Powerpoint Templates and Google slides for Secure Deployment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
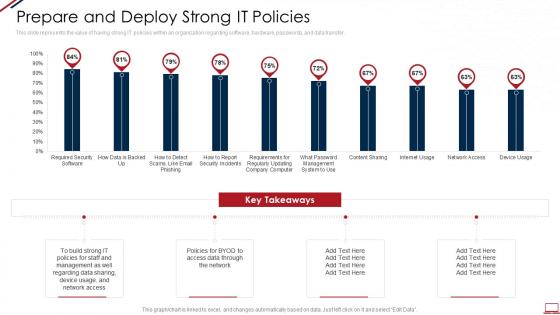 Computer system security prepare and deploy strong it policies
Computer system security prepare and deploy strong it policiesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Computer System Security Prepare And Deploy Strong It Policies. Use it as a tool for discussion and navigation on Prepare And Deploy Strong IT Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it prepare and deploy strong it policies ppt slides deck
Data security it prepare and deploy strong it policies ppt slides deckThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Data Security IT Prepare And Deploy Strong IT Policies Ppt Slides Deck. Use it as a tool for discussion and navigation on Build Strong, IT Policies, Required Security Software, Content Sharing, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security information and event management traditional siem deployment
Security information and event management traditional siem deploymentThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Present the topic in a bit more detail with this Security Information And Event Management Traditional SIEM Deployment. Use it as a tool for discussion and navigation on Visualization, Collection, Aggregation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Web application firewall waf it security use cases of web application firewall deployment
Web application firewall waf it security use cases of web application firewall deploymentThis slide represents the security use cases of web application firewall and how it would stop cyberattacks such as DDoS attacks, malicious bot abuse, and customer data breaches. Introducing Web Application Firewall Waf It Security Use Cases Of Web Application Firewall Deployment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Application, Performance, Deployment, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management traditional siem deployment model
Improve it security with vulnerability management traditional siem deployment modelThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Traditional Siem Deployment Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Real time analysis of security alerts traditional siem deployment model
Real time analysis of security alerts traditional siem deployment modelThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Deliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Traditional Siem Deployment Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Network Security Prepare And Deploy Strong It Policies
Network Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver an outstanding presentation on the topic using this Network Security Prepare And Deploy Strong It Policies. Dispense information and present a thorough explanation of Prepare And Deploy Strong It Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Prepare And Deploy Strong It Policies
Information Technology Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver an outstanding presentation on the topic using this Information Technology Security Prepare And Deploy Strong It Policies. Dispense information and present a thorough explanation of Prepare And Deploy Strong IT Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Siem For Security Analysis Traditional Siem Deployment Model
Siem For Security Analysis Traditional Siem Deployment ModelThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Present the topic in a bit more detail with this Siem For Security Analysis Traditional Siem Deployment Model. Use it as a tool for discussion and navigation on Vulnerability, Management, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Prepare And Deploy Strong It Policies
Information Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Information Security Prepare And Deploy Strong It Policies. Use it as a tool for discussion and navigation on Prepare And Deploy Strong IT Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Steps Enable Data Security Crm Software Deployment Guide
Implementation Steps Enable Data Security Crm Software Deployment GuideThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Implementation Steps Enable Data Security Crm Software Deployment Guide. Use it as a tool for discussion and navigation on Implementation, Authentication, Restrictions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps To Deploy People Centric Security
Steps To Deploy People Centric SecurityThe following slide showcases steps to enforce human centric security system to empower employees in handling useful information. It includes elements such as establishing environment for people centric security PCS, promoting culture of cyber security, etc. Introducing our premium set of slides with name Steps To Deploy People Centric Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Promote Culture Of Cybersecurity, Make Cyber Security An Obligation, Establish An Environment For PCS. So download instantly and tailor it with your information.
