Powerpoint Templates and Google slides for Network Method
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Methods of network protection sample diagram ppt design
Methods of network protection sample diagram ppt designPresenting methods of network protection sample diagram ppt design. This is a methods of network protection sample diagram ppt design. This is a six stage process. The stages in this process are error handing, controlled access, session management, network security, server and code management, data access.
-
 Critical path method network diagram creating business processes cpb
Critical path method network diagram creating business processes cpbThis is an editable three stages graphic that deals with topics like Critical Path Method Network Diagram, Creating Business Processes to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Network monitoring methods ppt powerpoint presentation professional graphics tutorials cpb
Network monitoring methods ppt powerpoint presentation professional graphics tutorials cpbPresenting this set of slides with name Network Monitoring Methods Ppt Powerpoint Presentation Professional Graphics Tutorials Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Network Monitoring Methods to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Project management network critical path method ppt powerpoint slides guide cpb
Project management network critical path method ppt powerpoint slides guide cpbPresenting this set of slides with name Project Management Network Critical Path Method Ppt Powerpoint Slides Guide Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Project Management Network Critical Path Method to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Network testing methodology ppt powerpoint presentation icon deck cpb
Network testing methodology ppt powerpoint presentation icon deck cpbPresenting this set of slides with name Network Testing Methodology Ppt Powerpoint Presentation Icon Deck Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Network Testing Methodology to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Network security authentication methods ppt powerpoint presentation file outfit cpb
Network security authentication methods ppt powerpoint presentation file outfit cpbPresenting this set of slides with name Network Security Authentication Methods Ppt Powerpoint Presentation Styles Brochure Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Network Security Authentication Methods to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Network testing methodology ppt powerpoint presentation styles demonstration cpb
Network testing methodology ppt powerpoint presentation styles demonstration cpbPresenting Network Testing Methodology Ppt Powerpoint Presentation Styles Demonstration Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase two stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Network Testing Methodology. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Network load balancer it methods we use for network load balancing
Network load balancer it methods we use for network load balancingThis slide describes the methods used in network load balancing, such as the least connection method, least response time, round robin, and IP hash method by the company. Introducing Network Load Balancer It Methods We Use For Network Load Balancing to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Least Connection Method, Least Response Time Method, Round Robin Method, using this template. Grab it now to reap its full benefits.
-
 Network Security Common Methods Used To Threaten Network Security
Network Security Common Methods Used To Threaten Network SecurityThis slide depicts the standard methods used to threaten network security by cybercriminals attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Network Security Common Methods Used To Threaten Network Security. This template helps you present information on five stages. You can also present information on Malicious, Necessary, Perform, Unavailable, Operations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Managing Network Security 60 Days Plan Methods
Network Security Managing Network Security 60 Days Plan MethodsThis slide depicts how the network security model will work in the first 30 days and the tasks the organization should focus on. Present the topic in a bit more detail with this Network Security Managing Network Security 60 Days Plan Methods. Use it as a tool for discussion and navigation on Managing Network Security 60 Days Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Methods We Use For Network Load Balancing Ppt Portfolio Demonstration
Methods We Use For Network Load Balancing Ppt Portfolio DemonstrationThis slide describes the methods used in network load balancing, such as the least connection method, least response time, round robin, and IP hash method by the company. Introducing Methods We Use For Network Load Balancing Ppt Portfolio Demonstration to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Least Response Time Method, Least Connection Method, Round Robin Method, using this template. Grab it now to reap its full benefits.
