Powerpoint Templates and Google slides for Cyber Data Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data security it assessment matrix of cyber risks ppt slides outline
Data security it assessment matrix of cyber risks ppt slides outlineThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Present the topic in a bit more detail with this Data Security IT Assessment Matrix Of Cyber Risks Ppt Slides Outline. Use it as a tool for discussion and navigation on Systems Involved, Owner Tenant, Mobile, Web Applications, Health Care. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
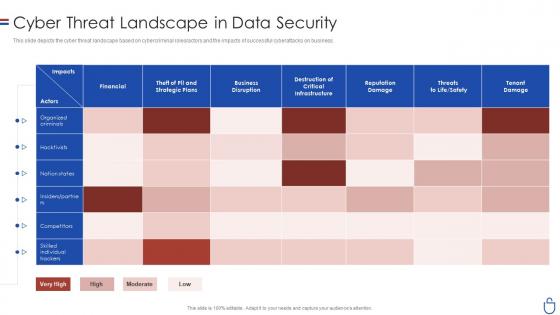 Data security it cyber threat landscape in data security
Data security it cyber threat landscape in data securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Data Security IT Cyber Threat Landscape In Data Security. Use it as a tool for discussion and navigation on Financial, Business Disruption, Reputation Damage, Tenant Damage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Data Analysis With Reported Incident Metrics
Cyber Security Data Analysis With Reported Incident MetricsThis slide shows the scorecard of the data security with key performance indicators. It also includes the progress status of data readiness and security audits with their value and targets that has to be achieved during the period. Presenting our well structured Cyber Security Data Analysis With Reported Incident Metrics. The topics discussed in this slide are Data Production Readdress, Data Production Officer Nominated, Explicit Consent Tracking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security
Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Course Description, Instructor, Rating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver an outstanding presentation on the topic using this Comparison Of Various Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Security Reporting, Phishing Simulations, Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Cyber Security Breach Lost Revenue Preventing Data Breaches Through Cyber Security
Impact Of Cyber Security Breach Lost Revenue Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the consequences of cyber security breach on the company revenue. It provides information about the revenue lost over different months caused by different cyber attack such as malware, social engineering attack, business email compromise etc. Deliver an outstanding presentation on the topic using this Impact Of Cyber Security Breach Lost Revenue Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Malware, Social Engineering Attack, Business Email Compromise using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 In House Training Schedule We Will Implement Preventing Data Breaches Through Cyber Security
In House Training Schedule We Will Implement Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to exhibit a comprehensive cyber security awareness training plan for the stakeholders. Information covered in this slide is related to malware, social engineering attack, business email compromise, ransomware, password attack, crypto jacking and IoT Based attack. Present the topic in a bit more detail with this In House Training Schedule We Will Implement Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Compromise, Training. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Measuring Security Awareness Campaign Results With KPIS Preventing Data Breaches Through Cyber Security
Measuring Security Awareness Campaign Results With KPIS Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase various key performance indicator KPIs which can assist the company to effectively track cyber security awareness campaign results. The KPIs are phishing rate, self reported incidents, security breaches, cost of security breach and campaign participation rate. Deliver an outstanding presentation on the topic using this Measuring Security Awareness Campaign Results With KPIS Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Phishing Rate, Security Breaches, Campaign Participation Rate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Preventing Data Breaches Through Cyber Security Awareness Table Of Contents
Preventing Data Breaches Through Cyber Security Awareness Table Of ContentsPresent the topic in a bit more detail with this Preventing Data Breaches Through Cyber Security Awareness Table Of Contents. Use it as a tool for discussion and navigation on Employees, Awareness Training, Cyber Security Breach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Pricing Plan Of Security Awareness Packages Preventing Data Breaches Through Cyber Security
Pricing Plan Of Security Awareness Packages Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the pricing plan of cyber security awareness package. It covers information about the total number of employees along with different packages such as silver, gold, platinum and diamond. Deliver an outstanding presentation on the topic using this Pricing Plan Of Security Awareness Packages Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Employees, Security, Awareness Packages using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Recognizing The Cyber Security Gaps Faced By Key Preventing Data Breaches Through Cyber Security
