Powerpoint Templates and Google slides for ATS
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Athlete Endorsement Deal Icon For Sports Brand
Athlete Endorsement Deal Icon For Sports BrandPresenting our set of slides with Athlete Endorsement Deal Icon For Sports Brand This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Athlete Endorsement Deal, Icon For Sports Brand.
-
 Key Elements Of Successful Athlete Endorsement Deal
Key Elements Of Successful Athlete Endorsement DealThis slide represents important elements assisting businesses to develop successful athlete endorsement deals. It includes various elements such as defining goals, conducting market research, negotiating terms, protecting rights, etc. Introducing our premium set of slides with Key Elements Of Successful Athlete Endorsement Deal Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Define Goals, Market Research, Negotiate Terms. So download instantly and tailor it with your information.
-
 Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks
Ethical Hacking And Network Security Security Measures To Prevent Phishing AttacksThis slide represents the security measures to prevent phishing attacks, such as using the spam filter, updating security software regularly, utilization of multi-factor authentication, and so on. Introducing Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Phishing Attacks, Spam Filter, Updating Security Software Regularly, Utilization Of Multi Factor Authentication, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Types Of Phishing Attack
Ethical Hacking And Network Security Types Of Phishing AttackThis slide represents the types of phishing attacks such a spear-phishing, clone phishing, whaling, BEC, vishing, and snowshoeing phishing. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Types Of Phishing Attack. This template helps you present information on three stages. You can also present information on Business Email Compromise, Clone Phishing, Snowshoeing, Phishing Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security What Is Phishing Attack
Ethical Hacking And Network Security What Is Phishing AttackThis slide represents what phishing attacks are and how phishers hoax people through emails, SMS, phone calls, and social media platforms. Introducing Ethical Hacking And Network Security What Is Phishing Attack to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Phishers Hoax, Social Media Platforms, System Hacking, Corporate Or Personal Data, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Infrastructure Icon To Prevent Malware Attacks
Cybersecurity Infrastructure Icon To Prevent Malware AttacksIntroducing our premium set of slides with Cybersecurity Infrastructure Icon To Prevent Malware Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Infrastructure, Icon To Prevent, Malware Attacks So download instantly and tailor it with your information.
-
 Implement Eco-Friendly Initiatives At Workplace Boosting Brand Image MKT SS V
Implement Eco-Friendly Initiatives At Workplace Boosting Brand Image MKT SS VThe following slide highlights some environment conscious practices to develop green ecosystem in organizations. It includes elements such as executing, recycling programs, saving energy, promoting green vendors, sustainable transportation, eco-friendly gifting etc. Increase audience engagement and knowledge by dispensing information using Implement Eco-Friendly Initiatives At Workplace Boosting Brand Image MKT SS V This template helps you present information on five stages. You can also present information on Execute Recycling Programs, Save Energy, Ecofriendly Gifting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Need For Sustainable Waste Management At Workplace Boosting Brand Image MKT SS V
Need For Sustainable Waste Management At Workplace Boosting Brand Image MKT SS VThe following slide illustrates the importance of sustainable waste management in organization to promote recycling programs and lower waste generation. It includes elements such as producing more space, saving money, boosting sustainability, reducing pollution, environmental conservation etc. Introducing Need For Sustainable Waste Management At Workplace Boosting Brand Image MKT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Produces Space, Saves Money, Boost Sustainability using this template. Grab it now to reap its full benefits.
-
 Key Principles Of Social Engineering Attack
Key Principles Of Social Engineering AttackThe purpose of this slide is to highlight how understanding key principles of social engineering attacks is crucial for developing effective defenses, promoting awareness, and safeguarding against manipulative tactics. Introducing our premium set of slides with Key Principles Of Social Engineering Attack. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Trust, Authority, Intimidation. So download instantly and tailor it with your information.