-
 Methodologies For Developing SDN 4d Approach Software Defined Networking IT
Methodologies For Developing SDN 4d Approach Software Defined Networking ITThis slide represents the 4D methodology of SDN development and includes the architecture and principles of the 4D approach. It also caters to the four planes that handle decision, distribution, discovery, and information. Deliver an outstanding presentation on the topic using this Methodologies For Developing SDN 4d Approach Software Defined Networking IT. Dispense information and present a thorough explanation of Architecture, Network Objectives, Centralized Controller using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Methodologies For Developing SDN Ethane Software Defined Networking IT
Methodologies For Developing SDN Ethane Software Defined Networking ITThis slide depicts the ethane methodology of SDN development by covering its overview and principles. It also caters to ethane architecture consisting of policies, registration, topology, bindings, flow entities, network devices, and an ethane controller. Present the topic in a bit more detail with this Methodologies For Developing SDN Ethane Software Defined Networking IT. Use it as a tool for discussion and navigation on Ethane Architecture, Overview, Ethane Principles. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Methodologies For Developing SDN Forces Software Defined Networking IT
Methodologies For Developing SDN Forces Software Defined Networking ITThis slide depicts the forwarding and control element separation methodology of SDN development and caters to the overview and deployment methods. It also includes the FORCES architecture, consisting of control and forwarding elements. Deliver an outstanding presentation on the topic using this Methodologies For Developing SDN Forces Software Defined Networking IT. Dispense information and present a thorough explanation of Control Element, Forwarding Element, Methods Of Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Predictive Modeling Methodologies Neural Network Model For Predictive Analytics
Predictive Modeling Methodologies Neural Network Model For Predictive AnalyticsThis slide depicts the neural networks model of predictive analytics that behave in the same manner as a human brain does. It used artificial intelligence and pattern recognition to operate on complex information connections. Increase audience engagement and knowledge by dispensing information using Predictive Modeling Methodologies Neural Network Model For Predictive Analytics. This template helps you present information on three stages. You can also present information on Neural Network Model, Predictive Analytics, Modular Neural Networks, Convolutional Neural Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Predictive Modeling Methodologies Overview Of Neural Network Model Types
Predictive Modeling Methodologies Overview Of Neural Network Model TypesThis slide depicts the different types of the neural network model, including their overview, use cases and usage. The main types include feed forward neural networks, recurrent, convolutional, deconvolutional and modular neural networks. Present the topic in a bit more detail with this Predictive Modeling Methodologies Overview Of Neural Network Model Types. Use it as a tool for discussion and navigation on Recurrent Neural Networks, Deconvolutional Neural Networks, Convolutional Neural Networks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Network Security Methods Using Blockchain Technology
Network Security Methods Using Blockchain TechnologyThis slide outlines network secure methods using blockchain medium by using strong authentication and cryptography key vaulting mechanisms. It covers strong identification and authentication, secure core technologies and communication. Introducing our premium set of slides with Network Security Methods Using Blockchain Technology. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strong Identities Authentication, Securing Core Technologies, Secure Communications. So download instantly and tailor it with your information.
-
 SDN Overlay Networks Methodologies For Developing SDN 4d Approach
SDN Overlay Networks Methodologies For Developing SDN 4d ApproachThis slide represents the 4D methodology of SDN development and includes the architecture and principles of the 4D approach. It also caters to the four planes that handle decision, distribution, discovery, and information. Deliver an outstanding presentation on the topic using this SDN Overlay Networks Methodologies For Developing SDN 4d Approach. Dispense information and present a thorough explanation of Centralized Controller, Network Devices, Disseminate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SDN Overlay Networks Methodologies For Developing SDN Ethane
SDN Overlay Networks Methodologies For Developing SDN EthaneThis slide depicts the ethane methodology of SDN development by covering its overview and principles. It also caters to ethane architecture consisting of policies, registration, topology, bindings, flow entities, network devices, and an ethane controller. Present the topic in a bit more detail with this SDN Overlay Networks Methodologies For Developing SDN Ethane. Use it as a tool for discussion and navigation on Ethane Architecture, Registration, Topology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SDN Overlay Networks Methodologies For Developing SDN Forces
SDN Overlay Networks Methodologies For Developing SDN ForcesThis slide depicts the forwarding and control element separation methodology of SDN development and caters to the overview and deployment methods. It also includes the FORCES architecture, consisting of control and forwarding elements. Deliver an outstanding presentation on the topic using this SDN Overlay Networks Methodologies For Developing SDN Forces. Dispense information and present a thorough explanation of Control Element, Forwarding Element, FORCES Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Methods To Invest In Blockchain Technology Network Working Of Blockchain Technology
Methods To Invest In Blockchain Technology Network Working Of Blockchain TechnologyThis slide talks about the various ways individuals or small businesses can invest in blockchain technology. The purpose of this slide is to share the different investment methods for blockchain, including buying stock, ETF, cryptocurrencies, and bitcoin mining. Increase audience engagement and knowledge by dispensing information using Methods To Invest In Blockchain Technology Network Working Of Blockchain Technology. This template helps you present information on four stages. You can also present information on Blockchain Stock, Buy Cryptocurrencies, Bitcoin Mining using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Using Different Types Of Guerilla Marketing Methods Using Viral Networking
Using Different Types Of Guerilla Marketing Methods Using Viral NetworkingThis slide showcases variations which can help online marketers in launching guerilla campaigns. It provides details about ambient, ambush, buzz, grassroots marketing along with their campaign activity and impact analysis. Introducing Using Different Types Of Guerilla Marketing Methods Using Viral Networking to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ambush Marketing, Grassroots Marketing using this template. Grab it now to reap its full benefits.
