Powerpoint Templates and Google slides for ATS
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Innovation icon in atom shape
Innovation icon in atom shapePresenting Innovation Icon In Atom Shape template. The slide is completely editable in PowerPoint and other office suites. The layout is compatible with Google Slides. Modify the slideshow according to the presentation requirement. You can include your company name, logo or brand symbol with ease. This template can be saved in multiple images and document formats such as JPG, PDF, etc. without any difficulty. High-quality graphics ensure that quality is not affected.
-
 Banking product icon atm cards white colors
Banking product icon atm cards white colorsPresenting banking product icon atm cards white colors. This is a banking product icon atm cards white colors. This is a one stage process. The stages in this process are banking product icons, financial product icons.
-
 Banking product icon atm machine white outline
Banking product icon atm machine white outlinePresenting this Banking Product Icon ATM Machine White Outline PowerPoint presentation. Include charts and graphs for a wonderful representation of information. The slide supports the standard and widescreen sizes for clarity. It is also compatible with Google Slides. Convert this into popular images or document formats such as JPEG, PNG or PDF. High-quality graphics ensure that quality does not hamper at any cost.
-
 Banking product icon atm machine with cash
Banking product icon atm machine with cashPresenting banking product icon atm machine with cash. This is a banking product icon atm machine with cash. This is a one stage process. The stages in this process are banking product icons, financial product icons.
-
 Banking product icon two atm cards
Banking product icon two atm cardsPresenting banking product icon two atm cards. This is a banking product icon two atm cards. This is a one stage process. The stages in this process are banking product icons, financial product icons.
-
 Sunset at beach with tree
Sunset at beach with treePresenting sunset at beach with tree. This is a sunset at beach with tree. This is a two stage process. The stages in this process are sunset icon, sun down icon, evening icon.
-
 Benchmarking global supply chain global supply chain atom economy
Benchmarking global supply chain global supply chain atom economyPresenting this set of slides with name - Benchmarking Global Supply Chain Global Supply Chain Atom Economy. This is an editable four graphic that deals with topics like benchmarking global supply chain, global supply chain, atom economy to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Automation icon with the gear attached
Automation icon with the gear attachedPresenting this set of slides with name - Automation Icon With The Gear Attached. This is a three stage process. The stages in this process are Automation Icon, Computerization Icon, Mechanization Icon.
-
 Smart icon attainable showing man on mountain
Smart icon attainable showing man on mountainPresenting this set of slides with name - Smart Icon Attainable Showing Man On Mountain. This is a one stage process. The stages in this process are Smart Icon, Intelligent Icon, Imagination Icon, Brain Icon.
-
 Performance service advertising incentives personal attention community relationship
Performance service advertising incentives personal attention community relationshipPresenting this set of slides with name - Performance Service Advertising Incentives Personal Attention Community Relationship. This is an editable five stages graphic that deals with topics like Performance Service, Advertising Incentives, Personal Attention, Community Relationship to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Marginally attached worker conference board job availability ethics tribes
Marginally attached worker conference board job availability ethics tribesPresenting this set of slides with name - Marginally Attached Worker Conference Board Job Availability Ethics Tribes. This is an editable five stages graphic that deals with topics like Marginally Attached Worker, Conference Board Job Availability, Ethics Tribes to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Appendix icon attached document business papers
Appendix icon attached document business papersPresenting this set of slides with name - Appendix Icon Attached Document Business Papers. This is a four stage process. The stages in this process are Supplement Icon, Addendum Icon, Appendix Icon.
-
 Appendix icon attached document business records
Appendix icon attached document business recordsPresenting this set of slides with name - Appendix Icon Attached Document Business Records. This is a three stage process. The stages in this process are Supplement Icon, Addendum Icon, Appendix Icon.
-
 Appendix icon attachment document binder
Appendix icon attachment document binderPresenting this set of slides with name - Appendix Icon Attachment Document Binder. This is a three stage process. The stages in this process are Supplement Icon, Addendum Icon, Appendix Icon.
-
 Bank atm icon with human and dollar image
Bank atm icon with human and dollar imagePresenting this set of slides with name - Bank Atm Icon With Human And Dollar Image. This is a two stage process. The stages in this process are Bank Icon, Finance Icons, Money Icon.
