Powerpoint Templates and Google slides for Encrypt Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Verified encrypted data security layer with arrows
Verified encrypted data security layer with arrowsPresenting this set of slides with name - Verified Encrypted Data Security Layer With Arrows. This is a six stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Data encryption strategies ppt powerpoint presentation outline format cpb
Data encryption strategies ppt powerpoint presentation outline format cpbPresenting this set of slides with name Data Encryption Strategies Ppt Powerpoint Presentation Outline Format Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Data Encryption Strategies to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Data encryption algorithm ppt powerpoint presentation diagram images cpb
Data encryption algorithm ppt powerpoint presentation diagram images cpbPresenting this set of slides with name Data Encryption Algorithm Ppt Powerpoint Presentation Diagram Images Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Data Encryption Algorithm to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Business Data Encryption Security Technology
Business Data Encryption Security TechnologyThis slide highlights the role of encryption technology which is used by business and organisation to protect the confidentiality of digital data storage and transmission. Key components are authentication, privacy, regulatory compliance and security. Presenting our set of slides with name Business Data Encryption Security Technology. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Privacy, Authentication, Regulatory Compliance, Security.
-
 Gaming Customer Experience Transformation With Data Encryption
Gaming Customer Experience Transformation With Data EncryptionThe following slide exhibits the role of data security technology which provides a sense of trust for online gaming customers and hence improves business brand image . Key components are authentication, privacy, regulatory compliance and security. Introducing our premium set of slides with Gaming Customer Experience Transformation With Data Encryption. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication, Privacy, Regulatory Compliance. So download instantly and tailor it with your information.
-
 Data Insurance Encryption In Powerpoint And Google Slides Cpb
Data Insurance Encryption In Powerpoint And Google Slides CpbPresenting our Data Insurance Encryption In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Data Insurance Encryption This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Enterprise Data Encryption IoT Cybersecurity Technology
Enterprise Data Encryption IoT Cybersecurity TechnologyThis slide exhibits the role of encryption technology and IoT that assists businesses and organizations to protect the confidentiality of digital data storage and transmission. Major elements are authentication, data privacy, compliance management, and security. Presenting our set of slides with Enterprise Data Encryption IoT Cybersecurity Technology. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication, Privacy, Management.
-
 Client Side Encryption Using Cryptomator Software Cloud Data Encryption
Client Side Encryption Using Cryptomator Software Cloud Data EncryptionThis slide discusses the Cryptomator software for cloud data encryption. The purpose of this slide is to highlight the steps involved in working with Cryptomator software, such as downloading and installing, using the password to view the encrypted files, etc. Increase audience engagement and knowledge by dispensing information using Client Side Encryption Using Cryptomator Software Cloud Data Encryption. This template helps you present information on one stages. You can also present information on Rapidly Encrypt, Online Storage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Client Side Encryption Using Nordlocker Software Cloud Data Encryption
Client Side Encryption Using Nordlocker Software Cloud Data EncryptionThis slide discusses the NordLocker software for cloud data encryption. The purpose of this slide is to highlight the steps involved in working with NordLocker software, such as downloading and installing, creating a password, using the password to view the encrypted files, etc. Introducing Client Side Encryption Using Nordlocker Software Cloud Data Encryption to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Download And Install, Create The Master, using this template. Grab it now to reap its full benefits.
