Powerpoint Templates and Google slides for Data Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 View competitive data analysis to identify opportunities and threats powerpoint slides
View competitive data analysis to identify opportunities and threats powerpoint slidesPresenting view competitive data analysis to identify opportunities and threats powerpoint slides. This Power Point template slide has been crafted with graphic of data bar graph and pie charts icons. This PPT slide contains the concept of competitive data analysis and identity opportunities representation. Use this PPT slide for business and marketing related presentations.
-
 Open source data icons slide gears threat ppt powerpoint presentation infographics good
Open source data icons slide gears threat ppt powerpoint presentation infographics goodPresenting this set of slides with name Open Source Data Icons Slide Gears Threat Ppt Powerpoint Presentation Infographics Good. The topics discussed in these slides are Business, Planning, Strategy, Marketing, Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Threat intelligence data model ppt powerpoint presentation model summary cpb
Threat intelligence data model ppt powerpoint presentation model summary cpbPresenting this set of slides with name Threat Intelligence Data Model Ppt Powerpoint Presentation Model Summary Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Threat Intelligence Data Model to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Big data security threats ppt powerpoint presentation styles layout cpb
Big data security threats ppt powerpoint presentation styles layout cpbPresenting this set of slides with name Big Data Security Threats Ppt Powerpoint Presentation Styles Layout Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Big Data Security Threats to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Big data security threats ppt powerpoint presentation icon samples cpb
Big data security threats ppt powerpoint presentation icon samples cpbPresenting this set of slides with name Big Data Security Threats Ppt Powerpoint Presentation Icon Samples Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Big Data Security Threats to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Computer virus a major threat for data storage companies
Computer virus a major threat for data storage companiesPresenting our set of slides with name Computer Virus A Major Threat For Data Storage Companies. This exhibits information on one stage of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Computer Virus A Major Threat For Data Storage Companies.
-
 Cybersecurity threat of ransomware hacking and data loss
Cybersecurity threat of ransomware hacking and data lossPresenting our set of slides with name Cybersecurity Threat Of Ransomware Hacking And Data Loss. This exhibits information on one stage of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity Threat Of Ransomware Hacking And Data Loss.
-
 Data security threat with pop up of virus detected
Data security threat with pop up of virus detectedIntroducing our premium set of slides with name Data Security Threat With Pop Up Of Virus Detected. Elucidate the one stage and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Security Threat With Pop Up Of Virus Detected. So download instantly and tailor it with your information.
-
 Data risk threat with virus image on the screen
Data risk threat with virus image on the screenIntroducing our premium set of slides with Data Risk Threat With Virus Image On The Screen. Elucidate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Risk, Threat Virus, Image Screen. So download instantly and tailor it with your information.
-
 30 60 90 day plan proper data management healthcare company reduce cyber threats ppt pictures
30 60 90 day plan proper data management healthcare company reduce cyber threats ppt picturesIntroducing 30 60 90 Day Plan Proper Data Management Healthcare Company Reduce Cyber Threats Ppt Pictures to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Day Plan, using this template. Grab it now to reap its full benefits.
