Powerpoint Templates and Google slides for Information Security Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Most Common Information Security Threats Training Ppt
Most Common Information Security Threats Training PptPresenting Most Common Information Security Threats. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
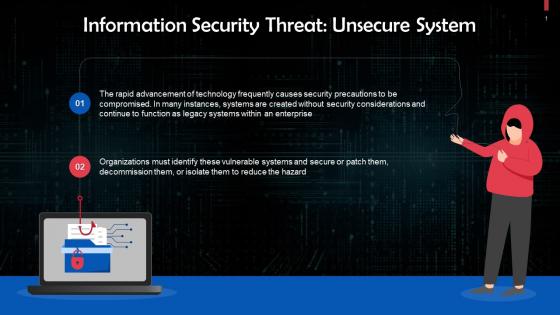 Unsecure Systems As An Information Security Threat Training Ppt
Unsecure Systems As An Information Security Threat Training PptPresenting Unsecure Systems as an Information Security Threat. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
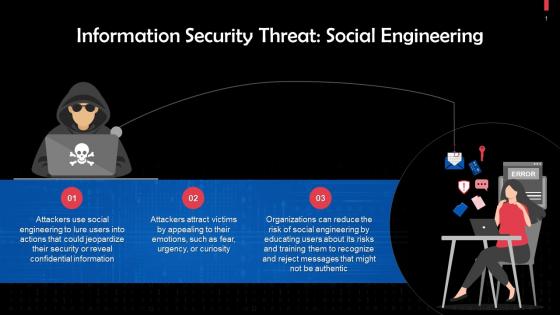 Social Engineering As An Information Security Threat Training Ppt
Social Engineering As An Information Security Threat Training PptPresenting Social Engineering as an Information Security Threat. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Social Media Attacks As An Information Security Threat Training Ppt
Social Media Attacks As An Information Security Threat Training PptPresenting Social Media Attacks as an Information Security Threat. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Lack Of Encryption As An Information Security Threat Training Ppt
Lack Of Encryption As An Information Security Threat Training PptPresenting Lack of Encryption as an Information Security Threat. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Security Misconfiguration As An Information Security Threat Training Ppt
Security Misconfiguration As An Information Security Threat Training PptPresenting Security Misconfiguration as an Information Security Threat. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Malware On Endpoints As An Information Security Threat Training Ppt
Malware On Endpoints As An Information Security Threat Training PptPresenting Malware on Endpoints as an Information Security Threat. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats
Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the cyber security expense overview to better allocate budget. It includes elements such as IT cost, revenue, security incidents, services down, issue status summary, total business hours lost etc. Deliver an outstanding presentation on the topic using this Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cyber Security Budget Spent, It Costs And Revenue, Issue Status Summary using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Insider Threat Information Security In Powerpoint And Google Slides Cpb
Insider Threat Information Security In Powerpoint And Google Slides CpbPresenting our Insider Threat Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Insider Threat Information Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Information Security Vulnerabilities Threats In Powerpoint And Google Slides Cpb
Information Security Vulnerabilities Threats In Powerpoint And Google Slides CpbPresenting Information Security Vulnerabilities Threats In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Eight stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Vulnerabilities Threats. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Managing Information Security Threats To Enhance Data Protection
Managing Information Security Threats To Enhance Data ProtectionThis slide represents strategies that help businesses mitigate threats of information security management and reduce data loss incidents. It includes various threats such as social media attacks, social engineering, lack of encryption, etc. Presenting our well structured Managing Information Security Threats To Enhance Data Protection. The topics discussed in this slide are Social Media Attacks, Social Engineering, Malware On Endpoints. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Potential Threats Impacting Information Security
Potential Threats Impacting Information SecurityThis slide highlights possible vulnerabilities to data security. The purpose of this template is to help businesses in overcoming various challenges in protecting data for creating a safer environment. It includes elements such as malware, phishing, data breaches, etc. Introducing our Potential Threats Impacting Information Security set of slides. The topics discussed in these slides are General Data Protection, Health Insurance Portability, Security Management Act FISMA. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Dashboard snapshot threat tracking electronic information security
Dashboard snapshot threat tracking electronic information securityThis slide depicts the dashboard for threat tracking in cyber security by covering monthly threat status, current risk status, threat based on the role, threats by owners, risk by threats, and threat report. Present the topic in a bit more detail with this Dashboard Snapshot Threat Tracking Electronic Information Security. Use it as a tool for discussion and navigation on Most Monthly Threat Status, Threat Dashboard, Current Risk Status, Threats Based Role, Risk By Threats, Threat Report, Threats Owners. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat and dashboard effective information security risk management process
Threat and dashboard effective information security risk management processFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Threat And Dashboard Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Security Recommendation, Security Controls, Active Remediation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Dashboard Snapshot For Threat Tracking In Information Security
