Powerpoint Templates and Google slides for Information Processed
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Information security process key initiatives for project safety it ppt gallery example
Information security process key initiatives for project safety it ppt gallery exampleThis slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Present the topic in a bit more detail with this Information Security Process Key Initiatives For Project Safety It Ppt Gallery Example. Use it as a tool for discussion and navigation on Process, Information, Dynamic, System, Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information security process to manage firms sensitive data key initiatives for project safety it
Information security process to manage firms sensitive data key initiatives for project safety itThis slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Deliver an outstanding presentation on the topic using this Information Security Process To Manage Firms Sensitive Data Key Initiatives For Project Safety It. Dispense information and present a thorough explanation of Management, Network, Security, Performed using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information security process to manage firms project safety management it
Information security process to manage firms project safety management itThis slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Present the topic in a bit more detail with this Information Security Process To Manage Firms Project Safety Management It. Use it as a tool for discussion and navigation on Security, Network, Employees, Dynamic, System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information security process to manage firms sensitive data project safety management it
Information security process to manage firms sensitive data project safety management itThis slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Deliver an outstanding presentation on the topic using this Information Security Process To Manage Firms Sensitive Data Project Safety Management It. Dispense information and present a thorough explanation of Management, Network, Systems, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Asset components effective information security risk management process
Asset components effective information security risk management processFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost.Present the topic in a bit more detail with this Asset Components Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Impact Rating On Business, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Budget for information effective information security risk management process
Budget for information effective information security risk management processMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost.Deliver an outstanding presentation on the topic using this Budget For Information Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Incident Management, Asset Management, Training Duration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Defining risk level effective information security risk management process
Defining risk level effective information security risk management processFollowing slide defines the incident risk level. It includes details about risk level, risk score and its description. Deliver an outstanding presentation on the topic using this Defining Risk Level Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Immediate Controlling, Controlling Measures, Offered By The Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Defining vulnerability rating effective information security risk management process
Defining vulnerability rating effective information security risk management processFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description.Present the topic in a bit more detail with this Defining Vulnerability Rating Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Occurrence Of Attack, Organization Is Reasonably, Organization Is Capable Enough. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Effective information security management process information security risk assessment
Effective information security management process information security risk assessmentThis slide illustrates information security risk assessment worksheet. Risk covered are monetary loss, reputation loss and loss of customer confidence.Deliver an outstanding presentation on the topic using this Effective Information Security Management Process Information Security Risk Assessment. Dispense information and present a thorough explanation of Facilities And Equipment, Unauthorized Disclosure, Valuable Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Employee training schedule effective information security risk management process
Employee training schedule effective information security risk management processThis slide illustrates employee training schedule. It covers details about employee name, its position, software name, course type, training mode and duration.Present the topic in a bit more detail with this Employee Training Schedule Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Training Duration, Intermediate, Training Mode. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact on security performance effective information security risk management process
Impact on security performance effective information security risk management processMentioned slide shows performance impact on security infrastructure after introducing risk assessment process. Deliver an outstanding presentation on the topic using this Impact On Security Performance Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of After Introducing, Risk Assessment Process, Assets Efficiently using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Incident management tool effective information security risk management process