-
 Abs healthcare company overview proper data management healthcare company reduce cyber threats
Abs healthcare company overview proper data management healthcare company reduce cyber threatsThis slide shows details about ABC Carbonated Drink Company such as company type, employees, headquarters, annual revenue, CEO, founding year etc. Present the topic in a bit more detail with this Abs Healthcare Company Overview Proper Data Management Healthcare Company Reduce Cyber Threats. Use it as a tool for discussion and navigation on Average, Revenue, Advertising, Global, Expenses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it types of threats in data security ppt slides graphic tips
Data security it types of threats in data security ppt slides graphic tipsThis slide depicts the main types of threats in data security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Data Security IT Types Of Threats In Data Security Ppt Slides Graphic Tips. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack, Cause Disruption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
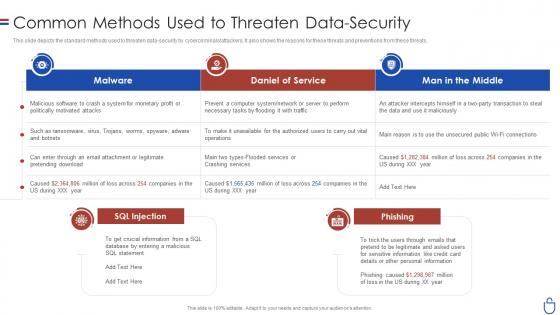 Data security it common methods used to threaten data security
Data security it common methods used to threaten data securityThis slide depicts the standard methods used to threaten data-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Present the topic in a bit more detail with this Data Security IT Common Methods Used To Threaten Data Security. Use it as a tool for discussion and navigation on Malware, Daniel Service, Man Middle, SQL Injection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
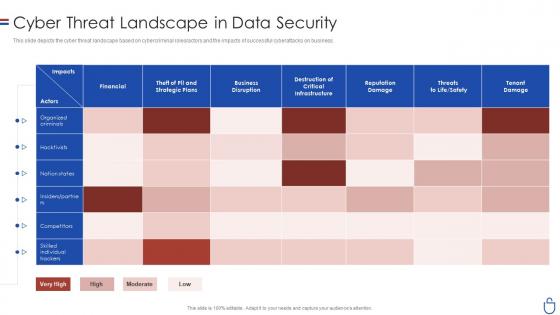 Data security it cyber threat landscape in data security
Data security it cyber threat landscape in data securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Data Security IT Cyber Threat Landscape In Data Security. Use it as a tool for discussion and navigation on Financial, Business Disruption, Reputation Damage, Tenant Damage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it dashboard snapshot for threat tracking in data security
Data security it dashboard snapshot for threat tracking in data securityThis slide depicts the dashboard snapshot for threat tracking in data security by covering monthly threat status, current risk status, threat-based on the role, threats by owners, risk by threats, and threat report. Deliver an outstanding presentation on the topic using this Data Security IT Dashboard For Threat Tracking In Data Security. Dispense information and present a thorough explanation of Monthly Threat Status, Current Risk Status, Threats Based On Role, Threats Owners, Risk Threats, Threat Report using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data security it latest threats in data security ppt slides background designs
Data security it latest threats in data security ppt slides background designsThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Increase audience engagement and knowledge by dispensing information using Data Security IT Latest Threats In Data Security Ppt Slides Background Designs. This template helps you present information on three stages. You can also present information on Dridex Malware, Romance Scams, Emotet Malware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threat management for organization critical addressing internal and external sources of threat data gathering
Threat management for organization critical addressing internal and external sources of threat data gatheringThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Present the topic in a bit more detail with this Threat Management For Organization Critical Addressing Internal And External Sources Of Threat Data Gathering. Use it as a tool for discussion and navigation on Targeted Intelligence, Malware Intelligence, Reputation Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icon showcasing data availability security against risks and threats
Icon showcasing data availability security against risks and threatsPresenting our set of slides with Icon Showcasing Data Availability Security Against Risks And Threats. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Showcasing Data Availability Security Against Risks And Threats.
-
 Addressing internal and external sources of threat data corporate security management
Addressing internal and external sources of threat data corporate security managementThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Introducing Addressing Internal And External Sources Of Threat Data Corporate Security Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Targeted Intelligence, Malware Intelligence, Reputation Intelligence, using this template. Grab it now to reap its full benefits.