Information Security Dashboard Snapshot For Threat Tracking In Information SecurityThis slide depicts the dashboard snapshot for threat tracking in cyber security by covering monthly threat status, current risk status, threat based on the role, threats by owners, risk by threats, and threat report. Deliver an outstanding presentation on the topic using this Information Security Dashboard For Threat Tracking In Information Security. Dispense information and present a thorough explanation of Dashboard, Information, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Management Framework For Information Security Threat And Vulnerability
Risk Management Framework For Information Security Threat And VulnerabilityFollowing slide displays threat and vulnerability management dashboard. It covers KPIs such as organization exposure score, system configuration score and severity score. Present the topic in a bit more detail with this Risk Management Framework For Information Security Threat And Vulnerability. Use it as a tool for discussion and navigation on Exposure Score, Top Vulnerable Software, Severity Distribution, Active Remediation, Configuration Score. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Security Dashboard Snapshot Threat Tracking Information Technology Security
Information Technology Security Dashboard Snapshot Threat Tracking Information Technology SecurityThis slide depicts the dashboard for threat tracking in cyber security by covering monthly threat status, current risk status, threat-based on the role, threats by owners, risk by threats, and threat report. Present the topic in a bit more detail with this Information Technology Security Dashboard Threat Tracking Information Technology Security. Use it as a tool for discussion and navigation on Dashboard, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Security Dashboard With Incident And Threat Management
Information Technology Security Dashboard With Incident And Threat ManagementThis slide shows the dashboard of cyber security with incidents and threat management. It includes overall progress, risk identified , number of critical incidents, initiative , incident and threat management etc. Introducing our Information Technology Security Dashboard With Incident And Threat Management set of slides. The topics discussed in these slides are Threat Management, Incident Management, Critical Risks Identified. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Quarterly Comparison Of Information Technology Security Threats
Quarterly Comparison Of Information Technology Security ThreatsThis slide shows the four types of security threats occurred during four quarters. It includes phishing, malware, IoT and password attacks. Introducing our Quarterly Comparison Of Information Technology Security Threats set of slides. The topics discussed in these slides are Quarterly Comparison, Information Technology, Security Threats. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Automation In Information Technology Time To Fix Security Threat With Manual Testing
Security Automation In Information Technology Time To Fix Security Threat With Manual TestingThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Deliver an outstanding presentation on the topic using this Security Automation In Information Technology Time To Fix Security Threat With Manual Testing. Dispense information and present a thorough explanation of Security, Threat, Manual Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Electronic information security cyber threat landscape in cloud security
Electronic information security cyber threat landscape in cloud securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Electronic Information Security Cyber Threat Landscape In Cloud Security. Use it as a tool for discussion and navigation on Organized Criminals, Hacktivists, Nation States, Insiders Partners, Competitors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Types of latest threats in electronic information security
Types of latest threats in electronic information securityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Increase audience engagement and knowledge by dispensing information using Types Of Latest Threats In Electronic Information Security. This template helps you present information on eight stages. You can also present information on Dridex Malware, Romance Scams, Emotet Malware, Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
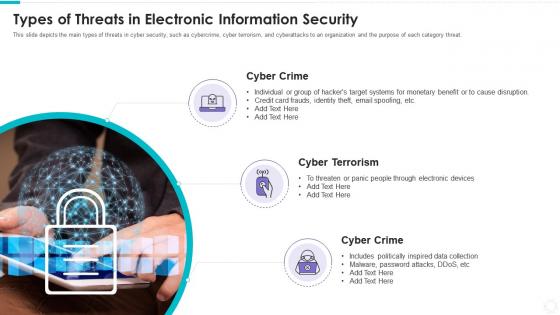 Types of threats in electronic information security
Types of threats in electronic information securityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Introducing Types Of Threats In Electronic Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Crime, Cyber Terrorism, using this template. Grab it now to reap its full benefits.
-
 Security information and event management threat intelligence services
Security information and event management threat intelligence servicesThis slide covers the threat intelligence services such as global intelligence, local intelligence, and other effective threat detection services. Introducing Security Information And Event Management Threat Intelligence Services to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Global Intelligence, Local Intelligence, Services, using this template. Grab it now to reap its full benefits.