Recognizing The Cyber Security Gaps Faced By Key Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline the different cyber security gaps which are faced by employees, line and senior managers. Information covered in this slide is related to ransomware, password attack, crypto jacking, IoT based attack, malware etc. Present the topic in a bit more detail with this Recognizing The Cyber Security Gaps Faced By Key Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Comprise, Iot Based Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness
Table Of Contents For Preventing Data Breaches Through Cyber Security AwarenessDeliver an outstanding presentation on the topic using this Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness. Dispense information and present a thorough explanation of Cyber Security Awareness, Online Courses, Automation Tools using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber Security
Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber SecurityPresent the topic in a bit more detail with this Tracking Sheet To Monitor The Performance Of Employees Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Compromise, Iot Based Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Schedule Matrix To Increase Data Security
Cyber Security Schedule Matrix To Increase Data SecurityThis slide signifies the IT schedule table to enhance data protection. It covers information about weekly schedule of activities to be conducted like configure technical security, conduct penetration test, install firewalls, conduct formal training.Presenting our well structured Cyber Security Schedule Matrix To Increase Data Security. The topics discussed in this slide are Conduct Stimulated, Configuring Technical, Unnatural Activities. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Policy Data Classification Policy Overview And Approaches
Cyber Security Policy Data Classification Policy Overview And ApproachesThis slide represents the data classification policy overview and approaches. Approaches include highly restricted, restricted, and internal use and types of data each approach will include. Deliver an outstanding presentation on the topic using this Cyber Security Policy Data Classification Policy Overview And Approaches. Dispense information and present a thorough explanation of Highly Restricted, Approaches, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Plan Useful Data Backup Schedule Improving Cyber Security Risks Management
Plan Useful Data Backup Schedule Improving Cyber Security Risks ManagementThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Present the topic in a bit more detail with this Plan Useful Data Backup Schedule Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Incremental Backup, Plan Useful, Data Backup Schedule. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
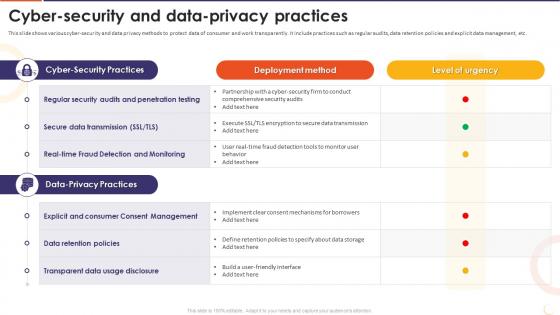 The Future Of Financing Digital Cyber Security And Data Privacy Practices
The Future Of Financing Digital Cyber Security And Data Privacy PracticesThis slide shows various cyber-security and data privacy methods to protect data of consumer and work transparently. It include practices such as regular audits, data retention policies and explicit data management, etc. Present the topic in a bit more detail with this The Future Of Financing Digital Cyber Security And Data Privacy Practices. Use it as a tool for discussion and navigation on Regular Security Audits, Penetration Testing, Secure Data Transmission, Data Retention Policies, Transparent Data Usage Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Checklist For Historical Data Analysis
Cyber Security Checklist For Historical Data AnalysisThis slide represents cyber security analysis checklist for providing systematic and organized approach to evaluate, improve and maintain organizations security posture. It includes basis such as aspects, tasks, checkpoints, authorized head, status and notes. Presenting our well structured Cyber Security Checklist For Historical Data Analysis. The topics discussed in this slide are Authorized, Status, Analysis. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Encrypt And Create Backup Of Useful Data Creating Cyber Security Awareness
Encrypt And Create Backup Of Useful Data Creating Cyber Security AwarenessThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost,. Present the topic in a bit more detail with this Encrypt And Create Backup Of Useful Data Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Accountable, Consulted, Responsible This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Plan Useful Data Backup Schedule Creating Cyber Security Awareness
Plan Useful Data Backup Schedule Creating Cyber Security AwarenessThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Deliver an outstanding presentation on the topic using this Plan Useful Data Backup Schedule Creating Cyber Security Awareness Dispense information and present a thorough explanation of Security And Privacy, Web Application Security, Infrastructure Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security KPIS To Measure Data Security