-
 Agenda for advanced security monitoring plan to remove cybersecurity threat and data infraction
Agenda for advanced security monitoring plan to remove cybersecurity threat and data infractionIncrease audience engagement and knowledge by dispensing information using Agenda For Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. This template helps you present information on seven stages. You can also present information on Agenda using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons slide for advanced security monitoring plan to remove cybersecurity threat and data infraction
Icons slide for advanced security monitoring plan to remove cybersecurity threat and data infractionIntroducing our well researched set of slides titled Icons Slide For Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Table of contents advanced security monitoring plan to remove cybersecurity threat and data infraction
Table of contents advanced security monitoring plan to remove cybersecurity threat and data infractionPresent the topic in a bit more detail with this Table Of Contents Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. Use it as a tool for discussion and navigation on Cybersecurity Monitoring Tools To Be Implemented, Essential Elements Of Security Monitoring Plan, Cybersecurity Monitoring Best Practices To Be Followed By The Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace A Internal And External Sources Threat Data Gathering
Vulnerability Administration At Workplace A Internal And External Sources Threat Data GatheringThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Present the topic in a bit more detail with this Vulnerability Administration At Workplace A Internal And External Sources Threat Data Gathering. Use it as a tool for discussion and navigation on Sources, Intelligence, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Security Risks Or Threats Cloud Data Protection
Cloud Security Risks Or Threats Cloud Data ProtectionThis slide represents the list of threats or risks that can impact the security of a cloud these risks include loss of intellectual property, compliance violations, malware attacks, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Security Risks Or Threats Cloud Data Protection. This template helps you present information on eight stages. You can also present information on Revenue Losses, Compliance Violations, Loss Of Data using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats Compliance Violations Cloud Data Protection
Cloud Security Threats Compliance Violations Cloud Data ProtectionThis slide depicts the value of compliance violations threat of cloud security in a business and how fast an organization can switch to a non-compliance state. Introducing Cloud Security Threats Compliance Violations Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Authentication Procedures, Business, Organizations, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Contract Breaches With Clients Cloud Data Protection
Cloud Security Threats Contract Breaches With Clients Cloud Data ProtectionThis slide defines the contract breaches with clients and customers that could be the biggest threat to the organizational data. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Contract Breaches With Clients Cloud Data Protection. This template helps you present information on four stages. You can also present information on Business Partners, Organization, Cloud using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats End User Control Cloud Data Protection
Cloud Security Threats End User Control Cloud Data ProtectionThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Business Data, Customers, Centralized Data, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Data Protection
Cloud Security Threats Loss Of Data Cloud Data ProtectionThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Data Protection. This template helps you present information on four stages. You can also present information on Storage Locations, Organization, Strategies using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats Malware Attacks Cloud Data Protection
Cloud Security Threats Malware Attacks Cloud Data ProtectionThis slide represents the malware threat of cloud security and how it can affect data stored on the cloud, further leading to company loss. Introducing Cloud Security Threats Malware Attacks Cloud Data Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Frameworks, Targets, Technology, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Revenue Losses Cloud Data Protection
Cloud Security Threats Revenue Losses Cloud Data ProtectionThis slide represents the revenue loss threat of cloud security and how an organization could lose customers trust and loyalty when it doesnt have a good recovery plan. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Revenue Losses Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organizations Could, Revenue, Customers using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats Shared Vulnerabilities Cloud Data Protection
Cloud Security Threats Shared Vulnerabilities Cloud Data ProtectionThis slide describes how organizations and providers share vulnerabilities of a system, so each party must take precautions to protect data. Introducing Cloud Security Threats Shared Vulnerabilities Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Secure Cloud Data, Organizations, Data Security, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Computing Security
Cloud Security Threats Loss Of Data Cloud Computing SecurityThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Computing Security. This template helps you present information on four stages. You can also present information on Service Providers, Organization, Backup Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Threats Loss Of Data Cloud Information Security
Cloud Security Threats Loss Of Data Cloud Information SecurityThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Information Security This template helps you present information on four stages. You can also present information on Cloud Administrations, Protection Frameworks, Technology Advances using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Breakdown Of Malicious Data Breach Risk Root Cause By Threat
Breakdown Of Malicious Data Breach Risk Root Cause By ThreatThis slide depicts division of data breach with root cause. It includes risk categories such as compromised credentials, cloud misconfiguration, third party software vulnerability, phishing, security compromise, social engineering, business email compromise, etc. Introducing our Breakdown Of Malicious Data Breach Risk Root Cause By Threat set of slides. The topics discussed in these slides are Social Engineering, Business Email Compromise, Malicious Insider. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Threat Modeling Process For Secure Data Assets
Threat Modeling Process For Secure Data AssetsThis slide shows threat modeling to protect business assets from risks. It contains two phases discovery and implementation that includes steps such as identify assets, analyze attack surface, attack vectors, analyze, prioritize and develop controls. Introducing our premium set of slides with name Threat Modeling Process For Secure Data Assets. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hackers Path, Identified Assets, Threat Routes. So download instantly and tailor it with your information.