-
 Specific attack strategies customer size specialist fastest source
Specific attack strategies customer size specialist fastest sourcePresenting this set of slides with name - Specific Attack Strategies Customer Size Specialist Fastest Source. This is an editable five stages graphic that deals with topics like Specific Attack Strategies, Customer Size Specialist, Fastest Source to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Bomb icon atomic nuclear with fins
Bomb icon atomic nuclear with finsPresenting this set of slides with name - Bomb Icon Atomic Nuclear With Fins. This is a one stage process. The stages in this process are Blast Icon, Bomb Icon, Explode Icon.
-
 Defining multiple views natural language interfaces native language attempt
Defining multiple views natural language interfaces native language attemptPresenting this set of slides with name - Defining Multiple Views Natural Language Interfaces Native Language Attempt. This is an editable two stages graphic that deals with topics like Defining Multiple Views, Natural Language Interfaces, Native Language Attempt to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Long waves moving atoms information technology business steering
Long waves moving atoms information technology business steeringPresenting this set of slides with name - Long Waves Moving Atoms Information Technology Business Steering. This is an editable four stages graphic that deals with topics like Long Waves, Moving Atoms, Information Technology Business Steering to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Minutes personal attention great job warm smiles excellent holiday cookies
Minutes personal attention great job warm smiles excellent holiday cookiesPresenting this set of slides with name - Minutes Personal Attention Great Job Warm Smiles Excellent Holiday Cookies. This is a eleven stage process. The stages in this process are Minutes Personal, Attention, Great Job, Warm Smiles, Excellent Holiday Cookies.
-
 Recognition minutes of personal attention great job
Recognition minutes of personal attention great jobPresenting this set of slides with name - Recognition Minutes Of Personal Attention Great Job. This is a eleven stage process. The stages in this process are Great Job, Excellent, Shout Out, High Fives, Warm Smiles.
-
 Purchases investment banking cyber security attacks marketing board cpb
Purchases investment banking cyber security attacks marketing board cpbPresenting this set of slides with name - Purchases Investment Banking Cyber Security Attacks Marketing Board Cpb. This is an editable three stages graphic that deals with topics like Purchases, Investment Banking, Cyber Security Attacks, Marketing Board to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Project cost estimate budget quality analysis marketing attack strategies cpb
Project cost estimate budget quality analysis marketing attack strategies cpbPresenting this set of slides with name - Project Cost Estimate Budget Quality Analysis Marketing Attack Strategies Cpb. This is an editable four stages graphic that deals with topics like Project Cost Estimate Budget, Quality Analysis , Marketing Attack Strategies to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Appendix icon closed pin attachment documents paperclip
Appendix icon closed pin attachment documents paperclipPresenting this set of slides with name - Appendix Icon Closed Pin Attachment Documents Paperclip. This is a one stage process. The stages in this process are Appendix Icon, Medical Icon, Health Icon.
-
 Appendix icon paperclip in the circle attachment
Appendix icon paperclip in the circle attachmentPresenting this set of slides with name - Appendix Icon Paperclip In The Circle Attachment. This is a one stage process. The stages in this process are Appendix Icon, Medical Icon, Health Icon.
-
 Appendix icon pin attachment copy round
Appendix icon pin attachment copy roundPresenting this set of slides with name - Appendix Icon Pin Attachment Copy Round. This is a one stage process. The stages in this process are Appendix Icon, Medical Icon, Health Icon.
-
 Atm icon machine having side buttons
Atm icon machine having side buttonsPresenting this set of slides with name - Atm Icon Machine Having Side Buttons. This is a three stages process. The stages in this process are Atm Icon, Payment Card Icon, Bank Card Icon.
-
 Atm icon machine with keypad and cash slot
Atm icon machine with keypad and cash slotPresenting this set of slides with name - Atm Icon Machine With Keypad And Cash Slot. This is a four stages process. The stages in this process are Atm Icon, Payment Card Icon, Bank Card Icon.
-
 Atm icon man withdrawing cash from machine
Atm icon man withdrawing cash from machinePresenting this set of slides with name - Atm Icon Man Withdrawing Cash From Machine. This is a four stages process. The stages in this process are Atm Icon, Payment Card Icon, Bank Card Icon.
-
 Atm icon showing machine with cash
Atm icon showing machine with cashPresenting this set of slides with name - Atm Icon Showing Machine With Cash. This is a four stages process. The stages in this process are Atm Icon, Payment Card Icon, Bank Card Icon.
