Powerpoint Templates and Google slides for Risk Sources
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Organization risk probability management overview sources ppt icon
Organization risk probability management overview sources ppt iconPresent the topic in a bit more detail with this Organization Risk Probability Management Overview Sources Ppt Icon. Use it as a tool for discussion and navigation on Guidance, Management, Plan, Responsibilities, Sources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Global sourcing matrix with supply risk
Global sourcing matrix with supply riskIntroducing our premium set of slides with Global Sourcing Matrix With Supply Risk. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Leverage Products, Strategic Products, Bottleneck Products, Routine Products. So download instantly and tailor it with your information.
-
 Operational risk event sources and causes approach to mitigate operational risk ppt elements
Operational risk event sources and causes approach to mitigate operational risk ppt elementsThis slide covers information about sources and causes of operational risk events. Events included are internal fraud, external fraud, employment practice and workshop safety and clients and business practices.Present the topic in a bit more detail with this Operational Risk Event Sources And Causes Approach To Mitigate Operational Risk Ppt Elements. Use it as a tool for discussion and navigation on employee fraud for personal, excessive concentration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Hedge Funds Risk Management With Alternative Return Sources Hedge Fund Risk And Return Analysis
Hedge Funds Risk Management With Alternative Return Sources Hedge Fund Risk And Return AnalysisThis slide showcases the various alternative return sources with hedge fund risk management which include bidirectional security, deal risk premium, complexity premium, spread risk premium and macro trends. Present the topic in a bit more detail with this Hedge Funds Risk Management With Alternative Return Sources Hedge Fund Risk And Return Analysis. Use it as a tool for discussion and navigation on Management, Alternative, Sources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Risk Management Strategies Information Technology Risks Form Human Threat Source
IT Risk Management Strategies Information Technology Risks Form Human Threat SourceThis slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Present the topic in a bit more detail with this IT Risk Management Strategies Information Technology Risks Form Human Threat Source. Use it as a tool for discussion and navigation on Computer Criminal, Terrorist, Industrial Espionage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Risk Management Strategies IT Vulnerabilities With Threat Source And Action
IT Risk Management Strategies IT Vulnerabilities With Threat Source And ActionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this IT Risk Management Strategies IT Vulnerabilities With Threat Source And Action. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
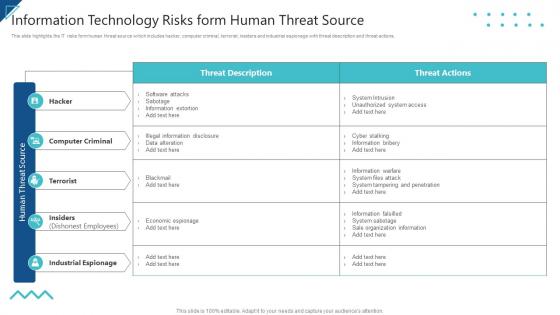 Enterprise Risk Management Information Technology Risks Form Human Threat Source
Enterprise Risk Management Information Technology Risks Form Human Threat SourceThis slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Present the topic in a bit more detail with this Enterprise Risk Management Information Technology Risks Form Human Threat Source. Use it as a tool for discussion and navigation on Computer Criminal, Terrorist, Industrial Espionage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise Risk Management IT Vulnerabilities With Threat Source And Action
Enterprise Risk Management IT Vulnerabilities With Threat Source And ActionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this Enterprise Risk Management IT Vulnerabilities With Threat Source And Action. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems
IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology SystemsThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this IT Vulnerabilities With Threat Source Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Vulnerabilities, Threat Source, Threat Action. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Risks Form Human Threat Source Risk Assessment Of It Systems
Information Technology Risks Form Human Threat Source Risk Assessment Of It SystemsThis slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Present the topic in a bit more detail with this Information Technology Risks Form Human Threat Source Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Information, Technology, Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It Vulnerabilities With Threat Source And Action Risk Assessment Of It Systems Ppt Slides Introduction