-
 Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security
Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Risk By Threats, Threat Report, Current Risk Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Threat Intelligence Data Sources For Analytics
Cyber Threat Intelligence Data Sources For AnalyticsThis slide provides a brief description of cyber threat intelligence data sources used in analytics to detect key threats and enable businesses to gain protection against cyber threats. It covers aspects such as data sources, description, types of source, best fit and benefits. Presenting our well structured Cyber Threat Intelligence Data Sources For Analytics. The topics discussed in this slide are Internal Intelligence, Counter Intelligence, Human Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Threat Intelligence System Architecture For Reliable Data Collection
Cyber Threat Intelligence System Architecture For Reliable Data CollectionThis slide represents an architecture for gathering reliable data and sustainable computing based on a block chain proposed cyber threat intelligence framework . It includes three layers device, feed and cloud. Introducing our Cyber Threat Intelligence System Architecture For Reliable Data Collection set of slides. The topics discussed in these slides are Cloud Layer, Feed Layer, Device Layer. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Threats Prevention Detection Correction
Data Threats Prevention Detection CorrectionThis slide presents threat prevention detection and correction plan for data management that could help in avoiding serious outcomes and protecting data from ongoing security issues. It includes RBAC implementation, audits and backup API for data management. Introducing our premium set of slides with Data Threats Prevention Detection Correction. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prevention, Detection, Correction. So download instantly and tailor it with your information.
-
 Top Vulnerable Industries To Cyber Security Threats And Data Breaches
Top Vulnerable Industries To Cyber Security Threats And Data BreachesThis slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Introducing our Top Vulnerable Industries To Cyber Security Threats And Data Breaches set of slides. The topics discussed in these slides are Government, Department. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Big Data Threats Vulnerabilities In Powerpoint And Google Slides Cpb
Big Data Threats Vulnerabilities In Powerpoint And Google Slides CpbPresenting our Big Data Threats Vulnerabilities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Big Data Threats Vulnerabilities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Preventive Measures For Data Theft Threats
Preventive Measures For Data Theft ThreatsThis slide covers security threats and preventive actions. The purpose of this template is to educate on various data theft methods and provide actionable steps to mitigate risks. It includes thumb sucking, data leakage, phishing attacks, data interception, and insider data theft. Presenting our set of slides with Preventive Measures For Data Theft Threats. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing, Interception, Data.
-
 Managing Information Security Threats To Enhance Data Protection
Managing Information Security Threats To Enhance Data ProtectionThis slide represents strategies that help businesses mitigate threats of information security management and reduce data loss incidents. It includes various threats such as social media attacks, social engineering, lack of encryption, etc. Presenting our well structured Managing Information Security Threats To Enhance Data Protection. The topics discussed in this slide are Social Media Attacks, Social Engineering, Malware On Endpoints. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Gathering And Analyzing Threat Intelligence Data Through ChatGPT Leveraging ChatGPT AI SS V
Gathering And Analyzing Threat Intelligence Data Through ChatGPT Leveraging ChatGPT AI SS VThis slide showcases various data sources that are leveraged by ChatGPT for threat intelligence to tack cyber attack on organization. Various data sources for threat intelligence are security blogs, social media and security forums. Introducing Gathering And Analyzing Threat Intelligence Data Through ChatGPT Leveraging ChatGPT AI SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Security Blogs, Security Forums, Social Media using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V
Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Automated Backup, Track Backup using this template. Grab it now to reap its full benefits.
-
 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats
Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Increase audience engagement and knowledge by dispensing information using Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Time Consuming Process, Speedy Process, Incremental Backup using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 External Threats To Data Security Management With Solutions
External Threats To Data Security Management With SolutionsThis slide showcases various external threats that affect the data security management of businesses with solutions to mitigate those risks. It includes various threats such as SQL injection, ransomware, phishing, and accidental exposure. Introducing our premium set of slides with External Threats To Data Security Management With Solutions. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Accidental Exposure, Unwanted Operations, Secure Mechanism. So download instantly and tailor it with your information.
-
 Security Management Policies To Mitigate Internal Data Threats
Security Management Policies To Mitigate Internal Data ThreatsThis slide focuses on the policies for security management helping companies to mitigate internal data threats efficiently. It includes policies for metadata, backup, internal protocol, emails, etc. Introducing our premium set of slides with Security Management Policies To Mitigate Internal Data Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protocol For Visitors, Internet Protocol, Security Audit. So download instantly and tailor it with your information.
-
 Our Threats Data Analytics And Storage Company Profile CP SS V
Our Threats Data Analytics And Storage Company Profile CP SS VThe following slide showcases the threats to Snowflake company and showcases external factors that can be a hurdle in business growth and development. It showcases elements such as market competition market competition and technology disruptions. Introducing Our Threats Data Analytics And Storage Company Profile CP SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weakness, Opportunities using this template. Grab it now to reap its full benefits.
