Powerpoint Templates and Google slides for Security Of Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 5 step course of action plan of data security
5 step course of action plan of data securityPresenting this set of slides with name 5 Step Course Of Action Plan Of Data Security. This is a five stage process. The stages in this process are Identify Information Assets, Identify Risk, Manage Risks Across The Information, Determine Value Of Information, Apply Security Measures. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Architecture of cloud security data cloud security it ppt ideas
Architecture of cloud security data cloud security it ppt ideasThis slide defines the architecture of the cloud security system and how data is kept, managed, and secured based on customer and service providers responsibilities.Introducing Architecture Of Cloud Security Data Cloud Security IT Ppt Ideas to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Cloud Security, using this template. Grab it now to reap its full benefits.
-
 Security of data and networks in edge computing edge computing it
Security of data and networks in edge computing edge computing itThis slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable. Introducing Security Of Data And Networks In Edge Computing Edge Computing IT to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Of Data And Networks In Edge Computing, using this template. Grab it now to reap its full benefits.
-
 Data security it types of threats in data security ppt slides graphic tips
Data security it types of threats in data security ppt slides graphic tipsThis slide depicts the main types of threats in data security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Increase audience engagement and knowledge by dispensing information using Data Security IT Types Of Threats In Data Security Ppt Slides Graphic Tips. This template helps you present information on three stages. You can also present information on Cyber Crime, Cyber Terrorism, Cyber Attack, Cause Disruption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it what are the benefits of data security
Data security it what are the benefits of data securityThis slide depicts the different benefits of deploying a data security model in an organization and how it can minimize the risk and save a companys time, money, and efforts. Increase audience engagement and knowledge by dispensing information using Data Security IT What Are The Benefits Of Data Security. This template helps you present information on five stages. You can also present information on Legitimate Traffic, Hardware Security Devices, Threats And Risks, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it elements of data security end user education
Data security it elements of data security end user educationThis slide shows the end user education within the data security model. It also represents various factors that effective training plans should involve. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security End User Education. This template helps you present information on ten stages. You can also present information on Hire Professional, Identify Weakest Points System, Assessment Employees Knowledge CS, Emphasis On Phishing Scams, Train Often, Password Protocols using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
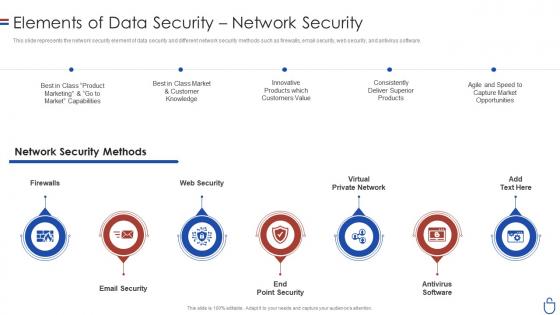 Data security it elements of data security network security
Data security it elements of data security network securityThis slide represents the network security element of data security and different network security methods such as firewalls, email security, web security, and antivirus software. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security Network Security. This template helps you present information on seven stages. You can also present information on Email Security, End Point Security, Antivirus Software, Virtual Private Network, Web Security, Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
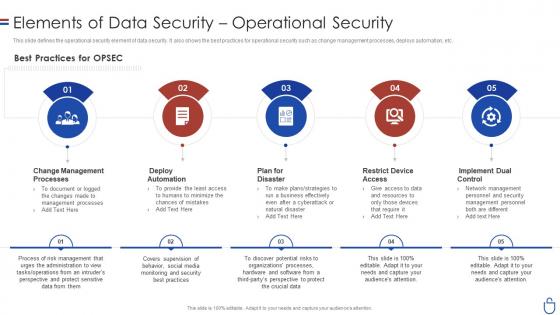 Data security it elements of data security operational security
Data security it elements of data security operational securityThis slide defines the operational security element of data security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Introducing Data Security IT Elements Of Data Security Operational Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Best Practices, OPSEC, Change Management Processes, Deploy Automation, Plan For Disaster, Restrict Device Access, Implement Dual Control, using this template. Grab it now to reap its full benefits.
-
 Data security it key elements of data security ppt slides background
Data security it key elements of data security ppt slides backgroundThis slide represents the different elements of data security such as application security, network security, information security, etc. Introducing Data Security IT Key Elements Of Data Security Ppt Slides Background to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Application Security, Network Security, End User Education, Cloud Security, Operational Security, Disaster Recovery Planning, Information Security, using this template. Grab it now to reap its full benefits.