-
 Legal Implications Of Social Engineering Attacks
Legal Implications Of Social Engineering AttacksThe purpose of this slide is to highlight how understanding the legal implications of social engineering attacks is crucial for compliance, liability mitigation, and effective incident response, enhancing overall legal resilience. Presenting our set of slides with Legal Implications Of Social Engineering Attacks. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Fraud And Deception, Privacy Violations, Impersonation.
-
 Major Types Of Social Engineering Attacks
Major Types Of Social Engineering AttacksThe purpose of this slide is to highlight the importance of recognizing major social engineering attacks for developing effective defenses and proactive cybersecurity. Introducing our premium set of slides with Major Types Of Social Engineering Attacks. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Angler Phishing, Ear Phishing, Phishing. So download instantly and tailor it with your information.
-
 Social Engineering Attack Lifecycle Stages
Social Engineering Attack Lifecycle StagesThe purpose of this slide is to highlight how understanding social engineering attack lifecycle stages informs proactive defense, identifying vulnerabilities, raising awareness, and fortifying security measures at each critical phase. Introducing our premium set of slides with Social Engineering Attack Lifecycle Stages. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Concluding The Interaction, Information Acquisition, Mislead Targets. So download instantly and tailor it with your information.
-
 Social Engineering Attack Statistical Report
Social Engineering Attack Statistical ReportThe purpose of this slide is to show how a social engineering attack statistical report informs decision-making, risk assessment, and targeted security measures against evolving threats. Presenting our set of slides with Social Engineering Attack Statistical Report. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Engineering Breaches, Phishing Attacks, Social Engineering.
-
 Social Engineering Phishing Attacks Icon
Social Engineering Phishing Attacks IconIntroducing our premium set of slides with Social Engineering Phishing Attacks Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Social Engineering Phishing Attacks. So download instantly and tailor it with your information.
-
 Steps To Perform Social Engineering Attack
Steps To Perform Social Engineering AttackThe slide aims to succinctly outline the steps of a social engineering attack, revealing strategies to exploit human vulnerabilities for unauthorized access or information retrieval. Introducing our premium set of slides with Steps To Perform Social Engineering Attack. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Preparation, Infiltration, Exploitation. So download instantly and tailor it with your information.
-
 Tactics Used By Social Engineer Attackers
Tactics Used By Social Engineer AttackersThe purpose of this slide is to highlight how understanding tactics used by social engineer attackers provides crucial insights for developing targeted countermeasures and enhancing organizational security. Presenting our set of slides with Tactics Used By Social Engineer Attackers. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Likability For Manipulation, Commitment Trigger, Authority And Credibility.
-
 Tips To Prevent Social Engineering Attacks
Tips To Prevent Social Engineering AttacksThe purpose of this slide is to highlight how tips for preventing social engineering attacks empower individuals and organizations to recognize, resist, and mitigate threats, enhancing cybersecurity. Introducing our premium set of slides with Tips To Prevent Social Engineering Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Email Security, Authentication Practices, Beware Of Offers. So download instantly and tailor it with your information.
