Powerpoint Templates and Google slides for CASB
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 CASB Forward Proxy Deployment Use Cases Cloud Access Security Broker CASB
CASB Forward Proxy Deployment Use Cases Cloud Access Security Broker CASBThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using CASB Forward Proxy Deployment Use Cases Cloud Access Security Broker CASB. This template helps you present information on two stages. You can also present information on Deploying Granular, Detecting Shadow, Activity Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 CASB Reverse Proxy Deployment Use Cases Cloud Access Security Broker CASB
CASB Reverse Proxy Deployment Use Cases Cloud Access Security Broker CASBThis slide illustrates the use cases of reverse proxy server deployment of the cloud access security broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Introducing CASB Reverse Proxy Deployment Use Cases Cloud Access Security Broker CASB. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Use Cases, Description, Access Constraints, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB Advantages And Disadvantages Proxy Based Deployment
Cloud Access Security Broker CASB Advantages And Disadvantages Proxy Based DeploymentThis slide represents the benefits and drawbacks of proxy based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Introducing Cloud Access Security Broker CASB Advantages And Disadvantages Proxy Based Deployment. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Advantages, Disadvantages, Based Deployment, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB Comparison Between Reverse Proxy And Load Balancer
Cloud Access Security Broker CASB Comparison Between Reverse Proxy And Load BalancerThis slide represents the difference between reverse proxy and load balancer. The purpose of this slide is to highlight the main differences between reverse proxy server and load balancer based on how they respond to client request, number of servers required, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB Comparison Between Reverse Proxy And Load Balancer. This template helps you present information on two stages. You can also present information on Reverse Proxy, Load Balancer, Comparison using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB Pros And Cons Of API Scanning CASB Deployment
Cloud Access Security Broker CASB Pros And Cons Of API Scanning CASB DeploymentThis slide outlines the advantages and disadvantages of the API scanning cloud access security broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Introducing Cloud Access Security Broker CASB Pros And Cons Of API Scanning CASB Deployment. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Pros, Cons, Casb Deployment, using this template. Grab it now to reap its full benefits.
-
 Overview Of CASB Deployment Models Cloud Access Security Broker CASB
Overview Of CASB Deployment Models Cloud Access Security Broker CASBThis slide talks about the implementation models of cloud access security broker. The purpose of this slide is to demonstrate the two types of CASB deployment, such as out of band and inline. The CASB deployment models include API scanning and forward and reverse proxy. Introducing Overview Of CASB Deployment Models Cloud Access Security Broker CASB. to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Deployment Models, Api Scanning, Forward Proxy, using this template. Grab it now to reap its full benefits.
-
 Why CASB Is Important For Businesses Cloud Access Security Broker CASB
Why CASB Is Important For Businesses Cloud Access Security Broker CASBThis slide outlines the importance of CASB for different organizations. The purpose of this slide is to showcase the various reasons for businesses to invest in the cloud access security broker model, including increased cloud adoption, better security, compliance, and cost effective and centralized management. Increase audience engagement and knowledge by dispensing information using Why CASB Is Important For Businesses Cloud Access Security Broker CASB. This template helps you present information on one stages. You can also present information on Reasons, Description, Increased Cloud Adoption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment
Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based DeploymentThis slide represents the benefits and drawbacks of proxy-based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy-based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Advantages And Disadvantages Of Proxy Based Deployment. This template helps you present information on two stages. You can also present information on Cloud Access Security Brokers, Cover Flexibility, Secure SaaS Applications, Enforcement Of Security Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use CasesThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases. This template helps you present information on two stages. You can also present information on Deploying Granular Access, Activity Controls, Detecting Shadow, IT In The Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use CasesThis slide illustrates the use cases of reverse proxy server deployment of the Cloud Access Security Broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Introducing Proxy to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Reverse Proxy Server Deployment, Cloud Access Security Broker, Reverse Proxy Deployment, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load Balancer
Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load BalancerThis slide represents the difference between reverse proxy and load balancer. The purpose of this slide is to highlight the main differences between reverse proxy server and load balancer based on how they respond to client request, number of servers required, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Comparison Between Reverse Proxy And Load Balancer. This template helps you present information on one stages. You can also present information on Reverse Proxy And Load Balancer, Reverse Proxy, Site Requires Several Servers, Scalability And Flexibility using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs Download
Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs DownloadIntroducing Cloud Access Security Broker CASB V2 For Table Of Contents Ppt Ideas Designs Download to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Shadow IT Management Lifecycle, Cloud Security Standards, Control Frameworks, Requirements, using this template. Grab it now to reap its full benefits.