-
 Data security it main principle of information security ppt slides topics
Data security it main principle of information security ppt slides topicsThis slide represents the main principles of information security such as confidentiality, integrity, and availability and how it makes data confidential and consistent, and available to authorized users. Introducing Data Security IT Main Principle Of Information Security Ppt Slides Topics to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Availability, Data, using this template. Grab it now to reap its full benefits.
-
 Addressing internal and external sources of threat data corporate security management
Addressing internal and external sources of threat data corporate security managementThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Introducing Addressing Internal And External Sources Of Threat Data Corporate Security Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Targeted Intelligence, Malware Intelligence, Reputation Intelligence, using this template. Grab it now to reap its full benefits.
-
 Essentials Of Information System Data And Application Security Audit
Essentials Of Information System Data And Application Security AuditThe following slide highlights the essentials of information system data and application security audit illustrating key headings which includes data confidentiality, information backup, application development and configuration management Introducing our premium set of slides with Essentials Of Information System Data And Application Security Audit. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Confidentiality, Application Development, Information Backup. So download instantly and tailor it with your information.
-
 Pillars Of Cloud Security Process Based Security Cloud Data Protection
Pillars Of Cloud Security Process Based Security Cloud Data ProtectionThis slide represents the process-based security pillar of cloud security. It also shows how it works and what precautions does it take. Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Process Based Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Operational Security, Management, Operations using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Segmentation Of Cloud Security Responsibilities Cloud Data Protection
Segmentation Of Cloud Security Responsibilities Cloud Data ProtectionThis slide shows cloud security responsibilities based on service type, namely Software as a Service SaaS, Platform as a service PaaS, Infrastructure as a Service IaaS. Increase audience engagement and knowledge by dispensing information using Segmentation Of Cloud Security Responsibilities Cloud Data Protection. This template helps you present information on three stages. You can also present information on Segmentation Of Cloud Security Responsibilities using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Approaches Of Cloud Disaster Recovery For Data Security
Approaches Of Cloud Disaster Recovery For Data SecurityThis slide shows four approaches of cloud disaster recovery that can be used by an organization to create a data secure environment. It includes backup and restore, warm study, pilot light and multi site active or active approach. Introducing our premium set of slides with Approaches Of Cloud Disaster Recovery For Data Security. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Backup And Restore, Warm Standby, Pilot Light. So download instantly and tailor it with your information.
-
 Four Steps Of Cyber Security Data Breach Risk Process
Four Steps Of Cyber Security Data Breach Risk ProcessThis slide covers steps utilised to breach data. It includes stages such as probing, performing initial attack, expansion of attacks and data lifting. Introducing our premium set of slides with name Four Steps Of Cyber Security Data Breach Risk Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Initial Attack, Expanded Attack, Breach Risk Process. So download instantly and tailor it with your information.
-
 Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security
Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Cyberbullying, Confidential Data, Training Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Impact Of Cyber Security Breach General Consequences Preventing Data Breaches Through Cyber Security
Impact Of Cyber Security Breach General Consequences Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline the impact of cyber security breach on the organization. The cyber attack make a significant impact on reputational damage, intellectual property IP theft, monetary penalty and operational disruption. Introducing Impact Of Cyber Security Breach General Consequences Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Damage, Theft Events, Monetary Penalty, using this template. Grab it now to reap its full benefits.
-
 Overview Of Cyber Security Awareness Course Preventing Data Breaches Through Cyber Security
Overview Of Cyber Security Awareness Course Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to provide a glimpse of the selected cyber security awareness course. It covers information about the instructor details, course content, attendees and learning outcome. Introducing Overview Of Cyber Security Awareness Course Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Course Content, Attendees, Learning Outcome, using this template. Grab it now to reap its full benefits.
-
 Statistics Highlighting Lack Of Cyber Security Awareness Preventing Data Breaches Through Cyber Security
Statistics Highlighting Lack Of Cyber Security Awareness Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline various statistics showing the lack of security awareness amongst the employees. The statistics covered in the slide is related to malware infection, using personal cloud server, malicious attachment etc. Introducing Statistics Highlighting Lack Of Cyber Security Awareness Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Confidential Data, Email, using this template. Grab it now to reap its full benefits.
-
 Understanding The Frequency And Weightage Of Cyber Preventing Data Breaches Through Cyber Security
Understanding The Frequency And Weightage Of Cyber Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the frequency and weightage of different cyber attacks on multiple departments. The major departments mentioned in the slide are financial, marketing, information technology IT and human resource HR. Introducing Understanding The Frequency And Weightage Of Cyber Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Financial Department, Marketing Team, IT Department, using this template. Grab it now to reap its full benefits.