-
 Network Security Methodologies In Powerpoint And Google Slides Cpb
Network Security Methodologies In Powerpoint And Google Slides CpbPresenting Network Security Methodologies In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Network Security Methodologies. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Methods For Gaining CPA Network Introduction To CPA Marketing And Its Networks
Methods For Gaining CPA Network Introduction To CPA Marketing And Its NetworksThis slide showcase the tactics used by publisher to get accepted by the CPA networks. It includes strategies such as website designing, domain address, effective communication and proactive behaviour etc.Increase audience engagement and knowledge by dispensing information using Methods For Gaining CPA Network Introduction To CPA Marketing And Its Networks. This template helps you present information on four stages. You can also present information on Improve Communication, Be Proactive, Enhance Reach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Storage Area Network San Data Transfer Methods In San Environment
Storage Area Network San Data Transfer Methods In San EnvironmentThis Slide Illustrates The Main Data Transmission Approaches In A Storage Area Network Environment. The Purpose Of This Slide Is To Give An Overview Of Data Transfer In SAN And The Three Methods Of It, Including Server-To-Storage, Server-To-Server, And Storage-To-Storage. Present The Topic In A Bit More Detail With This Storage Area Network San Data Transfer Methods In San Environment. Use It As A Tool For Discussion And Navigation On Environment, Conventional, Communication. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
 Storage Area Network San Hardware And Software Deployment Method Of Hci
Storage Area Network San Hardware And Software Deployment Method Of HciThis Slide Represents The Deployment Methods Of Hyper-Converged Infrastructure, Including Hardware And Software. The Purpose Of This Slide Is To Showcase The Comparison Between Hardware And Software HCI Deployment Based On Form, Intention, Applications, Benefits And Concerns. Deliver An Outstanding Presentation On The Topic Using This Storage Area Network San Hardware And Software Deployment Method Of Hci. Dispense Information And Present A Thorough Explanation Of Software, Deployment, Hardware Using The Slides Given. This Template Can Be Altered And Personalized To Fit Your Needs. It Is Also Available For Immediate Download. So Grab It Now.
-
 Storage Area Network San Methods To Identify Zone Members In San Environment
Storage Area Network San Methods To Identify Zone Members In San EnvironmentThis slide represents the two methods to recognize the zone members in a Storage Area Network zoning environment. The purpose of this slide is to showcase the zone members identification methods, such as WWN zoning and port zoning, and how these methods identify the zone members. Increase audience engagement and knowledge by dispensing information using Storage Area Network San Methods To Identify Zone Members In San Environment. This template helps you present information on two stages. You can also present information on Environment, Implemented, Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Storage Area Network San Methods To Use Storage In Virtual Environment
Storage Area Network San Methods To Use Storage In Virtual EnvironmentThis slide describes the different approaches to using storage in virtual ecosystems. The purpose of this slide is to showcase the three primary methods to utilize storage virtualization, including host-based, array-based, and network-based virtualization. Present the topic in a bit more detail with this Storage Area Network San Methods To Use Storage In Virtual Environment. Use it as a tool for discussion and navigation on Environment, Virtualization, Approaches. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Storage Area Network San San Zoning Overview Types And Implementation Methods
Storage Area Network San San Zoning Overview Types And Implementation MethodsThis Slide Represents The Overview Of Zoning In The Storage Area Networks Environment. The Purpose Of This Slide Is To Highlight The Zone Sets, Types Of Zoning, And Various Implementation Methods, Such As Zone By Initiator Port, By HBA Vendor, By The Operating System, By Application, And So On. Present The Topic In A Bit More Detail With This Storage Area Network San San Zoning Overview Types And Implementation Methods. Use It As A Tool For Discussion And Navigation On Overview, Implementation, Environment. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
 Limitations Of Switched Port Analyzer Method Network Security Using Secure Web Gateway
Limitations Of Switched Port Analyzer Method Network Security Using Secure Web GatewayThis slide discusses drawbacks of Switched Port Analyzer method. The purpose of this slide is to explain why SPAN port is not considered as a real-time method. The limitations are unable to see all traffic, cause delays on network, etc. Introducing Limitations Of Switched Port Analyzer Method Network Security Using Secure Web Gateway to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Problematic, Business, Architecture, using this template. Grab it now to reap its full benefits.