It Vulnerabilities With Threat Source And Action Risk Assessment Of It Systems Ppt Slides IntroductionThe following slide highlights the information technology vulnerabilities which includes the thread source from terminated employees and unauthorized users and threat action. Present the topic in a bit more detail with this It Vulnerabilities With Threat Source And Action Risk Assessment Of It Systems Ppt Slides Introduction. Use it as a tool for discussion and navigation on Vulnerabilities, Source, Information Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Improve Procurement Supply Chain Risks To Avoid Strategic Sourcing In Supply Chain Strategy SS V
Improve Procurement Supply Chain Risks To Avoid Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the techniques adopted to mitigate the risks of supply chain. Major risks covered are price instability, complex projects, poor supplier performance and inaccurate supply chain forecast. Present the topic in a bit more detail with this Improve Procurement Supply Chain Risks To Avoid Strategic Sourcing In Supply Chain Strategy SS V. Use it as a tool for discussion and navigation on Procurement, Improve, Unnecessary. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Analysis Risk Analysis Register To Determine Strategic Sourcing In Supply Chain Strategy SS V
Risk Analysis Risk Analysis Register To Determine Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the log register used to identify the potential risks and their mitigation plan. The risks covered are price instability, overspending, inaccurate forecasting, disruptions and fraud. Present the topic in a bit more detail with this Risk Analysis Risk Analysis Register To Determine Strategic Sourcing In Supply Chain Strategy SS V. Use it as a tool for discussion and navigation on Analysis, Register, Potential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Identification Checklist To Identify And Manage Strategic Sourcing In Supply Chain Strategy SS V
Risk Identification Checklist To Identify And Manage Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the checklist created to identify potential risks. The risks covered are inaccurate need analysis, inadequate vendor management, lack od automation, poor supplier management, overspending, etc. Deliver an outstanding presentation on the topic using this Risk Identification Checklist To Identify And Manage Strategic Sourcing In Supply Chain Strategy SS V. Dispense information and present a thorough explanation of Status, Responsible, Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Mitigation Plan To Reduce Strategic Sourcing In Supply Chain Strategy SS V
Risk Mitigation Plan To Reduce Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the strategies adopted to reduce risk impacts. The plans covered are adopting hedge funding, having flexible budget, using supply chain software, diversifying suppliers, creating a contingency plan, etc. Present the topic in a bit more detail with this Risk Mitigation Plan To Reduce Strategic Sourcing In Supply Chain Strategy SS V. Use it as a tool for discussion and navigation on Probability, Mitigation, Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Mitigation Vendor Risk Assessment And Mitigation Strategic Sourcing In Supply Chain Strategy SS V
Risk Mitigation Vendor Risk Assessment And Mitigation Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the various types of risks associated with vendors that affect a companys operations. Major risks covered are strategic, operational, financial, reputational, compliance and regulatory. Deliver an outstanding presentation on the topic using this Risk Mitigation Vendor Risk Assessment And Mitigation Strategic Sourcing In Supply Chain Strategy SS V. Dispense information and present a thorough explanation of Mitigation, Assessment, Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Monitoring Procurement Software To Assess And Strategic Sourcing In Supply Chain Strategy SS V
Risk Monitoring Procurement Software To Assess And Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the procurement software adopted by the firm to ensure seamless working. The slide covers features, benefits and pricing of the software. Present the topic in a bit more detail with this Risk Monitoring Procurement Software To Assess And Strategic Sourcing In Supply Chain Strategy SS V. Use it as a tool for discussion and navigation on Software, Procurement, Monitor. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Prioritization Impact Assessment Matrix For Risk Strategic Sourcing In Supply Chain Strategy SS V
Risk Prioritization Impact Assessment Matrix For Risk Strategic Sourcing In Supply Chain Strategy SS VThis slide provides an overview of the probability impact matrix to prioritize potential threats. The matrix includes scores that help to determine the risk level which is high, moderate and low. Deliver an outstanding presentation on the topic using this Risk Prioritization Impact Assessment Matrix For Risk Strategic Sourcing In Supply Chain Strategy SS V. Dispense information and present a thorough explanation of Probability, Impact, Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