-
 Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS V
Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Present the topic in a bit more detail with this Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS V. Use it as a tool for discussion and navigation on Network Security, Access Security, Data Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Datafication Of HR Measures To Maintain Data Security In Datafication
Datafication Of HR Measures To Maintain Data Security In DataficationThis slide talks about the measures to keep data secure in datafication, including legal requirements, technical measures and business practices, containing marketing campaigns, sales operations and customer service. The technical measures include encryption, firewalls, and access controls. Increase audience engagement and knowledge by dispensing information using Datafication Of HR Measures To Maintain Data Security In Datafication. This template helps you present information on four stages. You can also present information on Legal Requirements, Technical Measures, Business Practices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Different Types Of Network Security For Preventing Data Safely
Different Types Of Network Security For Preventing Data SafelyThis slide showcases various types of network security. The main purpose of this template is to ensure organizational data safety from any kind of threats. This includes firewall, remote access VPN, Network segmentation, email security, etc. Presenting our set of slides with Different Types Of Network Security For Preventing Data Safely. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Segmentation, Data Loss Prevention.
-
 Applications Of Big Data Analytics In Cyber Security
Applications Of Big Data Analytics In Cyber SecurityThis slide depicts the applications of big data analytics in implementing cybersecurity. The purpose of this slide is to help the business utilize big data security analytics in an appropriate manner for safeguarding business information. It includes data segmentation and clustering, tie series analysis and forecasting, etc. Introducing our premium set of slides with Applications Of Big Data Analytics In Cyber Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Calculation Of Statistical Parameters, Data Segmentation Clustering. So download instantly and tailor it with your information.
-
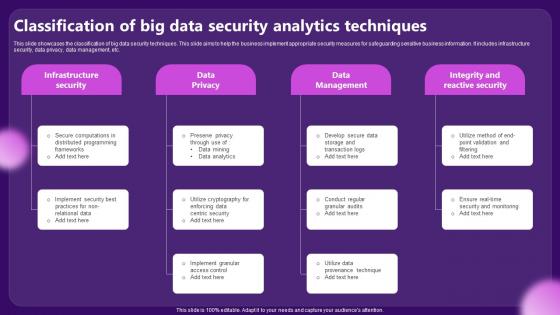 Classification Of Big Data Security Analytics Techniques
Classification Of Big Data Security Analytics TechniquesThis slide showcases the classification of big data security techniques. This slide aims to help the business implement appropriate security measures for safeguarding sensitive business information. It includes infrastructure security, data privacy, data management, etc. Presenting our set of slides with Classification Of Big Data Security Analytics Techniques. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure Security, Data Management.
-
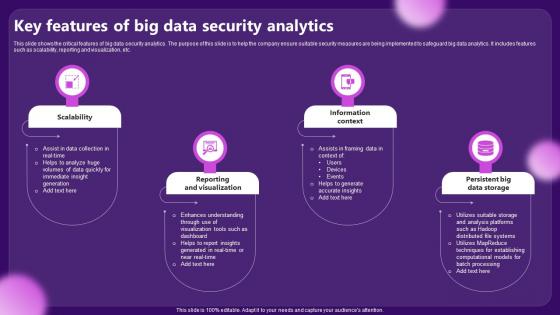 Key Features Of Big Data Security Analytics
Key Features Of Big Data Security AnalyticsThis slide shows the critical features of big data security analytics. The purpose of this slide is to help the company ensure suitable security measures are being implemented to safeguard big data analytics. It includes features such as scalability, reporting and visualization, etc. Presenting our set of slides with Key Features Of Big Data Security Analytics. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Scalability, Information Context.
-
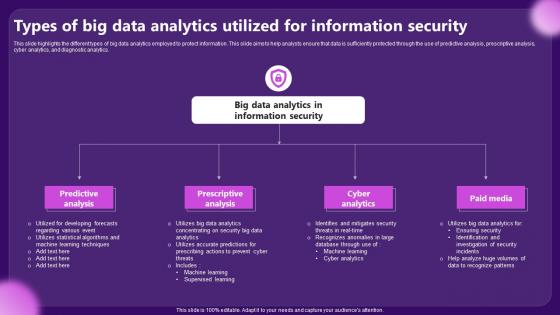 Types Of Big Data Analytics Utilized For Information Security
Types Of Big Data Analytics Utilized For Information SecurityThis slide highlights the different types of big data analytics employed to protect information. This slide aims to help analysts ensure that data is sufficiently protected through the use of predictive analysis, prescriptive analysis, cyber analytics, and diagnostic analytics. Presenting our set of slides with Types Of Big Data Analytics Utilized For Information Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Predictive Analysis, Prescriptive Analysis.
