Powerpoint Templates and Google slides for ATS
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Headspace investor funding competitive analysis at business level ppt slides maker
Headspace investor funding competitive analysis at business level ppt slides makerThe following slide depicts the competitive analysis at a business level at it highlights the key details of the competitors such as, name of competitor, their financing status, their location and the total number of employees etc. Present the topic in a bit more detail with this Headspace Investor Funding Competitive Analysis At Business Level Ppt Slides Maker. Use it as a tool for discussion and navigation on Financing Status, Location, Employees, Total Raised, Last Financing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comprehensive Framework For Athlete Increasing Brand Outreach Marketing Campaigns MKT SS V
Comprehensive Framework For Athlete Increasing Brand Outreach Marketing Campaigns MKT SS VThis slide showcases framework which can guide sporting brands for constructing athlete brands. It provides details about antecedents, media, oral communication, social agents, impressions, team and sport, on-field attributes, off-field attributes, etc. Present the topic in a bit more detail with this Comprehensive Framework For Athlete Increasing Brand Outreach Marketing Campaigns MKT SS V. Use it as a tool for discussion and navigation on Comprehensive, Framework, Brand Construction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Marketing Brand And Products At Soccer Increasing Brand Outreach Marketing Campaigns MKT SS V
Marketing Brand And Products At Soccer Increasing Brand Outreach Marketing Campaigns MKT SS VThe following slide showcases growth drivers and opportunities which can guide brands to market their products at soccer events. It provides information about leverage engagement, tell brand story, reach new market, etc. Deliver an outstanding presentation on the topic using this Marketing Brand And Products At Soccer Increasing Brand Outreach Marketing Campaigns MKT SS V. Dispense information and present a thorough explanation of Marketing, Communities, Leverage Engagement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Athlete Branding Search Engine Sporting Brand Comprehensive Advertising Guide MKT SS V
Athlete Branding Search Engine Sporting Brand Comprehensive Advertising Guide MKT SS VThis slide showcases key techniques which can help improve search engine optimization SEO of athlete branding. It provides details about technical optimization, on-page SEO, off-page SEO, merchandise sales, increased visibility, relevant content, etc. Present the topic in a bit more detail with this Athlete Branding Search Engine Sporting Brand Comprehensive Advertising Guide MKT SS V. Use it as a tool for discussion and navigation on Optimization, Engagement, Promotions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comprehensive Framework For Athlete Brand Sporting Brand Comprehensive Advertising Guide MKT SS V
Comprehensive Framework For Athlete Brand Sporting Brand Comprehensive Advertising Guide MKT SS VThis slide showcases framework which can guide sporting brands for constructing athlete brands. It provides details about antecedents, media, oral communication, social agents, impressions, team and sport, on-field attributes, off-field attributes, etc. Present the topic in a bit more detail with this Comprehensive Framework For Athlete Brand Sporting Brand Comprehensive Advertising Guide MKT SS V. Use it as a tool for discussion and navigation on Comprehensive, Framework, Construction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Marketing Brand And Products At Sporting Brand Comprehensive Advertising Guide MKT SS V
Marketing Brand And Products At Sporting Brand Comprehensive Advertising Guide MKT SS VThe following slide showcases growth drivers and opportunities which can guide brands to market their products at soccer events. It provides information about leverage engagement, tell brand story, reach new market, etc. Present the topic in a bit more detail with this Marketing Brand And Products At Sporting Brand Comprehensive Advertising Guide MKT SS V. Use it as a tool for discussion and navigation on Leverage Engagement, Marketing, Products. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Of Deib Model At Workplace Managing Diversity And Inclusion
