Powerpoint Templates and Google slides for Security Of Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Mode of communication for company online database security proposal ppt clipart
Mode of communication for company online database security proposal ppt clipartPresenting this set of slides with name Mode Of Communication For Company Online Database Security Proposal Ppt Clipart. The topics discussed in these slides are Communicate Medium, Weekly Calls, Monthly Catch Up, Review Sessions. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Statement of work and contract for company online database security proposal ppt file aids
Statement of work and contract for company online database security proposal ppt file aidsPresenting this set of slides with name Statement Of Work And Contract For Company Online Database Security Proposal Ppt File Aids. This is a one stage process. The stages in this process are Services Rendered, Mutual Cooperation, Terms Of Payment, Confidentiality, Plans Cancellation. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 4 dimensions of infrastructure security data ppt powerpoint presentation styles example topics
4 dimensions of infrastructure security data ppt powerpoint presentation styles example topicsPresenting this set of slides with name 4 Dimensions Of Infrastructure Security Data Ppt Powerpoint Presentation Styles Example Topics. The topics discussed in these slides are Employees, Structured, Suspires, Infrastructure, Data. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon showing technology challenge of data security
Icon showing technology challenge of data securityIntroducing our Icon Showing Technology Challenge Of Data Security set of slides. The topics discussed in these slides are Icon Showing, Technology Challenge, Data Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 8 principles of data protection and security
8 principles of data protection and securityIntroducing our premium set of slides with 8 Principles Of Data Protection And Security. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Accuracy, Data Security, Retention. So download instantly and tailor it with your information.
-
 Categories of security controls to minimize data risks
Categories of security controls to minimize data risksPresenting our set of slides with Categories Of Security Controls To Minimize Data Risks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Operational Security, Physical Security, Management Security.
-
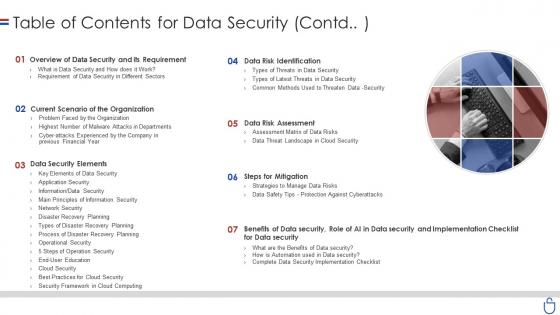 Data security it table of contents for data security contd
Data security it table of contents for data security contdIncrease audience engagement and knowledge by dispensing information using Data Security IT Table Of Contents For Data Security Contd. This template helps you present information on seven stages. You can also present information on Overview Data Security And Its Requirement, Current Scenario Organization, Data Security Elements, Steps Mitigation, Data Risk Assessment, Data Risk Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
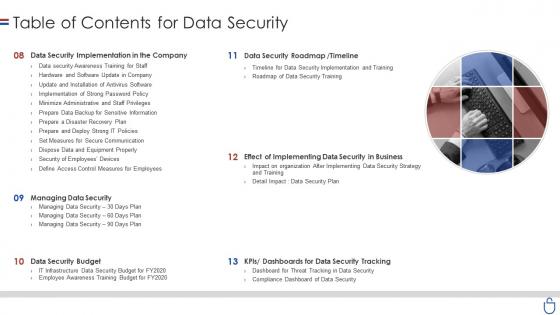 Data security it table of contents for data security ppt slides display
Data security it table of contents for data security ppt slides displayIntroducing Data Security IT Table Of Contents For Data Security Ppt Slides Display to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Data Security Implementation Company, Data Security Roadmap, Timeline, Managing Data Security, Data Security Budget, Dashboards Data Security Tracking, using this template. Grab it now to reap its full benefits.
-
 Data security it elements of data security disaster recovery planning
Data security it elements of data security disaster recovery planningThis slide depicts the disaster recovery plan in the data security model and what strategies an organization needs to adopt to recover from an attack or natural disaster. Introducing Data Security IT Elements Of Data Security Disaster Recovery Planning to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Business, Natural Disasters, Human Interfered Security Incidents, Technology, using this template. Grab it now to reap its full benefits.
