber Security Incidents Response Strategies Deployment to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Details, Strategies, Correlation, using this template. Grab it now to reap its full benefits.
-
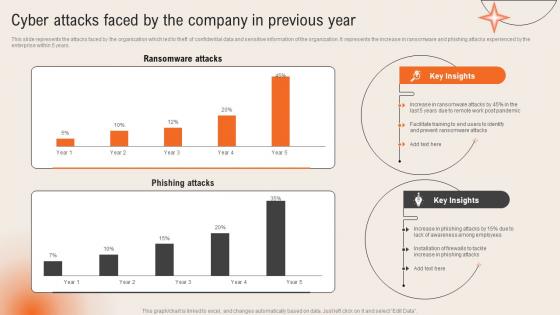 Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident Management
Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident ManagementThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years.Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Awareness Among Employees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks Management
Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks ManagementThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool name, features, trial period, cost and reviews etc. Deliver an outstanding presentation on the topic using this Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks Management. Dispense information and present a thorough explanation of Determines Suspicious, Features, Cyber Security Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ict Business Security Kpi Dashboard Comprehensive Guide For Deployment Strategy SS V
Ict Business Security Kpi Dashboard Comprehensive Guide For Deployment Strategy SS VThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents It covers details regarding issues by control type, risk categories, etc Deliver an outstanding presentation on the topic using this Ict Business Security Kpi Dashboard Comprehensive Guide For Deployment Strategy SS V Dispense information and present a thorough explanation of Risk Categories, Control Review Status, Standard Control Issues using the slides given This template can be altered and personalized to fit your needs It is also available for immediate download So grab it now
-
 Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V
Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS VThis slide represents key access security control models for organizations It includes discretionary access control, mandatory access control, role based access control and attributes based access control,Present the topic in a bit more detail with this Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Mandatory Access, Discretionary Access, Administrator Protected This template is free to edit as deemed fit for your organization Therefore download it now
-
 Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V
Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use It covers strong password authentication, data backup, network access control, etc Presenting our well structured Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V The topics discussed in this slide are Authentication Security, Most Businesses, Protect Against This is an instantly available PowerPoint presentation that can be edited conveniently Download it right away and captivate your audience
-
 Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS V
Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS VThis slide represents various types of information and communication technology ICT securities used by businesses It covers network security, endpoint security, access security, and data encryption Increase audience engagement and knowledge by dispensing information using Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS V This template helps you present information on four stages You can also present information on Network Security, End Point Security, Access Security using this PPT design This layout is completely editable so personaize it now to meet your audiences expectations
-
 Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V
Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS VThis slide represents overview of ICT information and communication technology business security It covers types and features for security such as network security, endpoint security etc Present the topic in a bit more detail with this Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Unauthorized Sources, Factor Authentication, Organizations Information This template is free to edit as deemed fit for your organization Therefore download it now
-
 Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations
Cyber Security Risk Assessment And Technology Deployment Plan To Improve OrganizationsThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations. Dispense information and present a thorough explanation of Consequences, Vulnerability, Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment
Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based DeploymentThis slide represents the benefits and drawbacks of proxy-based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy-based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment. This template helps you present information on two stages. You can also present information on Cloud Access Security Brokers, Cover Flexibility, Secure SaaS Applications, Enforcement Of Security Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment
Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB DeploymentThis slide outlines the use cases of API-based CASB deployment. This slide highlights the main use cases of API-based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment. Dispense information and present a thorough explanation of Malware In Cloud Services, Data Transfer Policies, Cloud Services, Auditing User Access Provisioning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 API Scanning CASB Deployment Model
Cloud Access Security Broker CASB V2 API Scanning CASB Deployment ModelThis slide outlines the overview of the API scanning model of CASB deployment. The purpose of this slide is to showcase its features and introduce APIs and how this deployment works. It also represents the architecture of the API scanning model and its components include mobile and corporate devices and APIs. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 API Scanning CASB Deployment Model. Use it as a tool for discussion and navigation on Corporate Devices, Facilitate Communication, Real Time Protection, Non Intrusive Security Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 CASB Deployment With Optional Components Pricing