-
 Methods To Implement Security Policies On Network Security Using Secure Web Gateway
Methods To Implement Security Policies On Network Security Using Secure Web GatewayThis slide demonstrates the different ways to enforce policies on remote and on-site employees using SWG. These are data loss prevention, encrypted traffic examination, protocol support, integration with anti-malware zero-day products, location flexibility, etc. Deliver an outstanding presentation on the topic using this Methods To Implement Security Policies On Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Organizational, Examination, Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Implementation Methodology Explicit Network Security Using Secure Web Gateway
Secure Implementation Methodology Explicit Network Security Using Secure Web GatewayThis slide talks about explicit scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of explicit SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Deliver an outstanding presentation on the topic using this Secure Implementation Methodology Explicit Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Implementation, Methodology, Concentrates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Web Gateway Methodology Inline Network Security Using Secure Web Gateway
Secure Web Gateway Methodology Inline Network Security Using Secure Web GatewayThis slide talks about the inline scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of inline SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Present the topic in a bit more detail with this Secure Web Gateway Methodology Inline Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Implementation, Methodology, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Swg Implementation Methodology Port Analyzer Port Network Security Using Secure Web Gateway
Swg Implementation Methodology Port Analyzer Port Network Security Using Secure Web GatewayThis slide talks about the SPAN scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of SPAN SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Present the topic in a bit more detail with this Swg Implementation Methodology Port Analyzer Port Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Implementation, Methodology, Analyzer. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Network Encryption Overview And Implementation Methods Encryption For Data Privacy In Digital Age It
Network Encryption Overview And Implementation Methods Encryption For Data Privacy In Digital Age ItThis slide talks about the network encryption methods to secure communication between two sites. This slide also demonstrates the ways to implement network encryption such as Communication Support Modules CSMs, Secure Sockets Layer SSL, etc. Deliver an outstanding presentation on the topic using this Network Encryption Overview And Implementation Methods Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Overview, Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Firewall Network Security Deployment Methods Of Firewall Security System
Firewall Network Security Deployment Methods Of Firewall Security SystemThis slide represents the key applications of firewall security systems. The purpose of this slide is to showcase the different deployment options of firewall security systems, such as software-based applications, hardware-based applications, and cloud-based applications. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Deployment Methods Of Firewall Security System This template helps you present information on Three stages. You can also present information on Software Based Applications, Hardware Based Applications, Cloud Based Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Network Security Intrusion Prevention Systems Ipss Overview And Methods
Firewall Network Security Intrusion Prevention Systems Ipss Overview And MethodsThis slide talks about the Intrusion Prevention System and its various methods for analyzing traffic. The purpose of this slide is to give an overview of Intrusion Prevention Systems and their methods, such as signature-based detection, statistical anomaly detection, and stateful protocol analysis detection. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Intrusion Prevention Systems Ipss Overview And Methods This template helps you present information on Three stages. You can also present information on Spyware Protection, Against Viruses, Prevents Hacking using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer Network Media Access Control Methods
Computer Network Media Access Control MethodsThis slide covers various methods of access control to regulate and manage access to the communication channel. It involves methods such as demand priority, token-passing collision avoidance, and collision detection. Introducing our premium set of slides with Computer Network Media Access Control Methods. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Demand Priority, Token Passing, Collision Detection. So download instantly and tailor it with your information.
-
 Training Method For Generative Adversarial Networks
Training Method For Generative Adversarial NetworksThis slide describes the training method for generative adversarial networks which include legitimate images, generative algorithm, discriminative algorithm, etc. Presenting our well structured Training Method For Generative Adversarial Networks The topics discussed in this slide are Discriminative Algorithm, Illegitimate ImageThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
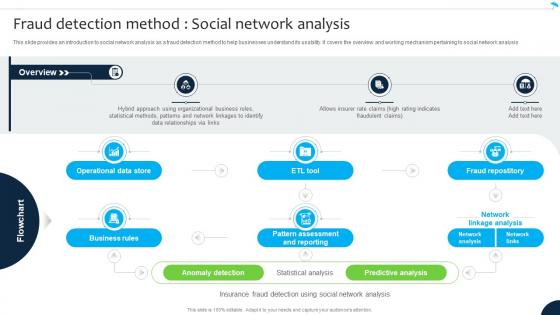 Fraud Detection Method Social Network Navigating The Future Of Insurance Data Analytics SS
Fraud Detection Method Social Network Navigating The Future Of Insurance Data Analytics SSThis slide provides an introduction to social network analysis as a fraud detection method to help businesses understand its usability. It covers the overview and working mechanism pertaining to social network analysis. Present the topic in a bit more detail with this Fraud Detection Method Social Network Navigating The Future Of Insurance Data Analytics SS. Use it as a tool for discussion and navigation on Operational Data Store, Business Rules, Pattern Assessment And Reporting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Sales Forecasting Models And Methods Approaching Sales Forecasting Using Neural Network SA SS
Sales Forecasting Models And Methods Approaching Sales Forecasting Using Neural Network SA SSPurpose of this slide is to use neural network for projecting company sales by analyzing historical data and applying trained algorithms of data science. Deliver an outstanding presentation on the topic using this Sales Forecasting Models And Methods Approaching Sales Forecasting Using Neural Network SA SS. Dispense information and present a thorough explanation of Perceptrons Determining Sales Pattern, Approaching Sales Forecasting, Neural Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Methods Of Cloud Data Network Security
Methods Of Cloud Data Network SecurityThis slide focuses on cloud data network security techniques including methods, strategic actions, and illustrations. Introducing our Methods Of Cloud Data Network Security set of slides. The topics discussed in these slides are Strategic Actions, Illustrations, Methods. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.