-
 Encourage Athletes To Post Behind The Scenes For Engaging Sports Event Marketing Strategy SS V
Encourage Athletes To Post Behind The Scenes For Engaging Sports Event Marketing Strategy SS VThis slide represents the details related to one of the strategies for effectively promoting sports events through social media platforms. It includes details related to overview, importance and impact of encouraging athletes to post behind-the-scenes for engaging fans. Increase audience engagement and knowledge by dispensing information using Encourage Athletes To Post Behind The Scenes For Engaging Sports Event Marketing Strategy SS V This template helps you present information on three stages. You can also present information on Overview, Importance, Engaging Fans using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies To Build Effective Brand Partnership With Athletes Sports Event Marketing Strategy SS V
Strategies To Build Effective Brand Partnership With Athletes Sports Event Marketing Strategy SS VThis slide represents techniques to be adopted by marketers for building effective brand partnerships for increasing brand recognition and boost customer loyalty. It includes strategies to develop brand partnerships such as identify right athlete etc. Increase audience engagement and knowledge by dispensing information using Strategies To Build Effective Brand Partnership With Athletes Sports Event Marketing Strategy SS V This template helps you present information on four stages. You can also present information on Unique Experiences, Charitable Causes, Identify Right Athlete using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Everything About Mobile Banking Cardless Atms As Emerging Trend In Mobile Banking Fin SS V
Everything About Mobile Banking Cardless Atms As Emerging Trend In Mobile Banking Fin SS VThis slide shows details regarding how users can withdraw money using cardless ATMs. It also includes information about the functioning of cardless ATMs which is facilitated via QR codes, NFC, verification code and biometric verification. Introducing Everything About Mobile Banking Cardless Atms As Emerging Trend In Mobile Banking Fin SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Verification Code, Biometric Verification, Emerging Trend In Mobile Banking, using this template. Grab it now to reap its full benefits.
-
 Everything About Mobile Banking Man In The Middle Mobile Banking Attack Methods Fin SS V
Everything About Mobile Banking Man In The Middle Mobile Banking Attack Methods Fin SS VThis slide shows overview of popular cyberattack related to mobile banking which is man in the middle MiTM. It also includes popular types of this attack which are WIFI network interception, DNS spoofing, email interception and malware. Present the topic in a bit more detail with this Everything About Mobile Banking Man In The Middle Mobile Banking Attack Methods Fin SS V. Use it as a tool for discussion and navigation on WIFI Network Interception, DNS Spoofing, Email Interception And Malware, Mobile Banking Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Business Development Services For Startups At Various Stages
Business Development Services For Startups At Various StagesThis slide shows business development services for organizations at different growth stages. The purpose of this slide is to help businesses in developing a strong marketinBusiness Development Services For Startups At Various Stages Business Development Services For Startups At Various Stages. This exhibits information on one stage of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Established Businesses, Successful Businesses, Marketing Strategies.
-
 Agenda For Social Engineering Attacks Prevention For Businesses
Agenda For Social Engineering Attacks Prevention For BusinessesIntroducing Agenda For Social Engineering Attacks Prevention For Businesses to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Attack, Prevention For Businesses, Social Engineering Lifecycle, Social Engineering Techniques, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Social Engineering Attacks Prevention For Businesses
Icons Slide For Social Engineering Attacks Prevention For BusinessesPresenting our well crafted Icons Slide For Social Engineering Attacks Prevention For Businesses set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Social Engineering Attacks Overview And Types Social Engineering Attacks Prevention
Social Engineering Attacks Overview And Types Social Engineering Attacks PreventionThis slide discusses about social engineering process of manipulating victims to provide access to their confidential information. This slide also outlines the types of social engineering attacks, such as phishing, pretexting, baiting, tailgating, impersonation, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Overview And Types Social Engineering Attacks Prevention. This template helps you present information on five stages. You can also present information on Quid Pro Quo Attack, Watering Hole Attack, Tailgating, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social Engineering
Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social EngineeringThis slide represents 30-60-90 plan to protect companies and their employees from social engineering attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Introducing Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social Engineering to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Simulation Test, Implement Continuous Monitoring, Third Party Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention About Anti Phishing Solutions Types And Benefits