Incident management tool effective information security risk management processMentioned slide covers incident management tools. Firm will select its incident management tool based on feature description such as automated workflow, user access, mobile support and platform.Present the topic in a bit more detail with this Incident Management Tool Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Notify Employee, Message During Any Breach, Automated Workflow. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
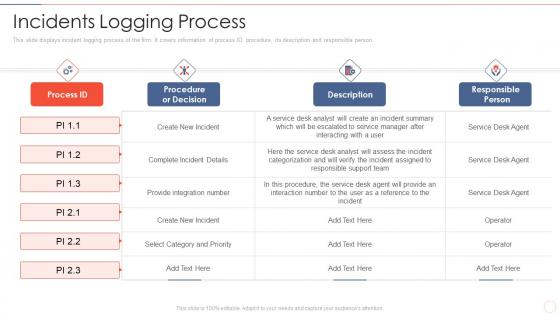 Incidents logging process effective information security risk management process
Incidents logging process effective information security risk management processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person.Deliver an outstanding presentation on the topic using this Incidents Logging Process Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Select Category And Priority, Procedure, The Service, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information security effective information security risk management process
Information security effective information security risk management processMentioned slide illustrates information security risk assessment worksheet. It include information about threat encountered, its vulnerability, asset and consequences and risk to the firm.Present the topic in a bit more detail with this Information Security Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Asset And Consequences, Overheating In Server Room, Asset And Consequences. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Mitigation plan for threat effective information security risk management process
Mitigation plan for threat effective information security risk management processMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode.Deliver an outstanding presentation on the topic using this Mitigation Plan For Threat Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Resources Required, Expected Resolution Time, Communication Mode using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Present security effective information security risk management process
Present security effective information security risk management processFollowing slide shows the current security management capabilities of the firm. It covers details about core functions, its description, key enablers, required and actual standard ratings.Present the topic in a bit more detail with this Present Security Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Assessing Information, Incident Occurrence Identification, Vulnerability Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk reporting and likelihood effective information security risk management process
Risk reporting and likelihood effective information security risk management processMentioned slide shows encountered risk reporting and its likelihood. It includes information about risk encountered, frequency, reported by status, attack scenario, affected asset and likelihood. Deliver an outstanding presentation on the topic using this Risk Reporting And Likelihood Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Attack Scenario, Risk Encountered, Equipment Failure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security risk management process incidents prioritization matrix effective information
Security risk management process incidents prioritization matrix effective informationThis slide shows incident prioritization matrix. Firm will use the matrix to prioritize incidents based on their urgency impact level Present the topic in a bit more detail with this Security Risk Management Process Incidents Prioritization Matrix Effective Information. Use it as a tool for discussion and navigation on Enterprise Or Multiple Segments, Single Segment Or Entire Site, Event Underway. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 System categorization worksheet effective information security risk management process
System categorization worksheet effective information security risk management processThis slide illustrates system categorization worksheet. It includes information about security system such as system name, its version, system location and other general information.Present the topic in a bit more detail with this System Categorization Worksheet Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on System Accessibility, Accessible Within Organization Boundary, Valuable Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 System disposal checklist effective information security risk management process
System disposal checklist effective information security risk management processMentioned slide shows system disposal checklist. It covers information such as system requirement, its compliance and remarks.Deliver an outstanding presentation on the topic using this System Disposal Checklist Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Stored Information Is Removed, Hardcopy Information, Requirement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 System management checklist effective information security risk management process
System management checklist effective information security risk management processFollowing slide displays system management checklist. It includes system management activities and frequency of performing them.Present the topic in a bit more detail with this System Management Checklist Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on System Monitoring, Security Patches, Virus Scanning . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table of contents for effective information security risk management process