-
 Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System
Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless SystemThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System. Use it as a tool for discussion and navigation on Considerations, Service, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated Iot
Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Present the topic in a bit more detail with this Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated Iot. Use it as a tool for discussion and navigation on Operations, Logistics, Potential Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Iot Security Lock For Safe Fleet Management Deploying Internet Logistics Efficient Operations
Iot Security Lock For Safe Fleet Management Deploying Internet Logistics Efficient OperationsThe following slide illustrates internet of things IoT security lock for safe fleet management. It provides information about unlocking methods, Bluetooth, QR code, power saving, alarm notifications, large memory, etc. Introducing Iot Security Lock For Safe Fleet Management Deploying Internet Logistics Efficient Operations to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Four Unlocking Methods, Multiple Positioning Methods, Multiple Alarm Notification, using this template. Grab it now to reap its full benefits.
-
 Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient Operations
Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient OperationsThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Deliver an outstanding presentation on the topic using this Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient Operations. Dispense information and present a thorough explanation of Strategy, Information, Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ensuring Checklist For Mobile Security Deployment Enterprise Mobile Security For On Device
Ensuring Checklist For Mobile Security Deployment Enterprise Mobile Security For On DeviceThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Deliver an outstanding presentation on the topic using this Ensuring Checklist For Mobile Security Deployment Enterprise Mobile Security For On Device. Dispense information and present a thorough explanation of Enforcing Effective, Automatic Configuration, Effective Handling using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ensuring Checklist For Mobile Security Deployment Unified Endpoint Security
Ensuring Checklist For Mobile Security Deployment Unified Endpoint SecurityThis slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Introducing Ensuring Checklist For Mobile Security Deployment Unified Endpoint Security to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Password Protection, Automatic Configuration, Patches Management, using this template. Grab it now to reap its full benefits.
-
 Key Steps Involved In Mobile Device Management Deployment Unified Endpoint Security
Key Steps Involved In Mobile Device Management Deployment Unified Endpoint SecurityThis slide provides information regarding key steps involved in deploying mobile device management system. Increase audience engagement and knowledge by dispensing information using Key Steps Involved In Mobile Device Management Deployment Unified Endpoint Security. This template helps you present information on five stages. You can also present information on Profile Configuration, Device Enrollment, Successful Configuration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Importance Of Secure Ecommerce Payment Systems Content Management System Deployment
Importance Of Secure Ecommerce Payment Systems Content Management System DeploymentThis slide represents the importance of payment gateways in facilitating systemized payment methods and providing consumers with fast and flexible way for making payments. It includes benefits of ecommerce payment systems such as meets digital needs, customer retention, security etc. Present the topic in a bit more detail with this Importance Of Secure Ecommerce Payment Systems Content Management System Deployment. Use it as a tool for discussion and navigation on Multiple Payment Modes, Customer Retention, Importance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Event And Incident Flow Diagram Incident Response Strategies Deployment
Cyber Security Event And Incident Flow Diagram Incident Response Strategies DeploymentThis slide represents the flow diagram showing the procedure of managing cyber security incidents in order to minimize its impact on business operations. It starts with detection of cyber security incident and ends with response to crisis situation. Increase audience engagement and knowledge by dispensing information using Cyber Security Event And Incident Flow Diagram Incident Response Strategies Deployment. This template helps you present information on one stages. You can also present information on Security, Cyber, Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Handler Contact Information Incident Response Strategies Deployment
Cyber Security Incident Handler Contact Information Incident Response Strategies DeploymentThis slide represents the contact information of the members responsible for handling and managing the cyber security incidents. It includes details related to name, organization, role and contact details of cyber security incident handler. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handler Contact Information Incident Response Strategies Deployment. This template helps you present information on three stages. You can also present information on Organisation, Role, Contact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Management Checklist After An Incident Response Strategies Deployment