-
 Use Cases Of Big Data Security Analytics
Use Cases Of Big Data Security AnalyticsThis slide depicts the use cases of utilizing bug data security analytics. This slide aims to help the business utilize security analytics to safeguard information and prevent data thefts and information leaks. It includes instances like cloud security monitoring, user behavior analysis, etc. Presenting our set of slides with Use Cases Of Big Data Security Analytics. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Security Monitoring, Insider Threat Detection.
-
 Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V
Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Increase audience engagement and knowledge by dispensing information using Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V. This template helps you present information on three stages. You can also present information on Authentication, Encryption, Firewall using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V
Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Incident Management, Request Fulfillment using this template. Grab it now to reap its full benefits.
-
 Use Case Of Splunk Big Data For Security Intelligence
Use Case Of Splunk Big Data For Security IntelligenceFollowing slide showcases uses of splunk big data for security management. The purpose of this slide is to help businesses in investigating threats and improving compliance. It includes elements such as security monitoring, incident reporting, etc. Presenting our set of slides with Use Case Of Splunk Big Data For Security Intelligence This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Monitoring, Compliance.
-
 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
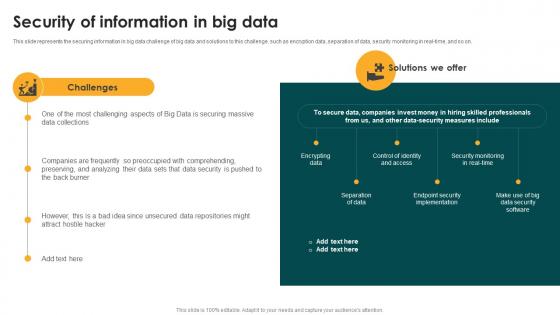 Security Of Information In Big Data Big Data Analytics And Management
Security Of Information In Big Data Big Data Analytics And ManagementThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Introducing Security Of Information In Big Data Big Data Analytics And Management to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Encrypting Data, Separation Of Data, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
 Business Impact Of Data Classification On Information Security
Business Impact Of Data Classification On Information SecurityThis slide shows key benefits of data classification for improving information security. The purpose of this slide is to help organizations in reducing burden of security teams by enhancing data protection strategies. It covers benefits such as risk evaluation, data backup, access control, compliance standards. Presenting our set of slides with Business Impact Of Data Classification On Information Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on General Data Protection Regulation, Compliance Standard, Protected Storage.
-
 Applications Of Digital Solution For Ensuring Data Security
Applications Of Digital Solution For Ensuring Data SecurityThis slide showcases use cases of digital solution. The main purpose of this template is to showcase methods for optimizing resources in business. This includes streamlining operations, improving decision making, enabling remote work, etc. Presenting our set of slides with Applications Of Digital Solution For Ensuring Data Security This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Streamlining Operations, Enhancing Customer Experience, Improve Decision Making
-
 Overview Of Virtual Private Network For Data Security
Overview Of Virtual Private Network For Data SecurityThis slide discusses the overview of virtual private network used for secure transfer of data through tunnelling protocols. Increase audience engagement and knowledge by dispensing information using Overview Of Virtual Private Network For Data Security. This template helps you present information on six stages. You can also present information on Public Network, Supporting Multiple Devices, Virtual Private Network, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security
Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data SecurityThis slide discusses the features of utility tokenization in data security. The purpose of this slide is to showcase the characteristics of utility tokenization which include service provided to user, purpose, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security. This template helps you present information on seven stages. You can also present information on Utility Tokenization, Data Security, Platforms Economic Activity, Blockchain Powered Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds
Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In DsThis slide highlights the steps for working of tokenization. The purpose of this slide is to outline the various ways of creating token and the phases which include initiating card transaction, producing tokens, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds. This template helps you present information on six stages. You can also present information on Mathematically Reversible, Cryptographic Function, Producing Tokens using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Impact Of Tokenization On Different Industries
Tokenization For Improved Data Security Impact Of Tokenization On Different IndustriesThis slide showcases the after tokenization impact on data security. It highlights the various factors that have improved the overall security by reducing time of release, rapid defect detection, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Impact Of Tokenization On Different Industries. This template helps you present information on six stages. You can also present information on Tokenization, Data Security, Rapid Defect Detection, Ensuring Trust And Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Introduction Of Utility Token In Data Security
Tokenization For Improved Data Security Introduction Of Utility Token In Data SecurityThis slide showcases the overview of utility tokens in data security. The purpose of this slide is to discuss the introduction of utility tokens required for data security and preventing thefts. Introducing Tokenization For Improved Data Security Introduction Of Utility Token In Data Security to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Data Security, Utility Tokens, Preventing Thefts, Unique To Each Platform, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Key Applications And Use Cases Of Tokenization