Cloud Access Security Broker CASB V2 CASB Deployment With Optional Components PricingThis slide outlines the pricing of CASB deployment with optional or add-on components. The purpose of this slide is to showcase the pricing of additional components in CASB deployment, including data security subscription, support, threat protection subscription, data retention, and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 CASB Deployment With Optional Components Pricing. Dispense information and present a thorough explanation of Data Security Subscription, Threat Protection Subscription, Data Retention, Customer Relationship Admins using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 CASB Deployment With Standard Components Pricing
Cloud Access Security Broker CASB V2 CASB Deployment With Standard Components PricingThis slide represents the cost of CASB deployment with standard components. This slide aims to showcase the pricing of classic elements for CASB deployment in an organization. The components include visibility, compliance, threat protection, and data security with Salesforce, Box, and Office 365 environments. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 CASB Deployment With Standard Components Pricing. Use it as a tool for discussion and navigation on Pricing Of Classic Elements, Components Include Visibility, Threat Protection, Data Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use CasesThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases. This template helps you present information on two stages. You can also present information on Deploying Granular Access, Activity Controls, Detecting Shadow, IT In The Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use CasesThis slide illustrates the use cases of reverse proxy server deployment of the Cloud Access Security Broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Introducing Proxy to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Reverse Proxy Server Deployment, Cloud Access Security Broker, Reverse Proxy Deployment, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working
Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And WorkingThis slide describes the overview of the forward proxy deployment mode of the CASB model, including its working. The purpose of this slide is to showcase the working of proxy-based CASB deployment and the main components include user or clients, forward proxy, internet and origin server. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Forward Proxy Deployment Overview And Working. Use it as a tool for discussion and navigation on Deployment Overview And Working, Web Servers They Visit, Forward Proxy Method Is A Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Overview Of CASB Deployment Models
Cloud Access Security Broker CASB V2 Overview Of CASB Deployment ModelsThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Overview Of CASB Deployment Models. This template helps you present information on four stages. You can also present information on Cloud Access Security Broker, Unmanaged Gadgets, Inline Deployment, Scalable And Strong Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Primary Types Of Reverse Proxy Server Deployment
Cloud Access Security Broker CASB V2 Primary Types Of Reverse Proxy Server DeploymentThis slide outlines the main types of reverse proxy server deployment, covering regular reverse proxies and load balancers. The purpose of this slide is to showcase how both methods work to manage traffic and offer security features to organizations. Introducing Cloud Access Security Broker CASB V2 Primary Types Of Reverse Proxy Server Deployment to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Regular Reverse Proxies, Load Balancers, Proxy Server Deployment, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB Deployment
Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB DeploymentThis slide outlines the advantages and disadvantages of the API scanning Cloud Access Security Broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB Deployment. This template helps you present information on one stages. You can also present information on Cloud Access Security, Broker Deployment Model, Scanning Deployment Model, Security Policy Modifications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Proxy Based CASB Deployment Model
Cloud Access Security Broker CASB V2 Proxy Based CASB Deployment ModelThis slide outlines the overview of proxy-based CASB deployment. The purpose of this slide is to highlight the proxy-based implementation of the CASB model and it also includes the fundamental modes of proxy deployment, including forward proxy and reverse proxy. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Proxy Based CASB Deployment Model. Dispense information and present a thorough explanation of Proxy Based Implementation, Proxy Deployment, Proxy And Reverse Proxy, Operation Of Several using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker CASB V2 Steps To Deploy Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Steps To Deploy Cloud Access Security BrokerThis slide outlines the steps to implement a Cloud Access Security Broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Steps To Deploy Cloud Access Security Broker. This template helps you present information on one stages. You can also present information on Speedier Installation, Comprehensive Coverage, Cloud Access Security Broker using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices To Secure Continuous Deployment Pipeline
Best Practices To Secure Continuous Deployment PipelineThis slide represents continuous deployment pipeline best practices. It aims to conduct consistent comprehensive audits on system and code to control high level security and minimize risk of cyberattack. It includes various elements such as eliminating hardcoded credentials from tools, restricting access to non humans, etc. Presenting our set of slides with Best Practices To Secure Continuous Deployment Pipeline. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Reduce, Security, Human.