Cyber Security Incident Management Checklist After An Incident Response Strategies DeploymentThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Checklist After An Incident Response Strategies Deployment. This template helps you present information on ten stages. You can also present information on Management, Security, Review using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Management Checklist Before Incident Response Strategies Deployment
Cyber Security Incident Management Checklist Before Incident Response Strategies DeploymentThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident Management before the occurrence of the incident. Introducing Cyber Security Incident Management Checklist Before Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Security, Management, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Incident Management Checklist During Incident Response Strategies Deployment
Cyber Security Incident Management Checklist During Incident Response Strategies DeploymentThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident Management during the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Checklist During Incident Response Strategies Deployment. This template helps you present information on nine stages. You can also present information on Record, Convene, Meeting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Response KPI Dashboard Incident Response Strategies Deployment
Cyber Security Incident Response KPI Dashboard Incident Response Strategies DeploymentThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Deliver an outstanding presentation on the topic using this Cyber Security Incident Response KPI Dashboard Incident Response Strategies Deployment. Dispense information and present a thorough explanation of Monitoring, Operational, Score using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Incidents Follow Up Report Incident Response Strategies Deployment
Cyber Security Incidents Follow Up Report Incident Response Strategies DeploymentThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer. Deliver an outstanding presentation on the topic using this Cyber Security Incidents Follow Up Report Incident Response Strategies Deployment. Dispense information and present a thorough explanation of Security, Incident, Cyber using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment
Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies DeploymentThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Present the topic in a bit more detail with this Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Accounts, Globally, Unresolved. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Systems Monitoring Report Incident Response Strategies Deployment
Cyber Security Systems Monitoring Report Incident Response Strategies DeploymentThis slide represents the report to effectively monitor the networks and systems of the organization. It includes kpis such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Systems Monitoring Report Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Success, Resolve, Intrusion. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Issues Faced By Organization Due To Cyber Security Incidents Response Strategies Deployment
Key Issues Faced By Organization Due To Cyber Security Incidents Response Strategies DeploymentThis slide shows the challenges faced by enterprise due to increase in cyber attacks. It includes cyber security incidents experienced by the organization such as cloud computing issues, theft of sensitive information, ransomware attacks etc. Increase audience engagement and knowledge by dispensing information using Key Issues Faced By Organization Due To Cyber Security Incidents Response Strategies Deployment. This template helps you present information on five stages. You can also present information on Compliance, Information, Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Budget Allocation For Cyber Incident Management Training Deploying Computer Security
Budget Allocation For Cyber Incident Management Training Deploying Computer SecurityThis slide represents the budget prepared to predict cash flows and allocate required resources for incident management training. It includes training budget of IT, HR, operations, and finance department etc.Present the topic in a bit more detail with this Budget Allocation For Cyber Incident Management Training Deploying Computer Security. Use it as a tool for discussion and navigation on Training Budget, Supply Chain, Operational. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Common Sources Of Precursors And Indicators Deploying Computer Security Incident Management
Common Sources Of Precursors And Indicators Deploying Computer Security Incident ManagementThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc.Present the topic in a bit more detail with this Common Sources Of Precursors And Indicators Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Antivirus Software, Based Guarantee, Operating System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
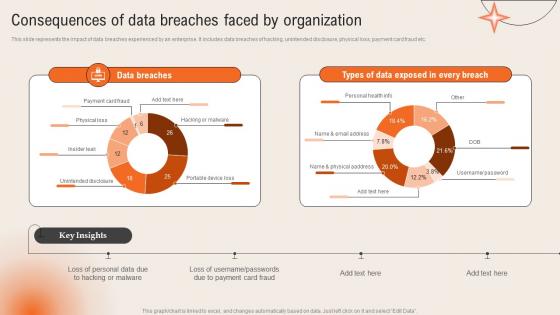 Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident Management
Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident ManagementThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc.Present the topic in a bit more detail with this Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Unintended Disclosure, Portable Device, Hacking Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incident Response Process Flow Chart Deploying Computer Security Incident Management
