Powerpoint Templates and Google slides for Cybersecurity Tools
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cybersecurity assessment tool ppt powerpoint presentation ideas visual cpb
Cybersecurity assessment tool ppt powerpoint presentation ideas visual cpbPresenting Cybersecurity Assessment Tool Ppt Powerpoint Presentation Ideas Visual Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the colour, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cybersecurity Assessment Tool. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
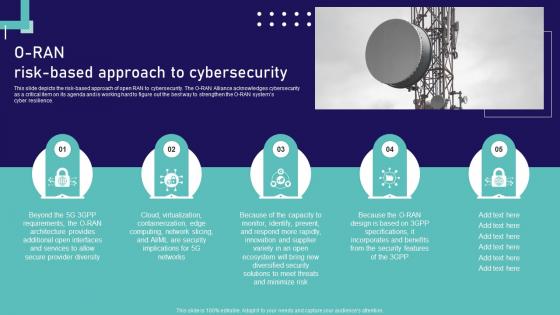 Open Ran Technology O Ran Risk Based Approach To Cybersecurity Ppt Professional Shapes
Open Ran Technology O Ran Risk Based Approach To Cybersecurity Ppt Professional ShapesThis slide depicts the risk-based approach of open RAN to cybersecurity. The O-RAN Alliance acknowledges cybersecurity as a critical item on its agenda and is working hard to figure out the best way to strengthen the O-RAN systems cyber resilience. Increase audience engagement and knowledge by dispensing information using Open Ran Technology O Ran Risk Based Approach To Cybersecurity Ppt Professional Shapes. This template helps you present information on five stages. You can also present information on Cybersecurity, Approach, Containerization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise Data Encryption IoT Cybersecurity Technology
Enterprise Data Encryption IoT Cybersecurity TechnologyThis slide exhibits the role of encryption technology and IoT that assists businesses and organizations to protect the confidentiality of digital data storage and transmission. Major elements are authentication, data privacy, compliance management, and security. Presenting our set of slides with Enterprise Data Encryption IoT Cybersecurity Technology. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication, Privacy, Management.
-
 IoT Cloud Computing Cybersecurity Technology Components
IoT Cloud Computing Cybersecurity Technology ComponentsThis slide represents a strategic framework for IoT cloud security technology which is used in various aspects of data and network protection. Key components are disaster recovery, governance, monitoring, user access management, data security, etc. Presenting our set of slides with IoT Cloud Computing Cybersecurity Technology Components. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Control, Management, Hardware.
-
 IoT Cybersecurity Technology Components And Protocol
IoT Cybersecurity Technology Components And ProtocolThis slide highlights the multiple security components and protocol of IoT technology that helps businesses and organizations in data management. Key elements are technologies, consumer, industrial, etc. Presenting our set of slides with IoT Cybersecurity Technology Components And Protocol. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technology, Protocol, Components.
-
 IoT Firewall Data Cybersecurity Technology
IoT Firewall Data Cybersecurity TechnologyThe below slide highlights the application of IoT firewall data security that ensures a safe connection over the internet. Key benefits are packet filtering, proxy service, unified threat management UTM, stateful inspection, and next generation firewall. Presenting our set of slides with IoT Firewall Data Cybersecurity Technology. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technology, Cybersecurity, Firewall.
-
 Ultimate Guide For Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SS
Ultimate Guide For Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SSIncrease audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Importance Of Cybersecurity In Blockchain Technology BCT SS This template helps you present information on Four stages. You can also present information on Decentralized Architecture, Public Key Cryptography using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Features Of OpenAI ChatGPT Tool How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
Key Features Of OpenAI ChatGPT Tool How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcase various features of OpenAI ChatGPT tool. Features include multi language support, text generation, question answering, customization, conversational AI, integration within web application, batching, scaling etc. Introducing Key Features Of OpenAI ChatGPT Tool How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Generation, Support, Customization, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Cybersecurity Technology Deployment Plan To Improve Organizations
Best Practices For Cybersecurity Technology Deployment Plan To Improve OrganizationsThis slide represents the best practices to be adopted by the organizations which aim to minimize impact of cyber security incidents on business operations and prevent them from happening again. It includes best practices such as create cyber incident management plan etc. Introducing Best Practices For Cybersecurity Technology Deployment Plan To Improve Organizations to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Process, Responsibilities, using this template. Grab it now to reap its full benefits.
-
 Big Data Analytics Cybersecurity Tools
Big Data Analytics Cybersecurity ToolsThe following slide highlights resources like EPP, SIEM, threat intelligence software, fraud detection, predictive modeling, and anti malware sandboxes to show big data analytics cybersecurity tools. It helps organizations to bolster their cyber defense capabilities and safeguard against a wide range of threats. Introducing our premium set of slides with Big Data Analytics Cybersecurity Tools. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Management, Intelligence. So download instantly and tailor it with your information.