-
 Firewall Network Security Deployment Methods Of Firewall Security System
Firewall Network Security Deployment Methods Of Firewall Security SystemThis slide represents the key applications of firewall security systems. The purpose of this slide is to showcase the different deployment options of firewall security systems, such as software-based applications, hardware-based applications, and cloud-based applications. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Deployment Methods Of Firewall Security System This template helps you present information on Three stages. You can also present information on Software Based Applications, Hardware Based Applications, Cloud Based Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Deploy Cloud Access Security Broker Next Generation CASB
Steps To Deploy Cloud Access Security Broker Next Generation CASBThis slide outlines the steps to implement a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Introducing Steps To Deploy Cloud Access Security Broker Next Generation CASB to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Deployment Location, Deployment Model, Release Model using this template. Grab it now to reap its full benefits.
-
 Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SS
Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SSThis slide showcases comparative analysis for internet of things IoT security tools. It provides details about secure cryptographic key provisioning, identity, access and relationship management, IoT device provisioning, etc. Introducing Create Continuous Update And Deployment Mechanisms Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Secure Deployment, Cryptographic Protocols, Automated Security Update Deployment, Monitoring And Response Mechanisms, using this template. Grab it now to reap its full benefits.
-
 Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SS
Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of auditing and monitoring for internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about response plan, etc. Increase audience engagement and knowledge by dispensing information using Deploy Security Auditing And Monitoring Mechanisms Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on three stages. You can also present information on Auditing And Reporting, Incident Response Planning, Record Of Security Actions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Concerns And Solution For Application Security Deployment
Concerns And Solution For Application Security DeploymentThis slide outlines the problems and relevant solutions of application security deployment to ensure smooth functioning. Present the topic in a bit more detail with this Concerns And Solution For Application Security Deployment. Use it as a tool for discussion and navigation on Implement Strict Input Validation, Employ Bot Detection Mechanisms, Application Security Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Application Security Implementation Plan RACI Matrix To Deploy Application Security
Application Security Implementation Plan RACI Matrix To Deploy Application SecurityThis slide showcases a RACI matrix for application security, outlining the appropriate roles and steps to be taken during application security implementation. Present the topic in a bit more detail with this Application Security Implementation Plan RACI Matrix To Deploy Application Security. Use it as a tool for discussion and navigation on Secure Development Practices, Risk Assessment, Data Encryption, Application Security . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Application Security Implementation Plan Risks And Mitigation Strategies While Deploying Application Security
Application Security Implementation Plan Risks And Mitigation Strategies While Deploying Application SecurityThe purpose of this slide is to discuss the challenges faced while implementing application security such as data breaches, third-party risks, etc. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Risks And Mitigation Strategies While Deploying Application Security. Dispense information and present a thorough explanation of Vulnerabilities In Applications, Data Breaches, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Application Security Implementation Plan Steps For Deploying Application Security Testing
Application Security Implementation Plan Steps For Deploying Application Security TestingThis slide showcases the steps for deploying effective application security testing which include establishing test case, including security exam, etc. Introducing Application Security Implementation Plan Steps For Deploying Application Security Testing to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Execute Security Exam, Examine Outcomes, Include Security Exam, Stablish Working Test Case, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Steps For Effective Encryption Method Deployment