Cyber Security Incident Response Process Flow Chart Deploying Computer Security Incident ManagementThis slide represents the flow chart representing the detection and reaction to cyber security incidents, determination of their scope and risk and reduction of likelihood of incident from reoccurring. It starts with incident declaration and ends with system recovery.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Response Process Flow Chart Deploying Computer Security Incident Management. This template helps you present information on Two stages. You can also present information on Agency Reporting, Investigation Scope Determination, Collection Preservation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incidents Follow Up Report Deploying Computer Security Incident Management
Cyber Security Incidents Follow Up Report Deploying Computer Security Incident ManagementThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer.Present the topic in a bit more detail with this Cyber Security Incidents Follow Up Report Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Confidential Information, Training Employees, Organizational Projects. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
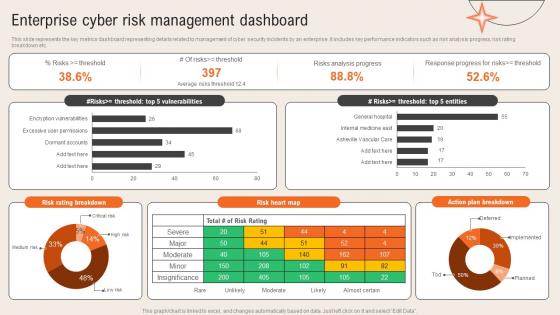 Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident Management
Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident ManagementThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc.Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Risks Analysis Progress, Response Progress, Action Plan Breakdown. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 As A Service Deployment Approach Of ZTNA Architecture Zero Trust Security Model
As A Service Deployment Approach Of ZTNA Architecture Zero Trust Security ModelThis slide outlines the overview of the as-a-service implementation approach of ZTNA architecture. The purpose of this slide is to highlight the ZTNA as a service architecture, including its advantages and disadvantages. The pros include fewer internal resources requirements and reassurance of up-to-date software. Present the topic in a bit more detail with this As A Service Deployment Approach Of ZTNA Architecture Zero Trust Security Model. Use it as a tool for discussion and navigation on Architecture, Deployment, Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Other ZTNA Architecture Deployment Approaches Zero Trust Security Model
Other ZTNA Architecture Deployment Approaches Zero Trust Security ModelThis slide represents the various deployment approaches for zero-trust network access architecture. The purpose of this slide is to showcase the other ZTNA approaches for architecture implementation and these are ZTA with enhanced identity governance, ZTA with micro-segmentation, and ZTA with SDN perimeters. Deliver an outstanding presentation on the topic using this Other ZTNA Architecture Deployment Approaches Zero Trust Security Model. Dispense information and present a thorough explanation of Enhanced Identity Governance, Micro Segmentation, Software Defined Network Perimeters using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Self Hosted Deployment Approach Of ZTNA Architecture Zero Trust Security Model
Self Hosted Deployment Approach Of ZTNA Architecture Zero Trust Security ModelThis slide illustrates the overview of the self-hosted deployment approach of ZTNA architecture. The purpose of this slide is to highlight the self-hosted deployment architecture of ZTNA and includes the pros and cons of the self-hosted deployment approach. Present the topic in a bit more detail with this Self Hosted Deployment Approach Of ZTNA Architecture Zero Trust Security Model. Use it as a tool for discussion and navigation on Architecture, Deployment, Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Different Types Of Secure Web Gateway Deployment Network Security Using Secure Web Gateway
Different Types Of Secure Web Gateway Deployment Network Security Using Secure Web GatewayThis slide demonstrates the various kinds of SWG deployments. The purpose of this slide is to explain the different types of Secure Web Gateway deployment methods such as on-premises deployment, cloud-based deployment and hybrid deployment. Increase audience engagement and knowledge by dispensing information using Different Types Of Secure Web Gateway Deployment Network Security Using Secure Web Gateway. This template helps you present information on three stages. You can also present information on Deployment, Businesses, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations
Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve OrganizationsThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Introducing Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing, Malware, Application, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB Model
Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB ModelThis slide represents the 30-0-90 days plan to implement the Cloud Access Security Broker model in an organization. The purpose of this slide is to showcase the various steps to be taken to deploy CASB at the interval every 30 days. Introducing Cloud Access Security Broker CASB V2 30 60 90 Days Plan To Deploy CASB Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Scope, Current Security Architecture, Security Operations Center Functions, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Proxy Based Vs API Based Deployment Of CASB