Implementation Of Deib Model At Workplace Managing Diversity And InclusionThis slide includes goals for the organization to hire and include diverse workforce for better growth opportunities. This could be achieved by hiring people from different geographies, hire people of all colors, increase women participation at all levels etc. Deliver an outstanding presentation on the topic using this Implementation Of Deib Model At Workplace Managing Diversity And Inclusion. Dispense information and present a thorough explanation of Diversity Metrics, Inclusion Metrics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Development Courses For Leaders ESCI Model For Assessing Leadership Skills At Functional Level
Development Courses For Leaders ESCI Model For Assessing Leadership Skills At Functional LevelThe following slide showcases the leadership assessment based on emotional and social competency inventory ESCI model. The model is used by organizations to track individual and group level emotional and social competency score. Deliver an outstanding presentation on the topic using this Development Courses For Leaders ESCI Model For Assessing Leadership Skills At Functional Level. Dispense information and present a thorough explanation of Leadership Assessment, Emotional And Social Competency Inventory, Organizations To Track Individual, Group Level Emotional, Social Competency Score using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Development Courses For Leaders Training Courses To Develop Skills For Managing Conflict At Workplace
Development Courses For Leaders Training Courses To Develop Skills For Managing Conflict At WorkplaceThe following slide showcases the training programs aiming to minimize effects of conflicts at all levels. Key training ptograms included here are strategies to deal with difficult team members, ways of managing conflict at workplace etc. Deliver an outstanding presentation on the topic using this Development Courses For Leaders Training Courses To Develop Skills For Managing Conflict At Workplace. Dispense information and present a thorough explanation of Training Programs, Strategies To Deal, Training Courses, Develop Skills, Managing Conflict At Workplace using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
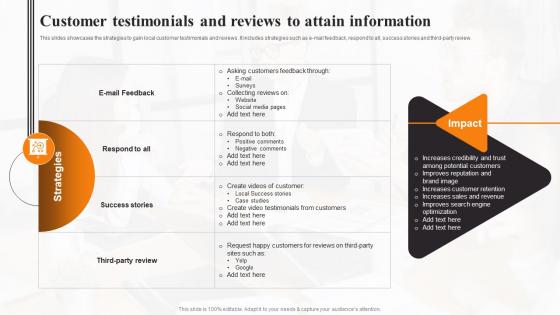 Customer Testimonials And Reviews To Attain Local Marketing Strategies To Increase Sales MKT SS
Customer Testimonials And Reviews To Attain Local Marketing Strategies To Increase Sales MKT SSThis slides showcases the strategies to gain local customer testimonials and reviews. It includes strategies such as e mail feedback, respond to all, success stories and third party review. Deliver an outstanding presentation on the topic using this Customer Testimonials And Reviews To Attain Local Marketing Strategies To Increase Sales MKT SS. Dispense information and present a thorough explanation of Customer, Reviews, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Eye Tracking Technology To Analyze Customer Visual Attention Digital Neuromarketing Strategy To Persuade MKT SS V
Eye Tracking Technology To Analyze Customer Visual Attention Digital Neuromarketing Strategy To Persuade MKT SS VThis slide represents eye tracking neuromarketing technology that enables assessment of customer visual attention along with emotional response for product. It includes stimulation, Area of Interest AOI, customer response etc. Deliver an outstanding presentation on the topic using this Eye Tracking Technology To Analyze Customer Visual Attention Digital Neuromarketing Strategy To Persuade MKT SS V. Dispense information and present a thorough explanation of Advertisement, Overall Result using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach Attack
Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach AttackThis slide represents the checklist for implementing a data breach response plan. The fundamental approaches are identify and isolate impacted systems or networks, perform a formal risk assessment, restore systems and address security flaws, notify affected parties, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach Attack. Use it as a tool for discussion and navigation on Data Breach Response Plan, Fundamental Approaches, Systems Or Networks, Perform A Formal Risk Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Common Data Breach Attack Vectors
Data Breach Prevention And Mitigation Common Data Breach Attack VectorsThis slide represents several data breach attack vectors. The main components are stolen or compromised credentials, social engineering attacks, ransomware, system vulnerabilities, human error and IT failures, physical or site security errors, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Common Data Breach Attack Vectors. Dispense information and present a thorough explanation of Brute Force Attacks, Purchasing Stolen Credentials, Phishing Scams, Fraudulent Emails, Deceptive Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major Business
Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major BusinessThis slide highlights the top data breach victims based on different industrial sectors. These industries include email service providers, social media websites, online auction websites, retail services, government agencies, file-sharing and hosting services, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major Business. Use it as a tool for discussion and navigation on Heartland Payment Systems, Email Service Provider, Social Media Website, Online Auction Website. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack
Data Breach Prevention And Mitigation Different Modes Of Data Breach AttackThis slide discusses the unintentional and intentional methods of data breach attacks. The examples outlined in this slide are accessing unsecured websites, downloading compromised software, losing work devices in a public place, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack. Dispense information and present a thorough explanation of Unintentional And Intentional Methods, Data Breach Attacks, Unsecured Websites, Downloading Compromised Software, Losing Work Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Athlete Branding Search Engine Offline And Digital Promotion Techniques MKT SS V
Athlete Branding Search Engine Offline And Digital Promotion Techniques MKT SS VThis slide showcases key techniques which can help improve search engine optimization SEO of athlete branding. It provides details about technical optimization, on page SEO, off page SEO, merchandise sales, increased visibility, relevant content, etc.Deliver an outstanding presentation on the topic using this Athlete Branding Search Engine Offline And Digital Promotion Techniques MKT SS V. Dispense information and present a thorough explanation of Technical Optimization, Increased Merchandise, Advertisements Promotions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comprehensive Framework For Athlete Offline And Digital Promotion Techniques MKT SS V
Comprehensive Framework For Athlete Offline And Digital Promotion Techniques MKT SS VThis slide showcases framework which can guide sporting brands for constructing athlete brands. It provides details about antecedents, media, oral communication, social agents, impressions, team sport, on field attributes, off field attributes, etc.Deliver an outstanding presentation on the topic using this Comprehensive Framework For Athlete Offline And Digital Promotion Techniques MKT SS V. Dispense information and present a thorough explanation of Oral Communication, Impression Management, Volunteered Advocacy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identify And Analyze Supply Chain Disruptions At Optimizing Material Acquisition Process
Identify And Analyze Supply Chain Disruptions At Optimizing Material Acquisition ProcessThe following slide identifies multiple supply chain disruptions at different locations of business It includes key components such as state, city, disruption status, disruption type and impact on business. Present the topic in a bit more detail with this Identify And Analyze Supply Chain Disruptions At Optimizing Material Acquisition Process. Use it as a tool for discussion and navigation on Analyze, Chain, Various. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Major Cyber Attacks Faced By Organization
Compressive Planning Guide Major Cyber Attacks Faced By OrganizationThis purpose of this slide is to showcase the major cyber attacks faced by business organization. The key attacks listed are phishing, malware attack, denial of service attacks, SQL injections, and ransomware. It also provides details regarding the major IT assets impacted and primary objective of each of the attacks. Present the topic in a bit more detail with this Compressive Planning Guide Major Cyber Attacks Faced By Organization. Use it as a tool for discussion and navigation on Database Servers, Network And Application Infrastructure, Denial Of Service Attack, Malware Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Dispense information and present a thorough explanation of Cyber Attacks Segmentation, Phishing Attack, Fraudulently Obtain Sensitive Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities
Compressive Planning Guide Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attack Risk Vulnerabilities, Vulnerability Exploited, Occurrence And Control Recommended. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Strategic Plan To Mitigate Cyber Attacks
Compressive Planning Guide Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Strategic Plan, Mitigate Cyber Attacks, Risk Mitigation Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Action Plan To Combat Cyber Crimes Major Cyber Attacks Faced By Organization