Application Security Implementation Plan Steps For Effective Encryption Method DeploymentThis slide highlights the steps for deploying effective encryption which include selecting appropriate algorithm, choosing correct key size, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Steps For Effective Encryption Method Deployment. This template helps you present information on six stages. You can also present information on Select Appropriate Algorithm, Select Appropriate Program, Maintain Key Security, Encryption Method Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Security Implementation Plan Steps To Deploy Efficient Access Control
Application Security Implementation Plan Steps To Deploy Efficient Access ControlThis slide discusses the process phases of implementing access control which include taking inventory of systems, examining staffs, etc. Introducing Application Security Implementation Plan Steps To Deploy Efficient Access Control to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Establish Roles, Resist Sporadic Adjustments, Examine The Staff, Take Inventory Of Systems, using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Team Structure For Application Security Deployment
Application Security Implementation Plan Team Structure For Application Security DeploymentThis slide represents the team structure for the application security in the IT infrastructure which includes manager, team lead, application security team, etc. Present the topic in a bit more detail with this Application Security Implementation Plan Team Structure For Application Security Deployment. Use it as a tool for discussion and navigation on Application Security Team, Database Management Team, Security Analyst, Malware Analyst. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Application Security Implementation Plan Timeline For Deploying Efficient Application Security
Application Security Implementation Plan Timeline For Deploying Efficient Application SecurityThis slide outlines the different steps performed while deploying application security, including planning phase, requirement gathering, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Timeline For Deploying Efficient Application Security. This template helps you present information on six stages. You can also present information on Education And Training, Patch Management, Incident Response Planning, Establish Security Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud Security
Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud SecurityThis slide represents the benefits and drawbacks of proxy-based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy-based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Increase audience engagement and knowledge by dispensing information using Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud Security. This template helps you present information on two stages. You can also present information on Proxy Based Cloud Access Security, Advantages Cover Flexibility, Proxy Based Deployment, Encrypted Connections Or Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Api Based Use Cases Of CASB Deployment CASB Cloud Security
Api Based Use Cases Of CASB Deployment CASB Cloud SecurityThis slide outlines the use cases of API-based CASB deployment. This slide highlights the main use cases of API-based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Present the topic in a bit more detail with this Api Based Use Cases Of CASB Deployment CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Services, Data Transfer Policies, Auditing User Access Provisioning. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Api Scanning CASB Deployment Model CASB Cloud Security
Api Scanning CASB Deployment Model CASB Cloud SecurityThis slide outlines the overview of the API scanning model of CASB deployment. The purpose of this slide is to showcase its features and introduce APIs and how this deployment works. It also represents the architecture of the API scanning model and its components include mobile and corporate devices and APIs. Deliver an outstanding presentation on the topic using this Api Scanning CASB Deployment Model CASB Cloud Security. Dispense information and present a thorough explanation of Deployment Works, Mobile And Corporate Devices, Submitting Queries Or Commands using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 CASB Deployment With Optional Components Pricing CASB Cloud Security
CASB Deployment With Optional Components Pricing CASB Cloud SecurityThis slide outlines the pricing of CASB deployment with optional or add-on components. The purpose of this slide is to showcase the pricing of additional components in CASB deployment, including data security subscription, support, threat protection subscription, data retention, and so on. Present the topic in a bit more detail with this CASB Deployment With Optional Components Pricing CASB Cloud Security. Use it as a tool for discussion and navigation on Threat Protection Subscription, Optional Components Pricing, Annual Pricing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 CASB Deployment With Standard Components Pricing CASB Cloud Security