-
 Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase different types of Internet of Things IoT security software. Identity and access management, antivirus software, firewall software, intrusion detection system, and data loss prevention are some of the major tools which are outlined in slide. Introducing Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Software, System, using this template. Grab it now to reap its full benefits.
-
 Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Introducing Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, using this template. Grab it now to reap its full benefits.
-
 Importance Of Cybersecurity In Blockchain Technology Guide For Blockchain BCT SS V
Importance Of Cybersecurity In Blockchain Technology Guide For Blockchain BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Introducing Importance Of Cybersecurity In Blockchain Technology Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Architecture, Key Cryptography, Smart Contracts using this template. Grab it now to reap its full benefits.
-
 Blockchain And Cybersecurity Importance Of Cybersecurity In Blockchain Technology BCT SS V
Blockchain And Cybersecurity Importance Of Cybersecurity In Blockchain Technology BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Increase audience engagement and knowledge by dispensing information using Blockchain And Cybersecurity Importance Of Cybersecurity In Blockchain Technology BCT SS V This template helps you present information on Four stages. You can also present information on Decentralized Architecture, Public Key Cryptography, Smart Contracts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain And Cybersecurity Overview Of Phishing Attack In Blockchain Technology BCT SS V
Blockchain And Cybersecurity Overview Of Phishing Attack In Blockchain Technology BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting blockchian to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Blockchain And Cybersecurity Overview Of Phishing Attack In Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Attached Fake Links, Investment Opportunities, Fake Website using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Tools To Safeguard Educational Institutes
Cybersecurity Tools To Safeguard Educational InstitutesThis slide depicts the cybersecurity tools to safeguard educational institutes. The purpose of this slide is to help the business ensure suitable cybersecurity measures are implemented to prevent cyberattacks. It includes tools such as packet sniffers, firewalls, etc. Presenting our set of slides with Cybersecurity Tools To Safeguard Educational Institutes. This exhibits information on Ten stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity Tools, Penetrating Tests, Encryption Tools
-
 Cybersecurity Technology To Protect NGOs Data
Cybersecurity Technology To Protect NGOs DataThe purpose of this slide is to highlight how cybersecurity technology protects NGOs data by preventing unauthorized access, ensuring integrity, and fortifying against cyber threats and breaches. Introducing our premium set of slides with Cybersecurity Technology To Protect NGOs Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Breaches And Hacking, Phishing And Social Engineering, Outdated Software And Systems, Data Privacy Compliance. So download instantly and tailor it with your information.
-
 Emerging Cybersecurity Challenges In Information Technology
Emerging Cybersecurity Challenges In Information TechnologyThis slide represents cybersecurity challenges in information technology for adapting to dynamic landscapes, strengthening defenses, and ensuring resilience of systems. It includes issues such as cloud, ransomware, IoT, phishing, and insider attacks. Introducing our premium set of slides with Emerging Cybersecurity Challenges In Information Technology Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Attacks, Iot Attacks, Insider Attacks So download instantly and tailor it with your information.
-
 Cybersecurity Automation Tools To Enhance Data Protection
Cybersecurity Automation Tools To Enhance Data ProtectionThis slide represents various cybersecurity automation tools that help companies to enhance data protection from threats and vulnerabilities. It includes various tools such as sprint, quals, splunk, logpoint, etc. Introducing our premium set of slides with Cybersecurity Automation Tools To Enhance Data Protection Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Features, Cybersecurity Automation, Data Protection So download instantly and tailor it with your information.
-
 Applications Of SCADA Cybersecurity Tools For Data Protection
Applications Of SCADA Cybersecurity Tools For Data ProtectionThis slide represents various applications of SCADA cybersecurity tools that assist IT companies to enhance their data protection effectively. It includes various applications such as data encryption, vulnerability assessment, etc. Introducing our premium set of slides with Applications Of SCADA Cybersecurity Tools For Data Protection Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Intrusion Detection Systems, Firewalls And Network Segmentation, Encryption And Secure Protocols. So download instantly and tailor it with your information.
-
 Use Cases Of Blockchain In Cybersecurity Decoding The Future Of Blockchain Technology BCT SS
Use Cases Of Blockchain In Cybersecurity Decoding The Future Of Blockchain Technology BCT SSThis slide highlights various use cases of integrating blockchain technology in cybersecurity. It includes edge computing with authentication, advance confidentiality, secured private messaging, improved PKI and intact domain systems. Increase audience engagement and knowledge by dispensing information using Use Cases Of Blockchain In Cybersecurity Decoding The Future Of Blockchain Technology BCT SS. This template helps you present information on five stages. You can also present information on Protected Edge Computing With Authentication, Advanced Confidentiality And Data Integrity, Secured Private Messaging using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Blockchain Technology Working For Organizational Cybersecurity
Blockchain Technology Working For Organizational CybersecurityThe below slide provides the working process for blockchain security technology used by organizations to enhance transaction privacy. The process involves steps such as initiation, validation, verification, etc. Presenting our set of slides with Blockchain Technology Working For Organizational Cybersecurity. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Transaction Initiated, Transaction Completed, Benefits Received.