Social Engineering Attacks Prevention About Anti Phishing Solutions Types And BenefitsThis slide highlights the services available for social engineering prevention, such as browser-based, email-based and API-based. This slide also outlines the benefits of these services. These include risk identification, damage control, zero-trust security, etc. Present the topic in a bit more detail with this Social Engineering Attacks Prevention About Anti Phishing Solutions Types And Benefits. Use it as a tool for discussion and navigation on Reduce Cybersecurity Attacks, Zero Trust Security, Deliver Operational Efficiency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Attacks Prevention Best Practices For Social Engineering Awareness Campaign
Social Engineering Attacks Prevention Best Practices For Social Engineering Awareness CampaignThis slide talks about the measures for successful social engineering awareness campaign. These include recognize phish, train staff while keeping their individual needs in mind, action-oriented employee engagement, plan constant training sessions, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Best Practices For Social Engineering Awareness Campaign. This template helps you present information on six stages. You can also present information on Plan Constant Training Sessions, Evaluate Training Outcomes, Consumable Tidbits Of Knowledge, Action Oriented Employee Engagement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Business Benefits Of Comprehensive Training Programs
Social Engineering Attacks Prevention Business Benefits Of Comprehensive Training ProgramsThis slide outlines the benefits of comprehensive training programs in organizations. These include align with company database, instructional library, auto-enrolment service, inform about real risks, track and evaluate and plan a year ahead. Introducing Social Engineering Attacks Prevention Business Benefits Of Comprehensive Training Programs to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Track And Evaluate, Instructional Library, Comprehensive Training Programs, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Checklist To Secure Organizations From Social Engineering
Social Engineering Attacks Prevention Checklist To Secure Organizations From Social EngineeringThis slide outlines the steps to be taken to protect the organization and its employees from social engineering attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real-time monitoring and develop an incident plan. Present the topic in a bit more detail with this Social Engineering Attacks Prevention Checklist To Secure Organizations From Social Engineering. Use it as a tool for discussion and navigation on Provide Staff Training, Multi Factor Authentication, Develop An Incident Response Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Attacks Prevention Common Attack Vectors For Social Engineering
Social Engineering Attacks Prevention Common Attack Vectors For Social EngineeringThis slide outlines the different components which result in successful social engineering attacks. These are software vulnerabilities, compromised credentials, weak passwords, malicious employees, poor encryption, ransomware, phishing, etc. Introducing Social Engineering Attacks Prevention Common Attack Vectors For Social Engineering to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Software Vulnerabilities, Compromised Credentials, Malicious Employees, Weak Passwords, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions Providers
Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions ProvidersThis slide compares the different anti-phishing solutions available in the market. It highlights the type of support provided, price and rating of various solutions. This slide also outlines the final service selection and the reasons supporting it. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Comparison Of Different Anti-Phishing Solutions Providers. Dispense information and present a thorough explanation of Anti Phishing Solutions, Final Service Selection, Reasons Supporting, Abnormal Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attacks Prevention Components Of Social Engineering Life Cycle
Social Engineering Attacks Prevention Components Of Social Engineering Life CycleThis slide represents the life cycle of the social engineering process. The main steps included are ground preparation for the attack, deceiving the victim to achieve a foothold, collecting the data over time, and closing the interaction without any suspicion. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Components Of Social Engineering Life Cycle. This template helps you present information on four stages. You can also present information on Ground Preparation For Attack, Collecting The Information, Social Engineering Life Cycle, Taking Control Of The Conversation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Different Types Of Social Engineering Attacks