-
 Distributed computing security of data and networks in distributed computing
Distributed computing security of data and networks in distributed computingThis slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable. Present the topic in a bit more detail with this Distributed Computing Security Of Data And Networks In Distributed Computing. Use it as a tool for discussion and navigation on Element, Computing, Protection, System, Network, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table of contents for data center security data center it ppt powerpoint presentation file show
Table of contents for data center security data center it ppt powerpoint presentation file showPresent the topic in a bit more detail with this Table Of Contents For Data Center Security Data Center It Ppt Powerpoint Presentation File Show. Use it as a tool for discussion and navigation on Data Center Management, Data Center Security, Technologies, Roadmap, Timeline. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table of contents advanced security monitoring plan to remove cybersecurity threat and data infraction
Table of contents advanced security monitoring plan to remove cybersecurity threat and data infractionPresent the topic in a bit more detail with this Table Of Contents Advanced Security Monitoring Plan To Remove Cybersecurity Threat And Data Infraction. Use it as a tool for discussion and navigation on Cybersecurity Monitoring Tools To Be Implemented, Essential Elements Of Security Monitoring Plan, Cybersecurity Monitoring Best Practices To Be Followed By The Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Planning And Implementation Of Crm Software Securing Our Data With Crm
Planning And Implementation Of Crm Software Securing Our Data With CrmThis slide highlights the CRM data security model which includes the user based, profile based, group based, record sharing and login based security. Deliver an outstanding presentation on the topic using this Planning And Implementation Of Crm Software Securing Our Data With Crm. Dispense information and present a thorough explanation of User Role Based Security, Profile Based Security, Record Sharing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Securing Our Data With Crm Planning And Implementation Of Crm Software
Securing Our Data With Crm Planning And Implementation Of Crm SoftwareThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security. Present the topic in a bit more detail with this Securing Our Data With Crm Planning And Implementation Of Crm Software. Use it as a tool for discussion and navigation on Securing Our Data With CRM. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Of Data And Networks In Edge Computing Distributed Information Technology
Security Of Data And Networks In Edge Computing Distributed Information TechnologyThis slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable. Deliver an outstanding presentation on the topic using this Security Of Data And Networks In Edge Computing Distributed Information Technology. Dispense information and present a thorough explanation of Security Of Data And Networks In Edge Computing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Architecture Of Cloud Security Cloud Data Protection
Architecture Of Cloud Security Cloud Data ProtectionThis slide represents the architecture of the cloud security system and how data is organized and secured under a cloud system. Deliver an outstanding presentation on the topic using this Architecture Of Cloud Security Cloud Data Protection. Dispense information and present a thorough explanation of Infrastructure Security, Monitoring, Processing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Data Protection Essential Pillars Of Cloud Security
Cloud Data Protection Essential Pillars Of Cloud SecurityThis slide shows the four essential pillars of cloud security, namely visibility and consistency, process based security, network security, and identity security. Introducing Cloud Data Protection Essential Pillars Of Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Process Based Security, Network Security, Identity Security, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Data Protection
Cloud Security Threats Loss Of Data Cloud Data ProtectionThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Data Protection. This template helps you present information on four stages. You can also present information on Storage Locations, Organization, Strategies using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Pillars Of Cloud Security Visibility And Consistency Cloud Data Protection
Pillars Of Cloud Security Visibility And Consistency Cloud Data ProtectionThis slide depicts the visibility and consistency pillar of cloud security, and it further includes asset inventory, best cloud framework, and data security. Introducing Pillars Of Cloud Security Visibility And Consistency Cloud Data Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Cloud Framework, Data Security, Asset Inventory, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Computing Security
Cloud Security Threats Loss Of Data Cloud Computing SecurityThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Computing Security. This template helps you present information on four stages. You can also present information on Service Providers, Organization, Backup Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Benefit Of Block Chain Technology For Securing Confidential Data Icon
Benefit Of Block Chain Technology For Securing Confidential Data IconPresenting our set of slides with Benefit Of Block Chain Technology For Securing Confidential Data Icon. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Block Chain Technology, Securing Confidential Data.