CASB Deployment With Standard Components Pricing CASB Cloud SecurityThis slide represents the cost of CASB deployment with standard components. This slide aims to showcase the pricing of classic elements for CASB deployment in an organization. The components include visibility, compliance, threat protection, and data security with Salesforce, Box, and Office 365 environments. Deliver an outstanding presentation on the topic using this CASB Deployment With Standard Components Pricing CASB Cloud Security. Dispense information and present a thorough explanation of Standard Components Pricing, Data Security With Salesforce, Deployment In An Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 CASB Reverse Proxy Deployment Use Cases CASB Cloud Security
CASB Reverse Proxy Deployment Use Cases CASB Cloud SecurityThis slide illustrates the use cases of reverse proxy server deployment of the cloud access security broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Deliver an outstanding presentation on the topic using this CASB Reverse Proxy Deployment Use Cases CASB Cloud Security. Dispense information and present a thorough explanation of Enforce Access Constraints, Controlling Download Data Access, Prevent Data Exfiltration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Forward Proxy Deployment Overview And Working CASB Cloud Security
Forward Proxy Deployment Overview And Working CASB Cloud SecurityThis slide describes the overview of the forward proxy deployment mode of the CASB model, including its working. The purpose of this slide is to showcase the working of proxy-based CASB deployment and the main components include user or clients, forward proxy, internet and origin server. Increase audience engagement and knowledge by dispensing information using Forward Proxy Deployment Overview And Working CASB Cloud Security. This template helps you present information on eight stages. You can also present information on Forward Proxy Deployment, Internet And Origin Server, According To The Internet Server using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Overview Of CASB Deployment Models CASB Cloud Security
Overview Of CASB Deployment Models CASB Cloud SecurityThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out-of-band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Introducing Overview Of CASB Deployment Models CASB Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Out Of Band Deployment, Inline Deployment, Terms Of Development And Operations, using this template. Grab it now to reap its full benefits.
-
 Primary Types Of Reverse Proxy Server Deployment CASB Cloud Security
Primary Types Of Reverse Proxy Server Deployment CASB Cloud SecurityThis slide outlines the main types of reverse proxy server deployment, covering regular reverse proxies and load balancers. The purpose of this slide is to showcase how both methods work to manage traffic and offer security features to organizations. Increase audience engagement and knowledge by dispensing information using Primary Types Of Reverse Proxy Server Deployment CASB Cloud Security. This template helps you present information on two stages. You can also present information on Regular Reverse Proxies, Load Balancers, Primary Types Of Reverse, Proxy Server Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Pros And Cons Of Api Scanning CASB Deployment CASB Cloud Security
Pros And Cons Of Api Scanning CASB Deployment CASB Cloud SecurityThis slide outlines the advantages and disadvantages of the API scanning cloud access security broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Introducing Pros And Cons Of Api Scanning CASB Deployment CASB Cloud Security to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Scanning Cloud Access Security, Broker Deployment Model, Scanning Deployment Model, using this template. Grab it now to reap its full benefits.
-
 Proxy Based CASB Deployment Model CASB Cloud Security
Proxy Based CASB Deployment Model CASB Cloud SecurityThis slide outlines the overview of proxy-based CASB deployment. The purpose of this slide is to highlight the proxy-based implementation of the CASB model and it also includes the fundamental modes of proxy deployment, including forward proxy and reverse proxy. Increase audience engagement and knowledge by dispensing information using Proxy Based CASB Deployment Model CASB Cloud Security. This template helps you present information on two stages. You can also present information on Forward Proxy Mode, Reverse Proxy Mode, Login Attempts, Access Efforts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Reverse Proxy CASB Deployment Model CASB Cloud Security
Reverse Proxy CASB Deployment Model CASB Cloud SecurityThis slide outlines the overview of the reverse proxy cloud access security model broker. The purpose of this slide is to showcase overview of working and various types of reverse proxy CASB. The main types include regular reverse proxies and load balancers. Increase audience engagement and knowledge by dispensing information using Reverse Proxy CASB Deployment Model CASB Cloud Security. This template helps you present information on five stages. You can also present information on Reverse Proxy Cloud, Access Security Model Broker, Proxies And Load Balancers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps To Deploy Cloud Access Security Broker CASB Cloud Security