Social Engineering Attacks Prevention Different Types Of Social Engineering AttacksThis slide represents the different types of social engineering attacks based on technology and human interaction. These two types are further divided into components such as mobile-based, computer-based, voice-based, physical mode, etc. Introducing Social Engineering Attacks Prevention Different Types Of Social Engineering Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Attacks, Physical Mode, Technology And Human Interaction, Email Phishing, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention For Businesses For Table Of Contents
Social Engineering Attacks Prevention For Businesses For Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention For Businesses For Table Of Contents. This template helps you present information on one stages. You can also present information on Resources And Training, Awareness Training Program, Training Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Human Based Social Engineering Attacks
Social Engineering Attacks Prevention Human Based Social Engineering AttacksThis slide discusses the different human-based techniques used by social engineering scammers. These attacks include impersonation, tailgating, baiting, pretexting, quid pro quo attacks, reverse social engineering and dumpster diving. Present the topic in a bit more detail with this Social Engineering Attacks Prevention Human Based Social Engineering Attacks. Use it as a tool for discussion and navigation on Reverse Social Engineering, Dumpster Diving, Social Engineering Attacks, Fraudulent Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Attacks Prevention Important Traits Of Social Engineering Attacks
Social Engineering Attacks Prevention Important Traits Of Social Engineering AttacksThe purpose of this slide is to outline the significant traits of a social engineering scam. The main points discussed in this slide are urgency, believability, trust, and heightened emotions such as fear, excitement, curiosity, sadness, guilt, etc. Introducing Social Engineering Attacks Prevention Important Traits Of Social Engineering Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Time Sensitive Opportunities, Believability, Heightened Emotions, Manipulated Emotions, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Main Goals Of Social Engineering Attackers
Social Engineering Attacks Prevention Main Goals Of Social Engineering AttackersThis slide highlights the motive of the scammers behind the social engineering attacks. The two primary goals discussed in this slide are disruption and theft. This slide also outlines several examples, such as ransomware, phishing attacks, impersonation, etc. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Main Goals Of Social Engineering Attackers. Dispense information and present a thorough explanation of Social Engineering Attackers, Phishing Attacks, Distributed Denial Of Service, Aims To Corrupt Data Or Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attacks Prevention Ontological Model Of Social Engineering Attack
Social Engineering Attacks Prevention Ontological Model Of Social Engineering AttackThe purpose of this slide is to represent the model of a social engineering attack which consists of several components. The major points depicted in this slide are social engineer, medium, goal, target, compliance principles, techniques, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Ontological Model Of Social Engineering Attack. This template helps you present information on six stages. You can also present information on Direct Communication, Bidirectional Communication, Unidirectional Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Red Flags Of A Social Engineering Attack
Social Engineering Attacks Prevention Red Flags Of A Social Engineering AttackThis slide highlights the signs of a social engineering attack. The purpose of this slide is to outline the various symptoms of cyber attack, such as strange messages from a friend, arouse emotions, create a sense of urgency, tempting offers, etc. Introducing Social Engineering Attacks Prevention Red Flags Of A Social Engineering Attack to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Attack, Arouse Emotions, Arouse Emotions Like Fear, Arouse Emotions, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Resources And Training Provided To Employees In Organization
Social Engineering Attacks Prevention Resources And Training Provided To Employees In OrganizationThis slide demonstrates the resources and training that can be provided by companies to their staff. These include employee training, check to see if you have already been breached, be aware of the various phishing attacks, invest in security education, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Resources And Training Provided To Employees In Organization. This template helps you present information on five stages. You can also present information on Invest In Security Education, Invest In Password, Employee Training, Phishing Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Roadmap To Implement Social Engineering Prevention Strategies
Social Engineering Attacks Prevention Roadmap To Implement Social Engineering Prevention StrategiesThis slide represents the roadmap to prevent social engineering attacks in organizations. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Attacks Prevention Roadmap To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Establish Policies And Procedures, Implement Technical Controls, Social Engineering Prevention Strategies, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Sciences Involved In Targeting Humans In Modern Social