-
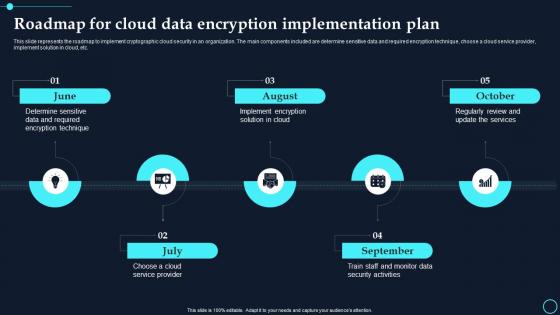 Roadmap For Cloud Data Encryption Implementation Plan Cloud Data Encryption
Roadmap For Cloud Data Encryption Implementation Plan Cloud Data EncryptionThis slide represents the roadmap to implement cryptographic cloud security in an organization. The main components included are determine sensitive data and required encryption technique, choose a cloud service provider, implement solution in cloud, etc.Increase audience engagement and knowledge by dispensing information using Roadmap For Cloud Data Encryption Implementation Plan Cloud Data Encryption. This template helps you present information on five stages. You can also present information on August, October using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Timeline For Cloud Data Security Implementation Cloud Data Encryption
Timeline For Cloud Data Security Implementation Cloud Data EncryptionThis slide represents the timeline to implement cloud data encryption in an organization. The main components included are determine sensitive data and required encryption technique, choose a cloud service provider, implement encryption solution in cloud, etc. Introducing Timeline For Cloud Data Security Implementation Cloud Data Encryption to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Test Encryption Solutions, Implement Encryptions Solution, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
 Encryption Implementation Strategies Symmetric Key Data Encryption Technique
Encryption Implementation Strategies Symmetric Key Data Encryption TechniqueThis slide illustrates the steps involved in transferring data using symmetric encryption. The purpose of this slide is to demonstrate how symmetric key encryption works. The critical components included are the sender, symmetric key, encrypted data, etc. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Symmetric Key Data Encryption Technique. This template helps you present information on five stages. You can also present information on Encrypted Data, Symmetric Key, Data Encryption Technique, Non Understandable Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Advantages Of Rivest Shamir Adleman Encryption Algorithm Encryption For Data Privacy In Digital Age It
Advantages Of Rivest Shamir Adleman Encryption Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of utilizing Rivest Shamir Adleman technique for data encryption. The advantages outlines in this slide are no key sharing, proof of authenticity, faster encryption, and no data modification. Increase audience engagement and knowledge by dispensing information using Advantages Of Rivest Shamir Adleman Encryption Algorithm Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Proof Of Authenticity, Faster Encryption, Data Modification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Advantages Of Using Symmetric Key Encryption Encryption For Data Privacy In Digital Age It
Advantages Of Using Symmetric Key Encryption Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of symmetric cryptography. The purpose of this slide is to elaborate the pros of using symmetric encryption techniques. The advantages are faster than asymmetric, better performance, improved optimization, etc. Introducing Advantages Of Using Symmetric Key Encryption Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Faster Than Asymmetric, Better Performance, Improved Optimization, using this template. Grab it now to reap its full benefits.
-
 Algorithms Based On Elliptic Curve Cryptography Encryption For Data Privacy In Digital Age It
Algorithms Based On Elliptic Curve Cryptography Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the applications of elliptic curve cryptography ECC in digital signatures, encryption, and key agreement. The algorithms discussed are ECDSA Elliptic Curve Digital Signature Algorithm, ECDH Elliptic Curve Diffie-Hellman, etc. Introducing Algorithms Based On Elliptic Curve Cryptography Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Digital Signatures, Minimal Computational Power, Fast Key Generation, using this template. Grab it now to reap its full benefits.
-
 Applications As A Service In Organizations Encryption For Data Privacy In Digital Age It
Applications As A Service In Organizations Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the major uses of Encryption-as-Service method in different domains. The key applications discussed in this slide are all-time security assurance, secure sensitive information and maintaining regulatory compliance. Introducing Applications As A Service In Organizations Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Maintaining Regulatory Compliance, Secure Sensitive Information, Security Assurance, using this template. Grab it now to reap its full benefits.
-
 Applications Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It
Applications Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide discusses the role of asymmetric encryption in authenticating the identity of the users. The several applications employed in this field are digital signatures, TLS or SSL handshake, managing cryptocurrency transactions and key sharing. Introducing Applications Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Digital Signatures, Managing Cryptocurrency Transactions, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Applications Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It
Applications Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age ItThis slide outlines the various fields which employ Elliptic Curve Cryptography algorithm to provide security. The applications of ECC discussed in this slide are Tor, National Security Agency NSA, blockchain, iMessage and Secure Sockets Layer SSL. Introducing Applications Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain, Cryptography Algorithm, Applications, using this template. Grab it now to reap its full benefits.