-
 Common methods used to threaten electronic information security
Common methods used to threaten electronic information securityIntroducing Common Methods Used To Threaten Electronic Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Daniel Service, Man Middle, SQL Injection, Phishing , using this template. Grab it now to reap its full benefits.
-
 Defining security threats effective information security risk management process
Defining security threats effective information security risk management processThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures.Introducing Defining Security Threats Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Natural Disaster, Environmental Control Failures, Deliberate Software Attacks, using this template. Grab it now to reap its full benefits.
-
 Mitigation plan for threat effective information security risk management process
Mitigation plan for threat effective information security risk management processMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode.Deliver an outstanding presentation on the topic using this Mitigation Plan For Threat Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Resources Required, Expected Resolution Time, Communication Mode using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat assessment effective information security risk management process
Threat assessment effective information security risk management processFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Threat Assessment Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Affected Asset, Potential Vulnerability, Vulnerability Ranking using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Effective information security defining categories of information security threats
Effective information security defining categories of information security threatsThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures. Increase audience engagement and knowledge by dispensing information using Effective Information Security Defining Categories Of Information Security Threats. This template helps you present information on four stages. You can also present information on Human Error, Natural Disaster, Environmental Control Failures, Deliberate Software Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Effective information security mitigation plan for resolving encountered threat
Effective information security mitigation plan for resolving encountered threatMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Present the topic in a bit more detail with this Effective Information Security Mitigation Plan For Resolving Encountered Threat. Use it as a tool for discussion and navigation on Security Breach, System Failure, Risk Level, Mitigation Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icon of information security response plan to prevent threats
Icon of information security response plan to prevent threatsIntroducing our premium set of slides with Icon Of Information Security Response Plan To Prevent Threats. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon Of Information Security Response Plan To Prevent Threats. So download instantly and tailor it with your information.
-
 Cyber threat security icon to capture sensitive information
Cyber threat security icon to capture sensitive informationIntroducing our premium set of slides with Cyber Threat Security Icon To Capture Sensitive Information. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Security Icon To Capture Sensitive Information. So download instantly and tailor it with your information.
-
 Information Security Common Methods Used To Threaten Information Security
Information Security Common Methods Used To Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Deliver an outstanding presentation on the topic using this Information Security Common Methods Used To Threaten Information Security. Dispense information and present a thorough explanation of Information, Security, Common using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Cyber Threat Landscape In Information Security
Information Security Cyber Threat Landscape In Information SecurityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Information Security Cyber Threat Landscape In Information Security. Use it as a tool for discussion and navigation on Landscape, Information, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Latest Threats In Information Security
Information Security Latest Threats In Information SecurityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Introducing Information Security Latest Threats In Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Latest Threats In Information Security, using this template. Grab it now to reap its full benefits.
-
 Types Of Threats In Information Security
Types Of Threats In Information SecurityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Types Of Threats In Information Security. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Management Framework For Information Security Threat Identification And Vulnerability
Risk Management Framework For Information Security Threat Identification And VulnerabilityFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Threat Identification And Vulnerability. Dispense information and present a thorough explanation of Communication And Network, Database, Failure To Segment Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Automating threat identification security information and event management
Automating threat identification security information and event managementIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Security Information And Event Management. This template helps you present information on four stages. You can also present information on Information, Management, Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification table of contents security information and event management
Automating threat identification table of contents security information and event managementIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Table Of Contents Security Information And Event Management. This template helps you present information on eleven stages. You can also present information on Company Overview, Management, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security information and event management services automating threat identification
Security information and event management services automating threat identificationThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Security Information And Event Management Services Automating Threat Identification. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security Common Methods Used Threaten Information Security
Information Technology Security Common Methods Used Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Introducing Information Technology Security Common Methods Used Threaten Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Daniel Of Service, Man In The Middle, SQL Injection , using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Cyber Threat Landscape In Information Technology Security
Information Technology Security Cyber Threat Landscape In Information Technology SecurityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Deliver an outstanding presentation on the topic using this Information Technology Security Cyber Threat Landscape In Information Technology Security. Dispense information and present a thorough explanation of Landscape, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Latest Threats In Information Technology Security