Social Engineering Attacks Prevention Sciences Involved In Targeting Humans In Modern SocialThis slide highlights the key sciences involved in the process of modern social engineering. These are psychology, pedagogy, cognitive sciences, psychiatry, marketing, communication sciences, philosophy, normative processes, organizational sociology, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Sciences Involved In Targeting Humans In Modern Social. This template helps you present information on thirteen stages. You can also present information on Modern Social Engineering, Psychology, Pedagogy, Cognitive Sciences, Psychiatry, Marketing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Social Engineering Awareness Training Program For Employees
Social Engineering Attacks Prevention Social Engineering Awareness Training Program For EmployeesThis slide represents the training program for employees which will help them to prevent various cyber security scams in business. The purpose of this slide is to outline the mode, venue and schedule for the different training programs. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Social Engineering Awareness Training Program For Employees. Dispense information and present a thorough explanation of Social Engineering Awareness, Training Program For Employees, Training Programs, Cyber Security Scams using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attacks Prevention Social Engineering Classification Chart Overview
Social Engineering Attacks Prevention Social Engineering Classification Chart OverviewIntroducing Social Engineering Attacks Prevention Social Engineering Classification Chart Overview to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Ingratiation, Instant Messaging, Waste Threats Management, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Social Engineering Methods Used By Attackers
Social Engineering Attacks Prevention Social Engineering Methods Used By AttackersThis slide demonstrates the popular procedures for conducting social engineering scams. These methods of performing social engineering attacks are phone calls, in-person interactions, tailgating, persuasion through third-party applications, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Social Engineering Methods Used By Attackers. This template helps you present information on four stages. You can also present information on Guide Them To Phishing Websites, Attackers Call Targets, Scammers Act As Employees, Fictitious Positions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network Use
Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network UseThis slide represents the protective measures for users to practice safe networking. The best practices mentioned in this slide are restrict others from connecting to primary wi-fi network, use a VPN, security of network-connected devices, etc. Introducing Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network Use to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Practice Safe Networking, Primary Wifi Network, Security Of Network Connected Devices, Social Engineering Prevention Strategies, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Step By Step Process Of Social Engineering Awareness Program
Social Engineering Attacks Prevention Step By Step Process Of Social Engineering Awareness ProgramThis slide demonstrates the working of cyber security awareness training programs for organizations. These include start with employee training, make fictitious cyber attack campaigns, reinforce the awareness training and track progress and upgrade. Increase audience engagement and knowledge by dispensing information using Social Engineering Attacks Prevention Step By Step Process Of Social Engineering Awareness Program. This template helps you present information on four stages. You can also present information on Awareness Training Program, Cyber Attack Campaigns, Start With Employee Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Attacks Prevention Technology Based Social Engineering Attacks
Social Engineering Attacks Prevention Technology Based Social Engineering AttacksThis slide discusses the different technology-based techniques used by social engineering scammers. These attacks include phishing, vishing, smishing, watering hole attacks, man-in-the-middle attacks, scareware and angler phishing. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Technology Based Social Engineering Attacks. Dispense information and present a thorough explanation of Watering Hole Attacks, Social Engineering Attacks, Angler Phishing, Fraudsters Fake Trusted Phone using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
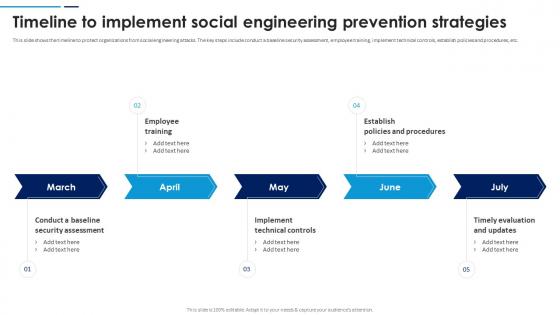 Social Engineering Attacks Prevention Timeline To Implement Social Engineering Prevention Strategies
Social Engineering Attacks Prevention Timeline To Implement Social Engineering Prevention StrategiesThis slide shows the timeline to protect organizations from social engineering attacks. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Attacks Prevention Timeline To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Establish Policies And Procedures, Timely Evaluation And Updates, Implement Technical Controls, Employee Training, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Understanding Social Engineering Threat Landscape