Action Plan To Combat Cyber Crimes Major Cyber Attacks Faced By OrganizationThis purpose of this slide is to showcase the major cyber attacks faced by business organization. The key attacks listed are phishing, malware attack, denial of service attacks, SQL injections, and ransomware. It also provides details regarding the major IT assets impacted and primary objective of each of the attacks. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Major Cyber Attacks Faced By Organization. Dispense information and present a thorough explanation of Major Cyber Attacks, Malware Attack, Denial Of Service Attacks, SQL Injections, IT Assets using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities
Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cloud Network Compromised, Financial Transactions, Credentials Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber Attacks
Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Risk Mitigation Plan, Multiple Cyber Attacks, Mitigation Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 ESCI Model For Assessing Leadership Skills At Functional Top Leadership Skill Development Training
ESCI Model For Assessing Leadership Skills At Functional Top Leadership Skill Development TrainingThe following slide showcases the leadership assessment based on emotional and social competency inventory ESCI model. The model is used by organizations to track individual and group level emotional and socialcompetency score. Deliver an outstanding presentation on the topic using this ESCI Model For Assessing Leadership Skills At Functional Top Leadership Skill Development Training. Dispense information and present a thorough explanation of Model, Leadership, Skills using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Storage Area Network Attacks Sniffing Storage Area Network San
Storage Area Network Attacks Sniffing Storage Area Network SanThis Slide Outlines The Sniffing Attack That Can Impact A Storage Area Network. The Purpose Of This Slide Is To Represent The Overview And Method To Control The Sniffing, Which Is Encryption. It Also Includes Sniffing Preventive Protocols For Fiber Channel And Ethernet Traffic, Such As ESP And SSL. Present The Topic In A Bit More Detail With This Storage Area Network Attacks Sniffing Storage Area Network San. Use It As A Tool For Discussion And Navigation On Encryption, Techniques, Confidentiality. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
 Storage Area Network San Direct Attached Storage Vs Storage Area Network
Storage Area Network San Direct Attached Storage Vs Storage Area NetworkThis Slide Describes The Comparison Between Direct-Attached Storage DAS And Storage Area Networks SAN. The Purpose Of This Slide Is To Highlight The Critical Differences Between DAS And SAN Based On Protocol, Applications, Pros And Cons, And Storage Devices. Deliver An Outstanding Presentation On The Topic Using This Storage Area Network San Direct Attached Storage Vs Storage Area Network. Dispense Information And Present A Thorough Explanation Of High Performance, Centralized Management, Powerful Compatibility Using The Slides Given. This Template Can Be Altered And Personalized To Fit Your Needs. It Is Also Available For Immediate Download. So Grab It Now.
-
 Storage Area Network San Network Attached Storage Vs San Storage
Storage Area Network San Network Attached Storage Vs San StorageThis Slide Represents The Difference Between Network-Attached Storage And Storage Area Networks. The Purpose Of This Slide Is To Differentiate The SAN And NAS Based On Fiber, Protocols, Data Processing, Use, Performance, And Ease Of Management. Deliver An Outstanding Presentation On The Topic Using This Storage Area Network San Network Attached Storage Vs San Storage. Dispense Information And Present A Thorough Explanation Of Ease Of Management, Performance, Data Processing Using The Slides Given. This Template Can Be Altered And Personalized To Fit Your Needs. It Is Also Available For Immediate Download. So Grab It Now.
-
 Storage Area Network San Storage Area Network Attacks Spoofing
Storage Area Network San Storage Area Network Attacks SpoofingThis Slide Outlines The Spoofing Attacks That Compromise Storage Area Network Security. The Purpose Of This Slide Is To Provide An Overview Of Spoofing And Different Control Points That Can Prevent Spoofing Attacks, Including Out-Of And In-Band Management Apps, Device-To-Device, A Device To Fabric, And So On. Deliver An Outstanding Presentation On The Topic Using This Storage Area Network San Storage Area Network Attacks Spoofing. Dispense Information And Present A Thorough Explanation Of Impersonation, Masquerading, Storage Using The Slides Given. This Template Can Be Altered And Personalized To Fit Your Needs. It Is Also Available For Immediate Download. So Grab It Now.