-
 Applications Of Quantum Encryption In Different Domains Encryption For Data Privacy In Digital Age It
Applications Of Quantum Encryption In Different Domains Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to demonstrate the various uses of quantum cryptography in several sectors, such as financial transactions, government and military communication, healthcare departments and Internet pf Things IoT. Increase audience engagement and knowledge by dispensing information using Applications Of Quantum Encryption In Different Domains Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Healthcare, Financial Transactions, Government And Military Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Applications Of Standard For Advanced Encryption Aes Encryption For Data Privacy In Digital Age It
Applications Of Standard For Advanced Encryption Aes Encryption For Data Privacy In Digital Age ItThis slide represents the uses of Standard for Advanced Encryption AES algorithm. The purpose of this slide is to explain the various applications of AES technique such as wireless security, encrypted browsing, general file encryption, etc. Introducing Applications Of Standard For Advanced Encryption Aes Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Wireless Security, Encrypted Browsing, General File Encryption , using this template. Grab it now to reap its full benefits.
-
 Applications Of Symmetric Key Data Encryption Encryption For Data Privacy In Digital Age It
Applications Of Symmetric Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide discusses the uses of symmetric encryption in real time scenarios. The purpose of this slide is to explain the various applications of symmetric encryption. These include online banking, secure Data at Rest and website authentication. Increase audience engagement and knowledge by dispensing information using Applications Of Symmetric Key Data Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on three stages. You can also present information on Online Banking, Secure Data At Rest, Website Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Applications Social Media Platforms Encryption For Data Privacy In Digital Age It
Applications Social Media Platforms Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the encryption methods employed by WhatsApp and Instagram. This slide also discusses the use of the signal protocol, symmetric and asymmetric key cryptography, and the Curve25519-based algorithm. Increase audience engagement and knowledge by dispensing information using Applications Social Media Platforms Encryption For Data Privacy In Digital Age It. This template helps you present information on eight stages. You can also present information on Encryption, Applications, Cryptography using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Benefits Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It
Benefits Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the advantages of Elliptic Curve Cryptography algorithm ECC. The benefits discussed in this slide are shorter key lengths, minimal computational power, faster key generation and incredibly fast generation of digital signatures. Increase audience engagement and knowledge by dispensing information using Benefits Of Elliptic Curve Cryptography Algorithm Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Shorter Key Lengths, Minimal Computational Power, Fast Key Generation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Benefits Of Using Encryption As A Service Technology Encryption For Data Privacy In Digital Age It
Benefits Of Using Encryption As A Service Technology Encryption For Data Privacy In Digital Age ItThis slide discusses the advantages of incorporating Encryption-as-a-Service in organizational network. The benefits outlined in this slide are enhance customer trust, boost data integrity, assist remote workers and avoid regulatory penalties. Introducing Benefits Of Using Encryption As A Service Technology Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Enhance Customer Trust, Assist Remote Workers, Avoid Regulatory Penalties, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Cloud Encryption Management Encryption For Data Privacy In Digital Age It
Best Practices For Cloud Encryption Management Encryption For Data Privacy In Digital Age ItThis slide talks about the steps to be taken for successful cloud cryptography management. The best practices involved are analyse security needs for cloud implementation, take regular backup of cloud data, main transparency and control, etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Cloud Encryption Management Encryption For Data Privacy In Digital Age It. This template helps you present information on eight stages. You can also present information on Manage Encryption Keys, Service Provider, Implement Data Classification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Business Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age It
Business Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to demonstrate the key uses of homomorphic encryption in different domains. The main business applications of this technology are supply chain security, regulatory compliance management and sensitive data analytics. Introducing Business Of Homomorphic Encryption Technology Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Supply Chain Security, Regulatory Compliance, Sensitive Data Analytics, using this template. Grab it now to reap its full benefits.