Social Engineering Attacks Prevention Understanding Social Engineering Threat LandscapeThis slide shows the threat landscape for social engineering. The key components included are email, social media and the internet, trends, criminal groups, malicious insiders, and attack vectors such as physical on-site attacks, mobile, network, cloud, etc. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Understanding Social Engineering Threat Landscape. Dispense information and present a thorough explanation of Social Media And Internet, Social Engineering Threat Landscape, Search Result Poisoning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Prevention Strategies For Safe Communication Social Engineering Attacks Prevention
Social Engineering Prevention Strategies For Safe Communication Social Engineering Attacks PreventionThis slide discusses several social engineering mitigation techniques. These include avoid clicking on links in emails and texts, use multi-factor authentication, select strong passwords, avoid sharing personal information, beware of internet friendships, etc. Introducing Social Engineering Prevention Strategies For Safe Communication Social Engineering Attacks Prevention to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering Prevention, Strategies For Safe Communication, Multi Factor Authentication, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Prevention Strategies For Safe Device Usage Social Engineering Attacks Prevention
Social Engineering Prevention Strategies For Safe Device Usage Social Engineering Attacks PreventionThe purpose of this slide is to represent the best practices for safe device usage. These safety measures include internet security software, never leave devices unsecured in public places, keep software updated and inspect all internet accounts. Increase audience engagement and knowledge by dispensing information using Social Engineering Prevention Strategies For Safe Device Usage Social Engineering Attacks Prevention. This template helps you present information on four stages. You can also present information on Internet Security Software, Keep Software Updated, Inspect All Internet Accounts, Devices Unsecured In Public using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Social Engineering Attacks Prevention For Businesses
Table Of Contents For Social Engineering Attacks Prevention For BusinessesIntroducing Table Of Contents For Social Engineering Attacks Prevention For Businesses to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Lifecycle And Process, Social Engineering Introduction, Attack Targets And Vectors, Statistics Of Social Engineering Scams, using this template. Grab it now to reap its full benefits.
-
 ATM Machines Van Colored Icon In Powerpoint Pptx Png And Editable Eps Format
ATM Machines Van Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon depicts a bank van, ideal for presentations on financial topics. It is a vector graphic with a bright, cheerful colour palette and is available in both PNG and SVG formats.
-
 ATM Machines Van Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
ATM Machines Van Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon depicts a bank van, perfect for presentations on banking, finance, and money management. It is a high quality vector image, suitable for both digital and print projects.
-
 Classification Of Attacks Based On 5g Iot Architecture Layers
Classification Of Attacks Based On 5g Iot Architecture LayersThis Slide Shows Classifying Attacks Based On 5G Iot Architecture Layers To Improve Network Security. It Further Includes Physical Device Layer, Communication Layer, Edge Computing Layer Etc. Presenting Our Set Of Slides With Classification Of Attacks Based On 5g Iot Architecture Layers. This Exhibits Information On Seven Stages Of The Process. This Is An Easy To Edit And Innovatively Designed Powerpoint Template. So Download Immediately And Highlight Information On Data Storage Layer, Management Service Layer, Collaboration And Processes Layer.
-
 Cardless ATMs As Emerging Trend Smartphone Banking For Transferring Funds Digitally Fin SS V
Cardless ATMs As Emerging Trend Smartphone Banking For Transferring Funds Digitally Fin SS VThis slide shows details regarding how users can withdraw money using cardless ATMs. It also includes information about the functioning of cardless ATMs which is facilitated via QR codes, NFC, verification code and biometric verification. Present the topic in a bit more detail with this Cardless ATMs As Emerging Trend Smartphone Banking For Transferring Funds Digitally Fin SS V. Use it as a tool for discussion and navigation on Qr Codes, Verification Code, Biometric Verification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Atmospheric Pressure Dimensional In Powerpoint And Google Slides Cpb
Atmospheric Pressure Dimensional In Powerpoint And Google Slides CpbPresenting our Atmospheric Pressure Dimensional In Powerpoint And Google Slides Cpb. PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Atmospheric Pressure Dimensional. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Valerian Root Heart Attack In Powerpoint And Google Slides Cpb
Valerian Root Heart Attack In Powerpoint And Google Slides CpbPresenting our Valerian Root Heart Attack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Valerian Root Heart Attack This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.