-
 Atm icon with multiple buttons and screen
Atm icon with multiple buttons and screenPresenting this set of slides with name - Atm Icon With Multiple Buttons And Screen. This is a three stages process. The stages in this process are Atm Icon, Payment Card Icon, Bank Card Icon.
-
 Alignment icon with object at bottom
Alignment icon with object at bottomPresenting this set of slides with name - Alignment Icon With Object At Bottom. This is a three stages process. The stages in this process are Alignment Icon, Arrangement Icon, Put In Order Icon.
-
 Portfolio value at risk ppt powerpoint presentation outline background
Portfolio value at risk ppt powerpoint presentation outline backgroundPresenting this set of slides with name - Portfolio Value At Risk Ppt Powerpoint Presentation Outline Background. This is a five stages process. The stages in this process are Business, Management, Planning, Strategy, Marketing.
-
 Portfolio value at risk ppt powerpoint presentation outline show
Portfolio value at risk ppt powerpoint presentation outline showPresenting this set of slides with name - Portfolio Value At Risk Ppt Powerpoint Presentation Outline Show. This is a five stage process. The stages in this process are Equity, Fixed Income, Private Real Estate, Hedge Fund, Correlation.
-
 Customer support executive icon at end of all ivr responses
Customer support executive icon at end of all ivr responsesPresenting this set of slides with name - Customer Support Executive Icon At End Of All Ivr Responses. This is a four stage process. The stages in this process are IVR Icon, Mobile Icon, Technology.
-
 Ivr responses icon showing respondent at end
Ivr responses icon showing respondent at endPresenting this set of slides with name - Ivr Responses Icon Showing Respondent At End. This is a four stage process. The stages in this process are IVR Icon, Mobile Icon, Technology.
-
 Impact of procrastination at workplace ppt styles background images
Impact of procrastination at workplace ppt styles background imagesPresenting this set of slides with name - Impact Of Procrastination At Workplace Ppt Styles Background Images. This is a six stage process. The stages in this process are Poor Employee Performance, Missed Opportunities, Increased Wasted Time.
-
 Impact of procrastination at workplace ppt powerpoint presentation design templates
Impact of procrastination at workplace ppt powerpoint presentation design templatesPresenting this set of slides with name - Impact Of Procrastination At Workplace Ppt Powerpoint Presentation Design Templates. This is a six stages process. The stages in this process are Increased Stressed Level, Missed Opportunities, Increased Wasted Time, Poor Employee Performance, Business.
-
 Our mission audience attention f14 ppt powerpoint presentation file graphics
Our mission audience attention f14 ppt powerpoint presentation file graphicsPresenting this set of slides with name Our Mission Audience Attention F14 Ppt Powerpoint Presentation File Graphics. This is a three stage process. The stages in this process are Our Vision, Mission, Goal, Business, Strategy . This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Employee assessment form attendance punctuality ppt powerpoint presentation
Employee assessment form attendance punctuality ppt powerpoint presentationPresenting this set of slides with name Employee Assessment Form Attendance Punctuality Ppt Powerpoint Presentation. The topics discussed in these slides are Work Quality, Attendance, Punctuality, Communication, Listening Skills. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Comparison audience attention ppt powerpoint presentation pictures slide portrait
Comparison audience attention ppt powerpoint presentation pictures slide portraitPresenting this set of slides with name Comparison Audience Attention Ppt Powerpoint Presentation Pictures Slide Portrait. This is a two stage process. The stages in this process are Compare, Marketing, Business, Management, Planning. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
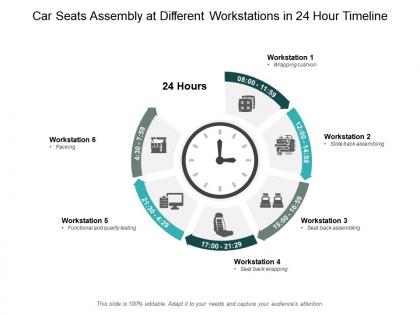 Car seats assembly at different workstations in 24 hour timeline
Car seats assembly at different workstations in 24 hour timelinePresenting this set of slides with name Car Seats Assembly At Different Workstations In 24 Hour Timeline. This is a six stage process. The stages in this process are 24 Hour Timeline, Quality Check, Warehouse. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Matrix audience attention ppt powerpoint presentation pictures infographic template
Matrix audience attention ppt powerpoint presentation pictures infographic templatePresenting this set of slides with name Matrix Audience Attention Ppt Powerpoint Presentation Pictures Infographic Template. This is a four stage process. The stages in this process are Marketing, Business, Management, Planning, Strategy. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Responsibility to customers audiences attention ppt powerpoint presentation icon smartart
Responsibility to customers audiences attention ppt powerpoint presentation icon smartartPresenting this set of slides with name Responsibility To Customers Audiences Attention Ppt Powerpoint Presentation Icon Smartart. This is a six stage process. The stages in this process are Our Team, Communication, Management, Business, Planning. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Preventive Measures For Man In The Middle Phishing Attacks And Strategies
Preventive Measures For Man In The Middle Phishing Attacks And StrategiesThis slide outlines the various methods of preventing man in the middle cyber attacks. The purpose of this slide is to explain how users can protect themselves from MITM scams. These include secure connections, avoid phishing emails, endpoint security, etc.Introducing Preventive Measures For Man In The Middle Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Secure Connections, Avoid Phishing Emails, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And Strategies
Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And StrategiesThis slide outlines the various preventive measures to avoid evil twin attacks. The key steps include use your own hotspot, avoid unsecured wi fis, disable auto connect, avoid logging into private accounts on public Wi Fi, use VPN, visit HTTPS websites, etc.Increase audience engagement and knowledge by dispensing information using Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And Strategies. This template helps you present information on seven stages. You can also present information on Appropriate Security Mechanisms, Transfer Protocol Secure, Accessing Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Preventive Measures To Avoid Watering Hole Phishing Attacks And Strategies
Preventive Measures To Avoid Watering Hole Phishing Attacks And StrategiesThis slide outlines the various preventive measures to avoid watering hole phishing attacks. The purpose of this slide is to help in protecting users from watering hole scams. The key steps include vulnerability scanning, security patches, input validation, etc.Introducing Preventive Measures To Avoid Watering Hole Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Scanning, Input Validation, Security Patches, using this template. Grab it now to reap its full benefits.
-
 Real World Examples Of Watering Hole Attacks Phishing Attacks And Strategies
Real World Examples Of Watering Hole Attacks Phishing Attacks And StrategiesThis slide describes the real world examples of watering hole phishing scams. These include Facebook, Twitter, Microsoft, and Apple scam, LuckyMouse scam, International Civil Aviation OrganizationICAO scam, Ccleaner scam and Holy Water scam.Increase audience engagement and knowledge by dispensing information using Real World Examples Of Watering Hole Attacks Phishing Attacks And Strategies. This template helps you present information on one stage. You can also present information on Ccleaner Scam, International Civil Aviation, Luckymouse Scam using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Resources And Training That Companies Can Phishing Attacks And Strategies
Resources And Training That Companies Can Phishing Attacks And StrategiesThis slide demonstrates the resources and training that can be provided by companies to their staff. These include employee training, check to see if you have already been breached, be aware of the various phishing attacks, invest in security education, etc.Introducing Resources And Training That Companies Can Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, Security Education, Password Manager, using this template. Grab it now to reap its full benefits.
-
 Steps To Take After Clicking Spear Phishing Link Phishing Attacks And Strategies
Steps To Take After Clicking Spear Phishing Link Phishing Attacks And StrategiesThis slide illustrates the steps to be taken immediately after falling for a spear phishing scam. The purpose of this slide is to outline the various steps such as disconnect from internet, backup your files, change your passwords and conduct a hardware scan.Increase audience engagement and knowledge by dispensing information using Steps To Take After Clicking Spear Phishing Link Phishing Attacks And Strategies. This template helps you present information on four stages. You can also present information on Two Factor Authentication, Data Immediately, Ethernet Cable using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies To Identify Smishing Cyber Scams Phishing Attacks And Strategies
Strategies To Identify Smishing Cyber Scams Phishing Attacks And StrategiesThis slide talks about the various methods of identifying smishing cyber attacks. The purpose of this slide is to help users identify smishing scams. These include suspicious texts from unknown numbers, unrequested links and files, money transfer requests, etc.Present the topic in a bit more detail with this Strategies To Identify Smishing Cyber Scams Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Requests Asking, Transfer Requests, Notifications Stating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies
Techniques Used By Cybercriminals To Conduct Phishing Attacks And StrategiesThis slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross site scripting, DMS cache poisoning, drive by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods.Deliver an outstanding presentation on the topic using this Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Demographic Information, Social Engineering, Include Dangerous using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tools Provided By Google To Prevent Phishing Attacks And Strategies
Tools Provided By Google To Prevent Phishing Attacks And StrategiesThis slide demonstrates the different tools provided by Google to prevent and report cyber phishing scams. These include to spot phishing mails with the help of Gmail, utilize safe browsing in chrome, look for unsafe saved passwords, password alert for chrome, etc.Deliver an outstanding presentation on the topic using this Tools Provided By Google To Prevent Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Saved Passwords, Notifications Concerning, Ever Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tricks Employed By Malicious Websites To Phishing Attacks And Strategies
Tricks Employed By Malicious Websites To Phishing Attacks And StrategiesThis slide talks about various tricks utilized by fraudulent websites to scam the visitors. The purpose of this slide is to make users aware of such different tricks such as freeordiscount offers, low interest ratesorfree credit cards, employment opportunities, etc.Introducing Tricks Employed By Malicious Websites To Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Fictitious Businesses, Feel Emergency, Emergency Warnings, using this template. Grab it now to reap its full benefits.