Cyber Security KPIS To Measure Data SecurityThe mentioned slide emphasizes critical key performance indicators KPIs such as the level of preparedness, unidentified devices, intrusion attempts, security incidents, and mean time to detect. These metrics serve as valuable benchmarks for measuring and improving data security, enabling organizations to assess their cybersecurity posture effectively. Introducing our Cyber Security KPIS To Measure Data Security set of slides. The topics discussed in these slides are Level Of Preparedness, Intrusion Attempts, Security Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Prevention Techniques For Cyber Security Data Attacks
Prevention Techniques For Cyber Security Data AttacksThe highlighted slide identifies critical types of cybersecurity attacks on data, including malware, phishing, password attacks, man in the middle attacks, and SQL injection. This information is essential for understanding and preparing against various threats, contributing to a more robust defense strategy for safeguarding data. Introducing our Prevention Techniques For Cyber Security Data Attacks set of slides. The topics discussed in these slides are Malware Attack, Phishing Attack, Password Attack. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Encryption And Authentication In Automotive Cyber Security
Data Encryption And Authentication In Automotive Cyber SecurityThis slide highlights data privacy and encryption in automotive cybersecurity. The purpose of this slide is to aid organizations in implementing measures for securing sensitive data from possible manipulation. It includes various measures for authentication and data encryption. Presenting our set of slides with Data Encryption And Authentication In Automotive Cyber Security This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication, Data Encryption, Authenticity Of Software
-
 Cyber Hazard Mitigation Plan For Data Security
Cyber Hazard Mitigation Plan For Data SecurityThis slide represents hazard mitigation plan to enhance cybersecurity and data protection including risks such as malware, phishing attack, and DDoS attack. Presenting our well structured Cyber Hazard Mitigation Plan For Data Security. The topics discussed in this slide are Malware, Phishing Attack, Ddos Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat
Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about a case study related to data breach recovery. It includes key elements such as incident date, challenges faced, LinkedIn response plan, and results. Deliver an outstanding presentation on the topic using this Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Regain Customer Trust, Rebuilding Business Reputation, Linkedin Response using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat
Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information leveraging multifactor authentication to increase cyber security. It includes key points such as failed login, geographic location, time of login, operating system, IP address, etc. Deliver an outstanding presentation on the topic using this Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Time Of Login Attempt, Operating System, Source Of IP Address using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices To Implement Ethics In Data Cyber Security
Best Practices To Implement Ethics In Data Cyber SecurityThis slide represents various best practices that assist companies to implement ethics to enhance their data cybersecurity. It include various best practices such as ethical code of conduct, ethical hacking and testing, third-party ethics. Introducing our Best Practices To Implement Ethics In Data Cyber Security set of slides. The topics discussed in these slides are Best Practices, Details, Impact. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Pam Framework For Optimizing Cyber Security And Data Protection
Pam Framework For Optimizing Cyber Security And Data ProtectionThis slide represents framework that assists companies to implement PAM cybersecurity to enhance their data protection and risk management. It includes various components such as use cases, defining requirements, architecture development, etc. Presenting our well structured Pam Framework For Optimizing Cyber Security And Data Protection. The topics discussed in this slide are Determine Use Cases, Define Requirements, Develop Architecture. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Applications Of Cyber Security In Banking For Data Protection
Applications Of Cyber Security In Banking For Data ProtectionThis slide represents cyber security applications in banking for data protection. This template aims to safeguard data and systems, ensure variety of cyber security tools and methodologies at access. It includes different approaches such as network security surveillance, software security, etc. Introducing our Applications Of Cyber Security In Banking For Data Protection set of slides. The topics discussed in these slides are Network Security Surveillance, Software Security, Risk Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.