-
 Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery
Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation galleryThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Increase audience engagement and knowledge by dispensing information using Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery. This template helps you present information on two stages. You can also present information on Challenges, Solution, Data Collections using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Components Of Data Security And Privacy Policies
Key Components Of Data Security And Privacy PoliciesThe following slide depicts some elements of data security and privacy policies to communicate the relevance and purpose of collected data. It includes elements such as scan vulnerabilities, manage patches, response to incidents, monitor compliance etc. Presenting our set of slides with name Key Components Of Data Security And Privacy Policies. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Scan Vulnerabilities, Manage Patches, Response To Incidents.
-
 Key Statistics Of It Security And Data Breach
Key Statistics Of It Security And Data BreachThe following slide depicts some statistical insights of IT security to prevent data breaches and financial loss. It includes facts such as annual cost incurred due to malware, threats due to ransomware, previous year records of data breach etc. Presenting our well structured Key Statistics Of It Security And Data Breach. The topics discussed in this slide are Mobile, Data, Breach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security
Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase information security gap analysis of the company. The slide covers information about the current and desired state, gap reasons identified, approaches to be deployed and priority level. Deliver an outstanding presentation on the topic using this Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Current State, Email, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Functional Chart Of Cyber Security Team Preventing Data Breaches Through Cyber Security
Functional Chart Of Cyber Security Team Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to provide glimpse of cyber security team in the form of org chart. The key stakeholders mentioned in the slide are chief information security officer CISO, cyber risk committee, cyber security director, cyber risk manager, security operations manager etc. Deliver an outstanding presentation on the topic using this Functional Chart Of Cyber Security Team Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Cyber Risk Manger, Security Training, Cyber Business Liaison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 How Much Employees Are Aware Of Cyber Security Preventing Data Breaches Through Cyber Security
How Much Employees Are Aware Of Cyber Security Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the cyber security assessment test result. It covers information about the pass fail rate of employees who received the security awareness training and fail rate by age. Present the topic in a bit more detail with this How Much Employees Are Aware Of Cyber Security Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Security Training, Assessment Test, Employees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Major Statistics Of Cyber Security Awareness Preventing Data Breaches Through Cyber Security
Major Statistics Of Cyber Security Awareness Preventing Data Breaches Through Cyber SecurityIntroducing Major Statistics Of Cyber Security Awareness Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Browser, Employees, Password Manager, using this template. Grab it now to reap its full benefits.
-
 Model For Protection And Security Of Healthcare Data
Model For Protection And Security Of Healthcare DataThis slide depicts the flowchart used for explaining the process of protecting the healthcare data. The purpose of this template is to define a model used for maintaining privacy and confidentiality of health data. It includes information related to security, trust, confidentiality and privacy. Introducing our Model For Protection And Security Of Healthcare Data set of slides. The topics discussed in these slides are Security, Trust, Confidentiality, Privacy. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SS
Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SSThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc.Present the topic in a bit more detail with this Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SS. Use it as a tool for discussion and navigation on Factor Authentication, Organizations Information, Ensure Confidentiality. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V
Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS VThis slide represents overview of ICT information and communication technology business security It covers types and features for security such as network security, endpoint security etc Present the topic in a bit more detail with this Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Unauthorized Sources, Factor Authentication, Organizations Information This template is free to edit as deemed fit for your organization Therefore download it now
-
 Types Of Encryption For Securing Big Data Analytics
Types Of Encryption For Securing Big Data AnalyticsThis slide highlights the various types of encryption techniques utilized for protecting big data analytics. The purpose of this slide is to help the business safeguard sensitive information for preventing data breaches and information thefts. It includes quantum proof encryption, homomorphic encryption, etc. Introducing our premium set of slides with Types Of Encryption For Securing Big Data Analytics. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Homomorphic Encryption, Differential Privacy. So download instantly and tailor it with your information.