-
 Vishing Attacks Prevention Email Signing phishing Attacks And Strategies
Vishing Attacks Prevention Email Signing phishing Attacks And StrategiesThis slide talks about the techniques which can help in protecting organizations from phishing and vishing attacks. The purpose of this slide is to explain two important methods of preventing cyber scams. These techniques are email signing and code signing.Deliver an outstanding presentation on the topic using this Vishing Attacks Prevention Email Signing phishing Attacks And Strategies. Dispense information and present a thorough explanation of Malicious Software, Code Signing, Code Signing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Warning Signs To Recognize Phishing Email Phishing Attacks And Strategies
Warning Signs To Recognize Phishing Email Phishing Attacks And StrategiesThis slide talks about the warning signs that can help the user to recognize phishing email. The purpose of this slide is to outline the signs of phishing mails such as no greeting, misleading hyperlinks, unauthorized attachments, spelling and grammatical errors, etc.Deliver an outstanding presentation on the topic using this Warning Signs To Recognize Phishing Email Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Information Immediately, Unauthorised Attachments, Generic Greeting using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Why Businesses Fall Victim To Phishing Attacks Phishing Attacks And Strategies
Why Businesses Fall Victim To Phishing Attacks Phishing Attacks And StrategiesThis slide outlines the various reasons responsible for businesses to fall victim to different phishing attacks. These include inadequate employee training, never evaluate the success of the training, careless browsing habits of the employees, etc.Introducing Why Businesses Fall Victim To Phishing Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Careless Browsing, Policy Improvement, Inadequate Employee Training, using this template. Grab it now to reap its full benefits.
-
 Working Of Watering Hole Phishing Attack Phishing Attacks And Strategies
Working Of Watering Hole Phishing Attack Phishing Attacks And StrategiesThis slide represents the working process of watering hole phishing attacks. The purpose of this slide is to illustrate the flow diagram of watering hole phishing scams. The key points include research and identification, analysis, preparation and execution.Introducing Working Of Watering Hole Phishing Attack Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Watering Hole Cyberattack, Employ Exploit, Subdomain Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
 Working Procedure Of Spear Phishing Attack Phishing Attacks And Strategies
Working Procedure Of Spear Phishing Attack Phishing Attacks And StrategiesThis slide illustrates the structure of spear phishing attack. The purpose of this slide is to explain the working flow of spear phishing attack. The key components include attacker, phishing email, targeted users, exploited system, internal network, etc.Increase audience engagement and knowledge by dispensing information using Working Procedure Of Spear Phishing Attack Phishing Attacks And Strategies. This template helps you present information on seven stages. You can also present information on Attacker Distributes, Attachments Targeted, Fraudulent Attachments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Working Process Of Evil Twin Phishing Attack Phishing Attacks And Strategies
Working Process Of Evil Twin Phishing Attack Phishing Attacks And StrategiesThis slide represents the working of evil twin phishing attacks. The key points include set up evil twin fake access point, set up a fake captive portal, push users to sign into evil twin wi fi and steal victims personal information and login credentials.Deliver an outstanding presentation on the topic using this Working Process Of Evil Twin Phishing Attack Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Personal Information, Captive Portal, Manipulate Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.