-
 Storage Area Network San Storage Area Network Attacks Unauthorized Access
Storage Area Network San Storage Area Network Attacks Unauthorized AccessThis Slide Represents The Unauthorized Type Of SAN Attack, Including Its Control Points. This Slide Aims To Give An Overview Of Unauthorized Access And The Various Control Points That Can Prevent Unauthorized Access, Including Out-Of-Band And In-Band Management Apps, Device-To-Device, Device-To-Fabric, And So On. Present The Topic In A Bit More Detail With This Storage Area Network San Storage Area Network Attacks Unauthorized Access. Use It As A Tool For Discussion And Navigation On Unauthorized, Overview, Service. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
 Organizational Behavior Management Determine Different Leadership Styles Existing At Workplace
Organizational Behavior Management Determine Different Leadership Styles Existing At WorkplaceThis slide provides information regarding different leadership styles existing at workplace in terms of Laissez Faire, autocratic and participative. Deliver an outstanding presentation on the topic using this Organizational Behavior Management Determine Different Leadership Styles Existing At Workplace. Dispense information and present a thorough explanation of Leadership Styles Existing, Workplace In Terms Of Laissez, Autocratic And Participative, Require Direct Supervision using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Understanding Human Workplace Addressing Different Conflict Management Styles At Organization
Understanding Human Workplace Addressing Different Conflict Management Styles At OrganizationThis slide provides information regarding conflict management styles at organization in terms of avoiding the conflict, accommodate, compromise, collaborate, compromise, compete. Deliver an outstanding presentation on the topic using this Understanding Human Workplace Addressing Different Conflict Management Styles At Organization. Dispense information and present a thorough explanation of Conflict Management Styles, Accommodate, Compromise, Collaborate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 AIOPS Applications And Use Case AIOPS Real World Applications At A Mobile Network Provider
AIOPS Applications And Use Case AIOPS Real World Applications At A Mobile Network ProviderThis slide outlines the real-world use cases of AIOps at a network provider. The purpose of this slide is to highlight the applications of AIOps at a mobile vendor. Applications include automated network optimization, network security, intelligent routing, customer experience management, and so on. Present the topic in a bit more detail with this AIOPS Applications And Use Case AIOPS Real World Applications At A Mobile Network Provider. Use it as a tool for discussion and navigation on Customer Experience Management, Improving Customer Service, Network Security, Automated Network Optimization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 AIOPS Applications And Use Case Checklist To Implement AIOPS At Telecom Operator
AIOPS Applications And Use Case Checklist To Implement AIOPS At Telecom OperatorThis slide outlines the checklist for AIOps deployment in the telecommunication industry. The purpose of this slide is to showcase the various steps telecom industries should keep in mind while implementing AIOps. The steps include defining project scope and goals, conducting data and systems evaluation, etc. Present the topic in a bit more detail with this AIOPS Applications And Use Case Checklist To Implement AIOPS At Telecom Operator. Use it as a tool for discussion and navigation on Monitor And Evaluate Outputs, Continuously Improve, Conduct Data And Systems Evaluation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Auto Dealership Business Car Dealership Industry Global Market At A Glance BP SS
Auto Dealership Business Car Dealership Industry Global Market At A Glance BP SSThe purpose of this slide is to highlight the market size of the global automobile and car dealership industry, including its share in 2021 and 2022, its forecasted value in 2030, and its CAGR. It also depicts the primary reasons driving the market growth, including the increasing millennial population and increasing demand post-pandemic. Present the topic in a bit more detail with this Auto Dealership Business Car Dealership Industry Global Market At A Glance BP SS. Use it as a tool for discussion and navigation on Global Automobile, Car Dealership Industry, Markets Growth, Millennial Population. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 How Does Organization Impact Addressing Different Conflict Management Styles At Organization
How Does Organization Impact Addressing Different Conflict Management Styles At OrganizationThis slide provides information regarding conflict management styles at organization in terms of avoiding the conflict, accommodate, compromise, collaborate, compromise, compete. Present the topic in a bit more detail with this How Does Organization Impact Addressing Different Conflict Management Styles At Organization. Use it as a tool for discussion and navigation on Conflict Management Styles, Accommodate, Compromise, Collaborate, Damage Relationships. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Prompt Engineering For Generative Ai Models To Attain Desired Results Generative Ai Artificial Intelligence AI SS