Table of contents for effective information security risk management processDeliver an outstanding presentation on the topic using this Table Of Contents For Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Present Scenario, Training And Budget, Dashboards using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat assessment effective information security risk management process
Threat assessment effective information security risk management processFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Threat Assessment Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Affected Asset, Potential Vulnerability, Vulnerability Ranking using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Building organizational security strategy plan information security process to manage firms sensitive
Building organizational security strategy plan information security process to manage firms sensitiveThis slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Information Security Process To Manage Firms Sensitive. Use it as a tool for discussion and navigation on Information, Process, Sensitive. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information and event management logging process real time analysis of security alerts
Information and event management logging process real time analysis of security alertsThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Present the topic in a bit more detail with this Information And Event Management Logging Process Real Time Analysis Of Security Alerts. Use it as a tool for discussion and navigation on Information, Management, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Effective information security incidents logging process
Effective information security incidents logging processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Present the topic in a bit more detail with this Effective Information Security Incidents Logging Process. Use it as a tool for discussion and navigation on Complete Incident Details, Select Category And Priority, Provide Integration Number. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Infrastructure Library Strategy Processes
Information Technology Infrastructure Library Strategy ProcessesThis slide represents the servicer strategy process of the ITIL, including service management, service portfolio management, business relationship management, demand management, and financial management. Deliver an outstanding presentation on the topic using this Information Technology Infrastructure Library Strategy Processes. Dispense information and present a thorough explanation of Services, Strategy, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Flow Diagram Of Incident Response Process
Information Security Program Cybersecurity Flow Diagram Of Incident Response ProcessMentioned slide addresses the upcoming incident response process through flow diagram. Here the diagram is divided into three sections namely preparatory, core response and close down. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Flow Diagram Of Incident Response Process. Dispense information and present a thorough explanation of Flow Diagram Of Incident Response Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Introducing New Incidents Logging Process
Information Security Program Cybersecurity Introducing New Incidents Logging ProcessThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Present the topic in a bit more detail with this Information Security Program Cybersecurity Introducing New Incidents Logging Process. Use it as a tool for discussion and navigation on Introducing New Incidents Logging Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Due Diligence Process In M And A Transactions Information Technology Due Diligence
Due Diligence Process In M And A Transactions Information Technology Due DiligenceMentioned slide covers information technology due diligence checklist. It includes IT examination criteria and its status. Deliver an outstanding presentation on the topic using this Due Diligence Process In M And A Transactions Information Technology Due Diligence. Dispense information and present a thorough explanation of Information, Technology, Checklist using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security And Iso 27001 Incorporation Isms Framework Into Corporate Control Processes
Information Security And Iso 27001 Incorporation Isms Framework Into Corporate Control ProcessesMentioned slide displays the incorporation of information security management system framework within the corporate control process. Deliver an outstanding presentation on the topic using this Information Security And Iso 27001 Incorporation Isms Framework Into Corporate Control Processes. Dispense information and present a thorough explanation of Framework, Corporate, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Loan Collection Process Improvement Plan Customer Information Gathering Process
Loan Collection Process Improvement Plan Customer Information Gathering ProcessPurpose of the following slide is to show the new KYC form of the organization to better understand the customer information in a better way , the provided image holder show the KYC form details Present the topic in a bit more detail with this Loan Collection Process Improvement Plan Customer Information Gathering Process. Use it as a tool for discussion and navigation on Information, Process, Introduce. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Customer Information Gathering Process Mortgage Recollection Strategy For Financial Institutions