Information Technology Security Latest Threats In Information Technology SecurityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Deliver an outstanding presentation on the topic using this Information Technology Security Latest Threats In Information Technology Security. Dispense information and present a thorough explanation of Latest Threats In Information Technology Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Threats In Information Technology Security
Information Technology Security Threats In Information Technology SecurityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Introducing Information Technology Security Threats In Information Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Types Of Threats In Information Technology Security, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Risks Or Threats Cloud Information Security
Cloud Security Risks Or Threats Cloud Information SecurityThis slide represents the list of threats or risks that can impact the security of a cloud these risks include loss of intellectual property, compliance violations, malware attacks, and so on.Increase audience engagement and knowledge by dispensing information using Cloud Security Risks Or Threats Cloud Information Security This template helps you present information on eight stages. You can also present information on Serious Repercussions, Organizations Should, Authentication Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Threats Compliance Violations Cloud Information Security
Cloud Security Threats Compliance Violations Cloud Information SecurityThis slide depicts the value of compliance violations threat of cloud security in a business and how fast an organization can switch to a non compliance state.Introducing Cloud Security Threats Compliance Violations Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Needed Information, Against Organization, Business Partners using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Contract Breaches With Clients Cloud Information Security
Cloud Security Threats Contract Breaches With Clients Cloud Information SecurityThis slide defines the contract breaches with clients and customers that could be the biggest threat to the organizational data.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Contract Breaches With Clients Cloud Information Security This template helps you present information on four stages. You can also present information on Organizations Cybercriminals, Customers OR Clients, Contact Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Threats End User Control Cloud Information Security
Cloud Security Threats End User Control Cloud Information SecurityThis slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats.Introducing Cloud Security Threats End User Control Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Wisely Considering, Storage Location, Procedures Strategies using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Information Security
Cloud Security Threats Loss Of Data Cloud Information SecurityThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Information Security This template helps you present information on four stages. You can also present information on Cloud Administrations, Protection Frameworks, Technology Advances using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Threats Malware Attacks Cloud Information Security
Cloud Security Threats Malware Attacks Cloud Information SecurityThis slide represents the malware threat of cloud security and how it can affect data stored on the cloud, further leading to company loss.Introducing Cloud Security Threats Malware Attacks Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Clients OR Customers, Organizations Experienced, Companies Organizations using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Revenue Losses Cloud Information Security
Cloud Security Threats Revenue Losses Cloud Information SecurityThis slide represents the revenue loss threat of cloud security and how an organization could lose customers trust and loyalty when it doesnt have a good recovery plan.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Revenue Losses Cloud Information Security This template helps you present information on five stages. You can also present information on Password Security, Clients Responsibility, Service Providers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Threats Shared Vulnerabilities Cloud Information Security
Cloud Security Threats Shared Vulnerabilities Cloud Information SecurityThis slide describes how organizations and providers share vulnerabilities of a system, so each party must take precautions to protect data.Introducing Cloud Security Threats Shared Vulnerabilities Cloud Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information Centers, Reduced Upfront, Diminished Opportunity using this template. Grab it now to reap its full benefits.
-
 F415 Risk Assessment And Management Plan For Information Security Analyzing Impact Security Threats
F415 Risk Assessment And Management Plan For Information Security Analyzing Impact Security ThreatsDeliver an outstanding presentation on the topic using this F415 Risk Assessment And Management Plan For Information Security Analyzing Impact Security Threats. Dispense information and present a thorough explanation of Analyzing, Organization, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Information Security Threats And Risk Assessment And Management Plan For Information Security
Identifying Information Security Threats And Risk Assessment And Management Plan For Information SecurityThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization Deliver an outstanding presentation on the topic using this Identifying Information Security Threats And Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Organization, Errors And Omissions, Employee Sabotage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Assessment And Management Plan For Information Security Analyzing The Impact Of Security Threats
Risk Assessment And Management Plan For Information Security Analyzing The Impact Of Security ThreatsDeliver an outstanding presentation on the topic using this Risk Assessment And Management Plan For Information Security Analyzing The Impact Of Security Threats. Dispense information and present a thorough explanation of Analyzing, Organization, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Four Information Technology Security Threats
Four Information Technology Security ThreatsIntroducing our premium set of slides with Four Information Technology Security Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Phishing Attacks, Cloud Jacking, Insider Threats. So download instantly and tailor it with your information.
-
 Information Technology Security Icon To Reduce Threats
Information Technology Security Icon To Reduce ThreatsIntroducing our premium set of slides with Information Technology Security Icon To Reduce Threats. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Technology Security Icon, Reduce Threats. So download instantly and tailor it with your information.
-
 Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems
Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Threat Risk, Risk Mitigation Plan, Risk Owner. This template is free to edit as deemed fit for your organization. Therefore download it now.