Prompt Engineering For Generative Ai Models To Attain Desired Results Generative Ai Artificial Intelligence AI SSThis slide provides information regarding the importance of prompt engineering in gaining desired results through generative AI systems. This approach helps in assessing fed inputs and showcasing relevant and contextual results across generative AI model. Present the topic in a bit more detail with this Prompt Engineering For Generative Ai Models To Attain Desired Results Generative Ai Artificial Intelligence AI SS. Use it as a tool for discussion and navigation on Engineering, Generative, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identify And Analyze Supply Chain Disruptions At Evaluating Key Risks In Procurement Process
Identify And Analyze Supply Chain Disruptions At Evaluating Key Risks In Procurement ProcessThe following slide identifies multiple supply chain disruptions at different locations of business It includes key components such as state, city, disruption status, disruption type and impact on business. Present the topic in a bit more detail with this Identify And Analyze Supply Chain Disruptions At Evaluating Key Risks In Procurement Process. Use it as a tool for discussion and navigation on Disruption, Impact, Various. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
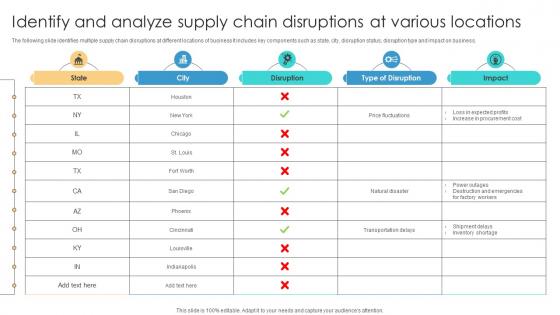 Risk Management Process Identify And Analyze Supply Chain Disruptions At Various Locations
Risk Management Process Identify And Analyze Supply Chain Disruptions At Various LocationsThe following slide identifies multiple supply chain disruptions at different locations of business It includes key components such as state, city, disruption status, disruption type and impact on business. Deliver an outstanding presentation on the topic using this Risk Management Process Identify And Analyze Supply Chain Disruptions At Various Locations Dispense information and present a thorough explanation of Price Fluctuations, Natural Disaster using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Life At Workplace Addressing Different Kinds Of Organizational Planned Change
Managing Life At Workplace Addressing Different Kinds Of Organizational Planned ChangeThis slide provides information regarding conflict management styles at organization in terms of avoiding the conflict, accommodate, compromise, collaborate, compromise, compete. Deliver an outstanding presentation on the topic using this Managing Life At Workplace Addressing Different Kinds Of Organizational Planned Change. Dispense information and present a thorough explanation of Avoiding The Conflict, Accommodate, Compromise, Collaborate, Conflict Management Styles using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Life At Workplace Association Of Organizational Behaviour To Applied Behavior Analysis
Managing Life At Workplace Association Of Organizational Behaviour To Applied Behavior AnalysisThis slide provides information regarding assessment of organizational behavior models on different parameters such as dependability, managerial inclination, employee inclination, employee requirements met, etc. Present the topic in a bit more detail with this Managing Life At Workplace Association Of Organizational Behaviour To Applied Behavior Analysis. Use it as a tool for discussion and navigation on Personal Dependency, Employee Psychological Result, Employee Requirements Met, Managerial Inclination . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Employee Code Of Conduct Addressing Different Conflict Management Styles At Organization
Employee Code Of Conduct Addressing Different Conflict Management Styles At OrganizationThis slide provides information regarding conflict management styles at organization in terms of avoiding the conflict, accommodate, compromise, collaborate, compromise, compete. Deliver an outstanding presentation on the topic using this Employee Code Of Conduct Addressing Different Conflict Management Styles At Organization. Dispense information and present a thorough explanation of Conflict Management, Styles At Organization, Collaborate, Compromise, Accommodate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Human Organizational Behavior Addressing Different Conflict Management Styles At Organization
Human Organizational Behavior Addressing Different Conflict Management Styles At OrganizationThis slide provides information regarding conflict management styles at organization in terms of avoiding the conflict, accommodate, compromise, collaborate, compromise, compete. Deliver an outstanding presentation on the topic using this Human Organizational Behavior Addressing Different Conflict Management Styles At Organization. Dispense information and present a thorough explanation of Conflict Management Styles, Accommodate, Compromise, Collaborate, Compromise using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Individual Performance Management Addressing Different Conflict Management Styles At Organization
Individual Performance Management Addressing Different Conflict Management Styles At OrganizationThis slide provides information regarding conflict management styles at organization in terms of avoiding the conflict, accommodate, compromise, collaborate, compromise, compete. Present the topic in a bit more detail with this Individual Performance Management Addressing Different Conflict Management Styles At Organization. Use it as a tool for discussion and navigation on Conflict Management Styles, Avoiding The Conflict, Accommodate, Compromise, Collaborate, Compromise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist To Maintain Hygiene At Food Stations Food Quality And Safety Management Guide