-
 Our Threats Data Warehouse Service Company CP SS V
Our Threats Data Warehouse Service Company CP SS VThe following slide showcases the threats to Snowflake company and showcases external factors that can be a hurdle in business growth and development. It showcases elements such as market competition market competition and technology disruptions. Increase audience engagement and knowledge by dispensing information using Our Threats Data Warehouse Service Company CP SS V This template helps you present information on four stages. You can also present information on Opportunities, Strategic Collaboration, Industry Growth using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Bfsi Sector Cybersecurity Threats In Big Data Analytics
Bfsi Sector Cybersecurity Threats In Big Data AnalyticsThis slide highlights cybersecurity in BFSI sector big data analytics threats. This includes phishing attacks, cyber physical attacks, internet of things attacks and threats by third party involved. Introducing our premium set of slides with name Bfsi Sector Cybersecurity Threats In Big Data Analytics. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Physical Attacks, Internet Of Things Attacks, Threats By Third Party Involved. So download instantly and tailor it with your information.
-
 Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat
Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about a case study related to data breach recovery. It includes key elements such as incident date, challenges faced, LinkedIn response plan, and results. Deliver an outstanding presentation on the topic using this Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Regain Customer Trust, Rebuilding Business Reputation, Linkedin Response using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat
Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information leveraging multifactor authentication to increase cyber security. It includes key points such as failed login, geographic location, time of login, operating system, IP address, etc. Deliver an outstanding presentation on the topic using this Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Time Of Login Attempt, Operating System, Source Of IP Address using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Mitigating Cybersecurity Threats With Data Loss Prevention Solutions
Mitigating Cybersecurity Threats With Data Loss Prevention SolutionsThis slide represents various data loss prevention strategies that assist companies in mitigating multiple cybersecurity threats to enhance information protection. It includes threats such as extrusion, insider threats, and unintended exposure. Introducing our Mitigating Cybersecurity Threats With Data Loss Prevention Solutions set of slides. The topics discussed in these slides are Extrusion, Insider Threats, Unintended Exposure. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Introduction Of Cyber Threat Intelligence For Data Security
Introduction Of Cyber Threat Intelligence For Data SecurityThis slide discusses the overview of cyber threat intelligence for proactively blocking attacks and security purpose. Introducing Introduction Of Cyber Threat Intelligence For Data Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Evolving Threats Demand Intelligence, Vital For Security Architecture, Proactively Blocks Attacks, using this template. Grab it now to reap its full benefits.
-
 Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SS
Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding impact of data loss due to threat agents such as insider threat, social engineering, malware, specific enterprise cyber threats, etc.Present the topic in a bit more detail with this Determining Data Loss Impact Due To Cyber Threat Safeguarding Business With Data Loss Cybersecurity SS. Use it as a tool for discussion and navigation on Insider Threat, Social Engineering, Maintenance Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Insider Threats Management Case Study Aspire Safeguarding Business With Data Loss Cybersecurity SS
Insider Threats Management Case Study Aspire Safeguarding Business With Data Loss Cybersecurity SSThis slide provides information regarding case study highlighting insider threat management at a pharmaceutical company to secure clients sensitive data, track employees activities, etc.Introducing Insider Threats Management Case Study Aspire Safeguarding Business With Data Loss Cybersecurity SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Challenge, Solution, Impact, Objective, Industry Healthcare, using this template. Grab it now to reap its full benefits.
-
 Protecting Sensitive Data From Network Security Threats
Protecting Sensitive Data From Network Security ThreatsThis slide highlights network security threats to protect from unauthorized access including trojan viruses, malware, and computer worms. Introducing our premium set of slides with name Protecting Sensitive Data From Network Security Threats. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Trojan Virus, Malware, Computer Worms. So download instantly and tailor it with your information.
-
 Cyber Threat Analysis With Data Encryption
Cyber Threat Analysis With Data EncryptionThe purpose of this slide is to highlight how cyber threat analysis with data encryption fortifies security. It offers proactive insights into potential threats, ensuring a robust defense, and safeguarding sensitive information in the evolving landscape of cyber threats. Introducing our Cyber Threat Analysis With Data Encryption set of slides. The topics discussed in these slides are Cybersecurity Threat, Budget Constraints, Inadequate Training And Awareness. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.