Steps To Deploy Cloud Access Security Broker CASB Cloud SecurityThis slide outlines the steps to implement a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Deliver an outstanding presentation on the topic using this Steps To Deploy Cloud Access Security Broker CASB Cloud Security. Dispense information and present a thorough explanation of Deployment Location, Deployment Model, Release Model, Cloud Access Security Broker using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Types Of Forward Proxy Server Deployment CASB Cloud Security
Types Of Forward Proxy Server Deployment CASB Cloud SecurityThis slide describes the two main categories of forward proxy server implementation. The purpose of this slide is to show how residential and data center proxies work, including their features. The components of a residential proxy include a proxy user, central proxy server, residential IP and internet. Present the topic in a bit more detail with this Types Of Forward Proxy Server Deployment CASB Cloud Security. Use it as a tool for discussion and navigation on Forward Proxy Server Deployment, Residential Proxy, Central Proxy Server. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Main Tools For Deploying Application Security
Main Tools For Deploying Application SecurityThis slide discusses the tools used for implementing application security such as Static Application Security Testing, Dynamic Application Security Testing, etc. Presenting our well structured Main Tools For Deploying Application Security The topics discussed in this slide are Security Scanning Tools, Runtime Protection ToolsThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Application Security Deployment Best Practices
Application Security Deployment Best PracticesThis slide discusses the best approaches for application security deployment which include assess threats, shift security left, control rights, etc. Presenting our set of slides with Application Security Deployment Best Practices This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Monitor App Security Results, Manage Access Levels
-
 Checklist For Effective Application Security Deployment
Checklist For Effective Application Security DeploymentThis slide showcases the actions performed while deploying application security, person responsible, status and comments for the same. Presenting our well structured Checklist For Effective Application Security Deployment The topics discussed in this slide are Person Responsible, StatusThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Key Benefits Of Application Security Deployment
Key Benefits Of Application Security DeploymentThis slide outlines the various advantages of deploying application security such as risk reduction, preserved brand reputation, trust enhancement, etc. Presenting our set of slides with Key Benefits Of Application Security Deployment This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Preserves Brand Reputation, Prevents Sensitive Data Leaks
-
 Web Security Upgradation Impact Of Web Security Deployment On Business
Web Security Upgradation Impact Of Web Security Deployment On BusinessThis slide showcases the after web security impact on industries which include security, reduced cyber threats in web, etc. Introducing Web Security Upgradation Impact Of Web Security Deployment On Business to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Decrease In Cyber Threats, Legal Consultations, Internet Safety Standards, using this template. Grab it now to reap its full benefits.
-
 Web Security Upgradation Raci Matrix To Deploy Web Security
Web Security Upgradation Raci Matrix To Deploy Web SecurityThis slide showcases a RACI matrix for web security, outlining the appropriate roles and steps to be taken during web security implementation. Present the topic in a bit more detail with this Web Security Upgradation Raci Matrix To Deploy Web Security. Use it as a tool for discussion and navigation on Risk Assessment, Authentication, Secure Development Practices, Data Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Web Security Upgradation Risks And Mitigation Strategies While Deploying Web Security
Web Security Upgradation Risks And Mitigation Strategies While Deploying Web SecurityThe purpose of this slide is to discuss the challenges faced while implementing web security such as alert overload, skill gap, etc. Present the topic in a bit more detail with this Web Security Upgradation Risks And Mitigation Strategies While Deploying Web Security. Use it as a tool for discussion and navigation on Risk, Impact, Mitigation Strategies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Chatbot Security Deployment Best Practices
Chatbot Security Deployment Best PracticesThis slide shows details regarding various best practices that can be adopted by organizations or businesses while deploying chatbots on their websites. These best practices are data segregation, input sanitization, content moderation, etc. Presenting our set of slides with Chatbot Security Deployment Best Practices. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Train Chatbot, Segregate Sensitive, Data From Models.