-
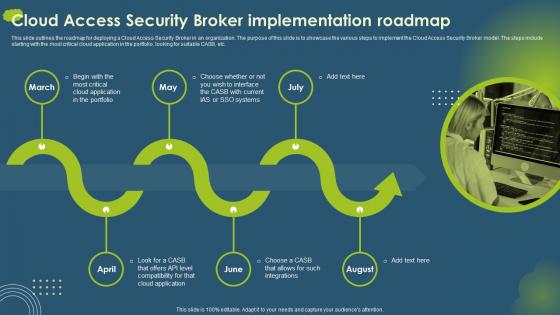 Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery Portrait
Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery PortraitThis slide outlines the roadmap for deploying a Cloud Access Security Broker in an organization. The purpose of this slide is to showcase the various steps to implement the Cloud Access Security Broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. Introducing Cloud Access Security Broker CASB V2 Implementation Roadmap Ppt Gallery Portrait to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Critical Cloud Application, Compatibility, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB Deployment
Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB DeploymentThis slide outlines the advantages and disadvantages of the API scanning Cloud Access Security Broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pros And Cons Of API Scanning CASB Deployment. This template helps you present information on one stages. You can also present information on Cloud Access Security, Broker Deployment Model, Scanning Deployment Model, Security Policy Modifications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Steps To Deploy Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Steps To Deploy Cloud Access Security BrokerThis slide outlines the steps to implement a Cloud Access Security Broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Steps To Deploy Cloud Access Security Broker. This template helps you present information on one stages. You can also present information on Speedier Installation, Comprehensive Coverage, Cloud Access Security Broker using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker CASB V2 Why CASB Is Important For Businesses
Cloud Access Security Broker CASB V2 Why CASB Is Important For BusinessesThis slide outlines the importance of CASB for different organizations. The purpose of this slide is to showcase the various reasons for businesses to invest in the Cloud Access Security Broker model, including increased cloud adoption, better security, compliance, and cost-effective and centralized management. Introducing Cloud Access Security Broker CASB V2 Why CASB Is Important For Businesses to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Cloud Adoption, Better Security, Compliance, Centralized Management, using this template. Grab it now to reap its full benefits.
-
 Cloud Access Security Broker CASB V2 Working Process Ppt Ideas Graphics Example
Cloud Access Security Broker CASB V2 Working Process Ppt Ideas Graphics ExampleThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Working Process Ppt Ideas Graphics Example. This template helps you present information on three stages. You can also present information on Cloud Access Security, Broker Working Process, Classification And Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud Security
Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud SecurityThis slide represents the benefits and drawbacks of proxy-based CASB deployment. The purpose of this slide is to showcase the various pros and cons of proxy-based cloud access security brokers and the advantages cover flexibility, secure SaaS applications, and so on. Increase audience engagement and knowledge by dispensing information using Advantages And Disadvantages Of Proxy Based Deployment CASB Cloud Security. This template helps you present information on two stages. You can also present information on Proxy Based Cloud Access Security, Advantages Cover Flexibility, Proxy Based Deployment, Encrypted Connections Or Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 CASB Cloud Security For Table Of Contents Ppt Ideas Graphics Download
CASB Cloud Security For Table Of Contents Ppt Ideas Graphics DownloadIntroducing CASB Cloud Security For Table Of Contents Ppt Ideas Graphics Download to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Security, Streamline Endpoint Protection Solution, Benefits Of Cloud Access Security, using this template. Grab it now to reap its full benefits.
-
 CASB Forward Proxy Deployment Use Cases CASB Cloud Security
CASB Forward Proxy Deployment Use Cases CASB Cloud SecurityThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using CASB Forward Proxy Deployment Use Cases CASB Cloud Security. This template helps you present information on two stages. You can also present information on Deploying Granular Access, Proxy Deployment Use Cases, Potential Security Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker Pillar Threat Protection CASB Cloud Security
Cloud Access Security Broker Pillar Threat Protection CASB Cloud SecurityThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Introducing Cloud Access Security Broker Pillar Threat Protection CASB Cloud Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker Pillar, Threat Protection Pillar, Machine Learning Algorithms, using this template. Grab it now to reap its full benefits.
-
 Primary Types Of Reverse Proxy Server Deployment CASB Cloud Security
Primary Types Of Reverse Proxy Server Deployment CASB Cloud SecurityThis slide outlines the main types of reverse proxy server deployment, covering regular reverse proxies and load balancers. The purpose of this slide is to showcase how both methods work to manage traffic and offer security features to organizations. Increase audience engagement and knowledge by dispensing information using Primary Types Of Reverse Proxy Server Deployment CASB Cloud Security. This template helps you present information on two stages. You can also present information on Regular Reverse Proxies, Load Balancers, Primary Types Of Reverse, Proxy Server Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Pros And Cons Of Api Scanning CASB Deployment CASB Cloud Security
Pros And Cons Of Api Scanning CASB Deployment CASB Cloud SecurityThis slide outlines the advantages and disadvantages of the API scanning cloud access security broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Introducing Pros And Cons Of Api Scanning CASB Deployment CASB Cloud Security to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Scanning Cloud Access Security, Broker Deployment Model, Scanning Deployment Model, using this template. Grab it now to reap its full benefits.
-
 Training Program For Cloud Access Security Broker CASB Cloud Security
Training Program For Cloud Access Security Broker CASB Cloud SecurityThis slide describes the training program for employees to implement cloud access security broke in an organization. The purpose of this slide is to highlight the training schedule for CASB deployment and the main components include agenda, system requirements, mode and cost of the training. Increase audience engagement and knowledge by dispensing information using Training Program For Cloud Access Security Broker CASB Cloud Security. This template helps you present information on one stages. You can also present information on Training Program For Employees, Cloud Access Security, System Requirements, Fast Internet Connection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Why CASB Is Important For Businesses CASB Cloud Security
Why CASB Is Important For Businesses CASB Cloud SecurityThis slide outlines the importance of CASB for different organizations. The purpose of this slide is to showcase the various reasons for businesses to invest in the cloud access security broker model, including increased cloud adoption, better security, compliance, and cost-effective and centralized management. Introducing Why CASB Is Important For Businesses CASB Cloud Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker Model, Cloud Adoption, Better Security, Compliance, using this template. Grab it now to reap its full benefits.