-
 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
 Data Packet Delivery Across Network Using Ipsec Protocols Encryption For Data Privacy In Digital Age It
Data Packet Delivery Across Network Using Ipsec Protocols Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to demonstrate the role of IPsec protocols in defining network security standards through RFC Request for Comments. The protocols discussed in this slide are IP AH, IP ESP, IKE and Key Management Protocol and Internet Security Association ISAKMP. Increase audience engagement and knowledge by dispensing information using Data Packet Delivery Across Network Using Ipsec Protocols Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Communication, Information, Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Disadvantages Of Using Quantum Encryption Technology Encryption For Data Privacy In Digital Age It
Disadvantages Of Using Quantum Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide outlines the several drawbacks of using quantum cryptography to secure the data transmission. The major cons of quantum encryption are expense, distance limitations, complexity, key distribution challenges and vulnerable to attacks. Introducing Disadvantages Of Using Quantum Encryption Technology Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Complexity, Vulnerable To Attacks, Distance Limitations, using this template. Grab it now to reap its full benefits.
-
 Drawbacks Of Using Symmetric Algorithms For Data Encryption For Data Privacy In Digital Age It
Drawbacks Of Using Symmetric Algorithms For Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the flaws of existing symmetric encryption techniques. The purpose of this slide is to explain the various disadvantages of symmetric cryptography. These include key leakage risk, lack of attribution data, no management system, etc. Increase audience engagement and knowledge by dispensing information using Drawbacks Of Using Symmetric Algorithms For Data Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Key Leakage Risk, Lack Of Attribution Data, No Management System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It
Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age ItThis slide discusses about the increasing adoption of encryption to solve current cyber security issues. The key points discussed are more use of cloud encryption in banking sector, introduction of homomorphic encryption, increase in BYOE adoption, etc. Increase audience engagement and knowledge by dispensing information using Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Homomorphic, Encryption, Introduction using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It
Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the various misconceptions and mistakes of organization while integrating cryptographic solutions into cloud. These include dependence on low-level encryption, reliance on cloud service providers for data protection, poor key management, etc. Introducing Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Data Protection, Poor Key Management, Software Engineers, using this template. Grab it now to reap its full benefits.
-
 Features Of Public Key Data Encryption Encryption For Data Privacy In Digital Age It
Features Of Public Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide demonstrates the characteristics of asymmetric encryption. The purpose of this slide is to explain the features of public key cryptography. These include dual keys, encryption and decryption, digital signatures, security, slow processing, etc. Increase audience engagement and knowledge by dispensing information using Features Of Public Key Data Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on six stages. You can also present information on Security, Slow Processing, Digital Signatures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Importance Of Data Encryption In Cloud Computing Encryption For Data Privacy In Digital Age It
Importance Of Data Encryption In Cloud Computing Encryption For Data Privacy In Digital Age ItThis slide talks about the role of cryptography in cloud computing. The purpose of this slide is to elaborate the importance of cloud cryptography. The key points are protects data from unauthorized access, maintains data confidentiality, ensures data integrity, etc. Introducing Importance Of Data Encryption In Cloud Computing Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Protects Data From Unauthorized Access, Maintains Data Confidentiality, Ensures Data Integrity, using this template. Grab it now to reap its full benefits.
-
 Importance Of Robust Network Data Encryption Encryption For Data Privacy In Digital Age It
Importance Of Robust Network Data Encryption Encryption For Data Privacy In Digital Age ItThis slide represents the various benefits of using network encryption. The advantages of this technology are protection against data Breaches, compliance with security regulations, protecting confidential information and intellectual property, etc. Increase audience engagement and knowledge by dispensing information using Importance Of Robust Network Data Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Protection Against Data Breaches, Data Encryption, Compliance With Security Regulations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Benefits Of Column Level Encryption Encryption For Data Privacy In Digital Age It
Key Benefits Of Column Level Encryption Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages of utilizing column level encryption. The benefits discussed in this slide are flexibility to decide the encrypted columns, efficiency and speed improvement, security due to different keys for different columns, etc. Introducing Key Benefits Of Column Level Encryption Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Flexibility, Security, Level Encryption, using this template. Grab it now to reap its full benefits.