Customer Information Gathering Process Mortgage Recollection Strategy For Financial InstitutionsPurpose of the following slide is to show the new KYC form of the organization to better understand the customer information in a better way, the provided image holder show the KYC form details Present the topic in a bit more detail with this Customer Information Gathering Process Mortgage Recollection Strategy For Financial Institutions. Use it as a tool for discussion and navigation on Information, Gathering, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Exploration Process In Detail Efficient Data Preparation Make Information
Data Exploration Process In Detail Efficient Data Preparation Make InformationThis slide shows the data exploration process in detail that can be used to bring out the basic understanding of the real time data into data analytics. Present the topic in a bit more detail with this Data Exploration Process In Detail Efficient Data Preparation Make Information. Use it as a tool for discussion and navigation on Univariate Analysis, Exploration, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Defining Risk Level And Impact Score Iso 27001certification Process Ppt Slides Information
Defining Risk Level And Impact Score Iso 27001certification Process Ppt Slides InformationFollowing slide defines the incident risk level. It includes details about risk level, risk score and its description. Deliver an outstanding presentation on the topic using this Defining Risk Level And Impact Score Iso 27001certification Process Ppt Slides Information. Dispense information and present a thorough explanation of Organization, Description, Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Iso 27001 Information Security Management Standard Iso 27001certification Process
Iso 27001 Information Security Management Standard Iso 27001certification ProcessDeliver an outstanding presentation on the topic using this Iso 27001 Information Security Management Standard Iso 27001certification Process. Dispense information and present a thorough explanation of Contextual Requirements, Leadership Requirements, Planning Requirements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Performance Indicators To Measure Information Security Controls Iso 27001certification Process
Performance Indicators To Measure Information Security Controls Iso 27001certification ProcessFollowing slide illustrates performance indicators for measuring information security controls. It includes controls details, performance indicator formula, target and periodicity. Deliver an outstanding presentation on the topic using this Performance Indicators To Measure Information Security Controls Iso 27001certification Process. Dispense information and present a thorough explanation of Performance, Measure, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Infrastructure Automation Playbook Information Technology Infrastructure Library ITIL Process
IT Infrastructure Automation Playbook Information Technology Infrastructure Library ITIL ProcessThis slide provides information regarding Information Technology Infrastructure Library ITIL process in terms of principles and key elements of ITIL. Present the topic in a bit more detail with this IT Infrastructure Automation Playbook Information Technology Infrastructure Library ITIL Process. Use it as a tool for discussion and navigation on Principles Associated ITIL, Key Elements ITIL. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Crm Implementation Process Crm Implementation Process Ppt Professional Information
Crm Implementation Process Crm Implementation Process Ppt Professional InformationPresent the topic in a bit more detail with this Crm Implementation Process Crm Implementation Process Ppt Professional Information. Use it as a tool for discussion and navigation on Crm Implementation Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Process Of Using Rapid Application Development Methodology Ppt Information
Process Of Using Rapid Application Development Methodology Ppt InformationThis slide represents the rapid application development model design, including business modeling, information modeling, process modeling, application generation, and testing and turnover. Present the topic in a bit more detail with this Process Of Using Rapid Application Development Methodology Ppt Information. Use it as a tool for discussion and navigation on Business Modelling, Information Modelling, Process Modelling. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Phase In Dsdm Dsdm Process Ppt Slides Information
Implementation Phase In Dsdm Dsdm Process Ppt Slides InformationThis slide depicts implementation as a phase of DSDM that consists of four tasks implementing the system, reviewing project documents, users validation, and training. Deliver an outstanding presentation on the topic using this Implementation Phase In Dsdm Dsdm Process Ppt Slides Information. Dispense information and present a thorough explanation of Implementation, Assistance, Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Crm Pipeline For Revenue Generation Information Gathered For Lead Qualification Process
Managing Crm Pipeline For Revenue Generation Information Gathered For Lead Qualification ProcessThe sales department will generate crucial information of potential lead through webinar by collecting the relevant data from prospective leads such as job title, phone number, name, email address, etc. Deliver an outstanding presentation on the topic using this Managing Crm Pipeline For Revenue Generation Information Gathered For Lead Qualification Process. Dispense information and present a thorough explanation of Information, Qualification, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Processing Methods For Data Analysis And Research