-
 Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V
Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V. Use it as a tool for discussion and navigation on Backup Repository, Encrypted Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display visual representation of internet of Things IoT security. The slide covers information about various IoT sensors, cloud for data collection, administration level, etc. Deliver an outstanding presentation on the topic using this Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Data, Security, Cyber using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies
Overview Of Encryption For Securing Data At Rest Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data at rest. The storage methods include file servers, network shares, document management systems, external storage, databases, endpoint devices, mobile devices, cloud storage, etc. Present the topic in a bit more detail with this Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies. Use it as a tool for discussion and navigation on Database Encryption, Information Rights Management, Data Leak Prevention, Mobile Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
 Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS
Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SSThis slide analyses the need of implementing data security initiatives to address key customer data challenges in retail industry. It also mentions types of customer data collected such as account, location, browsing, and profile. Deliver an outstanding presentation on the topic using this Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS Dispense information and present a thorough explanation of Customer Trust, Sensitive Information, Balancing Personalization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Components Of Big Data Analytics In Cyber Security
Components Of Big Data Analytics In Cyber SecurityThis slide showcases the components of big data analytics in cyber security. Its objective is to improve performance and security tactics in cyber security using big data. This includes data collection, data pre processing, data analysis, visualisation. Presenting our well structured Components Of Big Data Analytics In Cyber Security. The topics discussed in this slide are Collection, Storage, Analysis. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SS
Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SSThis slide covers key use cases of Oracle Database Crypto-Secure Data Management such as healthcare data protection, financial transactions, government data security, retail customer privacy, and intellectual property protection. Deliver an outstanding presentation on the topic using this Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SS Dispense information and present a thorough explanation of Healthcare Data, Financial Transactions, Customer Privacy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Introduction Of Application Security For Data Privacy
Introduction Of Application Security For Data PrivacyThis slide discusses the overview of application security which includes its objectives such as protecting data, minimize risk, etc. Increase audience engagement and knowledge by dispensing information using Introduction Of Application Security For Data Privacy. This template helps you present information on four stages. You can also present information on Covers Post Deployment Protection, Protects Data And Code, Application Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Of Tokenization For Improved Data Security
Table Of Contents Of Tokenization For Improved Data SecurityIncrease audience engagement and knowledge by dispensing information using Table Of Contents Of Tokenization For Improved Data Security. This template helps you present information on twelve stages. You can also present information on Data Security, Tokenization Market And Trends, Comparative Analysis, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security
Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data SecurityThis slide outlines the typical scenarios where tokenization is applied within data security contexts. The use cases include reducing compliance scope, restricting access to sensitive data, etc. Introducing Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restricting Access To Sensitive Data, Reducing Compliance Scope, Tokenization In Data Security, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Data Security Benefits Of Adopting Tokenization
Tokenization For Improved Data Security Data Security Benefits Of Adopting TokenizationThis slide discusses the cons of tokenization. The purpose of this slide is to showcase the advantages of tokenization such as utilizing less resources, decreases risk, stimulates innovation, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Data Security Benefits Of Adopting Tokenization. Dispense information and present a thorough explanation of Builds Customer Trust, Data Security Benefits, Adopting Tokenization, Fostering Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tokenization For Improved Data Security For Table Of Contents
Tokenization For Improved Data Security For Table Of ContentsPresent the topic in a bit more detail with this Tokenization For Improved Data Security For Table Of Contents. Use it as a tool for discussion and navigation on Overview And Process, Areas Of Application, Reasons For Conducting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology
Tokenization For Improved Data Security Future Trends Of Tokenization On Business And TechnologyThis slide highlights the anticipated developments in tokenizations impact on the realms of business and technology. The purpose of this slide is to outline the future trends of tokenization. Introducing Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Anticipated Developments, Business And Technology, Future Trends Of Tokenization, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Overview Of Platform Tokenization In Data Security
Tokenization For Improved Data Security Overview Of Platform Tokenization In Data SecurityThis slide discusses the introduction of first type tokenization in data security. The purpose of this slide is to highlight the overview of platform tokenization and how they gain security, transactional capacity, etc. Introducing Tokenization For Improved Data Security Overview Of Platform Tokenization In Data Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Ethereum Token Exchange, Platform Tokenization, Data Security, Security And Transactional Capacity, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Overview Of Security Tokenization In Data Security