-
 Key Benefits Of Data Encryption Techniques Encryption For Data Privacy In Digital Age It
Key Benefits Of Data Encryption Techniques Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages of employing encryption techniques to secure data. These include complete data security, ensure data integrity, security on various devices, guarantees compliance, safeguards intellectual property and enhance customer trust. Increase audience engagement and knowledge by dispensing information using Key Benefits Of Data Encryption Techniques Encryption For Data Privacy In Digital Age It. This template helps you present information on six stages. You can also present information on Security On Various Devices, Ensures Data Integrity, Guarantees Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Benefits Of Field Level Encryption Encryption For Data Privacy In Digital Age It
Key Benefits Of Field Level Encryption Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages of utilizing field level encryption on websites. The FLE benefits discussed in this slide are secure certain fields and documents, separate tasks, maintains compliance and seamless integration of encryption technique. Introducing Key Benefits Of Field Level Encryption Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Maintains Compliance, Seamless Integration, Separate Tasks, using this template. Grab it now to reap its full benefits.
-
 Key Features Affecting Working Of Des Algorithm Encryption For Data Privacy In Digital Age It
Key Features Affecting Working Of Des Algorithm Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various properties of Data Encryption Standard DES algorithm. The characteristics outlined in this slide are block cyphers, several encryption cycles, 64-bit key, permutation and replacement, and backward compatibility. Introducing Key Features Affecting Working Of Des Algorithm Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Several Encryption Cycles, Permutation And Replacement, Backward Compatibility, using this template. Grab it now to reap its full benefits.
-
 Key Features Of Encrypted Cloud Storage Encryption For Data Privacy In Digital Age It
Key Features Of Encrypted Cloud Storage Encryption For Data Privacy In Digital Age ItThis slide outlines the major characteristics of cloud cryptography. The purpose of this slide is to explain the main features of encrypted cloud storage. These are encryption, security, scalability, access control, collaboration, etc. Increase audience engagement and knowledge by dispensing information using Key Features Of Encrypted Cloud Storage Encryption For Data Privacy In Digital Age It. This template helps you present information on six stages. You can also present information on Encryption, Collaboration, Access Control using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Latest Advancements In Data Encryption Technology Encryption For Data Privacy In Digital Age It
Latest Advancements In Data Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide demonstrates the recent cryptographic trends in cyber security. The purpose of this slide is to represent the current advances in encryption technology. These include homomorphic encryption, honey encryption and biometric encryption. Increase audience engagement and knowledge by dispensing information using Latest Advancements In Data Encryption Technology Encryption For Data Privacy In Digital Age It. This template helps you present information on three stages. You can also present information on Homomorphic Encryption, Honey Encryption, Biometric Encryption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 List Of Communication Apps Using End To End Encryption Encryption For Data Privacy In Digital Age It
List Of Communication Apps Using End To End Encryption Encryption For Data Privacy In Digital Age ItThis slide demonstrates different texting apps utilizing end to end encryption to secure data transmission. The purpose of this slide is to outline the communication apps with default or optional end to end encryption such as Signal, WhatsApp, etc. Increase audience engagement and knowledge by dispensing information using List Of Communication Apps Using End To End Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Encryption, Communication, Conversations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Principal Use Cases Of Encryption Technology Encryption For Data Privacy In Digital Age It
Principal Use Cases Of Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide discusses the use of encryption in different domains. The purpose of this slide is to explain how encryption can be adopted for data protection in databases, cloud storage, compliance, payments and applications. Increase audience engagement and knowledge by dispensing information using Principal Use Cases Of Encryption Technology Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Encryption, Technology, Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Several Drawbacks Of Deniable Encryption Technology Encryption For Data Privacy In Digital Age It
Several Drawbacks Of Deniable Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various disadvantages of using deniable encryption. The flaws of this technology are increased complexity, potential misuse, weaker security, limited adoption and interoperability, and lack of ethical considerations. Increase audience engagement and knowledge by dispensing information using Several Drawbacks Of Deniable Encryption Technology Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Increased Complexity, Potential Misuse, Weaker Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps For Quantum Safe Certificate Migration Encryption For Data Privacy In Digital Age It
Steps For Quantum Safe Certificate Migration Encryption For Data Privacy In Digital Age ItThis slide demonstrates the process of replicating the old certificates with quantum-safe certificates. The steps included are Quantum-safe PKI, update server or s cryptography, update clients cryptography, install QS roots, install QS certificates, and deprecate old cryptography. Introducing Steps For Quantum Safe Certificate Migration Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cryptography, Install Qs Certificates, Process, using this template. Grab it now to reap its full benefits.