Cloud Access Security Broker CASB V2 Proxy Based Vs API Based Deployment Of CASBThis slide represents the comparison between proxy-based and API-based deployment of the CASB model. The purpose of this slide is to highlight the key differences between proxy-based and API-based deployment of cloud access security broker. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Proxy Based Vs API Based Deployment Of CASB. Use it as a tool for discussion and navigation on Performance And Security, Proxy Based Deployment, Standalone Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker CASB V2 Reverse Proxy CASB Deployment Model
Cloud Access Security Broker CASB V2 Reverse Proxy CASB Deployment ModelThis slide outlines the overview of the reverse proxy cloud access security model broker. The purpose of this slide is to showcase overview of working and various types of reverse proxy CASB. The main types include regular reverse proxies and load balancers. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Reverse Proxy CASB Deployment Model. This template helps you present information on five stages. You can also present information on Reverse Proxy, Cloud Access Security Model Broker, Web Server Anonymity, Websites With High Traffic using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Types Of Forward Proxy Server Deployment
Cloud Access Security Broker CASB V2 Types Of Forward Proxy Server DeploymentThis slide describes the two main categories of forward proxy server implementation. The purpose of this slide is to show how residential and data center proxies work, including their features. The components of a residential proxy include a proxy user, central proxy server, residential IP and internet. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Types Of Forward Proxy Server Deployment. Dispense information and present a thorough explanation of Proxy Server Deployment, Central Proxy Server, Proxy Server Implementation, Data Center Proxies Work using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Deploy Network Layer Firewall For Enforcing Security Policies
Deploy Network Layer Firewall For Enforcing Security PoliciesThis slide focuses on network layer firewall by controlling and monitoring cyber threats and enforcing access policies. It includes aspects such as non web attack, web attack, legitimate traffic, etc. Introducing our Deploy Network Layer Firewall For Enforcing Security Policies set of slides. The topics discussed in these slides are Operation Mode, Transparent Mode, Routed Mode. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Devsecops Best Practices For Secure Devsecops Pipeline Continuous Deployment Acceptance Stage
Devsecops Best Practices For Secure Devsecops Pipeline Continuous Deployment Acceptance StageThis slide discusses the continuous deployment acceptance stage of the DevSecOps pipeline. The purpose of this slide is to explain the acceptance phase and its security check, which includes thorough fuzz testing, dynamic application security testing, and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Devsecops Pipeline Continuous Deployment Acceptance Stage. Dispense information and present a thorough explanation of Thorough Fuzz Testing, Dynamic Application Security Testing, In Depth Static Analysis, Manual Security Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS
Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits key activities and tools for monitoring and diagnostics of IoT device security. It includes activities such as continuous monitoring, anomaly detection, vulnerability scanning, auditing and reporting, etc. Present the topic in a bit more detail with this Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Vulnerability Scanning, Auditing Reporting, Anomaly Detection . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Methods For Deploying Strong Device Authentication IoT Security And Privacy Safeguarding IoT SS
Methods For Deploying Strong Device Authentication IoT Security And Privacy Safeguarding IoT SSThis slide exhibits several IoT device authentication models for secure communication between machines. It includes methods such as digital certificates, hardware security module, trusted platform module and symmetric keys. Increase audience engagement and knowledge by dispensing information using Methods For Deploying Strong Device Authentication IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on four stages. You can also present information on Digital Certificates, Certificates Contains, Protect Cryptographic using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution
Firewall Network Security Global Firewall Market Segmentation By Deployment And SolutionThis slide provides an overview of global firewall market categorization based on deployment and solution type. The purpose of this slide is to showcase the firewall market share based on deployment types and solution type, such as software and hardware services. Deliver an outstanding presentation on the topic using this Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution Dispense information and present a thorough explanation of Oragnisation Size Segment Overview, Regional Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Progress Tracking Checklist For Mobile Security Deployment