Information Processing Methods For Data Analysis And ResearchThis slide covers the three main data processing methods manual, mechanical and electronic. The purpose of this template is to define different methods to analyze and research the data. Presenting our well structured Information Processing Methods For Data Analysis And Research. The topics discussed in this slide are Manual Data Processing, Mechanical Data Processing, Electronic Data Processing. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Workflow Of It Governance Process Information And Communications Governance Ict Governance
Workflow Of It Governance Process Information And Communications Governance Ict GovernanceThis slide describes the workflow of the IT governance process that starts from request acceptance, then goes to develop the business case, and then reaches its final status, which is approved or canceled. Present the topic in a bit more detail with this Workflow Of It Governance Process Information And Communications Governance Ict Governance. Use it as a tool for discussion and navigation on Governance, Process, Business. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ensuring Healthy Sales Pipeline Information Gathered For Lead Qualification Process
Ensuring Healthy Sales Pipeline Information Gathered For Lead Qualification ProcessThe sales department will generate crucial information of potential lead through webinar by collecting the relevant data from prospective leads such as job title, phone number, name, email address, etc. Present the topic in a bit more detail with this Ensuring Healthy Sales Pipeline Information Gathered For Lead Qualification Process. Use it as a tool for discussion and navigation on Communicating, Email Marketing, Business. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 ITIL Process Areas Service Strategy And Design Information Technology Infrastructure Library
ITIL Process Areas Service Strategy And Design Information Technology Infrastructure LibraryThis slide provides information regarding ITIL process areas in terms of service strategy and service design and associated sequential activities. Present the topic in a bit more detail with this ITIL Process Areas Service Strategy And Design Information Technology Infrastructure Library. Use it as a tool for discussion and navigation on Demand Management, Financial Management, Continuity Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enhancing Recruitment Process Through Information Comparative Assessment Of Cloud Recruitment Software
Enhancing Recruitment Process Through Information Comparative Assessment Of Cloud Recruitment SoftwareThis slide showcases comparative assessment which can guide HRs to choose amongst most suitable cloud recruitment software. It provides details about applicant tracking system, recruitment process management, candidate and employee management, etc. Deliver an outstanding presentation on the topic using this Enhancing Recruitment Process Through Information Comparative Assessment Of Cloud Recruitment Software. Dispense information and present a thorough explanation of Comparative, Assessment, Cloud Recruitment, Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enhancing Recruitment Process Through Information Difference Between Digital And Traditional Recruitment
Enhancing Recruitment Process Through Information Difference Between Digital And Traditional RecruitmentThis slide showcases major distinctions between traditional and digital hiring procedures. It provides details about human efforts, high volume impact, candidate engagement, scheduling, customization, costs, efficiency, effectiveness, etc. Present the topic in a bit more detail with this Enhancing Recruitment Process Through Information Difference Between Digital And Traditional Recruitment. Use it as a tool for discussion and navigation on Traditional Recruitment, Digital Recruitment, KPI Tracking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enhancing Recruitment Process Through Information KPIs Affected Post Recruitment Technology Utilization
Enhancing Recruitment Process Through Information KPIs Affected Post Recruitment Technology UtilizationThis slide showcases key performance indicators impacted after utilization of recruitment technology. It provides details about candidate quality, turnover rate, turnover cost, average hiring time, absences, hiring time, staff growth rate, etc. Deliver an outstanding presentation on the topic using this Enhancing Recruitment Process Through Information KPIs Affected Post Recruitment Technology Utilization. Dispense information and present a thorough explanation of Post Recruitment, Technology, Utilization, Turnover Rate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
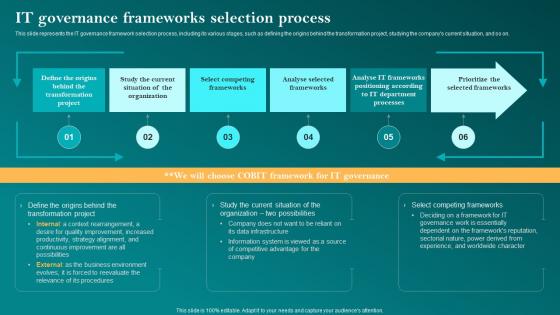 It Governance Frameworks Selection Process Corporate Governance Of Information Technology Cgit
It Governance Frameworks Selection Process Corporate Governance Of Information Technology CgitThis slide represents the IT governance framework selection process, including its various stages, such as defining the origins behind the transformation project, studying the companys current situation, and so on. Deliver an outstanding presentation on the topic using this It Governance Frameworks Selection Process Corporate Governance Of Information Technology Cgit. Dispense information and present a thorough explanation of Governance, Frameworks, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
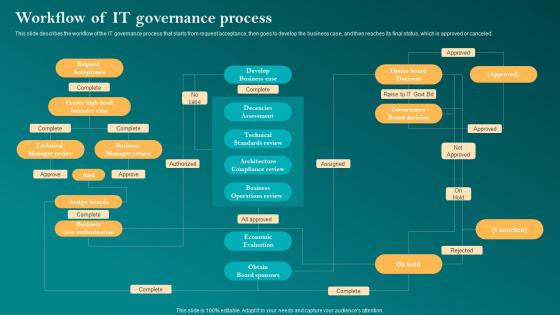 Workflow Of It Governance Process Corporate Governance Of Information Technology Cgit