-
 Steps To Implement Encryption Techniques In Organization Encryption For Data Privacy In Digital Age It
Steps To Implement Encryption Techniques In Organization Encryption For Data Privacy In Digital Age ItThis slide discusses the procedure for implementing encryption in applications. The steps mentioned in this slide are identify sensitive data, assess encryption requirements, choose encryption algorithms, implement data encryption at rest, etc. Introducing Steps To Implement Encryption Techniques In Organization Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Identify Sensitive Data, Choose Encryption Algorithms, Deploy Data Encryption In Transit, using this template. Grab it now to reap its full benefits.
-
 Steps To Set Up Field Level Encryption Encryption For Data Privacy In Digital Age It
Steps To Set Up Field Level Encryption Encryption For Data Privacy In Digital Age ItThis slide represents the process of setting up field level encryption technology. The key steps involved in this procedure are identify sensitive fields and select encryption method, get encryption keys, make a profile for field-level encryption, etc. Increase audience engagement and knowledge by dispensing information using Steps To Set Up Field Level Encryption Encryption For Data Privacy In Digital Age It. This template helps you present information on six stages. You can also present information on Requirements, Asymmetric, Symmetric using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Symmetric Blowfish Rc4 And Serpent Encryption For Data Privacy In Digital Age It
Symmetric Blowfish Rc4 And Serpent Encryption For Data Privacy In Digital Age ItThis slide discusses the three symmetric encryption algorithms. The purpose of this slide is to briefly explain the working of three symmetric-key encryption algorithms. These are Blowfish RC4 Rivest Cypher 4 and Serpent. Introducing Symmetric Blowfish, Rc4 And Serpent Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric, Algorithms, Encryption, using this template. Grab it now to reap its full benefits.
-
 Data Encryption Features In Application Security
Data Encryption Features In Application SecurityThis slide outlines the characteristics of encryption in application security such as security, easy-to-use, document support, etc. Introducing Data Encryption Features In Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Implement Strict Input Validation, Employ Bot Detection Mechanisms, Application Security Deployment, using this template. Grab it now to reap its full benefits.
-
 Emerging Encryption Trends For Enhancing Data Security
Emerging Encryption Trends For Enhancing Data SecurityThis slide represents latest trends in encryption which assists to scramble data into a secret code which can be unlocked with unique digital key. It includes latest trends in encryption such as homomorphic encryption, quantum encryption, etc. Presenting our set of slides with name Emerging Encryption Trends For Enhancing Data Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Quantum Cryptography, Homomorphic Encryption, Moving Target Defense.
-
 Key Benefits Of Data Encryption For Enterprises
Key Benefits Of Data Encryption For EnterprisesThis slide represents benefits of encryption for enterprises which protects data from any alteration and secures our connections. It includes key benefits of data encryption for enterprises such as privacy and security, regulations, secure internet browsing, etc. Introducing our premium set of slides with name Key Benefits Of Data Encryption For Enterprises. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Privacy And Security, Regulations, Secure Internet Browsing. So download instantly and tailor it with your information.