Tokenization For Improved Data Security Overview Of Security Tokenization In Data SecurityThis slide outlines the introduction of security tokenization in data security. The purpose of this slide is to highlight the overview of security tokenization which include the definition, purpose, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Overview Of Security Tokenization In Data Security. This template helps you present information on eight stages. You can also present information on Security Tokenization, Data Security, Considering Security Tokens, Conventional Financial Securities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain Technology
Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain TechnologyThis slide discusses the regulations of security tokens for data security. The purpose of this slide is to showcase various security token regulations which include D, A plus, S regulations, etc. Introducing Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regulations Of Security Tokens, Blockchain Technology, Data Security, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit Cards
Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit CardsThis slide describes the tokenizing of debit and credit cards for transactional purposes. The purpose of this slide is to showcase the transactional tokenization of debit and credit cards. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit Cards. This template helps you present information on six stages. You can also present information on Unique Alternate Codes, Consumer Benefits, Enhanced Security, Debit And Credit Cards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Various Examples Of Utility Tokens In Ds
Tokenization For Improved Data Security Various Examples Of Utility Tokens In DsThis slide outlines the different instances of utility tokens in data security. The purpose of this slide is to highlight the examples of utility tokens along with its description and use case. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Various Examples Of Utility Tokens In Ds. Dispense information and present a thorough explanation of Decentralized Token Exchange, Decentralized Prediction Markets, Distributed Computing And Resource using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Different Modes Of IP Security For Securing Data
Different Modes Of IP Security For Securing DataThis slide showcases various modes of IP security. The main purpose of this template is to secure communication between two endpoints. This includes Point-to-point security, tunnel mode, remote access, etc. Introducing our Different Modes Of IP Security For Securing Data set of slides. The topics discussed in these slides are IP Security, Secure Communication, Point To Point Security, Tunnel Mode. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Table Of Contents For Mobile Device Security For Data Protection Cybersecurity SS
Table Of Contents For Mobile Device Security For Data Protection Cybersecurity SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Mobile Device Security For Data Protection Cybersecurity SS This template helps you present information on Five stages. You can also present information on Financial Companies, Million Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Overview Of Archival Stage To Ensure Secure Data Lifecycle Management To Enhance Flow
Overview Of Archival Stage To Ensure Secure Data Lifecycle Management To Enhance FlowThis stage presents an overview of the archival data stage to optimizes how necessary resources perform in the active system. It includes information about goals and benefits such as minimizing cost, enhanced backup and restore performance and decrease in data loss. Present the topic in a bit more detail with this Overview Of Archival Stage To Ensure Secure Data Lifecycle Management To Enhance Flow. Use it as a tool for discussion and navigation on Data Archive Storage Devices, Long-Term Retention And Storage Of Data, Cost-Effective Information Storage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Generic Database Architecture Of Mobile Security Mobile Security
Generic Database Architecture Of Mobile Security Mobile SecurityThis slide illustrates the key database architecture of mobile security which include mobile worker, internet, mobile server, firewall and database server. Present the topic in a bit more detail with this Generic Database Architecture Of Mobile Security Mobile Security Use it as a tool for discussion and navigation on Logical Device Access, Mobile Functions This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Introduction Of Data Layer In Web Security Solution
Introduction Of Data Layer In Web Security SolutionThis slide discusses the overview of the sixth layer of web security, which is the data layer for enhancing security in the web. Introducing Introduction Of Data Layer In Web Security Solution to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Ensure Data Integrity, Employing Data Encryption Is Crucial, Safeguard Against Unintentional Data Loss Deletion, using this template. Grab it now to reap its full benefits.
-
 Encryption For Data Organizational Chart Of Cyber Security Department Cybersecurity SS
Encryption For Data Organizational Chart Of Cyber Security Department Cybersecurity SSThis slide showcases hierarchy chart focused on building cybersecurity teams to help improve business data encryption. It provides details about DevOps, CISO, encryption specialist, engineer, etc. Present the topic in a bit more detail with this Encryption For Data Organizational Chart Of Cyber Security Department Cybersecurity SS. Use it as a tool for discussion and navigation on Organizational Chart, Cyber Security Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Encryption For Data Security Cybersecurity SS
Table Of Contents Encryption For Data Security Cybersecurity SSIntroducing Table Of Contents Encryption For Data Security Cybersecurity SS to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Team For Encryption, Encryption Costs Analysis, Pre Implementation Best Practices, using this template. Grab it now to reap its full benefits.
-
 Methods Of Cloud Data Network Security
Methods Of Cloud Data Network SecurityThis slide focuses on cloud data network security techniques including methods, strategic actions, and illustrations. Introducing our Methods Of Cloud Data Network Security set of slides. The topics discussed in these slides are Strategic Actions, Illustrations, Methods. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.