Tokenization For Improved Data Security Key Applications And Use Cases Of TokenizationThis slide discusses various application fields of tokenization. The purpose of this slide is to highlight the areas of application which include mobile wallet services, online retail platforms, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Key Applications And Use Cases Of Tokenization. This template helps you present information on three stages. You can also present information on Mobile Wallet Services, Online Retail Platforms, Businesses Storing Customer, Card Data Securely using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Overview And Process Of Tokenization In Data Security
Tokenization For Improved Data Security Overview And Process Of Tokenization In Data SecurityThis slide highlights the introduction and phases of tokenization in data security. The purpose of this slide is to showcase the overview and process such as various assets, verification of ownership, transfer to blockchain, etc. Introducing Tokenization For Improved Data Security Overview And Process Of Tokenization In Data Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization In Data Security, While Ensuring Security, Small And Midsize Enterprises, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems
Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting SystemsThis slide discusses the concept of governance tokenization in data security. The purpose of this slide is to showcase the overview of governance tokenization which include usage, features, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems. This template helps you present information on eight stages. You can also present information on Lack A Central Authority, Pivotal Decision Making, Widely Used Savings Protocol using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money Transfer
Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money TransferThis slide outlines the introduction of transactional tokenization. The purpose of this slide is to highlight the overview of transactional tokenization such as efficiency, lower cost, facilities, etc. Introducing Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money Transfer to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Tokenization, Data Security, Considering Security Tokens, Conventional Financial Securities, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain
Tokenization For Improved Data Security Role Of Utility Tokens In BlockchainThis slide discusses the objective of utility tokens in block chain. The purpose of this slide is to highlight the role of utility tokens which include decentralized storage, exchange value for service, etc. Introducing Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Storage, Block Chain Currency, Enhanced User Experience, Token Ownership Rights, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security
Tokenization For Improved Data Security Salient Features Of Tokenization In Data SecurityThis slide outlines the key characteristics of tokenization in data security. The purpose of this slide is to highlight the properties of tokenization that include underlying representation, transferability, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security. This template helps you present information on five stages. You can also present information on Underlying Representation, Transferability, Fungibility, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets
Tokenization For Improved Data Security Working Of Security Tokenization In Financial AssetsThis slide highlights the phases of security tokenization. The purpose of this slide is to showcase the working of security tokenization along with its phases which include creation, dividend distribution, etc. Introducing Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Working Of Security Tokenization, Financial Assets, Dividend Distribution, Security Token Classification, using this template. Grab it now to reap its full benefits.
-
 Different Types Of Visualization Security For Protecting Data
Different Types Of Visualization Security For Protecting DataThis slides showcases various types of visualization data. The main purpose of this template is to showcase data encryption for shared data. This includes role based access control, encrypted file sharing, regular security audits, etc. Introducing our premium set of slides with Different Types Of Visualization Security For Protecting Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Methods, Regular Security Audits, Encrypted File Sharing. So download instantly and tailor it with your information.
-
 Role Of Visualization Security For Understanding Complex Data
Role Of Visualization Security For Understanding Complex DataThis slides showcase ways of simplifying data through visualization security. The main purpose of this template is to showcase ways in which data can be protected and gain insights from customers. This includes simplifying complex data, identification trends, real time monitoring, etc. Presenting our set of slides with Role Of Visualization Security For Understanding Complex Data. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Simplifying Complex, Identification Trends, Driving Innovation.
-
 Introduction Of Cyber Threat Intelligence For Data Security
Introduction Of Cyber Threat Intelligence For Data SecurityThis slide discusses the overview of cyber threat intelligence for proactively blocking attacks and security purpose. Introducing Introduction Of Cyber Threat Intelligence For Data Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Evolving Threats Demand Intelligence, Vital For Security Architecture, Proactively Blocks Attacks, using this template. Grab it now to reap its full benefits.
-
 Comparative Assessment Of Encryption Algorithms For Organizational Data Security
Comparative Assessment Of Encryption Algorithms For Organizational Data SecurityThis slide provides a comparative assessment of various data encryption algorithms on different parameters. The multiple parameters used for assessment are encryption standard and use cases. Introducing our premium set of slides with Comparative Assessment Of Encryption Algorithms For Organizational Data Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Aes, Tdes, Twofish, Blowfish. So download instantly and tailor it with your information.