-
 Encryption For Data Caesar Algorithm Implementation For Basic Encryption Cybersecurity SS
Encryption For Data Caesar Algorithm Implementation For Basic Encryption Cybersecurity SSThis slide showcases caesar algorithm deployment which can help employees learn basic techniques for basic encryption. It provides details about shift, displacement, shift value, decryption, etc. Introducing Encryption For Data Caesar Algorithm Implementation For Basic Encryption Cybersecurity SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Pre-Implementation Stage, Implementation Steps, Potential Benefit, using this template. Grab it now to reap its full benefits.
-
 Encryption For Data Encryption Awareness Training Implementation Plan Cybersecurity SS
Encryption For Data Encryption Awareness Training Implementation Plan Cybersecurity SSThis slide showcases training plan focused on building key encryption skills amongst organizations employees. It provides details about retention of training, backdoor access, internet society, etc. Introducing Encryption For Data Encryption Awareness Training Implementation Plan Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Existing Training Scenario, Details, Modules, Training Initiatives, using this template. Grab it now to reap its full benefits.
-
 Encryption For Data Homomorphic Cryptography For Data Base Security Cybersecurity SS
Encryption For Data Homomorphic Cryptography For Data Base Security Cybersecurity SSThis slide showcases homomorphic cryptography deployment which can help employees increase data privacy and outsourcing security. It provides details about private key, plaintext, decryption, etc. Introducing Encryption For Data Homomorphic Cryptography For Data Base Security Cybersecurity SS to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Homomorphic Encryption, Classified Plaintext, Decrypted Results, Data Owner Organization, using this template. Grab it now to reap its full benefits.
-
 Encryption For Data Key Management Algorithms And Dedicated Protocols Cybersecurity SS
Encryption For Data Key Management Algorithms And Dedicated Protocols Cybersecurity SSThis slide showcases key management protocols which can help companies increase efficiency and generation time. It provides details about hash functions, authentication, symmetric, etc. Introducing Encryption For Data Key Management Algorithms And Dedicated Protocols Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Cryptographic Hash Functions, Symmetric-Key Algorithms, Asymmetric-Key Algorithms, using this template. Grab it now to reap its full benefits.
-
 Comparative Assessment Of Encryption Algorithms For Organizational Data Security
Comparative Assessment Of Encryption Algorithms For Organizational Data SecurityThis slide provides a comparative assessment of various data encryption algorithms on different parameters. The multiple parameters used for assessment are encryption standard and use cases. Introducing our premium set of slides with Comparative Assessment Of Encryption Algorithms For Organizational Data Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Aes, Tdes, Twofish, Blowfish. So download instantly and tailor it with your information.
-
 Cloud Encryption Essentials For Robust Data Security
Cloud Encryption Essentials For Robust Data SecurityThe purpose of this slide is to highlight how cloud encryption essentials bolster robust data security. It safeguard sensitive information stored in cloud environments through cryptographic techniques. Presenting our set of slides with name Cloud Encryption Essentials For Robust Data Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Insider Threat Defense, Secure Data Transfers, Organizational Integrity.
-
 Data Encryption Hierarchy In SQL Sever
Data Encryption Hierarchy In SQL SeverThe slide illustrates how the data encryption hierarchy in SQL Server enhances security by implementing encryption methods at various levels. It ensures comprehensive data protection within the database. Presenting our set of slides with name Data Encryption Hierarchy In SQL Sever. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Service Master Key, Master Database Key, Database Level Key.
-
 Steps To Implement Data Encryption Backend Plans
Steps To Implement Data Encryption Backend PlansThe purpose of this slide is to guide organizations in implementing data encryption backend plans. It ensures seamless integration of robust strategies to safeguard sensitive data and enhance cybersecurity. Presenting our set of slides with name Steps To Implement Data Encryption Backend Plans. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Encryption Types, Algorithm Selection, Key Management.



