Powerpoint Templates and Google slides for Security Of Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 5 step course of action plan of data security
5 step course of action plan of data securityPresenting this set of slides with name 5 Step Course Of Action Plan Of Data Security. This is a five stage process. The stages in this process are Identify Information Assets, Identify Risk, Manage Risks Across The Information, Determine Value Of Information, Apply Security Measures. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Data security it what are the benefits of data security
Data security it what are the benefits of data securityThis slide depicts the different benefits of deploying a data security model in an organization and how it can minimize the risk and save a companys time, money, and efforts. Increase audience engagement and knowledge by dispensing information using Data Security IT What Are The Benefits Of Data Security. This template helps you present information on five stages. You can also present information on Legitimate Traffic, Hardware Security Devices, Threats And Risks, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
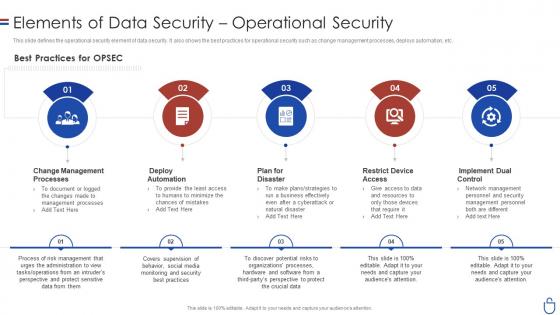 Data security it elements of data security operational security
Data security it elements of data security operational securityThis slide defines the operational security element of data security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Introducing Data Security IT Elements Of Data Security Operational Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Best Practices, OPSEC, Change Management Processes, Deploy Automation, Plan For Disaster, Restrict Device Access, Implement Dual Control, using this template. Grab it now to reap its full benefits.
-
 Use Case Of Splunk Big Data For Security Intelligence
Use Case Of Splunk Big Data For Security IntelligenceFollowing slide showcases uses of splunk big data for security management. The purpose of this slide is to help businesses in investigating threats and improving compliance. It includes elements such as security monitoring, incident reporting, etc. Presenting our set of slides with Use Case Of Splunk Big Data For Security Intelligence This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Monitoring, Compliance.
-
 Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security
Tokenization For Improved Data Security Salient Features Of Tokenization In Data SecurityThis slide outlines the key characteristics of tokenization in data security. The purpose of this slide is to highlight the properties of tokenization that include underlying representation, transferability, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security. This template helps you present information on five stages. You can also present information on Underlying Representation, Transferability, Fungibility, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