Checklist To Maintain Hygiene At Food Stations Food Quality And Safety Management GuideThis slide presents a checklist that can be used by managers to maintain hygiene at food stations. The major initiatives covered in the checklist relate to inspection, cleaning supplies, sterilization, clean clothing, etc. Present the topic in a bit more detail with this Checklist To Maintain Hygiene At Food Stations Food Quality And Safety Management Guide. Use it as a tool for discussion and navigation on Maintain, Hygiene, Stations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Employee Counselling For Enhancing Checklist For Effective Counselling Process At Workplace
Employee Counselling For Enhancing Checklist For Effective Counselling Process At WorkplaceThis slide shows detailed checklist for employee counselling process at workplace for tracking overall progress. It include checklist points such as building rapport, gathering employee related information, etc. Present the topic in a bit more detail with this Employee Counselling For Enhancing Checklist For Effective Counselling Process At Workplace. Use it as a tool for discussion and navigation on Establishing Rapport, Gathering Employee Information, Exploring Employee Thoughts, Developing Coping Skills. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Employee Counselling For Enhancing Overview Of Cooperative Counselling For Employees At Workplace
Employee Counselling For Enhancing Overview Of Cooperative Counselling For Employees At WorkplaceThis slide shows introduction of cooperative counselling for employees at workplace to ensure their well being. It include description, importance and steps involved in cooperative counselling, etc. Deliver an outstanding presentation on the topic using this Employee Counselling For Enhancing Overview Of Cooperative Counselling For Employees At Workplace. Dispense information and present a thorough explanation of Identify Employee Problems, Collaborative Goal Setting, Employees At Workplace, Prioritizes Emotional using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Checklist To Secure Organizations From Phishing
Phishing Attacks And Strategies To Mitigate Them V2 Checklist To Secure Organizations From PhishingThis slide outlines the steps to be taken to protect the organization and its employees from phishing attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real-time monitoring and develop an incident plan. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Checklist To Secure Organizations From Phishing. Use it as a tool for discussion and navigation on Phishing Attacks, Real Time Monitoring, Spam Filters, Multi Factor Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 How To Protect Users From Vishing Attacks
Phishing Attacks And Strategies To Mitigate Them V2 How To Protect Users From Vishing AttacksThis slide talks about the ways to protect users from vishing attacks. These include avoid calls from robots, never respond to audio-automated calls, verify the identity of the caller, never share personal information over the call, use multi-factor authentication, etc. Deliver an outstanding presentation on the topic using this Phishing Attacks And Strategies To Mitigate Them V2 How To Protect Users From Vishing Attacks. Dispense information and present a thorough explanation of Vishing Attacks, Audio Automated Calls, Personal Information, Multi Factor Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Popular Man In The Middle Phishing Kits Used
Phishing Attacks And Strategies To Mitigate Them V2 Popular Man In The Middle Phishing Kits UsedThis slide outlines the various phishing kits used by attackers to conduct man-in-the-middle scams. The purpose of thus slide is to describe the reported year and use of different MITM kits such as Evilginx2, Modlishka, Muraena, EvilnoVNC and EvilProxy. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Popular Man In The Middle Phishing Kits Used. Use it as a tool for discussion and navigation on Creates Special Tokens, Uniform Resource Locator, Expose Phishing Content, Stolen Session Cookie. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To Conduct
Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To ConductThis slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross-site scripting, DMS cache poisoning, drive-by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To Conduct. Use it as a tool for discussion and navigation on Social Networking Sites, Demographic Information From Websites, Social Engineering, Keyloggers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Tools Provided By Google To Prevent Phishing
Phishing Attacks And Strategies To Mitigate Them V2 Tools Provided By Google To Prevent PhishingThis slide demonstrates the different tools provided by Google to prevent and report cyber phishing scams. These include to spot phishing mails with the help of Gmail, utilize safe browsing in chrome, look for unsafe saved passwords, password alert for chrome, etc. Deliver an outstanding presentation on the topic using this Phishing Attacks And Strategies To Mitigate Them V2 Tools Provided By Google To Prevent Phishing. Dispense information and present a thorough explanation of Safe Browsing In Chrome, Phishing Mails Detection With Gmail, Two Step Verification, Password Alert For Chrome using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Of Business Disruption Caused By Phishing Phishing Attacks And Strategies To Mitigate Them V2