Workflow Of It Governance Process Corporate Governance Of Information Technology CgitThis slide describes the workflow of the IT governance process that starts from request acceptance, then goes to develop the business case, and then reaches its final status, which is approved or canceled. Present the topic in a bit more detail with this Workflow Of It Governance Process Corporate Governance Of Information Technology Cgit. Use it as a tool for discussion and navigation on Governance, Process, Workflow. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Strategic Planning Process
Information Technology Strategic Planning ProcessThe slide showcases a framework for information technology strategy development. It involves three phases design, develop and deliver. Introducing our Information Technology Strategic Planning Process set of slides. The topics discussed in these slides are Strategic, Planning, Process . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Business Processes To Capture Effective Information
Business Processes To Capture Effective InformationThis slide exhibits various business processes that help companies to get authentic and organized information for taking effective management decisions. It include four types of process such as contact, expense, invoice and inventory management. Introducing our Business Processes To Capture Effective Information set of slides. The topics discussed in these slides are Contact Management, Expense Management, Invoice Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security Process To Manage Firms Sensitive Data Defense Plan To Protect Firm Assets
Information Security Process To Manage Firms Sensitive Data Defense Plan To Protect Firm AssetsThis slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Present the topic in a bit more detail with this Information Security Process To Manage Firms Sensitive Data Defense Plan To Protect Firm Assets. Use it as a tool for discussion and navigation on Privileged Password Management, Network Administrator. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 C104 Use Case Of Robotic Process Automation In Information Technology RPA Adoption Strategy
C104 Use Case Of Robotic Process Automation In Information Technology RPA Adoption StrategyThe mentioned slide provides some application scenarios of robotic process automation in various banking operation activities.It incorporates customer onboarding, commercial banking, retail banking, lending, credit card processing, etc. Deliver an outstanding presentation on the topic using this C104 Use Case Of Robotic Process Automation In Information Technology RPA Adoption Strategy Dispense information and present a thorough explanation of Process Automation, Information Technology Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategic Health Information System Planning Process Health Information Management System
Strategic Health Information System Planning Process Health Information Management SystemThis slide covers strategic health information system planning process. It involves three phases such as assessment, HIS planning and costing and implementation. Deliver an outstanding presentation on the topic using this Strategic Health Information System Planning Process Health Information Management System. Dispense information and present a thorough explanation of Information, Process, Strategic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Transforming Medical Services With His Healthcare Information Technology Trends To Transform Processes
Transforming Medical Services With His Healthcare Information Technology Trends To Transform ProcessesThis slide covers healthcare information technology trends to ensure effective transformation of health services. It involves key trends such as internet of medical things, cognitive automation and cyber security and data privacy. Present the topic in a bit more detail with this Transforming Medical Services With His Healthcare Information Technology Trends To Transform Processes. Use it as a tool for discussion and navigation on Internet Of Medical Things, Cognitive Automation, Cyber Security And Data Privacy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
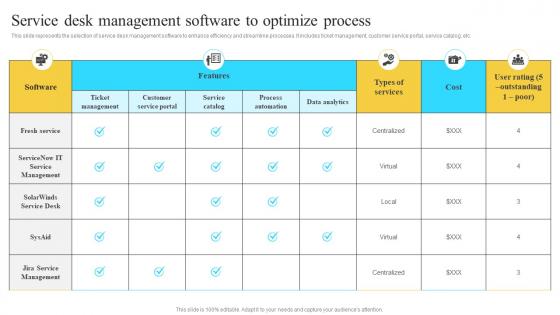 Implementation Of Information Service Desk Management Software To Optimize Process Strategy SS V
Implementation Of Information Service Desk Management Software To Optimize Process Strategy SS VThis slide represents the selection of service desk management software to enhance efficiency and streamline processes. It includes ticket management, customer service portal, service catalog, etc. Present the topic in a bit more detail with this Implementation Of Information Service Desk Management Software To Optimize Process Strategy SS V. Use it as a tool for discussion and navigation on Fresh Service, Ticket Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategic Engagement Process Multi Channel Outreach Plan To Disperse Product Information
Strategic Engagement Process Multi Channel Outreach Plan To Disperse Product InformationThis slide presents a multi-wave channel strategy to optimize consideration phase. It includes aspects such as media type, strategy, desired outcome and metrics. Deliver an outstanding presentation on the topic using this Strategic Engagement Process Multi Channel Outreach Plan To Disperse Product Information Dispense information and present a thorough explanation of Short And Simple, Open Ended Questions, Customer Feedback using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process
Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management ProcessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Present the topic in a bit more detail with this Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source. This template is free to edit as deemed fit for your organization. Therefore download it now.