Progress Tracking Checklist For Mobile Security DeploymentThis slide is a checklist to track progress on mobile security deployment which includes remote lock, proactive data wipe, auto configuration of devices, etc. Presenting our well structured Progress Tracking Checklist For Mobile Security Deployment. The topics discussed in this slide are Progress Tracking Checklist, Mobile Security Deployment, Configuration Of Devices. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Application Security Implementation Plan Authorization Deployment Steps For Application Security
Application Security Implementation Plan Authorization Deployment Steps For Application SecurityThis slide discusses the process phases for implementing effective authorization which include assessment, planning, defining access control policies, etc. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Authorization Deployment Steps For Application Security. This template helps you present information on seven stages. You can also present information on Technology Selection, Assessment And Planning, Training And Awareness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wireless Internet Security Us Market Size By Deployment
Wireless Internet Security Us Market Size By DeploymentThe following slide presents data on expected CAGR, deployment methods cloud, on-premise, security adoption trends, and more to depict the size and dynamics of the wireless internet security market in the United States, aiding in market analysis and decision-making. Presenting our well structured Wireless Internet Security Us Market Size By Deployment. The topics discussed in this slide are Deployment, Professional, Growth. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 30 60 90 Days Plan To Deploy CASB Model CASB Cloud Security
30 60 90 Days Plan To Deploy CASB Model CASB Cloud SecurityThis slide represents the 30-60-90 days plan to implement the cloud access security broker model in an organization. The purpose of this slide is to showcase the various steps to be taken to deploy CASB at the interval every 30 days. Introducing 30 60 90 Days Plan To Deploy CASB Model CASB Cloud Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, Cloud Access Security Broker, Connect To Current Security Architecture, Security Operations Center Functions, using this template. Grab it now to reap its full benefits.
-
 CASB Forward Proxy Deployment Use Cases CASB Cloud Security
CASB Forward Proxy Deployment Use Cases CASB Cloud SecurityThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using CASB Forward Proxy Deployment Use Cases CASB Cloud Security. This template helps you present information on two stages. You can also present information on Deploying Granular Access, Proxy Deployment Use Cases, Potential Security Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Proxy Based Vs Api Based Deployment Of CASB Cloud Security
Proxy Based Vs Api Based Deployment Of CASB Cloud SecurityThis slide represents the comparison between proxy-based and API-based deployment of the CASB model. The purpose of this slide is to highlight the key differences between proxy-based and API-based deployment of cloud access security broker. Present the topic in a bit more detail with this Proxy Based Vs Api Based Deployment Of CASB Cloud Security. Use it as a tool for discussion and navigation on Proxy Based Deployment, Requires Implementation, Security Filtering. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption For Data SSL Protocol Deployment For Secure Communication Cybersecurity SS
Encryption For Data SSL Protocol Deployment For Secure Communication Cybersecurity SSThis slide showcases secure socket layer SSL deployment which can help employees perform secure communication within businesses. It provides details about certificate authority, webmaster, etc. Present the topic in a bit more detail with this Encryption For Data SSL Protocol Deployment For Secure Communication Cybersecurity SS. Use it as a tool for discussion and navigation on Reduced Message Forgery, Reduced Data Theft, Less Eavesdropping. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Web Security Upgradation Timeline For Web Security Deployment In Business
Web Security Upgradation Timeline For Web Security Deployment In BusinessThis slide outlines the timeline for implementing web security in an organization which include assessment, planning, etc. Introducing Web Security Upgradation Timeline For Web Security Deployment In Business to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Assessment And Planning, Infrastructure Security, Secure Development Practices, using this template. Grab it now to reap its full benefits.
-
 Benefits Of Deploying Ai In Network Security
Benefits Of Deploying Ai In Network SecurityThis slide shows the major benefits of using artificial intelligence for security purposes. The major benefits are faster threat detection, improved accuracy, improved scalability and cost-saving Presenting our set of slides with Benefits Of Deploying Ai In Network Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Faster Threat Detection, Improved Accuracy, Scalability And Cost Saving .
-
 Deploying Ai Network Security In Defence Sector
Deploying Ai Network Security In Defence SectorThis slide shows how artificial intelligence is deployed in the defense sector to build strong network security. The major reasons for deploying AI are to analyse network threats, malware detection, insider threat detection and mitigation Introducing our premium set of slides with Deploying Ai Network Security In Defence Sector. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Threat Analysis, Malware Detection, Insider Threat Detection And Mitigation. So download instantly and tailor it with your information.