Overview Of Business Disruption Caused By Phishing Phishing Attacks And Strategies To Mitigate Them V2This slide discusses the impact of phishing attacks on businesses. The purpose of this slide is to outline the amount of money lost by well-reputed companies due to phishing scams. The companies included are Facebook and Google, Crelan Bank in Belgium, etc. Deliver an outstanding presentation on the topic using this Overview Of Business Disruption Caused By Phishing Phishing Attacks And Strategies To Mitigate Them V2. Dispense information and present a thorough explanation of Phishing Attacks On Businesses, Phishing Scams, Crelan Bank In Belgium using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Brand Awareness Campaign Plan To Attain Competitive Edge Strategies To Ramp Strategy SS V
Brand Awareness Campaign Plan To Attain Competitive Edge Strategies To Ramp Strategy SS VThis slide covers the brand awareness campaign planning sheet. It includes social media campaigns, influencer marketing, and trade show participation. It consists of the campaign objective, action steps, duration, budget, and expected campaign ROI. Present the topic in a bit more detail with this Brand Awareness Campaign Plan To Attain Competitive Edge Strategies To Ramp Strategy SS V Use it as a tool for discussion and navigation on Campaign Objective, Social Media Campaign, Influencer Marketing This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Brand Awareness Campaign Plan To Attain Competitive Edge Ways To Optimize Strategy SS V
Brand Awareness Campaign Plan To Attain Competitive Edge Ways To Optimize Strategy SS VThis slide covers the brand awareness campaign planning sheet. It includes social media campaigns, influencer marketing, and trade show participation. It consists of the campaign objective, action steps, duration, budget, and expected campaign ROI. Present the topic in a bit more detail with this Brand Awareness Campaign Plan To Attain Competitive Edge Ways To Optimize Strategy SS V Use it as a tool for discussion and navigation on Social Media Campaign, Campaign Objective, Campaign Budget This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cardless Atms As Emerging Trend In Mobile Banking E Wallets As Emerging Payment Method Fin SS V
Cardless Atms As Emerging Trend In Mobile Banking E Wallets As Emerging Payment Method Fin SS VThis slide shows details regarding how users can withdraw money using cardless ATMs. It also includes information about the functioning of cardless ATMs which is facilitated via QR codes, NFC, verification code and biometric verification. Deliver an outstanding presentation on the topic using this Cardless Atms As Emerging Trend In Mobile Banking E Wallets As Emerging Payment Method Fin SS V. Dispense information and present a thorough explanation of Verification Code, Biometric Verification, Transaction using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Man In The Middle Mobile Banking Attacking Methods E Wallets As Emerging Payment Method Fin SS V
Man In The Middle Mobile Banking Attacking Methods E Wallets As Emerging Payment Method Fin SS VThis slide shows overview of popular cyberattack related to mobile banking which is man in the middle MiTM. It also includes popular types of this attack which are WIFI network interception, DNS spoofing, email interception and malware. Present the topic in a bit more detail with this Man In The Middle Mobile Banking Attacking Methods E Wallets As Emerging Payment Method Fin SS V. Use it as a tool for discussion and navigation on Interception, Communication, Web Application. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Brand Awareness Campaign Plan To Attain Competitive Creating A Successful Marketing Strategy SS V
Brand Awareness Campaign Plan To Attain Competitive Creating A Successful Marketing Strategy SS VThis slide covers the brand awareness campaign planning sheet. It includes social media campaigns, influencer marketing, and trade show participation. It consists of the campaign objective, action steps, duration, budget, and expected campaign ROI. Deliver an outstanding presentation on the topic using this Brand Awareness Campaign Plan To Attain Competitive Creating A Successful Marketing Strategy SS V. Dispense information and present a thorough explanation of Influencer Marketing, Increase Brand, Awareness Through using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Upload Media At Radio Station Setting Up An Own Internet Radio Station
Upload Media At Radio Station Setting Up An Own Internet Radio StationThe slide outlines type of content to add in radio channel to attract users. Media types are music tracks, jingles and station IDs, promotional announcements, sound effects and drops, advertisements, etc. Present the topic in a bit more detail with this Upload Media At Radio Station Setting Up An Own Internet Radio Station. Use it as a tool for discussion and navigation on Promotional Announcements, Sound Effects, Advertisements. This template is free to edit as deemed fit for your organization. Therefore download it now.



